Abstract
This paper examines the role of software piracy in digital platforms where a platform provider makes a decision of how much software to produce in-house and how much to outsource from a third-party software provider. Using a vertical differentiation model, we theoretically investigate how piracy influences the software outsourcing decision. We find that when piracy is intermediate, the loss in in-house software profits due to piracy outweighs the loss in licensing fee profits. As a result, an increase in piracy leads to more outsourcing. However, when piracy is high, it becomes too expensive for the platform provider to subsidize the software provider, resulting in a decrease in outsourcing. Moreover, when software variety is also endogenously chosen by firms, the platform provider’s incentive to develop software variety in-house depends not only on the return from software profits but also on the return from hardware profits. Under such a situation, an increase in piracy always leads to less outsourcing and less total software variety. To provide additional insights on the outsourcing decision, we conduct empirical analyses using data from the U.S. handheld video game market between 2004 and 2012. This market is a classical two-sided market, dominated by two handheld platforms (Nintendo DS and Sony PlayStation Portable) and is known to have suffered from software piracy significantly. Our regression results show that in this market, piracy increases outsourcing but has no effect on the total software variety.
Similar content being viewed by others
1 Introduction
Software piracy has been a hotly debated topic in digital platforms such as video games, smartphone/tablet apps, and ebooks. Traditionally, studies on software piracy have mainly focused on how software piracy might increase/decrease the profits of software providers (see e.g., Conner and Rumelt 1991; Takeyama 1994; Givon, Mahajan, and Muller 1995; Shy and Thisse 1999; Peitz 2004; Jain 2008; Sinha et al. 2010; Vernik et al. 2011; Lahiri and Dey 2013). However, in digital platforms where consumers and software providers interact (e.g., Church and Gandal 1992), software piracy does not only affect the profits of software providers, but also the profits of platform providers. In order to use software, consumers first need to adopt a platform. This feature appears to suggest that platform providers might benefit from software piracy because it potentially increases the sales of platforms, which creates a conflict of interest in piracy protection between platform providers and software providers.
Despite its importance and relevance to digital platform businesses, little has been studied about the role of software piracy in a two-sided market setting. Notable exceptions are Rasch and Wenzel (2013, 2015). Built on the literature on two-sided markets (e.g., Rochet and Tirole 2006; Rysman 2009, Rasch and Wenzel 2013 theoretically study the conflict between platforms and software developers in a competitive platform market. Rasch and Wenzel (2015) extend this theoretical model and examine how the impact of piracy differs across prominent and non-prominent software developers. Our paper aims at contributing to this literature by examining the role of outsourcing decisions by a platform provider when software piracy exists. In many digital platforms, platform providers are also software providers (e.g., Nintendo, Microsoft, Apple, Google), and often in-house software accounts for a significant proportion of platform providers’ profits. For example, for Nintendo DS, a handheld video game device released by Nintendo in November 2004, Nintendo made USD 89.2 million revenue in the first year from own in-house software alone, and this was 53% of revenues for all software released on Nintendo DS and 25% of the revenue from Nintendo DS handheld device (hardware) in the same period. The in-house software production in digital platform markets is an important phenomenon, and has been studied in the context of vertical integration between platform providers and software providers (e.g., Lee 2013). However, no prior studies on software piracy have incorporated this important aspect into the analysis.Footnote 1
When software is provided by both platform and software providers, the effect of piracy on platform providers is not straightforward. While piracy might help increase the sales of platforms, it can hurt in-house software profits. Platforms might then pass on the loss to software providers by outsourcing software, but doing so will reduce the overall profits from software because the margin from in-house software is higher than that from licensing fee revenues. Our goal is to examine the impact of software piracy on the equilibrium outsourcing decision, or equivalently in-house production decision.
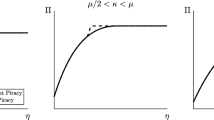
To investigate the question, we develop a vertical differentiation model of software piracy where upon buying a platform (hardware), consumers choose to buy a legal copy of software or use an illegal copy. Following previous studies, we capture the role of piracy through the deteriorated quality of illegal software (e.g., cost of acquiring knowledge for pirating software, psychological disutility). An increase in piracy in our model means that the quality of illegal software becomes closer to the quality of legal software.Footnote 2 Under this setting, we first consider two baseline scenarios: (1) full integration scenario, where the platform provider supplies both platform and software, and (2) full outsourcing scenario, where the platform provider supplies platform and the software provider supplies software. We show that in the full integration scenario, the platform provider’s combined profits from hardware and software are always decreasing in piracy. While the hardware profits are increasing in piracy, the loss of software profits due to piracy outweighs the gain in hardware profits. However, if the platform provider fully outsources software and earns software licensing fees from the software provider, the impact of software piracy on its profits is non-linear in piracy, and the platform provider benefits from an increase in piracy when piracy is relatively high. This is because, although the profits from software licensing fees are decreasing in piracy, the rate of the decline is smaller than that in in-house software profits in scenario (1). As a result, the gain in platform profits due to piracy can outweigh the loss in licensing fee profits when piracy is relatively high. We also find that under some conditions, the equilibrium licensing fee can be negative so as to subsidize the software firm.
Built on the two baseline scenarios, we examine the main scenario in which the platform provider chooses the degree of in-house versus outsourced software production. We find that when piracy is intermediate, an increase in piracy increases outsourcing. This can be explained through the mechanism combined from the two baseline scenarios: As piracy increases, the loss in in-house software profit due to piracy increases. Although the profit margin from in-house software is higher than licensing fees, the platform provider benefits from shifting software profits from in-house to licensing fees because the (negative) marginal impact of piracy can be reduced. However, when piracy is high to begin with, an increase in piracy decreases outsourcing. High piracy severely erodes the software firm’s profits and it becomes too costly for the platform provider to subsidize the software firm. As a result, the platform provider will decrease outsourcing. We show that this result is robust to modeling assumptions such as whether the price of in-house software is set by the hardware firm or the software firm.
Our main model focused on a situation where software variety is fixed and piracy influences the outsourcing decision. Another important and relevant situation to digital platforms is where software variety is also endogenously chosen and thus can change with piracy. We extend the main model by assuming that the platform provider chooses in-house software variety and the software firm chooses outsourced software variety. This modeling change generates additional incentive for the platform provider to produce in-house software: because the hardware demand depends on the total software variety, an increase in in-house software variety increases both hardware and in-house software profits. Also, the licensing fee will influence both licensing fee profits (directly) and hardware profits (indirectly via a change in the software variety supplied by the software provider). Our analysis shows that as piracy increases, (a) the total software variety decreases, and (b) the proportion of outsourced software decreases. The latter happens because of the additional benefit from hardware profits: even when piracy is very severe that very few consumers buy software legally, the platform provider still has an incentive to produce in-house software for “pirates” so as to increase profits from hardware itself.
Given that our theoretical result on the impact of piracy on the outsourcing decision depends on whether piracy influences the total software variety or not, we resort to an empirical investigation and derive additional insights on the outsourcing decision. We use data from the U.S. handheld video game market between 2004 and 2012. This market is a classical two-sided market (Clements and Ohashi 2005; Dubé, Hitsch, and Chintagunta 2010; Chao and Derdenger 2013; Derdenger and Kumar 2013; Lee 2013; Derdenger 2014), dominated by two handheld platforms (Nintendo DS and Sony PlayStation Portable) and is known to have suffered from software piracy significantly (Fukugawa 2011). For Nintendo DS, a device called Revolution 4 made hacking possible, and for Sony PlayStation Portable, Pandora battery was the key device for hacking. We obtain monthly data on software releases from NPD and create a measure for the proportion of outsourced software based on the monthly number of newly released in-house and outsourced video games. As we cannot directly observe the ease of piracy, we use U.S. Google Trends search volume on the two idiosyncratic devices as a proxy for the ease of piracy. Our identification assumption is that as more information about hacking devices becomes available, the chance of a consumer finding hacking information becomes higher, which induces more search behavior on Google. Under this assumption, U.S. Google Trends search volume captures variation in the cost of acquiring knowledge about pirating software. In order to control for potential endogeneity of the search volume, we also obtain Google Trends data on the same devices restricted to Japan (in Japanese) and use as an instrument.
