Abstract
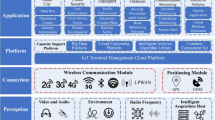
The upcoming fifth generation (5G) cellular network is required to provide seamless access for a massive number of Internet of Things (IoT) devices over the limited radio spectrum. In the context of massive spectrum sharing among heterogeneous IoT devices, wireless security becomes a critical issue owing to the broadcast nature of wireless channels. According to the characteristics of the cellular IoT network, physical layer security (PHY-security) is a feasible and effective way of realizing secure massive access. This article reviews the security issues in the cellular IoT network with an emphasis on revealing the corresponding challenges and opportunities for the design of secure massive access. Furthermore, we provide a survey on PHY-security techniques to improve the secrecy performance. Especially, we propose a secure massive access framework for the cellular IoT network by exploiting the inherent co-channel interferences. Finally, we discuss several potential research directions to further enhance the security of massive IoT.
Similar content being viewed by others
References
Zanella A, Bui N, Castellani A, et al. Internet of Things for smart cities. IEEE Internet Things J, 2014, 1: 22–32
Xu L D, He W, Li S. Internet of Things in industries: a survey. IEEE Trans Ind Inf, 2014, 10: 2233–2243
Zhang H B, Li J P, Wen B, et al. Connecting intelligent things in smart hospitals using NB-IoT. IEEE Internet Things J, 2018, 5: 1550–1560
Palattella M R, Dohler M, Grieco A, et al. Internet of Things in the 5G era: enablers, architecture, and business models. IEEE J Sel Areas Commun, 2016, 34: 510–527
Statista Research Department. Internet of Things (IoT) connected devices installed base worldwide from 2015 to 2025 (in billions). 2016. https://www.statista.com/statistics/471264/iot-number-of-connected-devices-worldwide
Chen X M. Massive Access for Cellular Internet of Things: Theory and Technique. Singapore: Springer, 2019
3GPP. Cellular System Support for Ultra-Low Complexity and Low Throughput Internet of Things (CIoT) (Release 13). Technical Report, TR 45.820 V13.1.0. Technical Specification Group GSM/EDGE Radio Access Network, 2015. https://portal.3gpp.org/desktopmodules/Specifications/SpecificationDetails.aspx?specificationId=2719
Han S J, Xu X D, Fang S S, et al. Energy efficient secure computation offloading in NOMA-based mMTC networks for IoT. IEEE Internet Things J, 2019, 6: 5674–5690
Zi R, Liu J, Gu L, et al. Enabling security and high energy efficiency in the Internet of Things with massive MIMO hybrid precoding. IEEE Internet of Things J, 2019, 6: 8615–8625
Khari M, Garg A K, Gandomi A H, et al. Securing data in Internet of Things (IoT) using cryptography and stegangraphy techniques. IEEE Trans Syst Man Cybernetics: Syst, 2019. doi: https://doi.org/10.1109/TSMC.2019.2903785
Liu Z, Seo H. IoT-NUMS: evaluating NUMS elliptic curve cryptography for IoT platforms. IEEE Trans Inform Forensic Secur, 2019, 14: 720–729
Yang N, Wang L F, Geraci G, et al. Safeguarding 5G wireless communication networks using physical layer security. IEEE Commun Mag, 2015, 53: 20–27
Mukherjee A. Physical-layer security in the Internet of Things: sensing and communication confidentiality under resource constraints. Proc IEEE, 2015, 103: 1747–1761
Gopala P K, Lai L, El Gamal H. On the secrecy capacity of fading channels. IEEE Trans Inform Theor, 2008, 54: 4687–4698
Chen X, Chen H H. Physical layer security in multi-cell MISO downlinks with incomplete CSI-A unified secrecy performance analysis. IEEE Trans Signal Process, 2014, 62: 6286–6297
