Abstract
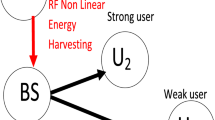
In this paper, we investigate the secrecy outage performance of the decode-and-forward cognitive relay network with the existence of the co-channel interference, where all nodes are equipped with single antenna and all channels experience Rayleigh fading channels, which are also independent non-identical distribution (i.n.i.d). We also consider the multiple user selection scheme and the single eavesdropper, which could wiretap the information at each hop. There is no evidence of the direct links from the source to the destinations because of the bad conditions. To evaluate the system secrecy performance, we derive the closed form expressions of the secrecy outage probabilities, and the Monte Carlo simulations are also presented to validate the accuracy of the theoretical analysis.




Similar content being viewed by others
References
Hussein, J., Ikki, S., & Boussakta, S. (2016). Analysis of opportunistic scheduling in dual-hop multi-user underlay cognitive network in the presence of co-channel interference. IEEE Transactions on Vehicular Technology. https://doi.org/10.1109/TVT.2015.2504244.
Ikki, S., & Aissa, S. (2010). Performance analysis of dual-hop relaying systems in presence of co-channel interference. In Proceedings of IEEE GLOBECOM, Miama, USA (pp. 1–5).
Yu, H., Lee, I.-H., & Stuber, G. L. (2012). Outage probability of decode-and-forward cooperative relaying systems with co-channel interference. IEEE Transactions on Wireless Communications, 11(1), 266–274.
Hussein, J., Ikki, S., Boussakta, S., & Tsimenidis, C. (May. 2015). Performance study of the dual-hop underlay cognitive network in the presence of co-channel interference. In Proceedings of IEEE 81st VTC-Spring, Glasgow, Scotland (pp. 1–5).
Fan, L., Zhang, S., Duong, T. Q., & Karagiannids, G. K. (2016). Secure swith-and-stay combing for cognitive relay networks. IEEE Transactions on Communications, 64(1), 70–82.
Krishna, V. S., & Bhatnagar, M. R. (2016). A joint antenna and path selection techniqe in single-relay-based DF cooperative MIMO networks. IEEE Transactions on Vehicular Technology, 65(3), 1340–1353.
Bhatnagar, M. R., Mallik, R. K., & Tirkkonen, O. (2016). Performance evaluation of best-path selection in a multiple decode-and-forward cooperative system. IEEE Transactions on Vehicular Technology, 65(4), 2722–2728.
Li, D. (2016). Opportunistic DF-AF selection for cognitive relay networks. IEEE Transactions on Vehicular Technology, 65(4), 2790–2796.
Park, J., Jang, C., & Lee, J. H. (2016). Outage analysis of underlay cognitive radio networks with multihop primary transmission. IEEE Communications Letters, 20(4), 800–803.
Kumar, D. P., Babu, M. S., & Prasad, M. S. G. (2016). Suboptimal comparison of AF and DF relaying for fixed target error probability. In Proceedings of ICCCI-2016 , Coimbatore, India (pp. 1–4).
Yang, Q., Ding, J., & Yang, J. (2016). Secrecy outage probability of dual-hop DF cognitive relay networks under interference constraints. In Proceedings of APCC 2016, Yogyakarta, Indonesia (pp. 76-80).
Ghose, S., Kundu, C., & Bose, R. (2016). Secrecy performance of dual-hop decode-and-forward relay system with diversity combing at the eavesdropper. IET Communications, 10(8), 904–914.
Yang, Z., Ding, Z., Fan, P., & Karagiannidis, G. K. (2016). Outage performance of cognitive relay networks with wireless information and power transfer. IEEE Transactions on Vehicular Technology, 65(5), 3828–3833.
Nguyen D. K., Matthaiou M., Duong T. Q., & Ochi H. (2015). RF energy haversting two-way cognitive DF relaying with transceiver impairments. In Proceedings of IEEE ICC 2015, London, UK (pp. 1970–1976).
Zhong, B., & Zhang, Z. (2018). Opportunistic two-way full-duplex relay selection in underlay cognitive networks. IEEE Systems Journal. https://doi.org/10.1109/JSYST.2016.2514601.
