Abstract
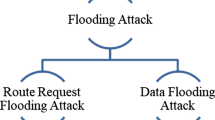
Mobile ad hoc networks are often deployed in environments where the nodes of the networks are unattended and have little or no physical protection against tampering. The nodes of mobile ad hoc networks are thus susceptible to compromise. The networks are particularly vulnerable to denial of service (DoS) attacks launched through compromised nodes or intruders. In this paper, we investigated the effects of flooding attacks in network simulation 2 (NS-2) and measured the packet delivery ratio and packet delay under different flooding frequencies and different numbers of attack nodes. Simulation results show that with the increase the flooding frequencies and the numbers of attack nodes, network performance drops. But when the frequency of flooding attacks is greater than a value, the performance decrease gets smooth. Meanwhile the packet delay firstly increases and then declines to a value of stability at the end.
Similar content being viewed by others
References
RFC 2501, Mobile ad hoc networking (MANET): Routing protocol performance issues and evaluation considerations [S].
Yi Ping, Dai Zhou-lin, Zhong Yi-ping, et al. Resisting flooding attacks in ad hoc networks [C]// Proceedings of International Conference on Information Technology: Coding and Computing (ITCC2005). Las Vegas, USA: IEEE Press, 2005: 657–662.
Desilva S, Boppana R V. Mitigating malicious control packet floods in ad hoc networks [C]// Proceedings of 2005 IEEE Wireless Communications and Networking Conference (WCNC2005). [s.l.]: IEEE, 2005: 2112–2117.
Guo Ying-hua, Perreau S. Trace flooding attack in mobile ad hoc networks [C]// Proceedings of 3rd International Conference on Intelligent Sensors, Sensor Networks and Information (ISSNIP 2007). NJ, USA: IEEE, 2007: 657–662.
Guo Ying-hua, Gordon S, Perreau S. A flow based detection mechanism against flooding attacks in mobile ad hoc networks [C]// Proceedings of 2007 IEEE Wireless Communications and Networking Conference (WCNC2007). [s.l.]: IEEE, 2007: 3105–3110.
Xia Zheng-you, Wang Lang. DIMH: A novel model to detect and isolate malicious hosts for mobile ad hoc network [J]. Computer Standards & Interfaces, 2006, 58(6): 660–669.
Yi Ping, Zou Fu-tai, Jiang Xing-hao, et al. Mutiagent cooperative intrusion response in mobile ad hoc networks [J]. Journal of Systems Engineering and Electronics, 2007, 18(4): 785–794.
Author information
Authors and Affiliations
Corresponding author
Additional information
Foundation item: the Shanghai Municipal Natural Science Foundation (No. 09ZR1414900), the National High Technology Research and Development Program (863) of China (Nos. 2006AA01Z436, 2007AA01Z452 and 2009AA01Z118)
Rights and permissions
About this article
Cite this article
Yi, P., Zhou, Yk., Wu, Y. et al. Effects of denial of service attack in mobile ad hoc networks. J. Shanghai Jiaotong Univ. (Sci.) 14, 580–583 (2009). https://doi.org/10.1007/s12204-009-0580-7
Received:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s12204-009-0580-7