Khisti A, Wornell G W. Secure transmission with multiple antennas I: the MISOME wiretap channel. IEEE Trans Inform Theor, 2010, 56: 3088–3104
Ji X S, Huang K Z, Jin L, et al. Overview of 5G security technology. Sci China Inf Sci, 2018, 61: 081301
Zhang J Q, Duong T Q, Woods R, et al. Securing wireless communications of the Internet of Things from the physical layer, an overview. Entropy, 2017, 19: 420
Shiu Y S, Chang S Y, Wu H C, et al. Physical layer security in wireless networks: a tutorial. IEEE Wirel Commun, 2011, 18: 66–74
Qi X H, Huang K Z, Li B, et al. Physical layer security in multi-antenna cognitive heterogeneous cellular networks: a unified secrecy performance analysis. Sci China Inf Sci, 2018, 61: 022310
Chen X M, Yin R. Performance analysis for physical layer security in multi-antenna downlink networks with limited CSI feedback. IEEE Wirel Commun Lett, 2013, 2: 503–506
Wang G, Lin Y, Meng C, et al. Secrecy energy efficiency optimization for AN-aided SWIPT system with power splitting receiver. Sci China Inf Sci, 2019, 62: 029301
Zou Y L, Zhu J, Wang X B, et al. A survey on wireless security: technical challenges, recent advances, and future trends. Proc IEEE, 2016, 104: 1727–1765
Chen X M, Lei L, Zhang H Z, et al. Large-scale MIMO relaying techniques for physical layer security: AF or DF? IEEE Trans Wirel Commun, 2015, 14: 5135–5146
Zhu J, Schober R, Bhargava V K. Secure transmission in multicell massive MIMO systems. IEEE Trans Wirel Commun, 2014, 13: 4766–4781
Mukherjee A, Fakoorian S A A, Huang J, et al. Principles of physical layer security in multiuser wireless networks: a survey. IEEE Commun Surv Tutorials, 2014, 16: 1550–1573
Chen X M, Ng D W K, Gerstacker W H, et al. A survey on multiple-antenna techniques for physical layer security. IEEE Commun Surv Tutorials, 2017, 19: 1027–1053
Chen X M, Zhong C J, Yuen C, et al. Multi-antenna relay aided wireless physical layer security. IEEE Commun Mag, 2015, 53: 40–46
Zhang Z Y, Wang X B, Zhang Y, et al. Grant-free rateless multiple access: a novel massive access scheme for Internet of Things. IEEE Commun Lett, 2016, 20: 2019–2022
Ding J, Qu D M, Jiang H, et al. Success probability of grant-free random access with massive MIMO. IEEE Internet Things J, 2019, 6: 506–516
Jeong B K, Shim B, Lee K B. MAP-based active user and data detection for massive machine-type communications. IEEE Trans Veh Technol, 2018, 67: 8481–8494
Shao X, Chen X, Jia R. Low-complexity design of massive device detection via Riemannian pursuit. In: Proceeding of IEEE Global Communications Conference (GLOBECOM), 2019. 1–6
Ahn J, Shim B, Lee K B. EP-based joint active user detection and channel estimation for massive machine-type communications. IEEE Trans Commun, 2019, 67: 5178–5189
Liu L, Yu W. Massive connectivity with massive MIMO-Part I: device activity detection and channel estimation. IEEE Trans Signal Process, 2018, 66: 2933–2946
Chen X M, Zhang Z Y, Zhong C J, et al. Fully non-orthogonal communication for massive access. IEEE Trans Commun, 2018, 66: 1717–1731
Wu Y P, Schober R, Ng D W K, et al. Secure massive MIMO transmission with an active eavesdropper. IEEE Trans Inform Theor, 2016, 62: 3880–3900
Chen J, Chen X M, Gerstacker W H, et al. Resource allocation for a massive MIMO relay aided secure communication. IEEE Trans Inform Forensic Secur, 2016, 11: 1700–1711
Li S, Li Q, Shao S H. Robust secrecy beamforming for full-duplex two-way relay networks under imperfect channel state information. Sci China Inf Sci, 2018, 61: 022307
Zhu F C, Gao F F, Lin H, et al. Robust beamforming for physical layer security in BDMA massive MIMO. IEEE J Sel Areas Commun, 2018, 36: 775–787
