Abstract
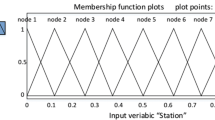
Energy efficiency playsa major role in designing a sensor network to improve network lifetime. Trust is also important for providing security to the data communication process. Delay is also a major challenge today due to the enormous volume of network users. To overcome all these issues, many researchers have developed energy-efficient security mechanisms for fulfilling the requirements. Even though they are not able to satisfy the current requirements and users in terms of energy consumption, delay, and security. For this purpose, this paper proposes a new algorithm called Fuzzy Trust-Based Energy-Aware Balanced Secure Routing Algorithm, which can provide the effective delay constrained secure routing. It uses fuzzy logic as a form of many-valued logic. In this method, the truth values of variables may be any real number between 0 and 1, both inclusive for making a final decision over sensor nodes. Considering the number of hops between the source and destination nodes, the energy level of the nodes, the trust scores. Moreover, a new trust model has introduced a new formula for calculating trust scores with the energy level of the communication delay, which is calculated by using the number of hops used for the specific communication, taking into account the number of hops between the source and destination nodes. The experimental results of the proposed secured routing algorithm demonstrated that the performance in terms of energy consumption, less delay, and high throughput with security is better when compared to the existing systems.






Similar content being viewed by others
References
Younis, O., & Fahmy, S. (2004). HEED: a hybrid, energy-efficient, distributed clustering approach for ad hoc sensor networks. In IEEE Transactions on Mobile Computing, 3(4), 366–379. https://doi.org/10.1109/TMC.2004.41.
Qin, D., Yang, S., Jia S., Zhang, Y., Ma, J., & Ding, Q. (2017). Research on trust sensing based secure routing mechanism for wireless sensor network. In IEEE Access, 5, 9599–9609. https://doi.org/10.1109/ACCESS.2017.2706973.
Huynh, T.-T., Dinh-Duc, A.-V., & Tran C.-H. (2016). Delay-constrained energy-efficient cluster-based multi-hop routing in wireless sensor networks. In Journal of Communications and Networks, 18(4), 580–588. https://doi.org/10.1109/JCN.2016.000081.
Logambigai, R., Ganapathy, S., & Kannan A. (2018).Energy–efficient grid–based routing algorithm using intelligent fuzzy rules for wireless sensor networks. Computers & Electrical Engineering, 68, 62–75. https://doi.org/10.1016/j.compeleceng.2018.03.036.
Heinzelman, W. B., Chandrakasan, A. P., & Balakrishnan, H. (2002). An application-specific protocol architecture for wireless microsensor networks. In IEEE Transactions on Wireless Communications, 1(4), 660–670. https://doi.org/10.1109/TWC.2002.804190.
El Assaf, A., Zaidi, S., Affes, S., & Kandil, N. (2016). Low-cost localization for multihop heterogeneous wireless sensor networks. In IEEE Transactions on Wireless Communications, 15(1), 472–484. https://doi.org/10.1109/TWC.2015.2475255.
Rathore, H., Badarla, V., & Shit, S. (2016). Consensus-aware sociopsychological trust model for wireless sensor networks. ACM Transactions on Sensor Networks, 12(3), 1–27. https://doi.org/10.1145/2903721.
Chen, L., Xiong, X., Chen, Y., Liu, K., Zhang, J., Jiang, Y., & Luo, Q. (2014). Why (n + 1)th-hop neighbours are more important than nth-hop ones for localisation in multi-hop WSNs, Electronics Letters, 50(22), 1646–1648. https://doi.org/10.1049/el.2014.2969.
Ahmed, A., Bakar, K. A., Channa, M. I., Haseeb, K., & Khan, A. W. (2015). TERP: A trust and energy aware routing protocol for wireless sensor network. IEEE Sensors Journal, 15(12), 6962–6972. https://doi.org/10.1109/JSEN.2015.2468576.
Le, T. N., Pegatoquet, A., Berder, O., & Sentieys, O. (2015). Energy-efficient power manager and MAC protocol for multi-hop wireless sensor networks powered by periodic energy harvesting sources. In IEEE Sensors Journal, 15(12), 7208–7220. https://doi.org/10.1109/JSEN.2015.2472566.
Zaidi, S., El Assaf, A., Affes, S., & Kandil, N. (2016). Accurate range-free localization in multi-hop wireless sensor networks. In IEEE Transactions on Communications, 64(9), 3886–3900. https://doi.org/10.1109/TCOMM.2016.2590436.
Ganapathy, S., Yogesh, P., Kannan, A. (2012). Intelligent agent-based intrusion detection system using enhanced multiclass SVM. Computational Intelligence and Neuroscience, 2012(9), 1–9. https://doi.org/10.1155/2012/850259.
Muthurajkumar, S., Ganapathy, S., Vijayalakshmi, M., & Kannan, A. (2017). An intelligent secured and energy efficient routing algorithm for MANETs. Wireless Personal Communications, 96(2), 1753–1769. https://doi.org/10.1007/s11277-017-4266-4.
Selvi, M., Velvizhy, P., Ganapathy, S., Nehemiah, H. K., & Kannan, A. (2017). A rule based delay constrained energy efficient routing technique for wireless sensor networks. Cluster Computing, 22(12), 1–10. https://doi.org/10.1007/s10586-017-1191-y.