Using monthly observations for the two handheld devices, we run regression analyses and estimate the effect of piracy on the proportion of outsourced software by controlling for other important factors such as the cumulative sales of hardware, system software updates, and platform- and month-fixed effects. We find that the effect of piracy is positive and significant. This result is in line with the theoretical prediction when the total software variety is predetermined. To further investigate this possibility, we examine whether piracy influences the total software variety (measured by the monthly number of newly released software) and indeed find that piracy does not have a significant effect. These two empirical analyses suggest that at least in the U.S. handheld video game market, data patterns are consistent with the model with predetermined software variety.
The rest of the paper is organized as follows. In Section 2, we develop a model of piracy and outsourcing decision using a vertical differentiation model with a monopolist platform provider, and present our main results. In Section 3, we examine alternative modeling assumptions, including endogenous software variety. Section 4 provides further insights on piracy and the outsourcing decision using empirical analyses. Section 5 concludes.
2 A model of software piracy
We examine the role of piracy in outsourcing software in a vertical differentiation model with a monopolist platform provider.Footnote 3 Our model consists of three players: the platform provider, the software provider, and consumers. The platform provider produces the hardware and sets the hardware price. It can also produce software by itself (in-house software), outsource software to the software provider (outsourced software), or mix of them. In this section, we assume that the total software variety developed is predetermined and normalized to one unit, and let δ ∈ [0, 1] be the proportion of software developed in-house and 1 − δ be the proportion outsourced. We assume that the cost of developing δ software for the platform provider is \(\frac {C_{h}}{2}\delta ^{2}\) and the cost of developing 1 − δ software for the software provider is \(\frac {C_{s}}{2}(1-\delta )^{2}\). Finally, we assume that software is undifferentiated, and that the marginal costs of hardware and software are zero.
The timeline of the model is as follows:
- 1.
The platform provider sets the price of hardware (ph) and the proportion of software developed in-house (δ).
If δ < 1 (some outsourcing), the platform provider sets the unit licensing fee (f ) paid by the software provider.
If δ = 1 (no outsourcing), the platform provider sets the price of software (ps).
- 2.
If δ < 1, the software provider observes f and sets the price of software (ps) that is common for all software.
- 3.
Consumers observe ph and ps, and decide to buy hardware and to buy or pirate software.
We first describe consumers’ purchase decisions, and then move on to the firms’ decisions.
2.1 Consumers’ purchase decisions
Suppose that the consumers who buy one unit of software have the following utility:
and the pirates have the following utility:
where v > 0 is the benefit from the hardware absent software; For example, smart phones have some benefit even without any apps, or PlayStation 4 has a built-in Blu-ray player;Footnote 4α is the benefit from the software; ph is the price of the hardware; ps is the price of the software; γ is the reduction in utility due to the fact that the software is pirated. It might be psychological disutility such as the fear of getting caught, the cost of acquiring knowledge for finding and using pirated software, the fact that the software is not pirated right away and so it’s a somewhat older game, or the fact that many pirated software have limited functionality, e.g., inability to play multiplayer sessions online for video games. Thus we interpret γ as a measure for the ease of piracy. The larger it is, the more serious is the problem they pose. If γ = 1, then no one buys the software, and if γ = 0, there’s no piracy. We assume that γ ∈ (0, 1). Hereafter, for better readability, we simply use the term “piracy” to refer to γ.
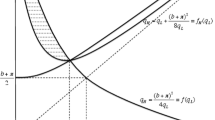
We assume that in order to play the software one has to purchase the hardware, that is, the reality of the digital platform business is such that the hardware cannot be pirated. In order to figure out who pirates and who buys, we let α be uniformly distributed between 0 and \(\bar {\alpha }\), and as we show shortly, Fig. 1 summarizes the distribution of buyers and pirates:
To show that indeed consumers with α ∈ [0, α1] do not buy the hardware, consumers with α ∈ [α1, α2] buy the hardware and pirate the software, while consumers with \(\alpha \in [\alpha _{2},\bar {\alpha }]\) buy both hardware and software, note that the utilities of both buyers and pirates are increasing in α and therefore if we define α1 as the lowest benefit such that upirate(α1) = 0, then for α < α1, the consumers do not purchase the hardware and thus are out of the market, and for α > α1, the consumers buy the hardware and have only to decide whether to pirate or purchase the software. Solving upirate(α1) from Eq. 2, this lower bound is given by the following:
The boundary α2 is such that the utilities of the pirates and legal buyer are exactly equal. Since from Eqs. 1 and 2, it is evident that \(\frac {\partial u_{legal}}{\partial \alpha }>\frac {\partial u_{pirate}}{\partial \alpha }\), consumers with α < α2 pirate the software and those with α > α2 buy it legally. Solving upirate(α2) = ulegal(α2) from Eqs. 1 and 2 yields the following:
We now discuss the optimal behavior of the firms where we first deal with one firm that produces both hardware and software (δ = 1: full integration), and then proceed to the case where production is done by separate entities (δ = 0: full outsourcing). Finally, we consider the case where δ ∈ (0, 1). Throughout our analysis, we make the following assumption.
Assumption 1
\(\bar {\alpha } > \sqrt {2}v\).
Intuitively, this assumption states that the utility from software is large enough as compared to the pure hardware benefit. We make this assumption because our focus in this paper is on the role of software and its piracy activities.
2.2 A single firm produces both hardware and software (Full Integration)
The profit of the monopolist producing both hardware and software is given by the following:
where the RHS of Eq. 5) is achieved by substituting from Eqs. 3 and 4. First order conditions with respect to both prices yield the following (it is straightforward to check the second order conditions are also satisfied). The superscript I implies that the variable in question is an equilibrium solution in this Integration case.
Substituting Eqs. 6 and 7 into Eqs. 3 and 4 yield the following:
Clearly \({\alpha _{2}^{I}}>{\alpha _{1}^{I}}\) for all range of parameters, and \({\alpha _{1}^{I}}\ge 0\) if \(\bar {\alpha }\gamma \ge v\). Assumption 1 guarantees that such γ exists. If this condition is not satisfied, it means that all consumers purchase the hardware and the hardware price does not depend on γ (i.e., ph = v). It is also easy to check that \(u_{pirate}(\alpha _{2})=u_{legal}(\alpha _{2})=\frac {v}{2}\). Thus the utility of the pirates spans the range from 0 to \(\frac {v}{2}\), while the utility of the legal buyers span the range of \(\frac {v}{2}\) to \(\frac {\bar {\alpha }+v}{2}\). Substituting Eq. 6 through 9 into 5 yields that the profits of the firm are declining with increase in piracy (γ) as is evident from the following equation:
Equation 10 also suggests that when Ch is large, the hardware firm prefers not to produce software at all. If the firm does not produce any software, it still can make profits on the hardware because of the intrinsic value of hardware v. The firm would then charge the price of ph = v, and at that price the entire market (\(\bar {\alpha }\)) would buy the hardware. Thus the firm would make the profits of \(\bar {\alpha }v\).
It is then easy to check that when Ch is large, a higher γ makes the hardware firm not produce software because \(\frac {\partial {\pi _{h}^{I}}}{\partial \gamma }<0\). The following Proposition summarizes the results of the Full Integration case.
Proposition 1
[Full Integration] For small Ch, the hardware firm will develop software for any γ ∈ (0, 1). For intermediate Ch, the hardware firm will only develop software when γis smaller than a threshold that is a function of\((\bar {\alpha },v,C_{h})\). For large Ch, the hardware firm will only sell hardware. When the hardware firm develops software, (i) the firm’s profits decrease in γand (ii) for a small γ, all consumers buy hardware at ph = vand the profits from hardware sales do not depend on γ.
We provide detailed analysis in Appendix A.1.
2.3 Separate production with hardware firm setting licensing fee (Full Outsourcing)
This case deals with two independent firms: The hardware firm (subscripted by h) sets the price of the hardware (ph) and the licensing fee (f ), and the software provider (subscripted by s) sets the price of the software (ps). We start with the software provider’s problem.
The profit function of the software provider is given by the following, where the RHS of the equation is achieved by substituting from Eq. 4. In accordance with the previous section, the superscript O implies that the variable in question pertains to this Outsourcing case.
The first-order condition gives
Substituting Eq. 12 into Eq. 11 yields the software provider’s profits:
This profits impose an important constraint: the software provider produces the software only if πs(f) ≥ 0. Since \(\frac {\partial \pi _{s}(f)}{\partial f}<0\), when Cs is large, the hardware firm needs to lower the licensing fee sufficiently (f could be negative) in order to make the software provider produce the software.
The hardware producer profits are given by the following where the RHS of the equation is achieved by substituting from Eqs. 3, 4 and 12.
