Abstract
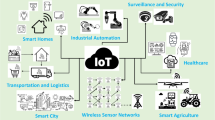
Wireless Sensor Networks (WSNs) are used to collect and transmitted the data in various applications from normal to those which requires significant security issues. Only legitimate users can get access to the data a secure and efficient user authentication scheme is required. As a part of this study, we analyze three recently proposed user authentication and session key establishment schemes for WSNs and shows their weaknesses. To remove the weaknesses of these schemes, we propose an improved user authentication and session key agreement scheme using keyed fuzzy extractors and Chebyshev chaotic maps. We use Burrows-Abadi-Needham logic analysis to exhibit that the proposed scheme ensures mutual authentication and establishes a session key between user and sensor node. We also use scyther tool to exhibit that the designed scheme offers all scurity features and resist all known attacks. The performance comparison exhibits that the proposed scheme is robust and efficient than other concerned schemes.




Similar content being viewed by others
References
Akyildiz, I. F., Su, W., Sankarasubramaniam, Y., & Cayirci, E. (2002). Wireless sensor networks: A survey. Computer Networks, 38(4), 393–422.
Alotaibi, M. (2018). An enhanced symmetric cryptosystem and biometric-based anonymous user authentication and session key establishment scheme for wsn. IEEE Access, 6, 70072–70087.
Amin, R., & Biswas, G. (2016). A secure light weight scheme for user authentication and key agreement in multi-gateway based wireless sensor networks. Ad Hoc Networks, 36, 58–80.
Amin, R., Islam, S. H., Kumar, N., & Choo, K. K. R. (2018). An untraceable and anonymous password authentication protocol for heterogeneous wireless sensor networks. Journal of Network and Computer Applications, 104, 133–144.
Benenson, Z., Gärtner, F. C., Kesdogan, D. (2004). User authentication in sensor networks. In GI Jahrestagung (2), Citeseer, pp 385–389.
Benenson, Z., Gedicke, N., & Raivio, O. (2005). Realizing robust user authentication in sensor networks. Real-World Wireless Sensor Networks (REALWSN), 14, 52.
Burrows, M., Abadi, M., & Needham, R. M. (1989). A logic of authentication. Proceedings of the Royal Society of London A Mathematical and Physical Sciences, 426(1871), 233–271.
Canetti, R., & Krawczyk, H. (2001). Analysis of key-exchange protocols and their use for building secure channels. In International Conference on the Theory and Applications of Cryptographic Techniques, Springer, pp 453–474.
Chang, C. C., & Le, H. D. (2015). A provably secure, efficient, and flexible authentication scheme for ad hoc wireless sensor networks. IEEE Transactions on Wireless Communications, 15(1), 357–366.
Cremers, C. (2014). Scyther user manual-draft february, 18, 2014.
Das, A. K. (2016). A secure and robust temporal credential-based three-factor user authentication scheme for wireless sensor networks. Peer-to-peer Networking and Applications, 9(1), 223–244.
Das, A. K., Sharma, P., Chatterjee, S., & Sing, J. K. (2012). A dynamic password-based user authentication scheme for hierarchical wireless sensor networks. Journal of Network and Computer Applications, 35(5), 1646–1656.
Das, A. K., Kumari, S., Odelu, V., Li, X., Wu, F., & Huang, X. (2016). Provably secure user authentication and key agreement scheme for wireless sensor networks. Security and Communication Networks, 9(16), 3670–3687.
Das, M. L. (2009). Two-factor user authentication in wireless sensor networks. IEEE Transactions on Wireless Communications, 8(3), 1086–1090.
Dodis, Y., Kanukurthi, B., Katz, J., Reyzin, L., & Smith, A. (2012). Robust fuzzy extractors and authenticated key agreement from close secrets. IEEE Transactions on Information Theory, 58(9), 6207–6222.
Fan, R., Dj, He., Xz, Pan, et al. (2011). An efficient and dos-resistant user authentication scheme for two-tiered wireless sensor networks. Journal of Zhejiang University SCIENCE C, 12(7), 550–560.
Farash, M. S., Turkanović, M., Kumari, S., & Hölbl, M. (2016). An efficient user authentication and key agreement scheme for heterogeneous wireless sensor network tailored for the internet of things environment. Ad Hoc Networks, 36, 152–176.
He, D., Gao, Y., Chan, S., Chen, C., & Bu, J. (2010). An enhanced two-factor user authentication scheme in wireless sensor networks. Ad hoc & Sensor Wireless Networks, 10(4), 361–371.
