Abstract
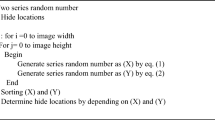
Information technology is playing a greater role in different spheres of life for quick operational processes. It helps in time-saving in the era of globalization by exchanging information over the internet. However, using the internet as a medium for information exchange can cause the risk of data being hacked/modified. The hackers have found illegitimate actions of cyberspace anonymity a great platform. These intruders are technically well-skilled to modify, breach and steal sensitive information. Thus, providing security to such important data is a big challenge for researchers. This paper presents novel image steganography using edge detection technique and chaotic function. The edge regions of an image have been used to hide sensitive information. These edge regions have been detected using a combination of Canny and Laplacian of Gaussian detectors. Before embedding, the important data is encrypted using coupled chaos functions (Logistic and Sine maps) to improve data security. The maps in the presented framework have been used in an alternative manner in which the output of one maps’ iteration is used as an initial key to another map. The proposed method is analyzed for quality, security, and payload. From the evaluation perspective, the proposed framework shows better results for Peak Signal to Noise Ratio of 43.97 dB, Number of Changes per Rate of 99.9998%, Unified Average Changed Intensity of 52.8914%, and Entropy value of 7.7883. The comparison of the proposed scheme shows superiority over state-of-the-art techniques, hence proving the efficacy of the proposed scheme.







Similar content being viewed by others
References
Jan, A.; Parah, S.A.; Malik, B.A.; Rashid, M.: Secure data transmission in IoTs based on CLoG edge detection. Future Gener. Comput. Syst. (2021). https://doi.org/10.1016/j.future.2021.03.005
Lawrence, A.: 27 April 2021. https://www.databreaches.net/reverb-discloses-data-breach-exposing-musicians-personal-info
Jecica, D.: 2 April 2021. https://healthitsecurity.com/news/patient-data-from-multiple-providers-leaked-in-third-party-github-incident
Protenus Breach Barometer. https://blog.protenus.com/key-takeaways-from-the-2021-breach-barometer
Miri, A.; Faez, K.: An image steganography method based on integer wavelet transform. Multimed. Tools Appl. 77, 13133–13144 (2018)
Sahu, A.K.; Swain, G.: Reversible image steganography using dual-layer LSB matching. Sens. Imaging 21, 1 (2020)
Ghosal, S.K.; Mukhopadhyay, S.; Hossain, S.; Sarkar, R.: Exploiting Laguerre transform in image steganography. Comput. Electr. Eng. 89, 106964 (2021)
Lin, J.; Qian, Z.; Wang, Z.; Zhang, X.; Feng, G.: A new steganography method for dynamic GIF images based on palette sort. Wirel. Commun. Mob. Comput. 2020, 8812087 (2020)
Wang, J.; Yang, C.; Wang, P.; Song, X.; Lu, J.: Payload location for JPEG image steganography based on co-frequency sub-image filtering. Int. J. Distrib. Sens. Netw. 16(1), 256 (2020)
Shen, S.Y.; Huang, L.H.: A novel adaptive data hiding based on improved EMD and interpolation. Multimed. Tools Appl. 48, 131–141 (2015)
Saidi, M.; Hermassi, H.; Rhouma, R.; Belghith, S.: A new adaptive image steganography scheme based on DCT and chaotic map. Multimed. Tools Appl. 76(11), 13493–13510 (2017)
Kumar, R.; Kim, D.S.; Jung, K.H.: Enhanced AMBTC based data hiding method using hamming distance and pixel value differencing. J. Inf. Secur. Appl. 47, 94–103 (2019)
Malik, A.; Sikka, G.; Verma, H.K.: An AMBTC compression based data hiding scheme using pixel value adjusting strategy. Multidim. Syst. Sign. Process. 29(4), 1801–1818 (2018)
Kim, C.; Yang, C.N.; Leng, L.: High-capacity data hiding for ABTC-EQ based compressed image. Electronics 9(4), 644 (2020)
Kim, C.; Shin, D.; Leng, L.; Yang, C.N.: Lossless data hiding for absolute moment block truncation coding using histogram modification. J. Real-Time Image Proc. 14(1), 101–114 (2018)
