Abstract
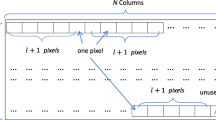
For improving the steganographic security, the data-hiders always hope to lower the distortion level and to preserve the original data distribution. A novel efficient data hiding scheme with a histogram-preserving property is proposed in this work. After decomposing cover samples into a series of binary sequences, a number of candidate vectors representing each secret bit-block are produced, and a criterion for lowering steganographic distortion and keeping flip balance is set up for optimal selection from the candidates. A combination of flipping rates for different binary sequences to maximize the secret capacity is also studied. This way, the original data distribution in cover sequence is preserved, and a payload-distortion performance approaching the theoretical upper bound can be achieved.
Similar content being viewed by others
References
Wang, H., & Wang, S. (2004). Cyber warfare: steganography vs. steganalysis. Communication of the ACM, 47(10), 76–82.
Zhang, X., & Wang, S. (2006). Dynamical running coding in digital steganography. IEEE Signal Processing Letters, 13(3), 165–168.
Fridrich, J., & Soukal, D. (2006). Matrix embedding for large payloads. IEEE Transformations on Information Forensics and Security, 3(1), 390–394.
Zhang, W., Zhang, X., & Wang, S. (2008). Maximizing steganographic embedding efficiency by combining hamming codes and wet paper codes. In Lecture notes in computer science : Vol. 5284. Proceedings of the 10th information hiding workshop (pp. 60–71). Berlin: Springer.
Sallee, P. (2004). Model-based steganography. In Lecture notes in computer science : Vol. 2939. Proceedings of the 6th information hiding workshop (pp. 154–167). Berlin: Springer.
Zhang, X., Wang, S., & Zhang, K. (2003). Steganography with least histogram abnormality. In Lecture notes in computer science : Vol. 2776. Computer network security (pp. 395–406). Berlin: Springer.
Wu, H., Dugelay, J., & Cheung, Y. (2008). A data mapping method for steganography and its application to images. In Lecture notes in computer science : Vol. 5284. Proceedings of the 10th information hiding workshop (pp. 236–250). Berlin: Springer.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Zhang, X., Wang, S. Efficient data hiding with histogram-preserving property. Telecommun Syst 49, 179–185 (2012). https://doi.org/10.1007/s11235-010-9364-5
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11235-010-9364-5