The first-order conditions with respect to ph and f yield the following:
If we substitute Eq. 16 into Eq. 12, we get the software price:
The price of the hardware remains as before, but the price of the software increased, and thus we see the effect of double marginalization: the price to the consumers is higher. Also we can recalculate the boundaries by substituting Eqs. 15 and 17 into Eqs. 3 and 4:
Thus the lower bound α1 did not change while the upper bound increased from \(\frac {\bar {\alpha }}{2}\) to \(\frac {3\bar {\alpha }}{4}\). Thus the fact that a separate firm produces the software, increases pirates (since it increases the software price). We can now compute the profits of the two firms as follows:
Now we can ask about the effect of piracy (γ). Suppose γ is increased. Then the price of the software drops while the hardware price increases. In the Full Integration case, the absolute changes are equal, i.e., \(\left |\frac {\partial p_{h}}{\partial \gamma }\right |=\left |\frac {\partial p_{s}}{\partial \gamma }\right |=\frac {\bar {\alpha }}{2}\). In the Full Outsourcing case, the decrease in software price is higher than the increase in the price of the hardware as demonstrated by the following inequality:
More interestingly, while the software firm clearly loses from piracy (see Eq. 21), the hardware firm may benefit from piracy when \(\gamma \ge \frac {v}{\bar {\alpha }}\). Differentiating (20) with respect to γ yields that \(\frac {\partial \pi _{h}}{\partial \gamma }\ge 0\) if:
If \(v\le \bar {\alpha }\gamma \le \sqrt {2}v\), then we get the expected result that \(\frac {\partial \pi _{h}}{\partial \gamma }\le 0\). However if \(\bar {\alpha }\gamma \ge \sqrt {2}v\), then the firm producing the hardware benefits from piracy. The reason is that this firm indeed loses twice: Once on the licensing fee (see Eq. 16), and second because the lower bound for buying the hardware α1 is getting slightly larger (see Eq. 18). But when piracy is large to begin with (as required by condition (22)), the change in this lower bound is small. On the other hand, the hardware firm gains considerably by charging more for the hardware at a rate of \(\frac {\bar {\alpha }}{2}\) (see Eq. 15), and so if \(\bar {\alpha }\) is large enough (as required by condition (22)), then the overall effect is to increase its profits when piracy increases.
As in the previous case, as a sanity check, we can compute what will be the profits of the hardware producer if it decides not to buy any software from the software provider, and compare it to the profits given in Eq. 20. We first note that the software provider develops software if \({\pi _{s}^{O}}\ge 0\). For a range of (γ, Cs) such that \({\pi _{s}^{O}}>0\) (inner solutions), it is easy to check that \({\pi _{h}^{O}}>\bar {\alpha }v\) for any γ within the range. This is because the hardware firm earns positive licensing fee profits (i.e., \(\frac {\bar {\alpha }^{2}(1-\gamma )}{8}>0\)), and the profits from hardware sales are at least as large as \(\bar {\alpha }v\).
Now consider a range of (γ, Cs) such that \({\pi _{s}^{O}}\le 0\) (corner solutions). Under this condition, the hardware firm has two options: (i) lower the licensing fee and guarantee that \({\pi _{s}^{O}}=0\), or (ii) abandon software and only sell hardware (and earn \(\pi _{h}=\bar {\alpha }v\)). Recall (13). The constraint πs = 0 implies that
where the last identity comes from the constraint that the demand for software is nonnegative. Under this f, the demand for software is \(\sqrt {\frac {C_{s}}{2(1-\gamma )}}\). Substituting this licensing fee and Eq. 15 into Eq. 14 yields
When \(\gamma <\frac {v}{\bar {\alpha }}\), we have seen that the hardware firm has an incentive to make the software provider develop software as long as the licensing profits are nonnegative, which is equivalent to a nonnegative licensing fee. When \(\gamma \ge \frac {v}{\bar {\alpha }}\), the optimal f could be negative and the profit loss due to the negative f could be fully compensated by an increase in the profits from hardware (as it increases with γ). However, for a very large γ, the “subsidy” to the software firm through a negative licensing fee becomes too large to be compensated by hardware profits. As a result, the hardware firm will prefer not having software.
The following Proposition summarizes the results of the Full Outsourcing case.
Proposition 2
[Full Outsourcing] For small Csand γ, the hardware firm will set a positive licensing fee and the software firm produces software and earn positive profits. As γ increases, the hardware firm’s profits could increase in γ. For a large γ, the software producer earns zero profits and the licensing fee becomes negative. As γ further increases, the hardware firm prefers not to subsidize the software firm, i.e., it only sells hardware.
We provide complete analysis in Appendix A.2.
2.4 Piracy and endogenous outsourcing decision
Built on the previous two baseline analyses, we now allow the hardware firm to control how much of the software they produce in-house (δ) and how much they outsource (1 − δ). The hardware firm sets the price of the hardware (ph), the proportion of software developed in house (δ), and the licensing fee (f ). The software firm sets the price of the software (ps).
From the analyses in the two baseline cases, we know that when the cost of developing software is large and/or when piracy is too high, the hardware firm prefers to sell only hardware. This intuition still holds in the current scenario. Because our goal is to study the effect of piracy on the outsourcing decision and not on when the hardware firm should sell only the hardware, we focus on the interior solution in the current scenario. Unless otherwise noted, we assume that the costs of software development (Ch, Cs) are sufficiently small that firms prefer to produce software.
We start with the software firm’s problem. As we will see below, the software firm’s equilibrium software pricing will be identical to the Full Outsourcing case. Given (δ, f), the software firm’s problem is
The first-order condition with respect to ps is the same as before, and gives
Plugging these into πs, we get
The profits for the hardware firm consists of three elements: hardware profits (\(\pi _{h}^{hw}\)), profits from licensing fees for outsourced software (\(\pi _{h}^{sw,out}\)), and in-house software profits (\(\pi _{h}^{sw,in}\)). The profit function of the hardware firm is
The hardware firm maximizes the profits by choosing the price of hardware (ph), licensing fee (f ), and proportion of in-house software (δ). First, consider the hardware price. The first-order condition with respect to ph does not involve other endogenous variables (f and δ), and the optimal ph can be obtained as
The first-order conditions for f and δ are
First, the first-order condition with respect to f gives
Equation 24 implies that the optimal licensing fee is positive, and this is because we focus on the interior solution. Also, note that for any δ, f is uniquely determined. To see this, notice that
The above inequality also implies that as the proportion of in-house software increases, the licensing fee goes down. To see this intuitively, note that the marginal return from f for outsourced software profit \(\left (\frac {\partial \pi _{h}^{sw,out}}{\partial f}\right )\) and that for in-house software profit \(\left (\frac {\partial \pi _{h}^{sw,in}}{\partial f}\right )\) are
The first-order condition with respect to f requires \(\frac {\partial \pi _{h}}{\partial f}=\frac {\partial \pi _{h}^{sw,out}}{\partial f}+\frac {\partial \pi _{h}^{sw,in}}{\partial f}=0\). Also, as Eq. 24 implies that the optimal f is strictly positive for δ > 0, the marginal return from f for in-house software is strictly negative (i.e., \(\frac {\partial \pi _{h}^{sw,in}}{\partial f}<0\)). The negative marginal return is because when the licensing fee increases, it increases the price, which decreases the demand. Thus, the profit from in-house software also decreases. These two observations suggest that at the optimal f, the marginal return from f for outsourced software is strictly positive (i.e, \(\frac {\partial \pi _{h}^{sw,out}}{\partial f}>0\)). Thus, if the hardware chooses to increase the proportion of in-house software, then it should lower the licensing fee so that it increases the return from additional in-house software.
Now, substituting the expression for the optimal f (Eq. 24) into the first-order condition for δ, we get
This condition characterizes the optimal δ. The analytical solution is complicated and multiple solutions could exit. However, we can get intuitions implicitly. The marginal revenue in Eq. 25 is a convex function of δ on [0,1], and the marginal cost is linear in δ. Figure 2 shows a graphical representation of condition (25).
