Abstract
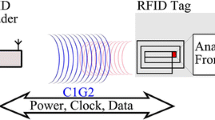
RFID is a core technology enabling a ubiquitous environment. Its various applications have shown great progress in our daily life in fields such as distribution management, non-contacting authentication, payment cards, and hi-pass (highway toll payment) cards among others. However, the low security of RF (radio frequency) in the authentication stage makes most RFID tags on the market susceptible to privacy breaches and malicious attacks. This paper presents a lightweight bilateral RFID protocol design which reinforces the security vulnerabilities of conventional RFID systems. This design lightens the encryption process, enabling the adoption of protocols in the UHF bands proposed by the EPC Class-1 Generation-2 standards. It also utilizes the core characteristics of EPC tags, facilitating tag-to-tag bilateral authentication. Additionally, multi-tag authentication is applied for the inventory management and distribution environments that use UHF band RFID systems. The proposed protocol provides robust security regarding the known flaws of RF communication and has taken hardware into consideration allowing practical utilization such as management of food, medicine and medical supplies, and manufacturing components.






Similar content being viewed by others
References
Finkenzeller K (2003) RFID handbook: fundamentals and applications in contactless smart cards and identification, 2nd edn. Wiley, New York
Yan L, Zhang Y, Yang LT, Ning H (2007) The internet of things from RFID to the next-generation pervasive networked systems. Auerbach Publications, Boca Raton
Chien H-Y, Chen C-H (2007) Mutual authentication protocol for RFID conforming to EPC class-1 generation-2 standards. Comput Stand Interfaces 29(2):254–259 (Elsevier Science Publishers)
Piramuthu S (2007) Protocols for RFID tag/reader authentication. Decis Support Syst 43(3):897–914
Kim C, Avoine G (2011) RFID distance bounding protocols with mixed challenges. IEEE Trans Wirel Commun 10(5):1618–1626
Kim C, Avoine G, Koeune F, Standaert F-X, Pereira O (2009) The Swiss-knife RFID distance bounding protocol. In: Information security and cryptology–ICISC 2008, Lecture Notes in Computer Science, vol 5461, pp 98–115
Habibi MH, Gardeshi M, Alaghband MR (2011) Practical attacks on a RFID authentication protocol conforming to EPC C-1 G-2 standard. Int J UbiComp (IJU) 2(1):1–13
Peris-Lopez P, Hernandez-Castro JC, Estevez-Tapiador JM, Ribagorda A (2009) An ultra light authentication protocol resistant to passive attacks under the Gen-2 specification. J Inf Sci Eng 25(1):33–57
Peris-Lopez P, Hernandez-Castro JC, Estervez-Tapiador JM, Ribagorda A (2009) Cryptanalysis of a novel authentication protocol conforming to EPC-C1G2 standard. Comput Stand Interfaces 31(2):372–380
Jules A (2004) Yoking proofs for RFID tags. In: IEEE Computer Society, Proceedings of the first international workshop on pervasive computing and communication security-PerSec 2004, pp 138–143
Lin CC, Lai YC, Tygar JD, Yang CK, Chiang CL (2007) Coexistence proof using chain of timestamps for multiple RFID tags. In: Proceedings of advances in web and network technologies and information management, LNCS, vol 4537, pp 634–643
Cho J, Yeo S, Hwang S, Rhee S, Kim S (2008) In: Enhanced Yoking proof protocols for RFID tags and tag groups. In: 22nd international conference on advanced information networking and applications, pp 1591–1596
Saito J, Sakurai K (2005) Grouping proof for RFID tags. In: Proceedings of the 19th international conference on advanced information networking and applications (AINA’05), pp 621–624
Piramuthu S (2006) On existence proofs for multiple RFID Tags. In: IEEE Computer Society Press. IEEE international conference on pervasive services, workshop on security, privacy and trust in pervasive and ubiquitous computing–SecPerU 2006, pp 317–320
Jung Y, Kim H, Lee A, Jun M (2012) Study on 2BP distance bounding protocol to prevent relay attack in RFID environment. In: KIPS Conference 2012, Korea Information Processing Society
EPC Global Inc. (2008) EPCTM radio frequency identity protocols C1G2 UHF RFID Protocol Ver1.2.0
Jung H (2015) A memory efficient anti-collision protocol to identify memoryless RFID tags. J Inf Process Syst 11(1):95–103
Dahane A, Berrached N-E, Loukil A (2015) A virtual laboratory to practice mobile wireless sensor networks: a case study on energy efficient and safe weighted clustering algorithm. J Inf Process Syst 11(2):205–228
Malhotra N, Nagpal G (2015) Genetic symmetric key generation for IDEA. J Inf Process Syst 11(2):239–247
Acknowledgments
This work was supported by the ICT R&D program of MSIP/IITP. [R0112-14-1061, The analysis technology of a vulnerability on an open-source software, and the development of Platform].
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Kang, J. Lightweight mutual authentication RFID protocol for secure multi-tag simultaneous authentication in ubiquitous environments. J Supercomput 75, 4529–4542 (2019). https://doi.org/10.1007/s11227-016-1788-6
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11227-016-1788-6