Abstract
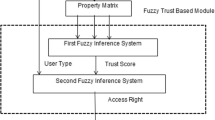
Authorization management is important precondition and foundation for coordinating and resource sharing in open networks. Recently, authorization based on trust is widely used whereby access rights to shared resource are granted on the basis of their trust relation in distributed environment. Nevertheless, dynamic change of the status of credential and chain of trust induces to uncertainty of trust relation. Considering uncertainty of authorization and analyzing deficiency of authorization model only based on trust, we proposes joint trust-risk evaluation and build the model based on fuzzy set theory, and make use of the membership grade of fuzzy set to express joint trust-risk relation. Finally, derivation principle and constraint principle of joint trust-risk relationships are presented. The authorization management model is defined based on joint trust-risk evaluation, proof of compliance and separation of duty are analyzed. The proposed model depicts not only trust relationship between principals, but also security problem of authorization.
Similar content being viewed by others
References
Blaze M, Feigenbaum J, Lacy J. Decentralized Trust Management[C]//Proceedings of the 17th Symposium on Security and Privacy. Okaland: IEEE Computer Society Press, 1996: 164–173.
Grandison T. Trust Management for Internet Applications[D]. London: Imperial College London, 2003.
Misztal B. Trust in Modern Societies[M]. Cambridge: Polity Press, 1996.
Beth T, Borcherding M, Klein B. Valuation of Trust in Open Networks[C]//Proceedings of the European Symposium on Research in Security (ESORICS). Berlin: Springer-Verlag, 1994: 3–18.
Tang W, Chen Z. Research of Subjective Trust Management Model Based on the Fuzzy Set Theory[J]. Journal of Software, 2003, 14(8):1401–1408(Ch).
Dimmock N, Belokosztolszki A, Eyers D. Using Trust and Risk in Role-Based Access Control Policies[C]//Proceedings of the Ninth ACM Symposium on Access Control Models and Technologies (SACMAT),New York, June, 2004: 156–162.
Sandhu R, Coyne E J, Feinstein H L,et al. Role-Based Access Control Models[J]. IEEE Computer, 1996, 29(2): 38–47.
Li Ninghui, Winsborough W H, Mitchell J C. Beyond Proof-of-Compliance: Safety and Availability Analysis in Trust Management[C]//Proceedings of IEEE Symposium on Security and Privacy. Oakland: IEEE Computer Society Press,2003: 123–139.
Li N H, Bizri Z, Tripunitara M V. On Mutually Exclusive Roles and Separation of Duty[C]//Proceedings of 2004 ACM Conference on Computer and Communications Security (CCS’04), Washington, October, 2004.
Zadeh L A. The Concept of a Linguistic Variable and Its Application to Approximate Reasoning[M]. New York: American Elsevier Publishing Company, 1973.
Author information
Authors and Affiliations
Corresponding author
Additional information
Foundation item: Supported by the National Natural Science Foundation of China (60403027)
Biography: YANG Qiuwei(1980–), male Ph.D. candidate, research direction: trust management and access control model.
Rights and permissions
About this article
Cite this article
Yang, Q., Wu, S., Hong, F. et al. Authorization management framework based on joint trust-risk evaluation. Wuhan Univ. J. of Nat. Sci. 12, 9–12 (2007). https://doi.org/10.1007/s11859-006-0129-7
Received:
Issue Date:
DOI: https://doi.org/10.1007/s11859-006-0129-7