We plot the marginal revenue for four different values of γ (the convex curves labeled as \(MR_{1},\dots ,MR_{4}\)), and a line for the marginal cost over δ. As γ increases, the marginal revenue curve shifts down (from MR1 to MR4). Depending on the value of γ, the number of solutions to Eq. 25 is given as
First, when \(\gamma <1-\frac {128C_{h}}{27\bar {\alpha }^{2}}\), the marginal revenue is greater than the marginal cost for all δ. Thus, we have a corner solution that corresponds to the Full Integration case (δ = 1). In other words, when γ is very small, the loss of in-house software profits due to piracy is so small that the hardware firm prefers to produce all software in-house (note that the per-software profits when outsourcing is (p(s) − f)Qs, which is smaller than piQi unless f = 0). For \(\gamma \ge 1-\frac {128C_{h}}{27\bar {\alpha }^{2}}\), we have at most two solutions. For example, MR3 intersects the marginal cost line twice (points a and b in Fig. 2). However, we can show that solution b (\(\delta >\frac {2}{3}\)) is a saddle point, and thus the optimal proportion of in-house software (δ) is less than or equal to \(\frac {2}{3}\) (we provide the second-order condition in Appendix A.3).
Furthermore, it is easy to see that as the marginal revenue shifts down (due to a higher γ), the optimal δ decreases (point a shifts to the left). Thus, we have \(\frac {\partial \delta }{\partial \gamma }<0\) for \(\delta <\frac {2}{3}\). This can also be shown by multiplying both sides of Eq. 25 by (2 − δ)2 and differentiating with respect to γ:
Finally, MR4 shows the situation where γ is too high that the software firm’s profits, πs(δ, f), just become zero. To see this, notice that
Thus, the marginal revenue in Eq. 25 corresponds to the software firm’s per-software gross profits. In order to ensure πs(δ, f) ≥ 0, the marginal revenue curve in Fig. 2 has to be above or equal to the line \(\frac {C_{s}(1-\delta )}{2}\) at the optimal δ. In other words, if γ is too high that the marginal revenue curve moves below MR4, the constraint πs(δ, f) ≥ 0 and the first-order condition \(\frac {\partial \pi _{h}}{\partial \delta }\) cannot be satisfied simultaneously. Thus, the optimal δ has the lower-bound which is given by \(C_{h}\delta =\frac {C_{s}(1-\delta )}{2}\), or \(\delta =\frac {C_{s}}{2C_{h}+C_{s}}\). The upper-bound of γ can be simply computed as \(\gamma =1-\frac {4(4C_{h}+C_{s})^{2}C_{h}C_{s}}{(2C_{h}+C_{s})^{3}\bar {\alpha }^{2}}\).
The following Proposition 3a summarizes the main results of the endogenous outsourcing scenario when γ is not too low or too high (we provide details in Appendix A.3).
Proposition 3a
When\(\gamma \in \left [1-\frac {128C_{h}}{27\bar {\alpha }^{2}},1-\frac {4(4C_{h}+C_{s})^{2}C_{h}C_{s}}{(2C_{h}+C_{s})^{3}\bar {\alpha }^{2}}\right ]\), the hardware firm will outsource part of the production to the software firm. In particular, there exists a unique optimal strategy\((p_{h}^{*},f^{*},\delta ^{*})\)by the hardware firm that satisfies
Moreover, the optimal δ∗lies on the interval\(\left [\frac {C_{s}}{2C_{h}+C_{s}},\frac {2}{3}\right ]\). Under this optimal strategy, we have
That is, as piracy increases, the hardware firm will use more outsourcing for the production of software.
One remark for Proposition 3a is that the range, \(\left [\frac {C_{s}}{2C_{h}+C_{s}},\frac {2}{3}\right ]\), is non-empty only when Cs ≤ 4Ch. This condition also ensures that the range of γ, \(\left [1-\frac {128C_{h}}{27\bar {\alpha }^{2}},1-\frac {4(4C_{h}+C_{s})^{2}C_{h}C_{s}}{(2C_{h}+C_{s})^{3}\bar {\alpha }^{2}}\right ]\), is non-empty. In other words, if Cs > 4Ch, there is no interior solution.
Now what will happen to \(\frac {\partial \delta }{\partial \gamma }\) when \(\gamma >1-\frac {4(4C_{h}+C_{s})^{2}C_{h}C_{s}}{(2C_{h}+C_{s})^{3}\bar {\alpha }^{2}}\)? For this range of γ, the software firm earns zero profits and thus the optimal δ is chosen at the intersection of the marginal revenue curve and the line \(\frac {C_{s}(1-\delta )}{2}\) in Fig. 2. The question is whether the marginal revenue curve shifts up or down as γ goes up. If it shifts up, then δ will decrease in γ. If it shifts down, then δ will increase in γ. Note that the marginal revenue can be implicitly written as \(\frac {(\bar {\alpha }(1-\gamma )-f(\delta ;\gamma ))^{2}}{4(1-\gamma )}\) (for the interior solution above, we had \(f(\delta ;\gamma )=\frac {\bar {\alpha }(1-\gamma )(1-\delta )}{2-\delta }\)). The Full Outsourcing scenario suggests that as γ increases, the licensing fee will compensate the loss in the software firm’s profits to some extent, but not to the extent that the software firm’s per-software gross profits increases. Thus, we expect that the marginal revenue curve shifts down, and thus δ increases in γ. The following Proposition 3b summarizes the result for corner solutions (we provide details in Appendix A.5).
Proposition 3b
When\(\gamma <1-\frac {128C_{h}}{27\bar {\alpha }^{2}}\), we have a corner solution where the hardware firm will prefer to produce all software in-house (Full integration). When\(\gamma >1-\frac {4(4C_{h}+C_{s})^{2}C_{h}C_{s}}{(2C_{h}+C_{s})^{3}\bar {\alpha }^{2}}\), we have another corner solution where πs = 0. The optimal strategy\((p_{h}^{*},f^{*},\delta ^{*})\)is unique, and the hardware firm will decrease outsourcing as γincreases, i.e., \(\frac {\partial \delta }{\partial \gamma }>0\).Footnote 5
In summary, the analysis of the main scenario shows that when piracy is intermediate, an increase in piracy leads to more outsourcing. However, when piracy is too high to subsidize the software firm, the hardware firm will reduce outsourcing and increase in-house production. In the next section, we will examine the robustness of the main result to different modeling assumptions.
3 Extensions
In this section, we explore boundary conditions for the main result on the outsourcing decision by assessing the implications of modeling assumptions.
3.1 When hardware does not provide benefits absent software (v = 0)
In our main model, we assumed that consumers derive benefits from the hardware absent software and we capture this via a positive constant v in the utility function. This assumption is reasonable for markets such as smart phones, video game consoles, etc., but may not hold for other markets such as DVD or Blue-ray player markets where hardware is completely useless absent software. We thus examine the implication of this assumption for the effect of software piracy on the outsourcing decision below.
We first note that v has an important implication for the relationship between piracy and the hardware firm’s profits. A positive v allows the hardware firm to charge more on the hardware, and it helps the hardware firm to stay in the market even when piracy becomes high. Another important implication is that v influences how the profits from hardware change with piracy. To see this, recall the Full Integration case. In Eq. 10, it is easy to see that when \(\gamma \ge \frac {v}{\bar {\alpha }}\), the change in the hardware firm’s profit due to an increase in piracy is
When v > 0, the change is negative. However, when v = 0, the hardware firm’s profit becomes independent of γ. In other words, the additional hardware profit due to an increase in piracy is exactly offset by the reduced software profit.
However, as it can be seen from the analysis in Section 2.4, our key result on the effect of piracy on the outsourcing decision (Propositions 3a and 3b) remains unchanged even when v = 0. This is because the role of v is limited only in hardware pricing and thus has no impact on the outsourcing decision. Because of this, in the following extensions, we assume that v = 0.
3.2 When pricing of in-house software is done by the hardware firm
In the main scenario with endogenous outsourcing, we assumed that all software pricing, including in-house software, is done by the software firm, and that in-house and outsourced software prices are identical. This assumption was partly motivated by the observation that when in-house and outsourced software provide the same utility, they should be priced identically. However, even when in-house and outsourced software provide the same utility, they can be highly differentiated and do not compete directly. Under such a situation, in-house and outsourced software can be priced differently by the hardware and software firms, respectively. In order to see whether the assumption on who sets the price of in-house software is crucial for our key result, we examine a model where in-house software pricing is done by the hardware firm. We keep all other aspects of the model from Section 2.4 (except that we now assume v = 0).
