Abstract
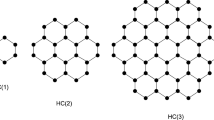
In this paper, for the unbalanced Feistel network which employs diffusion matrices in a switching way, we study the fixed number of its differential active S-boxes. Firstly we obtain some lower bounds of the differential active S-boxes for m, 2m and 3m rounds of Feistel structure, respectively. By concatenating these rounds, a fixed number of differential active S-boxes for arbitrary round number is derived. Our results imply that the unbalanced Feistel network using DSM is more secure than the traditional structure.
Similar content being viewed by others
References
Shahriar A Z M, Atiquzzaman M, Ivancic W. Network mobility in satellite networks: architecture and the protocol [J]. International Journal of Communication Systems, 2013, 26(2): 177–197.
Han Y L, Gui X L. Adaptive secure multicast in wireless networks [J]. International Journal of Communication Systems, 2009, 22(9): 1213–1239.
Al-Bayati A K S, Aloquili O M, Nabulsi J I A. Efficient use of DS/CDMA signals for broadband communications over power lines [J]. International Journal of Communication Systems, 2013, 26(2): 212–221.
Le A, Loo J, Lasebae A, et al. 6LoWPAN: a study on QoS security threats and countermeasures using intrusion detection system approach [J]. International Journal of Communication Systems, 2012, 25(9): 1189–1212.
National Bureau of Standards(NBS). Data Encryption Standard, FIPS PUB 46 [S]. Washington D C: National Bureau of Standards, 1977.
Kara O. Square reflection cryptanalysis of 5-round Feistel networks with permutations [J]. Information Processing Letters, 2013, 113(19–21): 827–831.
Bogdanov A. On unbalanced Feistel networks with contracting MDS diffusion [J]. Designs, Codes and Cryptography, 2011, 59(1–3): 35–58.
Hoang V T, Rogaway P. On Generalized Feistel Networks [C]// CRYPTO, LNCS 6223. Berlin: Springer-Verlag, 2010: 613–630.
Aoki K, Ichikawa T, Kanda M, et al. Camellia: A 128-bit block cipher suitable for multiple platforms-design and analysis[C]// 7th Annual International Workshop, SAC 2000. Berlin: Springer-Verlag, 2012: 39–56.
Schneier B. The blowfish encryption algorithm [J]. Dr Dobb’s Journal, 1994, 19(4): 38–40.
Schneier B, Kelsey J. Unbalanced Feistel networks and block cipher design [C]// Third International Workshop LNCS 1039. Berlin: Springer-Verlag, 1996: 121–144.
Adams C. CAST-256[EB/OL]. [2013-10-18]. http://www.nist.gov/aes.
Shirai T, Shibutani K, Akishita T, et al. The 128-bit block cipher CLEFIA [C]// Fast Software Encryption, LNCS 4593. Berlin: Springer-Verlag, 2007: 181–195.
Kanda M. Practical security evaluation against differential and linear cryptanalysis for Feistel ciphers with SPN round function [C]// 7th Annual International Workshop, SAC 2000. Berlin: Springer-Verlag, 2012: 324–338.
Author information
Authors and Affiliations
Corresponding author
Additional information
Foundation item: Supported by the National Natural Science Foundation of China (11204379) and Innovation Scientists and Technicians Troop Construction Projects of Henan Province(104100510025)
Biography: GUO Jiansheng, male, Professor, Ph.D., research direction: information systems, the theory of cryptography and quantum computation.
Rights and permissions
About this article
Cite this article
Guo, J., Hu, X. & Luo, W. Upper bounds of differential characteristic probability for unbalanced Feistel network employing DSM. Wuhan Univ. J. Nat. Sci. 19, 173–177 (2014). https://doi.org/10.1007/s11859-014-0997-1
Received:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11859-014-0997-1