Sowmya, P.; Karuna, G.; Shalini, R.S.; Suneetha, C.H.K.: An exploiting study on image edge detection quality evaluation using various algorithms. Mater. Today Proc. (2020). https://doi.org/10.1016/j.matpr.2020.09.511
Ayub, N.; Selwal, A.: An improved image steganography technique using edge based data hiding in DCT domain. J. Int. Math. 23(2), 357–366 (2020)
Ghosal, S.K.; Mandal, J.K.; Sarkar, R.: High payload image steganography based on Laplacian of Gaussian (LoG) edge detector. Multimed. Tools Appl. 77, 30403–30418 (2018)
Banik, B.G.; Bandyopadhyay, S.M.: An image steganography method on edge detection using multiple LSB modification technique. J. Basic Appl. Res. Int. 9(2), 75–80 (2015)
Parah, S.A.; Kaw, J.A.; Bellavista, P.; Loan, N.A.; Bhat, G.M.; Muhammad, K.; Victor, A.: Efficient security and authentication for edge-based Internet of Medical Things. IEEE Trans. Internet Things J. (2021). https://doi.org/10.1109/JIOT.2020.3038009
Ghosal, S.K.; Chatterjee, A.; Sarkar, R.: Image steganography based on Kirsch edge detection. Multimed. Syst. 27, 73–87 (2021)
Prasad, S.; Pal, A.K.: Stego-key-based image steganography scheme using edge detector and modulus function. Int. J. Comput. Vis. Robot. 10(3), 223–240 (2020)
Garav, K.; Ghanekar, U.: Image steganography algorithm based on edge region detection and hybrid coding. Comput. Model. Technol. 22(1), 40–56 (2018)
Dhargupta, S.; Chakraborty, A.; Ghosal, S.K.; Saha, S.; Sarkar, R.: Fuzzy edge detection based steganography using modified Gaussian distribution. Multimed. Tools Appl. 25, 1548 (2019)
Sajedi, H.; Yaghobi, S.R.: Information hiding methods for E-Healthcare. Smart Health 15, 100104 (2020)
Bhagat, D.; Bhardwaj, R.: A survey on medical images for reversible data hiding techniques. IEEE Trans. (2019)
Asanbe, M.O.: Hybrid data security: a review of cryptography and steganography techniques. Villanova J. Sci. Technol. Manag. 2(1), 1547 (2020)
Kaur, R.; Singh, B.: A novel approach for data hiding based on combined application of discrete cosine transform and coupled chaotic map. Multimed. Tools Appl. (2021)
Delmi, A.; Suryadi, S.; Satria, Y.: Digital image steganography by using edge adaptive based chaos cryptography. J. Phys: Conf. Ser. 1442, 012041 (2017)
Eyssa, A.A.; Abdelsamie, F.E.; Abdelnaiem, A.E.: An efficient image steganography approach over wireless communication system. Wirel. Pers. Commun. 110, 321–337 (2020)
Jan, A.; Parah, S.A.; Malik, B.A.: A novel Laplacian of Gaussian and chaotic encryption based image steganography technique. In: 2020 international conference for emerging technology (INCET), Belgaum, 1–4 (2020). https://doi.org/10.1109/INCET49848.2020.9154173
Jan, A.; Parah, S.A.; Malik, B.A.: Logistic map-based image steganography using edge detection. Adv. Intell. Syst. Comput. (2021). https://doi.org/10.1007/978-981-15-6067-5_50
Parah, S.A.; Sheikh, J.A.; Akhoon, J.A.; Loan, N.A.: Electronic health record hiding in images for smart city applications: a computationally efficient and reversible information hiding technique for secure communication. Futur. Gener. Comput. Syst. (2018). https://doi.org/10.1016/j.future.2018.02.023
Khan, M.F.; Ahmed, A.; Saleem, K.: A novel cryptographic substitution box design using Gaussian distribution. IEEE Access 7, 15999–16007 (2019)
Parah, S.A.; Bhat, G.M.; Sheikh, J.A.: A secure and efficient data hiding technique based on pixel adjustment. Am. J. Eng. Technol. Res. 14(2), 38–44 (2014)
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Jan, A., Parah, S.A., Hassan, M. et al. Realization of Efficient Steganographic Scheme Using Hybrid Edge Detection and Chaos. Arab J Sci Eng 48, 1859–1872 (2023). https://doi.org/10.1007/s13369-022-06960-w
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s13369-022-06960-w