We start by discussing the change in consumers’ purchase decisions. When in-house and outsourced software are priced differently, there will be a segment of consumers who buy one of the software type and pirate the other. Thus, we modify consumers’ utility functions as follows (for v = 0). Let pi and ps be the price of in-house and outsourced software, respectively. Then,
For example, when outsourced software is more expensive than in-house software (i.e., ps > pi), there will be four segments of consumers in terms of purchase patterns: (1) those who buy both in-house and outsourced software (b, b), (2) those who buy in-house software but pirate outsourced software (b, p), (3) those who pirate both in-house and outsourced software (p, p), and (4) those who do not buy hardware. We note that there is no segment of consumers who buy outsourced software but pirate in-house software. We can show the utility from this purchase pattern is dominated by one of the above purchase patterns for all α.
Given the segments of consumers who buy, the per-software demand for in-house and outsourced software can be written as
The software firm’s problem remains unchanged. The hardware firm’s profit now becomes
The only difference from the main analysis is that the marginal revenue from additional in-house software is now a function of the price of in-house software, not the licensing fee. Solving the hardware firm’s profits given the constraints we had before, we obtain the following proposition for an intermediate γ (interior solution):
Proposition 4a
When\(\gamma \in \left [1-\frac {8C_{h}}{\bar {\alpha }^{2}},1-\frac {8C_{h}C_{s}}{(C_{h}+C_{s})\bar {\alpha }^{2}}\right ]\), there exists a unique optimal strategy\((p_{h}^{*},p_{i}^{*},f^{*},\delta ^{*})\)by the hardware firm:
It is then immediate that as piracy increases, the hardware firm will use more outsourcing for the production of software.
The proof is provided in Appendix A.5. Proposition 4a confirms that our key result on the outsourcing decision is robust to the change in the assumption on who prices in-house software. To see why the proportion of in-house software decreases with γ, consider the first-order condition with respect to δ:
The hardware firm earns more from in-house software than from outsourced software because it does not fully capture the profits of the outsourced software. However, the impact of γ on in-house software is larger (in an absolute term) than that on licensing fee profits. As a result, as γ increases, the hardware firm will shift software production from in-house to outsourcing.
When γ is too low or too high, we have similar results to the main analysis (see Appendix A.6).
Proposition 4b
When\(\gamma <1-\frac {8C_{h}}{\bar {\alpha }^{2}}\), we have a corner solution where the hardware firm will prefer to produce all software in-house (Full integration). When\(\gamma >1-\frac {8C_{h}C_{s}}{(C_{h}+C_{s})\bar {\alpha }^{2}}\), we have another corner solution where πs = 0. The optimal strategy\((p_{h}^{*},f^{*},\delta ^{*})\)is unique, and the hardware firm will decrease outsourcing as γ increases, i.e., \(\frac {\partial \delta }{\partial \gamma }>0\).Footnote 6
3.3 Endogenous software variety
Our main analysis on the outsourcing decision in Section 2.4 focused on a situation where the total software variety is predetermined and piracy influences the hardware firm’s decision on the proportion of software developed in-house versus outsourced. In this extension, we examine another interesting and relevant situation where piracy influences the total software variety as well. We extend the previous model in Section 3.2 (i.e., pricing of in-house software is done by the hardware firm) by endogenizing the in-house and outsourced software varieties.
Let ni and ns be the in-house and outsourced software varieties, respectively. As before, we assume that all software provides identical benefits, and thus we have the same price pi for all ni in-house software and ps for all ns outsourced software. Consumers’ buying and pirating decisions are thus similar to the model in Section 3.2, and the utility functions are given as
As before, the per-software demand functions for in-house and outsourced software are given by
Importantly, under the current setup, the marginal consumer who is indifferent between buying and not buying hardware is given by
Thus the demand for hardware depends not only on the price of hardware and piracy (ph, γ) but also on (ni, ns):
The software firm’s problem given the licensing fee is now
The first-order conditions with respect to ps and ns give
We note that the optimal outsourced software variety is proportional to the per-software profits, (ps(f) − f)Qs(f), and decreases as the licensing fee increases.
The hardware firm’s profit is then
As we have discussed, the critical difference from the model with predetermined software variety is the dependency of the hardware demand on the in-house and outsourced software varieties: as ni or ns increases, the demand for hardware increases. When determining the optimal in-house software variety ni, the marginal return on ni consists of not only the additional in-house software profits but also the additional demand for hardware. Also, the licensing fee influences the hardware firm’s profits in two channels: (1) via a change in ns, which affects both the hardware demand and profits from the licensing fee, and (2) via a direct impact on per-software licensing fee profits (i.e., fQs(f)). Since \(\frac {\partial n_{s}}{\partial f}<0\), the former is negative, but the latter is positive for \(f<\frac {\bar {\alpha }(1-\gamma )}{2}\) (which is the optimal licensing fee under the exogenous software variety in Section 3.2). Thus, the hardware firm will balance these two forces to determine the optimal licensing fee.
We now present our results.
Proposition 5
For γ ∈ (0, 1), there exists a unique optimal strategy\((p_{h}^{*},p_{i}^{*},f^{*},n_{i}^{*})\)by the hardware firm.
- 1.
Licensing fee: There exists a\(\gamma _{1}\in (\frac {1}{2},1)\)such that\(\frac {\partial f^{*}}{\partial \gamma }\le 0\)for γ ∈ (0, γ1] and\(\frac {\partial f^{*}}{\partial \gamma }>0\)for γ ∈ (γ1, 1). When\(\gamma >\frac {1}{2}\), f∗ < 0.
- 2.
In-house software variety:\(\frac {\partial n_{i}^{*}}{\partial \gamma }=0\)for\(\gamma \in (0,\frac {1}{2}]\)and\(\frac {\partial n_{s}^{*}}{\partial \gamma }<0\)for\(\gamma \in (0,\frac {1}{2})\).
- 3.
Outsourced software variety:\(\frac {\partial n_{i}^{*}}{\partial \gamma }<0\)for γ ∈ (0, 1).
- 4.
Proportion of outsourced software (\(\frac {n_{s}^{*}}{n_{i}^{*}+n_{s}^{*}}\)) decreases in γ for all γ ∈ (0, 1).
- 5.
The hardware and software firms’ profits decrease in γ for all γ ∈ (0, 1).
The proof is provided in Appendix A.7. First, we note that when the software varieties are endogenous, both the hardware and software firms can optimally adjust the varieties to avoid a negative profit. As a result, the market will not break down even when γ is high.
Now the important difference from the previous result is that outsourcing decreases in γ for all γ. Both in-house and outsourced software varieties are (weakly) decreasing in γ, but the declining rate for the outsourced software variety is larger. In the limit where γ goes to one, the outsourced software variety approaches zero while the in-house software variety approaches a positive value. The former is because the software firm earns profits only from software, so as γ approaches one, the sales of outsourced software approaches zero. As a result, it cannot finance to develop any software. However, the hardware firm earns profits from hardware as well. Thus, even when γ is close to one so that the sales of in-house software is close zero, the hardware firm has an incentive to develop in-house software for “pirates” who will pay for hardware. Thus, the in-house software variety does not approach zero.
The above intuition highlights the main difference from the previous analyses with predetermined total software variety. When software variety is independent of piracy and the outsourcing decision is all about who makes the predetermined variety, the hardware firm will choose the decision purely based on the marginal return on software. As we argue above, when piracy is intermediate, piracy reduces the marginal return on in-house software more than the return on outsourced software and thus the hardware firm will increase outsourcing. However, when software variety is endogenous and changes with piracy, the marginal return on in-house software depends also on the return on hardware profits. As a result, the hardware firm will have an incentive to keep the in-house production even when piracy becomes severe.
We can also show that the results in Proposition 5 does not depend on who sets ns. In the above analysis, we assume that ns is set by the software firm. Alternatively, we can assume that both ni and ns are controlled by the hardware firm.Footnote 7 Under this assumption, the hardware firm’s marginal return on ns is always positive and thus we only get a corner solution where the software firm earns zero profits. Similar to the analysis above, the optimal ns will be proportional to the per-software profits earned by the software firm (i.e., (ps − f)Qs), and the results remain unchanged.
3.4 Proportional licensing fee
This extension examines the licensing fee structure. Our previous models assume that the licensing fee is charged per unit of software sold. However, in some platform markets, the licensing fee is proportional to software revenue. For example, Apple charges a 30% commission on application developers. We thus extend the previous models by assuming that the licensing fee is proportional to the revenue of outsourced software. Below we conduct this analysis under the endogenous software variety setting, and discuss the analysis under the exogenous software variety setting in Appendix A.8.
