Abstract
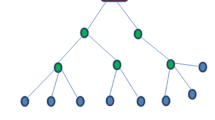
Wireless sensor networks are randomly deployed and responsible for monitoring geographical area wide. In WSN, the aggregation of data is very complex because of its limited power and computing capabilities. Issue in data aggregation is that the data may be passed on malicious node. All the existing data aggregation techniques undergo security issues because of the transfer of large amount of data. In this paper we propose a protocol named Secure Data Aggregation Protocol (SDAP) which identifies the malicious node by providing a logical group in the form of tree topology. In the tree topology the aggregation is formed by aggregating the nodes, which are non-leaf node and high level of trust is required to provide a better approximation and accuracy against the security threats. Thus the data is securely aggregated and the efficiency is achieved in data aggregation.










Similar content being viewed by others
References
Hu, L., & Evans, D. (2003 Jan 23). Secure aggregation for wireless networks. Proceedings of Workshop on Security and Assurance in Ad hoc Networks, Orlando, FL.
Przydatek, B., Song, D. & Perrig, A. (2003). SIA: Secure information aggregation in sensor networks. Proceedings of SenSys’ 03, Nov 5–7, Los Angeles, CA.
Cam, H., Ozdemir, S., Nair, P., & Muthuavinashiappan, D. (2003). ESPDA: Energy-efficient and secure pattern based data aggregation for wireless sensor networks. Proceedings of IEEE sensors,2, 732–736.
Ozdemir, S., Ozgur Sanli, H., & Cam, H. (2004 Sep). SRDA: Secure reference-based data aggregation protocol for wireless sensor networks. In IEEE 60th conference on vehicular technology, VTC2004-Fall, Vol. 7, pp. 26–29, pp. 4650–4654.
Yang, Y., Wang, X., Zhu, S., & Cao, G. (2006). SDAP: A secure hop-by-hop data aggregation protocol for sensor networks. In Proceedings of the 7th ACM international symposium on mobile ad hoc networking and computing (MobiHoc ’06), pp. 356–367.
Othman, S. B., Trad, A., Youssef, H. & Alzaid, H. (2013). Secure data aggregation with MAC authentication in wireless sensor networks. 12th IEEE international conference on trust, security and privacy in computing and communications, ISSN: 2324–898X, pp 188–195.
Rivest, R., Adleman, L., & Dertouzos, M. (1978). On data banks and privacy homomorphisms. Foundations of Secure Computation,4, 169–179.
Girao, J., Schneider, M., & Westhoff, D. (2005). CDA: Concealed data aggregation in wireless sensor networks. IEEE International Conference on Communications,5, 3044–3049.
Wagner, D. (2004). Resilient aggregation in sensor networks. In Proceedings of the 2nd ACM Workshop on Security of Ad-hoc and Sensor Networks.
Perrig, R. S., Tygar, J. D., Wen, V., & Culler, D. E. (2002). SPINS: Security protocols for sensor networks. Wireless Networks,8(5), 521–534.
Junior, W., Figueriredo, T., Wong, H.-C. & Loureiro, A. Malicious node detection in wireless sensor networks. The 18th International parallel and distributed processing symposium (IPDPS’04), April 26–30, 2004, Santa Fe, Nex Mexico, USA
Curiac, D.-I., Banias, O., Dragan, F., Volosencu, C. & Dranga, O. (2007). Malicious node detection in wireless sensor networks using an autoregression technique. The 3rd International conference on networking and services (ICNS’07), June 19–25, 2007, Athens, Greece.
Yim, S.-J., & Choi, Y.-H. (2012). Neighbor-based malicious node detection in wireless sensor networks. Wireless Sensor Network,4, 219–225. https://doi.org/10.4236/wsn.2012.49032.
Gomathi, G., Yalini, C., & Revathi, T. K. (2014). Secure data aggregation technique for wireless sensor networks in the presence of security threats. International Journal of Emerging Technologies and Engineering (IJETE), 1(9), 229–234.
Ayday, E., Lee, H., & Fekri, F. (2009). An iterative algorithm for trust and reputation management. In Proceedings of the IEEE international conference on symposium on information, pp. 2051–2055.
Jiang, J., Han, G., Wang, F., Member, S. L. (2015). An efficient distributed trust model for wireless sensor networks. IEEE, and Mohsen Guizani, Fellow, IEEE Transactions On Parallel And Distributed Systems, Vol. 26, No. 5, May 2015.
Chang, J. M., Tsou, P. C., Woungang, I., Chao, H. C., & Lai, C. F. (2015). Defending against collaborative attacks by malicious nodes in MANETs: Cooperative bait detection approach. IEEE Systems Journal,9(1), 65–75.
Grgic, K., Zagar, D., & Cik, V. K. (2016). System for malicious node detection in IPv6-based wireless sensor networks. Journal of Sensors. https://doi.org/10.1155/2016/6206353.
Nirmal Raja, K., & Maraline Beno, M. (2017). Secure data aggregation in wireless sensor Network-Fujisaki Okamoto (FO) authentication scheme against Sybil attack. Journal of Medwell Systems. https://doi.org/10.1007/s10916-017-0743-2.
Shim, K. A., & Park, C. M. (2015). A secure data aggregation scheme based on appropriate cryptographic primitives in heterogeneous wireless sensor networks. IEEE Trans. Parallel and Distributed Systems (TPDS),26(8), 2128–2139.
X. Jinhui, T. Yang, Y. Feiyue, P. Leina, X. Juan., H. Yao. (2018). Intrusion detection system for hybrid DoS attacks using energy trust in wireless sensor networks. Scicedirect, Procedia, Computer Science 131, 8th International Congress of Information and Communication Technology (ICICT-2018), pp. 1188–1195.
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Gomathi, S., Gopala Krishnan, C. Malicious Node Detection in Wireless Sensor Networks Using an Efficient Secure Data Aggregation Protocol. Wireless Pers Commun 113, 1775–1790 (2020). https://doi.org/10.1007/s11277-020-07291-5
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11277-020-07291-5