Abstract
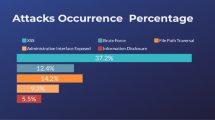
Nowadays, Web applications are considered to be one of the most ubiquitous platforms for providing the information and service release over the World Wide Web, particularly those deployed in health care, banking, e-commerce operations, etc. Boom of social networking sites and modern Web applications that transfer dynamic information to the client-side Web browsers has increased the user-generated and feature-rich HTML content on the Internet. This enhanced HTML content includes a malicious attack vector for Web-related attacks. Cross-site scripting (XSS) attacks are presently the most exploited security problems in modern Web applications and activated by an attacker to utilize the vulnerabilities of the poorly written Web application source code. Users across all over the popular social networking Web sites are exposed to XSS attacks. These attacks are generally caused by the malicious scripts, which do not validate the user-injected input appropriately and exploit the vulnerabilities in the source code of the Web applications. It results in the loss of confidential information such as stealing of cookies, theft of passwords, and other private credentials. In this paper, we propose a robust framework known as XSS-SAFE (Cross-Site Scripting Secure Web Application FramEwork), which is a server-side automated framework for the detection and mitigation of XSS attacks. XSS-SAFE is designed based on the idea of injecting the features of JavaScript and introduced an idea of injecting the sanitization routines in the source code of JavaScript to detect and mitigate the malicious injected XSS attack vectors. We repeatedly inject the feature content, generate rules, and insert sanitization routines for the discovery of XSS attacks. We have evaluated our approach on five real-world JavaServer Pages (JSP) programs. The results indicate that XSS-SAFE detects and mitigates most of the previously known and unknown XSS attacks with minimum false positives, zero false-negative rate, and low runtime overhead.
Similar content being viewed by others
References
Flanagan D.: JavaScript: The Definitive Guide, 4th edn. O’Reilly, Newton (2001)
MacDonald, M.; Szpuszta, M.: Pro ASP.NET 2.0 in C#,” 2005, 1st edn. Apress. ISBN 1-59059-496-7
Symantec Corporation. Symantec Global Internet Security Threat Report, vol. 19 (2014)
CERT/CC. Cert R _ advisory ca-2000-02 malicious html tags embedded in client web requests. [online]. http://www.cert.org/advisories/CA-2000-02.html (01/30/06), Feb 2000
Rager, A.: Xss-proxy. http://xss-proxy.sourceforge.net
Samy.: Technical explanation of the myspace worm. http://namb.la/popular/tech.html
Open Web Application Security Project (OWASP), http://www.owasp.org
Gupta, S.; Gupta, B.B.: PHP-sensor: a prototype method to discover workflow violation and XSS vulnerabilities in PHP web applications. In: Proceedings of the 12th ACM International Conference on Computing Frontiers (CF’15), Ischia, Italy (2015)
Gupta B.B., Gupta S., Gangwar S., Kumar M., Meena P.K.: Cross-site scripting (XSS) abuse and defense: exploitation on several testing bed environments and its defense. J. Inf. Priv. Sec. 11(2), 118–136 (2015)
Gupta, S.; Gupta, B.B.: Cross-site scripting (XSS) attacks and defense mechanisms: classification and state-of-the-art. Int. J. Syst. Assur. Eng. Manag. (2015). doi:10.1007/s13198-015-0376-0
Klein, A.: Cross site scripting explained. White Paper, Sanctum Security Group, http://crypto.stanford.edu/cs155/CSS.pdf, June 2002
Gupta, S.; Sharma, L., et al.: Prevention of cross-site scripting vulnerabilities using dynamic hash generation technique on the server side. Int. J. Adv. Comput. Res. 3, 49–54 (2012)