The software firm’s profit is now modified as
where f ∈ [0,1] is the proportion of the outsourced software revenue taken by the hardware firm.Footnote 8 As before, we assume that f is chosen by the hardware firm. Since the optimal price of outsourced software now does not depend on the licensing fee, it will be simply
The outsourced software variety is then
Notice that the optimal variety is proportional to the licensing fee.
The hardware firm’s profit is then
The following proposition summarizes the results (The proof is provided in Appendix A.8).
Proposition 6
For γ ∈ (0, 1), there is a unique optimal strategy (\(p_{h}^{*},p_{i}^{*},f^{*},n_{i}^{*}\)) by the hardware firm. Under this optimal strategy,\(n_{i}^{*}\)is independent of γ for all γ ∈ (0, 1) while\(n_{s}^{*}\)is independent of γ for\(\gamma \in (0,\frac {1}{2}]\)and decreasing in γ for\(\gamma \in (\frac {1}{2},1)\). Thus, the proportion of outsourced software is weakly decreasing in γ.
Proposition 6 states that ni is now independent of γ even when \(\gamma >\frac {1}{2}\). This is mainly because under the proportional licensing fee, the demand for outsourced software is independent of γ (always \(\frac {\bar {\alpha }}{2}\)). Thus, even when γ becomes high, the constraint on Qh ≥ Qs is always satisfied. Thus, the optimal ni will not change from low γ to high γ. Furthermore, we find that ns is independent of γ when \(\gamma \le \frac {1}{2}\). This is because the optimal ns is now proportional to f and the impact of piracy on ns completely cancels out with the impact of piracy on f.
Overall, the model with a proportional licensing fee suggests that the proportion of outsourced software is constant when γ is low, but is decreasing in γ when γ is high. Thus, the overall pattern is consistent with the finding of Proposition 5.
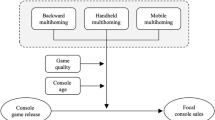
4 Empirical investigation
Our theoretical examination shows that the degree of outsourcing can go up or down with piracy, depending on the level of piracy and whether total software variety is influenced by piracy or not. We thus resort to an empirical investigation in order to gain more insights about the outsourcing decision. The empirical context is the U.S. handheld video game market between 2004 and 2012. Video game markets are a canonical example of two-sided markets in which software firms interact with consumers through platforms (video game consoles/handhelds) (Clements and Ohashi 2005; Dubé, Hitsch, and Chintagunta 2010; Chao and Derdenger 2013; Derdenger and Kumar 2013; Lee 2013; Derdenger 2014). During the sample period, the handheld market was dominated by two major platforms: Nintendo DS (NDS), released in November 2004 by Nintendo, and Sony PlayStation Portable (PSP), released in March 2005 by Sony Computer Entertainment.Footnote 9
These two platforms provide a novel empirical setting for investigating software piracy and outsourcing. First, software titles on NDS and PSP are developed by both the hardware firm (Nintendo/Sony) and third-party software firms (e.g., Activision Blizzard, Electronic Arts, Square Enix).Footnote 10 Thus, we can examine the extent to which software titles are developed in-house versus outsourced. Second, these platforms are known to have suffered from software piracy significantly (Fukugawa 2011). According to a study conducted by Computer Entertainment Suppliers Association in Japan in 2010, the estimated total revenues lost due to software piracy on NDS and PSP is $41.7 billion from 2004 to 2009 worldwide.Footnote 11 The significant effect of piracy was mainly because of the devices that easily make illegally downloaded software playable on NDS and PSP. For NDS, a small device called the Revolution for DS (R4) made hacking possible. It is a cartridge that can be inserted into NDS and allow downloaded ROMs to be booted on NDS from a microSD card. For Sony PSP, hacking was made possible via a Pandora battery and a Magic Memory Stick. In response to the popularity of the R4 cartridge, Nintendo eventually took a legal action. However, Sony did not take any legal action.
4.1 Data
We first describe the empirical measures used for our empirical examination. Our goal is to examine the effect of software piracy on the proportion of outsourced software. We collected data on measures for (1) the proportion of outsourced software (dependent variable), (2) the ease of software piracy (key independent variable), and (3) control variables. The unit of our analysis is (platform, month), and our sample size is 172.Footnote 12 In what follows, we will explain each set of measures.
4.1.1 Measure for the dependent variable
To measure the extent to which software is developed in-house versus outsourced, we obtain data from NPD on all software titles released on NDS and PSP from their inception to February 2012. For each software, we use its publisher identity for grouping software into in-house (when the publisher is the platform provider) and outsourced (when the publisher is a third-party software provider).Footnote 13 For NDS, 1,777 software titles are released during the sample period, and 109 titles (6.1%) are by Nintendo (i.e., in-house). Examples of top selling in-house software titles include New Super Mario Bros., Mario Kart DS, and Pokémon Diamond Version, and examples of top selling outsourced software include Guitar Hero on Tour Bundle (by Activision Blizzard), Lego Star Wars: The Complete Saga (by LucasArts), and Cooking Mama (by Majesco Entertainment). For PSP, we observe 626 titles and 77 of them (12.3%) are by Sony. Examples of in-house software include God of War: Chains of Olympus, SOCOM U.S. Navy SEALs: Fireteam Bravo, and Ratchet & Clank: Size Matters, and examples of outsourced software include Grand Theft Auto: Liberty City Stories (by Take-Two Interactive), Need for Speed: Most Wanted (by Electronic Arts), and Star Wars: Battlefront II (by LucasArts).
Our key dependent variable is the proportion of outsourced software. Table 1 presents summary statistics on the number of newly released software and the degree of outsourcing for NDS and PSP. We compute the measure for the dependent variable using the number of newly released software in a given month. Since software can be released at the beginning or at the end of the month, we use the two-month average number. This operation also helps us deal with a situation in which there is no software release in a given month (in which case, the proportion of outsourced software cannot be computed).Footnote 14 The average number of newly released software is 15.1 per month for NDS and 6.94 per month for PSP. The average number of outsourced software is 14.0 (89.0% of all software) for NDS and 6.0 for PSP (85.7%).
The left panel of Fig. 3 plots the monthly number of newly released software over time. For NDS, it starts low and increases up to 2007. After that, it fluctuates significantly but the trend is relatively stable around 15-20 game titles. For PSP, the trend up to 2007 is similar to NDS except that the first-month number for PSP is high. After 2007, it decreases slightly and becomes stable around 5 game titles per month. The right panel shows the monthly proportion of outsourced software over time. For NDS, in the early lifecycle, it is relatively low and fluctuates significantly, and then increases and becomes stable. However, for PSP, it is relatively stable over time. Notice that in both panels, part of the fluctuations might be due to seasonality (especially for the number of newly released software, because more games might be released during the holiday season). Thus, we will include month fixed effects as controls to account for such variation.
4.1.2 Measure for the key independent variable
The key independent variable of our regression analysis is the ease of piracy. In the theoretical model, we operationalize it as the deteriorated quality of software relative to a legal version (γ). The deteriorated quality may be due to a variety of reasons, but one such factor is the cost of using pirated software. For NDS and PSP, in order to play illegally downloaded games, consumers need to know how to use the device (R4 for NDS and Pandora battery for PSP) for hacking the system of the handheld devices. Since this is an illegal act, most consumers search information online and find out how-to. Such information is initially spread and shared only among hardcore hackers. But what was unique about NDS and PSP software piracy is that the device made hacking so popular and accessible to regular gamers that the information on the device became widely spread online.Footnote 15 As more websites appear and explain how to use the device, the cost of using pirated software decreases. In other words, we could use the volume/accessibility of online information as a proxy for the ease of using pirated software.
In our regression analysis, we use Google Trends’ search volume to approximate the accessibility of online information on how to use the device.Footnote 16 Since Google Trends is a result of consumers’ interest in a certain keyword, it may not exactly match with the information accessibility. Thus, our key identification assumption is that as more information becomes available, the chance of finding information becomes higher. As a result, the search volume increases. Under this assumption, consumers’ interest in the device (as captured by Google Trends) will capture variation in the accessibility of information on how to use the device.
Specifically, we use the term “ds r4” and “psp pandora battery” as the search keywords for NDS and PSP, respectively.Footnote 17 We made the inquiry separately and obtain the monthly search volume over our sample period using the U.S. as the specified region. The value of the search volume is scaled on a range of 0 to 100 (by Google). Since we retrieved data separately for NDS and PSP, both series will have 100 as the peak search volume value. Thus the comparison of the search volume between NDS and PSP is meaningless, and only the time-series variation within each series matters. In our regression, we include the platform fixed effect as a control for adjusting the level effect.
