Abstract
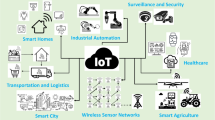
Along with the rapid development of Internet-of-Things (IoT), fog-to-cloud computing is now popularly considered as a new paradigm to support kinds of IoT applications. Like traditional cloud storage, fog-to-cloud storage also suffers from many security threatens. One of most important concerns is how to check the integrity of outsourced IoT data (in cloud server). Although fruitful auditing schemes were proposed for traditional cloud storage, few of them can be directly applied in the fog-to-cloud setting. In the recent work of Tian et al., for the first time, they considered this problem. However, in their protocol, the computational complexity and communication overhead are very high for mobile sinks or fog node, which has constraint computational ability. Moreover, the dynamic update function was not considered in their work. In this paper, we follow the line of Tian et al. and re-consider the public auditing technique in fog-to-cloud-based IoT scenarios. Based on the linearly homomorphic proxy re-signature technique, we propose a new public auditing protocol, which does not only support dynamic update of IoT data but also preserves the privacy against third party auditor. Performance analysis shows that our protocol outperforms that of Tian et al. and hence is rather practical for fog-to-cloud-based applications.









Similar content being viewed by others
References
Bonomi F, Milito R, Zhu J, Addepalli S (2012) Fog computing and its role in the internet of things. In Proceedings of 1st edition of the MCC workshop on mobile cloud computing. New York, pp 13–16
Wang H, Feng L, Ji Y et al (2022) Toward usable cloud storage auditing, revisited. IEEE Syst J 16(1):693–700
Zhang T (2016) Fog boosts capabilities to add more things securely to the internet. In http://blogs.cisco.com/innovation/fog-boosts-capabilities-to-add-more-things-securely-to-the-internet
Roman R, Lopez J, Mambo M (2018) Mobile edge computing fog et al.: A survey and analysis of security threats and challenges. Future Gen Comput Syst 78:680–698
Ateniese G, Burns R, Curtmola R et al (2007) Provable data possession at untrusted stores. In CCS’2014, ACM. Alexandria, Virginia, USA, pp 598–609
Barsoum A, Hasan MA (2015) Provable multicopy dynamic data possession in cloud computing systems. IEEE Trans Inf Forensics Sec 10(3):485–497
Chang J, Ji Y, Xu M et al (2019) General transformations from single-genearation to multi-generation for homomorphic message authentication schemes in network coding. Futur Gener Comput Syst 91:416–425
Chang J, Ma H, Zhang A, Xu M, Xue R (2019) RKA security of identity-based homomorphic signature scheme. IEEE Access 7:50858–50868
Shacham H, Waters B (2013) Compact proofs of retrievability. J Cryptol 26:442–483
Tian H, Chen Y, Chang C, Jiang H, Huang Y, Chen Y, Liu J (2017) Dynamic-hash-table based public auditing for secure cloud storage. IEEE Trans Serv Comput 10:701–714
Tian H, Nan F, Chang C, Huang Y, Lu J, Du Y (2019) Privacy-preserving public auditing for secure data storage in fog-to-cloud computing. J Netw Comput Appl 127:59–69
Wang C, Ren K, Lou W, Li J (2010) Toward publicly auditable secure cloud data storage sevices. IEEE Network 24:19–24
Wang Q, Wang C, Ren K, Lou W, Li J (2011) Enabling public auditability and data dynamics for storage security in cloud computing. IEEE Trans Parallel Distrib Syst 22:847–859
Wu Y, Jiang Z, Wang X et al (2017) Dynamic data operations with deduplication in privacy-preserving public auditing for secure cloud storage. IEEE Int Conf on Comput Sci Eng
Yuan J, Yu S (2015) Public integrity auditing for dynamic data sharing with multiuser modification. IEEE Trans Inf Forensics Secur 10:1717–1726
Zhu Y, Ahn G, Hu H et al (2013) Dynamic audit services for outsourced storages in clouds. In IEEE Trans. Services Computing 6:227–238
Lin Q, Li J, Huang Z et al (2018) A short linearly homomorphic proxy signature scheme. IEEE Access 6:12966–12972
Rabaninejad R, Attari MA, Asaar MR et al (2019) A lightweight auditing service for shared data with secure user revocation in cloud storage. in ieee transac serv comput early access. https://doi.org/10.1109/TSC.2019.2919627
Jues A, Kaliski J (2007) PoRs: Proofs of retrievability for large files. In CCS’2007, ACM. Alexandria, Virginiz, USA, 584–597
Erway C, Küpçü A, Papamanthou C, Tamassia R (2009) Dynamic provable data possession. ACM CCS, pp 213–222
Yu Y, Au M, Ateniese G et al (2017) Identity-based remote data integrity checking with perfect data privacy preserving for cloud storage. IEEE Trans Inf Forensics Secur 12:767–778
Shen J, Shen J, Huang X et al (2017) An efficient public auditing protocol with novel dynamic structure for cloud data. IEEE Trans Inf Forensics Secur 12:2402–2415
Merkle RC (1980) Protocols for public key cryptosystems. In IEEE Security and Privacy, pp 122–122
Kaswan A, Singh V, Jana PK (2018) A Multi-objective and pso based energy efficient path design for mobile sink in wireless sensor networks. Pervasive Mobile Computing 46:122–136
Wang T, Li Y, Wang G, Cao J, Bhuiyan M, Jia W (2017) Sustainable and efficient data collection from wsns to cloud. IEEE Trans Sustain Comput
Zhang X, Si W (2021) Efficient auditing scheme for secure data storage in fog-to-cloud computing. IEEE Access 9:37951–37960
Akinyele J et al (2013) Charm: A framework for rapidly prototyping cryptosystems. J Cryptogr Eng 3(2):111–128
Lynn B. The standard pairing based crypto library. In http://crypto.standford.edu/pbc
Acknowledgements
The authors would like to thank anonymous referees for their valuable suggestions and comments. This work is supported in part by National Natural Science Foundation of China (No. 61872284), in part by Project of Natural Science Research in Shaanxi (No. 2022JM365), and in part by Foundation of SKLOIS (No. 2021-MS-04).
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflicts of interest
We declare that we have no conflict of interest.
Rights and permissions
About this article
Cite this article
Chang, J., Xu, M. & Xue, R. Public auditing protocol with dynamic update and privacy-preserving properties in fog-to-cloud-based IoT applications. Peer-to-Peer Netw. Appl. 15, 2021–2036 (2022). https://doi.org/10.1007/s12083-022-01332-5
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s12083-022-01332-5