He, J., Yang, Z., Zhang, J., Liu, W., & Liu, C. (2018). On the security of a provably secure, efficient, and flexible authentication scheme for ad hoc wireless sensor networks. International Journal of Distributed Sensor Networks, 14(1), 1550147718756311.
Jiang, Q., Ma, J., Lu, X., & Tian, Y. (2015). An efficient two-factor user authentication scheme with unlinkability for wireless sensor networks. Peer-to-peer Networking and Applications, 8(6), 1070–1081.
Jung, J., Kim, J., Choi, Y., & Won, D. (2016). An anonymous user authentication and key agreement scheme based on a symmetric cryptosystem in wireless sensor networks. Sensors, 16(8), 1299.
Kalra, S., & Sood, S. K. (2015). Advanced password based authentication scheme for wireless sensor networks. Journal of Information Security and Applications, 20, 37–46.
Khan, M. K., & Alghathbar, K. (2010). Cryptanalysis and security improvements of two-factor user authentication in wireless sensor networks. Sensors, 10(3), 2450–2459.
Ko, L. C. (2008). A novel dynamic user authentication scheme for wireless sensor networks. In 2008 IEEE International Symposium on Wireless Communication Systems, IEEE, pp 608–612.
Kocher, P., Jaffe, J., & Jun, B. (1999). Differential power analysis. In Annual International Cryptology Conference, Springer, pp 388–397.
Kumar, P., & Lee, H. J. (2011). Cryptanalysis on two user authentication protocols using smart card for wireless sensor networks. In 2011 Wireless Advanced, IEEE, pp 241–245.
Kumari, S., & Renuka, K. (2020). A provably secure biometrics and ecc-based authentication and key agreement scheme for wsns. International Journal of Communication Systems, 33(3), e4194.
Kumari, S., Li, X., Wu, F., Das, A. K., Arshad, H., & Khan, M. K. (2016). A user friendly mutual authentication and key agreement scheme for wireless sensor networks using chaotic maps. Future Generation Computer Systems, 63, 56–75.
Li, C. T., Weng, C. Y., & Lee, C. C. (2013). An advanced temporal credential-based security scheme with mutual authentication and key agreement for wireless sensor networks. Sensors, 13(8), 9589–9603.
Li, W., Li, B., Zhao, Y., Wang, P., & Wei, F. (2018). Cryptanalysis and security enhancement of three authentication schemes in wireless sensor networks. Wireless Communications and Mobile Computing 2018.
Li, X., Niu, J., Bhuiyan, M. Z. A., Wu, F., Karuppiah, M., & Kumari, S. (2017). A robust ecc-based provable secure authentication protocol with privacy preserving for industrial internet of things. IEEE Transactions on Industrial Informatics, 14(8), 3599–3609.
Li, X., Niu, J., Kumari, S., Wu, F., Sangaiah, A. K., & Choo, K. K. R. (2018). A three-factor anonymous authentication scheme for wireless sensor networks in internet of things environments. Journal of Network and Computer Applications, 103, 194–204.
Maitra, T., Amin, R., Giri, D., & Srivastava, P. (2016). An efficient and robust user authentication scheme for hierarchical wireless sensor networks without tamper-proof smart card. IJ Network Security, 18(3), 553–564.
Mason, J. C., & Handscomb, D. C. (2002). Chebyshev polynomials. Chapman and Hall/CRC.
Mnif, A., Cheikhrouhou, O., & Jemaa, M. B. (2011). An id-based user authentication scheme for wireless sensor networks using ecc. In ICM 2011 Proceeding, IEEE, pp 1–9.
Nyang, D., & Lee, M. K. (2009). Improvement of dass two-factor authentication protocol in wireless sensor networks. IACR Cryptology ePrint Archive, 2009, 631.
Roy, S., Chatterjee, S., Das, A. K., Chattopadhyay, S., Kumari, S., & Jo, M. (2017). Chaotic map-based anonymous user authentication scheme with user biometrics and fuzzy extractor for crowdsourcing internet of things. IEEE Internet of Things Journal, 5(4), 2884–2895.
Santos-González, I., Rivero-García, A., Burmester, M., Munilla, J., & Caballero-Gil, P. (2020). Secure lightweight password authenticated key exchange for heterogeneous wireless sensor networks. Information Systems, 88, 101423.