Figure 4 shows the search volume for “ds r4” (left panel) and “psp pandora battery” (right panel) over the sample period. In addition to the search volume in the U.S., we plot the search volume restricted to Japan (in Japanese equivalent of the keywords). As we will explain below, the search volume obtained from Japan will be used as an instrument in our regression. The search volume for NDS is essentially zero for about two years after NDS release (until November 2006), and increases sharply during 2007. In this year, NDS software piracy became a serious issue for software firms and some software firms started embedding a code in software that prevents pirates from playing an illegally downloaded version.Footnote 18 However, such a prevention code was often cracked by hackers a few days after release, and it never became a real solution. In July 2008, Nintendo filed a lawsuit in Japan against companies that sell the R4 cartridge and Tokyo District Court ruled against the distribution of the R4 cartridge in February 2009. This coincides with a significant decline in the search volume in Japan. In the U.S., the legal action was not taken during our sample period, which is consistent with the longer lasting U.S. search volume.
We observe similar patterns for PSP. The search volume is zero until July 2007, and sharply increases in the rest of 2007. The trend happened in Japan slightly earlier than in the U.S. Sony, instead of taking a legal action, constantly introduced system software updates as well as new hardware models that embed better protection against piracy.
4.1.3 Control variables
In order to control for other factors that might influence the proportion of outsourced software, we collect additional data and generate control variables. First, we obtain data from NPD on monthly hardware unit sales for NDS and PSP from their inception to February 2012. We then compute the cumulative number of hardware unit sales and include this variable to control for the effect of platform lifecycle on the dependent measure. We plot the cumulative hardware sales over time in the left panel of Fig. 5. Overall, the difference between NPD and PSP was small in the beginning, but gets wider as time goes on. A periodic jump is due to the Christmas seasonal effect. As we discussed above, platform’s lifecycle could play an important role in influencing the proportion of in-house versus outsourced software. At the beginning of the lifecycle, third-party software firms may be skeptical about the success of a new platform. Moreover, the cost of developing software for a new platform may be high because programmers may not be familiar with the development environment for making software for the new platform. As time goes on, if the platform turns out to be a success (which is captured by a large number of cumulative hardware sales), software firms will have more incentive to release software on the platform.
Second, we obtain monthly occurrence data on system software update releases for both NDS and PSP. System software is similar to an operating system in computer, and controls all functionalities available on a handheld device. System software updates are not necessarily targeted against software piracy (e.g., fixing known bugs, adding new features to the device), but can also be used for embedding piracy protection features. The right panel of Fig. 5 shows the cumulative number of system software updates over time for NDS and PSP. As we mentioned earlier, Sony was active in providing updates for improving piracy protection but Nintendo was not.
If software firms expect new system software updates by a platform in a given month, and if the updates are related to piracy protection, they may align the introduction of a software title with the system software updates. Thus we include monthly system software updates as a control variable.Footnote 19
Finally, as we discussed above, we include month fixed effects to control for popular months for introducing software. Since we have only two platforms, we are not able to control for calendar time fixed effects. We tried specifications with year fixed effects but found that they are highly correlated with the (logged) cumulative hardware sales and created a multicollinearity issue. Thus, we dropped year fixed effects.
4.2 Results
4.2.1 Piracy and the proportion of in-house software
Our econometric model is
where the subscripts i and t index platform and time, yit is a measure for the proportion of outsourced software, Git is Google Trends’ search volume for hacking devices (a proxy for the ease of piracy), Xit is a vector of observed controls (logged cumulative hardware sales, system software updates, and month fixed effects), μi is a platform fixed effect, and 𝜖it is an error term. Our main parameter of interest is α, the effect of piracy on the proportion of outsourced software.
The key econometric issue in estimating the above model is that Git and 𝜖it may be correlated. For example, it is possible that Google Trends U.S. search volume may be correlated with a new release of popular games in the U.S. That is, when a popular game is released, consumers might search for information about hacking device so that they can play it for free illegally, which makes the search volume endogenous. While popular games can be in-house or outsourced software, our data show that in-house software tends to be more popular: the average total unit sales of in-house games is higher than that of outsourced games, for both NDS (932K units for in-house versus 119K for outsourced) and PSP (200K for in-house versus 126K for outsourced). We thus estimate the model using the Two-Stage Least Squares. We use Google Trends Japan’s search volume for hacking devices (in Japanese) as an instrument for the U.S. measure. As we saw in Fig. 4, these two measures are highly correlated. Also, because the set of video games available and released in Japan in a given month are different from those in the U.S., we expect that Google Trends Japan’s search volume is uncorrelated with the error term.Footnote 20
We report the parameter estimates of the model in Table 2. We estimated six models that differ in the set of independent variables. For all the specifications, we compute the standard errors based on the heteroskedasticity- and autocorrelation-consistent (HAC) variance estimates (Newey and West 1987) with the Bartlett kernel and the bandwidth of two. Also, in order to check the validity of the instruments, we report the first-stage F-statistic of excluded instruments. The F-statistics suggest that our instruments are not weak (Staiger and Stock 1997).
Model 1 includes Google Trends U.S. search volume, logged cumulative hardware sales, platform and month fixed effects. We find that the search volume has a positive and significant effect on the proportion of outsourced software, indicating that higher ease of piracy increases the proportion of outsourced software. The (logged) cumulative hardware sales has a positive and significant effect, suggesting that we see more outsourced software in the later platform lifecycle. This result is consistent with our earlier discussion that platform providers might have an incentive to introduce in-house software to boost hardware sales in the early platform lifecycle. Also, software firms may have more incentive to introduce software to a platform with a larger customer base. Model 2 adds the monthly number of system software updates. The effect of the search volume continues to be positive and significant. We find that the monthly number of system software updates has a positive effect on the proportion of outsourced software, but not significant. The sign is consistent with our discussion above that software firms might find it profitable to align their software release with the timing of system software updates.
In Models 3-6, we repeat the same analysis by using either 6-month or 12-month lagged value of the three independent variables. Due to production lead time, product development decisions are typically made prior to the actual release date. As a result, the dependent variable observed in a given month could be a function of the past values of independent variables (i.e., the information available at the time of making the development decision). Because we do not observe exactly when the product development decision was made, we try 6-month and 12-month lagged values.Footnote 21 These time windows are reasonable for NDS and PSP because handheld games tend to be of small read-only memory (ROM) capacity that do not require a long development period. While typical PC or console games take about one to three years to complete, the development time for handheld games is similar or slightly longer than mobile game development, which can be a few months.Footnote 22 Note that for these models, the potential endogeneity issue may be less severe because the decision to develop a popular in-house game may not always be observed by consumers. However, it is still possible that video game publishers make a new game release preannouncement, and consumers who observe it may still search for the hacking device to get prepared for the actual release date. Thus, we continue to use the Google Japan’s search volume as an instrument (lagged either 6 or 12 months). The results for Models 3-6 are largely consistent with our previous findings.
We add a remark for the result. It is possible that the positive effect of piracy on the proportion of outsourced software may be due to reverse causality. That is, when the hardware firm has more in-house software, it may have more incentive to monitor piracy and invest in reducing piracy, leading to a positive correlation between piracy and the proportion of outsourced software. While we cannot completely rule out this possibility using our data, we argue that institutional details in the handheld video game market may help mitigate this concern. First, in this market, software piracy became a serious issue around the end of 2006 and this is mainly due to the diffusion of new hacking devices (the R4 cartridge and the pandora battery). The diffusion was rather unexpected news to Nintendo and Sony, and the low piracy prior to the end of 2006 is not mainly driven by high piracy protection. Moreover, Nintendo did not take any legal action to fight against piracy until July 2008, which is more than a year and a half after the emergence of the hacking devices.Footnote 23 By that time, the proportion of in-house software was pretty low, and thus the legal action taken by Nintendo does not seem to be driven by the need to protect in-house software against piracy. Thus, at least in this market it seems less likely that a high proportion of in-house software led to low piracy.