Gao, X., Zhu, X., Li, J., Wu, F., Chen, G., Du, D. Z., & Tang, S. (2017). A novel approximation for multi-hop connected clustering problem in wireless networks. In IEEE/ACM Transactions on Networking, 25(4), 2223–2234. https://doi.org/10.1109/TNET.2017.2690359.
Thangaramya, K., Logambigai, R., SaiRamesh, L., Kulothungan, K., Kannan, A., Ganapathy, S. An energy efficient clustering approach using spectral graph theory in wireless sensor networks. 2017 Second International Conference on Recent Trends and Challenges in Computational Models (ICRTCCM), 2017, 126–129. https://doi.org/10.1109/ICRTCCM.2017.41.
Sun, B., & Li, D. (2018). A comprehensive trust-aware routing protocol with multi-attributes for WSNs. In IEEE Access, 6, 4725–4741. https://doi.org/10.1109/ACCESS.2017.2786944.
Singh, M., Sardar, A. R., Majumder, K., & Sarkar, S. K. (2017). A lightweight trust mechanism and overhead analysis for clustered WSN. IETE Journal of Research, 63(3), 297–308. https://doi.org/10.1080/03772063.2017.1284613.
Liu, X., Xiong, N., Zhang, N., Liu, A., Shen, H., & Huang, C. (2018). A trust with abstract information verified routing scheme for cyber-physical network. In IEEE Access, 6, 3882–3898. https://doi.org/10.1109/ACCESS.2018.2799681.
Asuquo, P., Cruickshank, H., AnyigorOgah, C. P., Lei, Ao., & Sun, Z. (2018). A distributed trust management scheme for data forwarding in satellite DTN emergency communications. In IEEE Journal on Selected Areas in Communications, 36(2), 246–256. https://doi.org/10.1109/JSAC.2018.2804098.
Kuo, Y.-W., Li, C.-L., Jhang, J.-H., & Lin, S. (2018). Design of a wireless sensor network-based IoT platform for wide area and heterogeneous applications. In IEEE Sensors Journal, 18(12), 5187–5197. https://doi.org/10.1109/JSEN.2018.2832664.
Li, Y., & Liang, Y. (2018). Compressed sensing in multi-hop large-scale wireless sensor networks based on routing topology tomography. In IEEE Access, 6, 27637–27650. https://doi.org/10.1109/ACCESS.2018.2834550.
Firoozi, F., Zadorozhny, V. I., & Li, F. Y. (2018). Subjective logic-based in-network data processing for trust management in collocated and distributed wireless sensor networks. In IEEE Sensors Journal, 18(15), 6446–6460. https://doi.org/10.1109/JSEN.2018.2848205.
Lambor, S. M., & Joshi, S. M. (2018). Optimal hops for minimal route power under SINR constraints in wireless sensor networks. IET Wireless Sensor Systems, 8(4), 176–182. https://doi.org/10.1049/iet-wss.2017.0078.
Lyu, Z., Wei, Z., Pan, J., Chen, H., Xia, C., Han, J., & Shi, L. (2019). Periodic charging planning for a mobile WCE in wireless rechargeable sensor networks based on hybrid PSO and GA algorithm. Applied Soft Computing Journal, 75, 388–403, https://doi.org/10.1016/j.asoc.2018.11.022.
Daiya, V., Ebenezer, J., & Jehadeesan, R. (2021). Mapping obfuscation-based PHY security scheme for resource-constrained wireless sensor network. IETE Technical Review, 38(2), 221–230. https://doi.org/10.1080/02564602.2019.1709573.
Chen, Z., He, M., Liang, W., & Chen, K. (2015). Trust-aware and low energy consumption security topology protocol of wireless aensor network. Journal of Sensors, 2015, 1–10. https://doi.org/10.1155/2015/716468.
Kim, J., Jang, K. Y., Choo, H., Kim, W. (2007). Energy efficient LEACH with TCP for wireless sensor networks. Computational Science & its Applications- ICCSA, 2007, 275–285, https://doi.org/10.1007/978-3-540-74477-1_27.
Weichao, W., Fei, D., Qijian, X. (2009). An improvement of LEACH routing protocol based on trust for wireless sensor networks. 2009 5th International Conference on Wireless Communications, Networking and Mobile Computing, 2009, 1–4. https://doi.org/10.1109/WICOM.2009.5303346.
Miglani, A., Bhatia, T., Goel, S. (2015). TRUST based energy efficient routing in LEACH for wireless sensor network. 2015 Global Conference on Communication Technologies (GCCT), 2015, 361–365. https://doi.org/10.1109/GCCT.2015.7342684.
Funding
The authors have not disclosed any funding.
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of interest
The authors have not disclosed any competing interests.
Data availability
Enquiries about data availability should be directed to the authors.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Anitha, R., Bapu, B.R.T., Kuppusamy, P.G. et al. FEBSRA: Fuzzy Trust Based Energy Aware Balanced Secure Routing Algorithm for Secured Communications in WSNs. Wireless Pers Commun 125, 63–86 (2022). https://doi.org/10.1007/s11277-022-09541-0
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11277-022-09541-0