Abstract
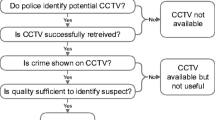
Recently, with the increase of terror and crime the utilization of security surveillance systems including CCTV increases. However, the issues of privacy invasion occurred by exposing the data recorded through video surveillance system have been raised. In this paper, the intelligent video surveillance system which can prevent the invasion of privacy and complement the monitoring function which will be declined by privacy protection is proposed. The proposed system checks the identification using the smart card and camera at the entrance and extracts the height and color information of object. Inside of the building where only a camera is installed without smart card terminal installed checks the identification using height and color information of object. With the implemented identification function the proposed system sorts the object receiving the privacy protection, implements the monitoring function and provides monitoring and protection function at the same time.
Similar content being viewed by others
References
Langheinrich, M. (2002). Privacy invasions in ubiquitous computing. In Proc. workshop on socially-informed design of privacy enhancing solutions in ubiquitous computing.
Westin, A. (1967). Privacy and freedom. New York: Atheneum.
Chang, Y., Yan, R., Chen, D., & Yang, J. (2006). People identification with limited labels in privacy-protected video. In Proc. IEEE int. conf. multimedia and expo (pp. 1005–1008).
Tansuriyavong, S., & Hanaki, S. I. (2001). Privacy protection by concealing persons in circumstantial video image. In Proc. perceptive user interfaces (pp. 1–4).
Venkatesh, B. R., & Makur, A. (2006). Object-based surveillance video compression using foreground motion compensation. In IEEE control, automation robotics and vision (pp. 1–6).
Matusek, F., & Reda, R. (2008). Efficient secure storage of privacy enhanced video surveillance data in intelligent video surveillance systems. In Proc. IEEE int. symposium on computer and information sciences (Vol. 23, pp. 1–5).
Schiff, J., Meingast, M., Mulligan, D. K., Sastry, S., & Goldberg, K. (2007). Respectful cameras: detecting visual markers in real-time to address privacy concerns. In IEEE intelligent robots and systems (pp. 971–978).
Martinez-Ponte, I., Desurmont, X., Meessen, J., & Delaigle, J. (2005). Robust human face hiding ensuring privacy. In Proc. int. workshop on image analysis for multimedia interactive services.
Dufaux, F., Ouaret, M., Abdeljaoued, Y., Navarro, A., Vergnenegre, F., & Ebrahimi, T. (2006). Privacy enabling technology for video surveillance. In Proc. SPIE mobile multimedia/image processing for military and security applications (Vol. 6250).
Dufaux, F., & Ebrahimi, T. (2008). Scrambling for privacy protection in video surveillance systems. IEEE Transactions on Circuits and Systems for Video Technology, 18, 1168–1174.
Kitahara, I., Kogure, K., & Hagita, N. (2004). Stealth vision for protecting privacy. Proceedings - International Conference on Pattern Recognition, 4, 404–407.
Kitahara, I. (2008). Interactive video surveillance by using environmental and mobile cameras. In IEEE automation congress (pp. 1–6).
Moncrieff, S., Venkatesh, S., & West, G. A. W. (2009). Dynamic privacy in public surveillance. IEEE Computer Society, 42, 22–28.
Kim, D. H., Lee, J. Y., Yoon, H. S., & Cha, E. Y. (2007). A non-cooperative user authentication system in robot environments. IEEE Trans. Comsum. Electron., 53.
Bovyrin, A., & Rodyushkin, K. (2005). Human height prediction and roads estimation for advanced video surveillance systems. In IEEE conf. on advanced video and signal based surveillance (Vols. 15–16, pp. 219–223).
Jeges, E., Kispal, I., & Hornak, Z. (2008). Measuring human height using calibrated cameras. In IEEE conf. on human system interactions (pp. 755–760).
Choi, Y. J., Kim, K. J., Nam, Y. Y., & Cho, W. D. (2008). Retrieval of identical clothing images based on local color histograms. Convergence and Hybrid Information Technology, 1, 818–823.
Xiaoyi, Y., Chinomi, K., Koshimizu, T., Nitta, N., Ito, Y., & Babaguchi, N. (2008). Privacy protecting visual processing for secure video surveillance. In IEEE int. conf. on image processing (pp. 1672–1675).
Moon, H. M., & Pan, S. B. (2009). Implementation of the privacy in video surveillance system. In Proc. IEEE int. conf. secure software and reliability improvement (pp. 285–285).
Criminisi, A., Zisserman, A., Gool, L. V., Bramble, S., & Compton, D. (1998). A new approach to obtain height measurements from video. Proceedings - SPIE, 3576, 1–6.
Criminisi, A. (2002). Single-view metrology: algorithms and application. In Proceedings of the 24th DAGM symposium on pattern recognition.
Gervautz, M., & Purgathofer, W. (1990). A simple method for color quantization: octree quantization. In New trends in computer graphics (pp. 287–293).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Moon, HM., Chae, SH., Moon, D. et al. Intelligent video surveillance system using two-factor human information. Telecommun Syst 52, 2249–2257 (2013). https://doi.org/10.1007/s11235-011-9530-4
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11235-011-9530-4