Abstract
Network intrusion detection systems are useful tools that support system administrators in detecting various types of intrusions and play an important role in monitoring and analyzing network traffic. In particular, anomaly detection-based network intrusion detection systems are widely used and are mainly implemented in two ways: (1) a supervised learning approach trained using labeled data and (2) an unsupervised learning approach trained using unlabeled data. Most studies related to intrusion detection systems focus on supervised learning. However, the process of acquiring labeled data is expensive, requiring manual labeling by network experts. Therefore, it is worthwhile investigating the development of unsupervised learning approaches for intrusion detection systems. In this study, we developed a network intrusion detection system using an unsupervised learning algorithm autoencoder and verified its performance. As our results show, our model achieved an accuracy of 91.70%, which outperforms previous studies that achieved 80% accuracy using cluster analysis algorithms. Our results provide a practical guideline for developing network intrusion detection systems based on autoencoders and significantly contribute to the exploration of unsupervised learning techniques for various network intrusion detection systems.








Similar content being viewed by others
References
Akhgar B, Saathoff GB, Arabnia HR, Hill R, Staniforth A, Bayerl PS (2015) Application of big data for national security: a practitioner’s guide to emerging technologies. Butterworth-Heinemann, Oxford, p 320. https://doi.org/10.1016/B978-0-12-801967-2.01002-8
Deligiannidis L, Arabnia HR (2015) Security surveillance applications utilizing parallel video-processing techniques in the spatial domain. In: Deligiannidis L, Arabnia HR (eds) Emerging trends in image processing, computer vision and pattern recognition. Morgan Kaufmann, Boston, pp 117–130. https://doi.org/10.1016/B978-0-12-802045-6.00008-9
Choche A, Arabnia H (2011) A methodology to conceal qr codes for security applications. In: Proceedings of the 10th International Conference on Information and Knowledge Engineering. pp 151–157
Javaid A, Niyaz Q, Sun W, Alam M (2016) A deep learning approach for network intrusion detection system. In: Proceedings of the 9th EAI International Conference on Bio-inspired Information and Communications Technologies (formerly BIONETICS), 2016. ICST (Institute for Computer Sciences, Social-Informatics and Telecommunications Engineering), pp 21–26. https://doi.org/10.4108/eai.3-12-2015.2262516
Bace R, Mell P (2001) NIST special publication on intrusion detection systems. National Institute of Standards and Technology, Gaithersburg
Gogoi P, Borah B, Bhattacharyya DK (2010) Anomaly detection analysis of intrusion data using supervised & unsupervised approach. J Converg Inf Technol 5(1):95–110
Panda M, Abraham A, Patra MR (2010) Discriminative multinomial Naïve Bayes for network intrusion detection. In: 2010 Sixth International Conference on Information Assurance and Security. pp 5–10. https://doi.org/10.1109/ISIAS.2010.5604193
Naoum RS, Abid NA, Al-Sultani ZN (2012) An enhanced resilient backpropagation artificial neural network for intrusion detection system. Int J Comput Sci Netw Secur 12(3):11–16
Thaseen S, Kumar CA (2013) An analysis of supervised tree based classifiers for intrusion detection system. In: 2013 International Conference on Pattern Recognition, Informatics and Mobile Engineering. pp 294–299. https://doi.org/10.1109/ICPRIME.2013.6496489
Syarif I, Prugel-Bennett A, Wills G (2012) Unsupervised clustering approach for network anomaly detection. 2012 networked digital technologies. Springer, Berlin, pp 135–145
Heba FE, Darwish A, Hassanien AE, Abraham (2010) A principle components analysis and support vector machine based intrusion detection system. In: 2010 10th International Conference on Intelligent Systems Design and Applications. pp 363–367. https://doi.org/10.1109/ISDA.2010.5687239
Bengio Y, Lamblin P, Popovici D, Larochelle H (2006) Greedy layer-wise training of deep networks. In: Proceedings of the 19th International Conference on Neural Information Processing Systems, Canada. pp 153–160
Sakurada M, Yairi T (2014) Anomaly detection using autoencoders with nonlinear dimensionality reduction. In: Proceedings of the MLSDA 2014 2nd Workshop on Machine Learning for Sensory Data Analysis. ACM, pp 4–11. https://doi.org/10.1145/2689746.2689747
Mirsky Y, Doitshman T, Elovici Y, Shabtai A (2018) Kitsune: an ensemble of autoencoders for online network intrusion detection. arXiv Preprint. arXiv:1802.09089
Vincent P, Larochelle H, Bengio Y, Manzagol P-A (2008) Extracting and composing robust features with denoising autoencoders. In: Proceedings of the 25th International Conference on Machine Learning, Helsinki, Finland. ACM, pp 1096–1103. https://doi.org/10.1145/1390156.1390294
Bengio Y (2009) Learning Deep Architectures for AI. Found Trends Mach Learn 2(1):1–127. https://doi.org/10.1561/2200000006
Hinton GE, Salakhutdinov RR (2006) Reducing the dimensionality of data with neural networks. Science 313(5786):504–507. https://doi.org/10.1126/science.1127647
Cao L, Huang W, Sun F (2016) Building feature space of extreme learning machine with sparse denoising stacked-autoencoder. Neurocomput 174:60–71. https://doi.org/10.1016/j.neucom.2015.02.096
Robbins H, Monro S (1951) A stochastic approximation method. Ann Math Stat 22(3):400–407
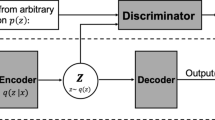
Kingma DP, Welling M (2013) Auto-encoding variational bayes. arXiv Preprint. arXiv:1312.6114
Tavallaee M, Bagheri E, Lu W, Ghorbani AA (2009) A detailed analysis of the KDD CUP 99 data set. In: 2009 IEEE Symposium on Computational Intelligence for Security and Defense Applications. pp 1–6. https://doi.org/10.1109/CISDA.2009.5356528
Kingma DP, Ba J (2014) Adam: A method for stochastic optimization. arXiv Preprint. arXiv:1412.6980
Acknowledgements
This research was supported by the project “Efficient Operation of LTE Device and IT infrastructure Assets Self-diagnosis Integrated Control System” of the Korea Evaluation Institute of Industrial Technology.
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Appendix
Rights and permissions
About this article
Cite this article
Choi, H., Kim, M., Lee, G. et al. Unsupervised learning approach for network intrusion detection system using autoencoders. J Supercomput 75, 5597–5621 (2019). https://doi.org/10.1007/s11227-019-02805-w
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11227-019-02805-w