Li B, Fei Z S. Probabilistic-constrained robust secure transmission for energy harvesting over MISO channels. Sci China Inf Sci, 2018, 61: 022303
Qi Q, Chen X M. Wireless powered massive access for cellular Internet of Things with imperfect SIC and nonlinear EH. IEEE Internet Things J, 2019, 6: 3110–3120
Zhang S, Xu X M, Peng J H, et al. Physical layer security in massive internet of things: delay and security analysis. IET Commun, 2019, 34: 93–98
Seo H, Hong J P, Choi W. Low latency random access for sporadic MTC devices in Internet of Things. IEEE Internet Things J, 2019, 6: 5108–5118
Jiang N, Deng Y S, Nallanathan A, et al. Analyzing random access collisions in massive IoT networks. IEEE Trans Wirel Commun, 2018, 17: 6853–6870
Jia D, Fei Z S, Xiao M, et al. Enhanced frameless slotted ALOHA protocol with Markov chains analysis. Sci China Inf Sci, 2018, 61: 102304
Shao X D, Chen X M, Zhong C J, et al. A unified design of massive access for cellular Internet of Things. IEEE Internet Things J, 2019, 6: 3934–3947
Jiang T, Shi Y M, Zhang J, et al. Joint activity detection and channel estimation for IoT networks: phase transition and computation-estimation tradeoff. IEEE Internet Things J, 2019, 6: 6212–6225
Chen Z L, Sohrabi F, Yu W. Sparse activity detection for massive connectivity. IEEE Trans Signal Process, 2018, 66: 1890–1904
Li Y, Xia M H, Wu Y C. Activity detection for massive connectivity under frequency offsets via first-order algorithms. IEEE Trans Wirel Commun, 2019, 18: 1988–2002
Yu G, Chen X, Ng D W K. Low-cost design of massive access for cellular internet of things. IEEE Trans Commun, 2019, 67: 8008–8020
Chen X M, Jia R D. Exploiting rateless coding for massive access. IEEE Trans Veh Technol, 2018, 67: 11253–11257
Chen X M, Zhang Z Y, Zhong C J, et al. Exploiting multiple-antenna techniques for non-orthogonal multiple access. IEEE J Sel Areas Commun, 2017, 35: 2207–2220
Ding Z G, Lei X F, Karagiannidis G K, et al. A survey on non-orthogonal multiple access for 5G networks: research challenges and future trends. IEEE J Sel Areas Commun, 2017, 35: 2181–2195
Jia R D, Chen X M, Zhong C J, et al. Design of non-orthogonal beamspace multiple access for cellular Internet-of-Things. IEEE J Sel Top Signal Process, 2019, 13: 538–552
Moon S, Lee H S, Lee J W. SARA: sparse code multiple access-applied random access for IoT devices. IEEE Internet Things J, 2018, 5: 3160–3174
Jia M, Wang L F, Guo Q, et al. A low complexity detection algorithm for fixed up-link SCMA system in mission critical scenario. IEEE Internet Things J, 2018, 5: 3289–3297
Alnoman A, Erkucuk S, Anpalagan A. Sparse code multiple access-based edge computing for IoT systems. IEEE Internet of Things J, 2019, in press
Yang T H, Zhang R Q, Cheng X, et al. Secure massive MIMO under imperfect CSI: performance analysis and channel prediction. IEEE Trans Inform Forensic Secur, 2019, 14: 1610–1623
Chen X M, Ng D W K, Chen H H. Secrecy wireless information and power transfer: challenges and opportunities. IEEE Wirel Commun, 2016, 23: 54–61
Wang H M, Huang K W, Tsiftsis T A. Multiple antennas secure transmission under pilot spoofing and Jamming attack. IEEE J Sel Areas Commun, 2018, 36: 860–876
Wu Y, Wen C K, Chen W, et al. Data-aided secure massive MIMO transmission under th pilot contamination attack. IEEE Trans Commun, 2019, 67: 4765–4781
Jeong S, Lee K, Kang J. Cooperative jammer design in cellular network with internal eavesdroppers. In: Proceedings of IEEE Military Commun Conf (MILCOM), 2012. 1–5