Li, N., Li, Y., Wang, T., Peng, M., & Wang, W. (2015). Full-duplex based spectrum sharing in cognitive two-way relay networks. In Proceedings of IEEE 26th PIMRC , Hong Kong, China (pp. 997–1001).
Prudnikov, A. P., Brychkov, Y. A., & Marichev, O. I. (1992). Integrals and series volume 4: Direct laplace transforms. New York: Gordon and Breach Science Publishers.
Gradshteyn, I. S., & RyzhikI, M. (2007). Table of integrals, series and products (7th ed.). New York: Academic Press.
Acknowledgements
The authors acknowledge the financial support by the National Natural Science Foundation of China under Grant No. 61472343.
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher’s Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Appendices
Appendices
1.1 Appendix 1: Proof of Corollary 1
According to \(Z_1 = \frac{{Id_{nD}^{ - \alpha }}}{{\left( {\rho - 1} \right) {N_{{0_D}}}}}{\left| {{h_{nD}}} \right| ^2} - \frac{{\rho Id_{nE}^{ - \alpha }}}{{\left( {\rho - 1} \right) {N_{{0_E}}}}}{\left| {{h_{nE}}} \right| ^2}\), the CDF of \(Z_1\) can be expressed as
where \(X_1 = \frac{{{{\left| {{h_{SR}}} \right| }^2}}}{{1 + \sum \nolimits _{i = 1}^{{L_R}} {{{\left| {{h_{Ri}}} \right| }^2}} }}\) and \(Y_1 = {\left| {{h_{SE}}} \right| ^2}\). The CDF of \(X_1\) is \({F_{X_1}}\left( x \right) = 1 - \exp \left( { - \frac{1}{{{\beta _1}}}x} \right) {\left( {\frac{{{\beta _1}}}{{{\lambda _R}x + {\beta _1}}}} \right) ^{{L_R}}}\), and the PDF of \(Y_1\) is \({f_{Y_1}}\left( y \right) = \frac{1}{{{\varepsilon _1}}}\exp \left( { - \frac{1}{{{\varepsilon _1}}}y} \right)\). By substituting \({F_{X_1}}\left( x \right)\) and \({f_{Y_1}}\left( y \right)\) into (24), \({F_{Z_1}}\left( z \right)\) can be referenced in Corollary1.
1.2 Appendix 2: Proof of Corollary 2
To solve the integration in (11), we should simplify the Gamma function first according to [18, eq. (8.352.5)],
Next, we can rewrite \({P_1}\) as
\({I_1}\) can be easily derived as
\({I_2}\) can be rewritten as
To obtain the integration P, we should deal with the form of integration \(H=\int _0^\infty {\exp \left( { - ax} \right) Ei\left( { - bx - c} \right) dx}\) first, and we will detailedly illustrate the process. After further derivation, H can be rewritten as
According to [18, eq. (6.224.1)], we can derive
In addition, \({H_2}\) can be rewritten as
where \({\theta \left( {t} \right) }\) is the unit step function. According to [17, eq. (3.4.1.9)], we can derive
Thus, we can obtain the final result H by combining (30) and (31)
Thus, according to (33), we can easily obtain the \({I_2}\)
where the details of \({a_1}\), \({b_1}\) and \({c_1}\) can be referenced the Corollary 2.
Next, \({I_3}\) can be expressed as
we can simplify the integration by letting \(s = {T_3}{T_3}t + {T_3}{\beta _1}\), after further derivation, and \({I_3}\) can be rewritten
Once more, we should let \(y = \frac{1}{{{\alpha _1}{T_3}{T_4}}} - \frac{{{T_2}}}{{{T_3}{T_4}}} + 1\) to calculate the integration. Now, \({I_3}\) is
According to \(\Gamma \left( {\alpha ,x} \right) = \int _x^\infty {{e^{ - t}}{t^{\alpha - 1}}dt}\) [18, eq. (8.350.2)], we can derive the closed form of \({I_3}\)
Thus, combining the results of \({I_1}\), \({I_2}\) and \({I_3}\), \(P_1\) is shown in (13).
Rights and permissions
About this article
Cite this article
Yang, Q., Ding, J. & Hu, A. Secrecy Outage Performance Analysis of DF Cognitive Relay Network With Co-channel Interference. Wireless Pers Commun 107, 549–564 (2019). https://doi.org/10.1007/s11277-019-06288-z
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11277-019-06288-z