Abstract
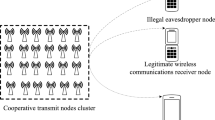
The issue of physical layer security of the wireless single-input multiple-output (SIMO) system is addressed in this paper. We propose a two-step transmission scheme with artificial noise to improve the security and the scheme does not require the channel state information of the eavesdropper. In the first step, the destination which has multiple antennas generates a random reference symbol and artificial noise and transmits them in the direction of the source and its orthogonal space, respectively. The reference symbol is received by the source without being polluted by the artificial noise, while it is jammed by the artificial noise for the eavesdropper. In the second step, the symbol of the source is multiplied by the received reference symbol and then transmitted. Finally, the destination can directly estimate the symbol of the source using the reference symbol. However, the eavesdropper needs to additionally estimate the reference symbol for demodulating the symbol of the source, which usually obtains an inaccurate result due to the artificial noise. The information-theoretic security of our scheme is analyzed and a lower bound of the achievable secrecy rate is derived. The performance of the new scheme is compared with that of the traditional approach under different input signals through numerical simulations. The results show that the proposed scheme outperforms the traditional SIMO approach especially in the high SNR region.
Similar content being viewed by others
References
Wyner A D. The wire-tap channel. Bell Syst Tech J, 1975, 54: 1355–1387
Csiszár I, Körner J. Broadcast channels with confidential messages. IEEE Trans Inf Theory, 1978, 24: 339–348.
Leung-Yan-Cheong S, Hellman M. The Gaussian wire-tap channel. IEEE Trans Inf Theory, 1978, 24: 451–456
Bloch M, Barros J, Rodrigues M R D, et al. Wireless information-theoretic security. IEEE Trans Inf Theory, 2008, 54: 2515–2534
Gopala P K, Lai L, El Gamal H. On the secrecy capacity of fading channels. IEEE Trans Inf Theory, 2008, 54: 4687–4698
Hero III A O. Secure space-time communication. IEEE Trans Inf Theory, 2003, 49: 3235–3249
Parada P, Blahut R. Secrecy capacity of SIMO and slow fading channels. In: Proceedings of IEEE ISIT 2005, Adelaide, 2005. 2152–2155
Goel S, Negi R. Guaranteeing secrecy using artificial noise. IEEE Trans Wirel Commun, 2008, 7: 2180–2189
Khisti A, Wornell G W. Secure transmission with multiple antennas I: the MISOME wiretap channel. IEEE Trans Inf Theory, 2010, 56: 3088–3104
Khisti A, Wornell G W. Secure transmission with multiple antennas II: the MIMOME wiretap channel. IEEE Trans Inf Theory, 2010, 56: 5515–5532
Oggier F, Hassibi B. The secrecy capacity of the MIMO wiretap channel. IEEE Trans Inf Theory, 2011, 57: 4961–4972
Li X, Hwu J, Ratazzi E P. Array redundancy and diversity for wireless transmissions with low probability of interception. In: Proceedings of 40th IEEE International Conference on Acoustics, Speech and Signal Processing, Toulouse, 2006. IV
Fei Z S, Ni J Q, Zhao D, et al. Ergodic secrecy rate of two-user MISO interference channels with statistical CSI. Sci China Inf Sci, 2014, 57: 102302
Wang C, Wang H M. On the secrecy throughput maximization for MISO cognitive radio network in slow fading channels. IEEE Trans Inf Forensics Secur, 2014, 9: 1814–1827
Wang H M, Yin Q, Xia X G. Distributed beamforming for physical-layer security of two-way relay networks. IEEE Trans Signal Process, 2012, 61: 3532–3545
Wang H M, Luo M, Xia X G, et al. Joint cooperative beamforming and jamming to secure AF relay systems with individual power constraint and no eavesdropper’s CSI. IEEE Signal Process Lett, 2013, 20: 39–42
Wang H M, Luo M, Yin Q, et al. Hybrid cooperative beamforming and jamming for physical-layer security of two-way relay networks. IEEE Trans Inf Forensics Secur, 2013, 8: 2007–2020
Mu P, Wang H M, Yin Q. Improving the secrecy rate of wireless SIMO systems via two-step transmission. In: Proceedings of IEEE GLOBECOM 2013 Workshops, Atlanta, 2013. 1280–1285
Rodrigues M R D, Somekh-Baruch A, Bloch M. On Gaussian wiretap channels with M-PAM inputs. In: Proceedings of IEEE European Wireless Conference, Lucca, 2010. 774–781
Hjørungnes A. Complex-Valued Matrix Derivatives. Cambridge: Cambridge University Press, 2011
Xiao C, Zheng Y R. On the mutual information and power allocation for vector Gaussian channels with finite discrete inputs. In: Proceedings of IEEE GLOBECOM, New Orleans, 2008. 1–5
Geist J M. Capacity and cutoff rate for dense M-ary PSK constellations. In: Proceedings of Military Communications Conference, Monterey, 1990. 768–770
Cover T M, Thomas J A. Elements of Information Theory. Hoboken: John Wiley & Sons, Inc., 2006
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Wang, B., Mu, P., Yang, P. et al. Two-step transmission with artificial noise for secure wireless SIMO communications. Sci. China Inf. Sci. 58, 1–13 (2015). https://doi.org/10.1007/s11432-014-5256-8
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11432-014-5256-8