Gupta, S.; Sharma, L.: Exploitation of cross-site scripting (XSS) vulnerability on real world web applications and its defense. Int. J. Comput. Appl. 14, 28–33 (2012)
Gupta, S.; Gupta, B.B.: BDS: Browser Dependent XSS Sanitizer. Book on Cloud-Based Databases with Biometric Applications, IGI-Global’s Advances in Information Security, Privacy, and Ethics (AISPE) series, USA (2014)
Cross-Site Scripting (XSS) Attacks Information and Archive. http://xssed.com/
Netscape, Accessed from: http://isp.netscape.com/
ECMA Script, Accessed from http://www.ecmascript.org/docs.php
Sandboxing: https://developer.apple.com/app-sandboxing/
Mozilla Corporation. Same origin policy for JavaScript, https://developer.mozilla.org/En/Same origin policy for JavaScript
JAuction-0.3, http://sourceforge.net/projects/jauction/
Jvote, Accessed from http://sourceforge.net/projects/jspvote/
MeshCMS: http://cromoteca.com/en/meshcms/
Easy JSP Forum, http://sourceforge.net/projects/easyjspforum
Shaihriar, H.; Zulkernine, M.: S2XS2: a server side approach to automatically detect XSS attacks. In: Ninth International Conference on Dependable, Automatic Secure Computing, IEEE, 2011 pp. 7–17
Shahriar, H.; Zulkernine, M.: Injecting comments to detect javascript code injection attacks. In: Proceedings of the 6th IEEE Workshop on Security, Trust, and Privacy for Software Applications, Munich, Germany, July 2011, pp. 104–109
Cao, Y.; Yegneswaran, V.; Possas, P.; Chen.: Pathcutter: severing the self-propagation path of xssjavascript worms in social web networks. In: Proceedings of the 19th Network and Distributed System Security Symposium (NDSS), San Diego, CA, USA (2012)
Chandra V.S., Selvakumar S.: Bixsan: browser independent XSS sanitizer for prevention of XSS attacks. ACM SIGSOFT Softw. Eng. Notes 36(5), 1 (2011)
Rsnake. XSS Cheat Sheet. http://ha.ckers.org/xss.html (2008)
Saxena, P.; Hanna, S.; Poosankam, P.; Song, D.: FLAX: systematic discovery of client-side validation vulnerabilities in rich web applications. In: NDSS (2010)
Stamm, S.; Sterne, B.; Markham, G.: Reining in the web with content security policy. In: ACM Proceedings of the 19th International Conference on World Wide Web, WWW ’2010, New York, NY, USA, pp. 921–930
Wurzinger, P.; Platzer, C.; Ludl, C.; Kirda, E.; Kruegel, C.: SWAP: Mitigating XSS attacks using a reverse proxy. In: ICSE Workshop on Software Engineering for Secure Systems. IEEE Computer Society (2009)
Galan, E.; Alcaide, A.; Orfila, A.; Blasco, J.: A Multi-agent Scanner to Detect Stored—XSS Vulnerabilities? In: IEEE International Conference on Internet Technology and Secure Transactions (ICITST), June 2010, pp. 332–337
Gundy, M.V.; Chen, H.: Noncespaces: using randomization to enforce information flow tracking and thwart cross-site scripting attacks. In: Proceedings of the 16th Annual Network and Distributed System Security Symposium (NDSS), San Diego, CA, Feb 8–11 (2009)
Agten, P.; Acker, S.V.; Brondsema, Y.; Phung, P.H.; Desmet, L.; Piessens, F.: Jsand: complete client-side sandboxing of third-party JavaScript without browser modifications. In: Zakon, R.H. (ed.) ACSAC. ACM, pp. 1–10 (2012)
Jflex—The Fast Scanner Generator for Java: http://www.jflex.de/
Java Parser Cup: http://www.cs.princeton.edu/~appel/modern/java/CUP/
Jericho HTML parser, Accessed from http://jericho.htmlparser.net/
Jsoup: Java HTML Parser: http://jsoup.org/
Rhino Parser, Accessed from http://www.mozilla.org/rhino
Rhino, Accessed from http://www.mozilla.org/rhino
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Gupta, S., Gupta, B.B. XSS-SAFE: A Server-Side Approach to Detect and Mitigate Cross-Site Scripting (XSS) Attacks in JavaScript Code. Arab J Sci Eng 41, 897–920 (2016). https://doi.org/10.1007/s13369-015-1891-7
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s13369-015-1891-7