Singh, A., Awasthi, A. K., & Singh, K. (2017). Cryptanalysis and improvement in user authentication and key agreement scheme for wireless sensor network. Wireless Personal Communications, 94(3), 1881–1898.
Srinivas, J., Das, A. K., Wazid, M., & Kumar, N. (2018). Anonymous lightweight chaotic map-based authenticated key agreement protocol for industrial internet of things. IEEE Transactions on Dependable and Secure Computing
Tseng, H. R., Jan, R. H., & Yang, W. (2007). An improved dynamic user authentication scheme for wireless sensor networks. In IEEE GLOBECOM 2007-IEEE Global Telecommunications Conference, IEEE, pp 986–990.
Turkanovic, M., & Holbl, M. (2013). An improved dynamic password-based user authentication scheme for hierarchical wireless sensor networks. Elektronika ir Elektrotechnika, 19(6), 109–116.
Turkanović, M., Brumen, B., & Hölbl, M. (2014). A novel user authentication and key agreement scheme for heterogeneous ad hoc wireless sensor networks, based on the internet of things notion. Ad Hoc Networks, 20, 96–112.
Vaidya, B., Makrakis, D., & Mouftah, H. T. (2010). Improved two-factor user authentication in wireless sensor networks. 2010 IEEE 6th International Conference on Wireless and Mobile Computing (pp. 600–606). IEEE: Networking and Communications.
Vaidya, B., Rodrigues, J. J., & Park, J. H. (2010). User authentication schemes with pseudonymity for ubiquitous sensor network in ngn. International Journal of Communication Systems, 23(9–10), 1201–1222.
Wang, D., & Wang, P. (2014). On the anonymity of two-factor authentication schemes for wireless sensor networks: Attacks, principle and solutions. Computer Networks, 73, 41–57.
Wang, D., & Wang, P. (2014). Understanding security failures of two-factor authentication schemes for real-time applications in hierarchical wireless sensor networks. Ad Hoc Networks, 20, 1–15.
Wang, D., Wang, P., & Wang, C. (2020). Efficient multi-factor user authentication protocol with forward secrecy for real-time data access in wsns. ACM Transactions on Cyber-Physical Systems, 4(3), 1–26.
Wong, K. H., Zheng, Y., Cao, J., & Wang, S. (2006). A dynamic user authentication scheme for wireless sensor networks. In IEEE International Conference on Sensor Networks, Ubiquitous, and Trustworthy Computing (SUTC’06), IEEE, vol 1, pp 8–pp.
Xiong, L., Peng, D., Peng, T., Liang, H., & Liu, Z. (2017). A lightweight anonymous authentication protocol with perfect forward secrecy for wireless sensor networks. Sensors, 17(11), 2681.
Xue, K., Ma, C., Hong, P., & Ding, R. (2013). A temporal-credential-based mutual authentication and key agreement scheme for wireless sensor networks. Journal of Network and Computer Applications, 36(1), 316–323.
Yoo, S. G., Park, K. Y., & Kim, J. (2012). A security-performance-balanced user authentication scheme for wireless sensor networks. International Journal of Distributed Sensor Networks, 8(3), 382810.
Yuan, J., Jiang, C., & Jiang, Z. (2010). A biometric-based user authentication for wireless sensor networks. Wuhan University Journal of Natural Sciences, 15(3), 272–276.
Yuan, J. J. (2014). An enhanced two-factor user authentication in wireless sensor networks. Telecommunication Systems, 55(1), 105–113.
Acknowledgements
On behalf of all the co-authors, I confirm that the manuscript is the authors’ original work and the manuscript has not received prior publication and is not under consideration for publication elsewhere.
Funding
This work not received any external funding.
Author information
Authors and Affiliations
Contributions
Gaurav analyzed three recently proposed schemes, proposed an enhanced scheme and then gave it’s formal and informal security analysis; conceptualization and supervision is by Rahul Kumar.
Corresponding author
Ethics declarations
Conflict of interest
The authors declare that they have no conflict of interest.
Availability of data and material
The data and material used to support the findings of this study are included within the article.
Code availability
The code of formal security proof using scyther tool of the proposed scheme is included within the article.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Tyagi, G., Kumar, R. An Improved Multifactor User Authentication Scheme for Wireless Sensor Networks. Wireless Pers Commun 123, 1311–1343 (2022). https://doi.org/10.1007/s11277-021-09182-9
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11277-021-09182-9