Deng Z, Sang Q, Gao Y, et al. Optimal relay selection for wireless relay channel with external eavesdropper: a NN-based approach. In: Proceedings of IEEE/CIC intern Conf Commun (ICCC), 2018. 515–519
Deng H, Wang H M, Yuan J H, et al. Secure communication in uplink transmissions: user selection and multiuser secrecy gain. IEEE Trans Commun, 2016, 64: 3492–3506
Wang H M, Yang Q, Ding Z G, et al. Secure short-packet communications for mission-critical IoT applications. IEEE Trans Wirel Commun, 2019, 18: 2565–2578
Mokari N, Parsaeefard S, Saeedi H, et al. Secure robust ergodic uplink resource allocation in relay-assisted cognitive radio networks. IEEE Trans Signal Process, 2015, 63: 291–304
Chen X M, Zhang Y. Mode selection in MU-MIMO downlink networks: a physical-layer security perspective. IEEE Syst J, 2017, 11: 1128–1136
Chen X M, Jia R D, Ng D W K. On the design of massive non-orthogonal multiple access with imperfect successive interference cancellation. IEEE Trans Commun, 2019, 67: 2539–2551
Chen X M, Zhang Z Y, Zhong C J, et al. Exploiting inter-user interference for secure massive non-orthogonal multiple access. IEEE J Sel Areas Commun, 2018, 36: 788–801
Zhang Y Y, Shen Y L, Wang H, et al. On secure wireless communications for IoT under eavesdropper collusion. IEEE Trans Automat Sci Eng, 2016, 13: 1281–1293
Liu L, Larsson E G, Yu W, et al. Sparse signal processing for grant-free massive connectivity: a future paradigm for random access protocols in the Internet of Things. IEEE Signal Process Mag, 2018, 35: 88–99
Shao X D, Chen X M, Zhong C J, et al. Protocol design and analysis for cellular internet of things with massive access. In: Proceedings of IEEE International Conference on Communications (ICC), 2019. 1–6
Wang J, Zhang Z Y, Hanzo L. Joint active user detection and channel estimation in massive access systems exploiting reed-muller sequences. IEEE J Sel Top Signal Process, 2019, 13: 739–752
Kapetanovic D, Zheng G, Rusek F. Physical layer security for massive MIMO: an overview on passive eavesdropping and active attacks. IEEE Commun Mag, 2015, 53: 21–27
Lu L, Li G Y, Swindlehurst A L, et al. An overview of massive MIMO: benefits and challenges. IEEE J Sel Top Signal Process, 2014, 8: 742–758
Chen X M, Yuen C, Zhang Z Y. Exploiting large-scale MIMO techniques for physical layer security with imperfect channel state information. In: Proceedings of IEEE Global Communication Conference (GLOBECOM), 2014. 1–6
Xu C, Zeng P, Liang W, et al. Secure resource allocation for green and cognitive device-to-device communication. Sci China Inf Sci, 2018, 61: 029305
Hu J W, Yang N, Cai Y M. Secure downlink transmission in the Internet of Things: how many antennas are needed? IEEE J Sel Areas Commun, 2018, 36: 1622–1634
Li T Q, Ai Z Y, Ji W Z. Primate stem cells: bridge the translation from basic research to clinic application. Sci China Life Sci, 2019, 62: 12–21
Liu T Q, Han S, Meng W X, et al. Dynamic power allocation scheme with clustering based on physical layer security. IET Commun, 2018, 6: 2546–2551
Acknowledgements
This work was supported by National Natural Science Foundation of China (Grant Nos. 61871344, 61922071, U1709219, 61725104), National Science and Technology Major Project of China (Grant No. 2018ZX03001017-002), and National Key R&D Program of China (Grant No. 2018YFB1801104).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Qi, Q., Chen, X., Zhong, C. et al. Physical layer security for massive access in cellular Internet of Things. Sci. China Inf. Sci. 63, 121301 (2020). https://doi.org/10.1007/s11432-019-2650-4
Received:
Revised:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11432-019-2650-4