4.2.2 Piracy and the total software variety
Overall, our empirical analysis shows that the effect of piracy on the proportion of outsourced software is positive. This result is in line with the theoretical prediction derived from the model with predetermined software variety and when piracy is intermediate (i.e., the software firm’s profits are not zero). To further investigate this, we conduct another regression analysis and directly examine whether the model assumption itself is consistent with the data pattern in the U.S. handheld video game market. Our key parameter of interest is the effect of piracy on the total software variety. The idea behind the model with predetermined software variety is that piracy influences the outsourcing decision but not the software variety decision. In contrast, the model with endogenous software variety allows both the software variety and the outsourcing decision to depend on piracy. Thus, when taking the theoretical models to the data, what is important is not whether the total software variety itself changes over time, but whether the total software variety changes with piracy. The model with predetermined software variety predicts no change, while the model with endogenous software variety predicts a negative effect of piracy.
Table 3 shows the estimation results. Similar to Table 2, we include the Google Trends’ search volume, logged cumulative hardware sales, software updates, and platform and month fixed effects. We note that the previous concern about the endogeneity of the Google Trends’ search volume applies here again: when more games are released (or announced to be released), consumers might search for information about how to use hacking devices. Thus, we continue to use the Google Trends’ search volume from Japan as an instrument.
Throughout the six models in Table 3, we consistently find that the effect of piracy is not significant. Also, the effect of the logged cumulative hardware sales is positive and significant. Additional analyses that examine in-house and outsourced software varieties separately reveal that the reason for the non-significant effect mainly comes from the non-significant effect of piracy on outsourced software variety: piracy has a negative and significant impact on the monthly number of newly released in-house software, but has no effect on the monthly number of newly released outsourced software. Together with the earlier result on outsourcing, in the U.S. handheld video game market, the data pattern supports the theoretical prediction from the model with exogenous software variety. However, we note that our empirical results are based only on this market and may not hold in other platform markets. For example, more empirical evidence is needed to fully understand how the relationship between piracy and the outsourcing decision changes with specific platform characteristics. We leave this for future research.
5 Discussion and conclusion
In this paper we examine the role of software piracy in the outsourcing decision of a platform provider. In particular, we look at a hardware producer such as Sony, that has to make a software outsourcing decision, that is how many games to produce in-house, and how many to outsource from a third-party software provider, where the games are routinely pirated, and that level of piracy has to be taken into account in the outsourcing decision. In such markets, there is a built-in tension between the hardware and software firms with respect to piracy: As the hardware cannot be pirated, the hardware firm indirectly benefits from piracy (up to a level) since all pirates have to purchase the hardware.
Using a vertical differentiation model, as well as empirical study using data from the U.S. handheld video game market, we find that an increase in piracy increases the level of outsourcing of the hardware provider, as well as increasing its profits. The reason for the increase in outsourcing as a response to increase in piracy occurs because as piracy increases, the loss in in-house software production due to piracy increases. Although the profit margin from in-house software is higher than licensing fees, the platform provider benefits from shifting software profits from in-house to licensing fees because the negative marginal impact of piracy can be reduced.
This main result occurs when the level of piracy is intermediate, between a lower and an upper bound. When the level of piracy is smaller than the lower bound, the hardware firm will prefer to produce all software in-house. When the level of piracy becomes larger than the upper bound, the software firm’s profits vanish, and the hardware firm will be willing to subsidize the software firm by lowering the licensing fee up to a limit of piracy. At this point, an increase in piracy will decrease outsourcing because it is more costly for the hardware firm to subsidize the software firm than to produce in-house.
These results point at a major difficulty for the software producers: In practice, much of the anti-piracy measures are within the realm of the hardware producer. These include measures such as developing new models that prevent modification of hardware (Fukugawa 2011).Footnote 24 However, in intermediate levels of piracy, as piracy becomes more prevalent, the hardware firm’s profits increase, and at the same time it shifts the burden to the software firms by outsourcing more. It has no incentive to stop piracy at these levels. Only when the level of piracy becomes acute (as it did in the US in 2008) do the hardware firm’s incentives align with the software firm so that actions is taken in the form of change of hardware or legal action.
Notes
We thus interpret the piracy parameter in our model as the ease of piracy. See Section 2.
Throughout the paper, we use hardware and platform interchangeably.
Two platforms in our empirical application, Nintendo DS and Sony PlayStation Portable, have this feature. For example, the hardware benefit for Nintendo DS may come from pre-existing software (Rasch and Wenzel 2013) as Nintendo DS is backward-compatible with Game Boy Advance cartridges. Sony PlayStation Portable has a built-in media player that can can play music and video, and an internet web browser.
Since the analytical analysis alone is intractable, we show the result based on a mixture of analytical and numerical analyses.
Once again, we show the result based on a mixture of analytical and numerical analyses.
Note that this is also equivalent to a model where the hardware firm sets the total software variety n and the proportion of in-house software δ (so that ni = nδ and ns = n(1 − δ)).
We focus on non-negative commission rates.
We note that our theoretical model examines a monopoly platform’s decision. Although the empirical application in this section has two platforms, NDS and PSP are highly differentiated from one another. PSP’s target consumer segment was conventional gamers who appreciate high-quality graphics in a portable device, and NDS went after children and casual gamers and offered a new way of playing games with touch screen and pen.
We note that neither Nintendo nor Sony developed software for its rival’s platform.
Our theoretical prediction is based on a static model, but our empirical measures are observed at the monthly level. Although developing a dynamic model is beyond the scope of this paper, we conjecture that our prediction on the outsourcing decision will extend to a dynamic setting. In a dynamic variant of our model, consumers in subsequent periods will have a lower α, which reduces the equilibrium hardware price over time (Nair 2007; Liu 2010). If consumers are forward-looking, they might delay purchase and this will increase α1 in Fig. 1 in period 1. However, as we saw, since the optimal δ is independent of ph at least for an interior solution, we expect that the impact of γ on δ will still remain unchanged.
We note that it is possible that in-house software is developed by an independent software developer and published by a platform provider (see Gil and Warzynski 2015; Ishihara and Rietveld 2017). In this study, we focus on publisher identity because the decision to release a game is made by publishers.
The two-month average number is the average of the values at time t − 1 and t for t > 1. For t = 1 (release month for handheld devices), we simply use that month’s value. Even with this operation, there is one missing value for PSP, and thus the regression uses 171 observations.
In fact, the R4 cartridge for NDS became widely well-known even among primary school children in Japan, and many parents (who do not play video games) did not realize it is illegal and they made inquiries at video game shops as to how to use the R4 cartridge to make downloaded games playable on NDS.
Google Trends (https://trends.google.com/trends/) shows how often a particular keyword is searched relative to the total search volume.
We did not use “nds” because “ds” was a more widely used term for referring to Nintendo DS. For PSP, we did not include a term “Magic Memory Stick,” mainly because it makes the search volume significantly smaller. Also, consumers only need to buy a Pandora battery (Magic Memory Stick can be easily made by downloading software and storing it in a regular Memory Stick).
We also tried adding the cumulative system software updates, but it was not significant and did not affect our main results.
Some video games are released both in the U.S. and Japan, but not necessarily in the same month. Most games have either U.S. or Japan as a primary target market, and based on the performance in the primary market, they may also be released in the other market. Even popular games that are targeted at both markets from the beginning may not be released in the same month. For example, Pokémon Diamond Version, one of the best-selling Nintendo DS games, was released in April 2007 in the U.S., and in September 2006 in Japan.
For observations where the timing of product development decision falls in the pre-release period of a platform (e.g. the decision on games released two months after the platform release), we assume that the cumulative hardware sales and software updates were zero. Also, since piracy was not an issue at all in the early stage of the platforms’ lifecycle, we assume that Google trends’ value was zero for those observations.
We note that Nintendo was aware of the piracy issue in 2007. For example, Nintendo commented in Nov. 2007 that it is “keeping a close eye on the products and studying them” (https://kotaku.com/nintendo-and-54-companies-battle-evil-r4-in-court-5030319).
While software firms tried to embed codes in games that prevented pirates from playing pirated versions, such prevention codes were quickly cracked by hackers and became useless.
For simplicity, we drop some of the constraints that will obviously not bind (e.g., ph, ps ≥ 0).
The upper bound of γ is obtained when the marginal return on δ equals the marginal cost when δ = 1, i.e., \(\frac {\bar {\alpha }^{2}(1-\gamma )}{4}=C_{h}\).
We also have Qh(ph) ≥ Qi(pi), but the latter is always \(\frac {\bar {\alpha }}{2}\) and the former is greater than or equal to \(\frac {\bar {\alpha }}{2}\). Thus the constraint is always satisfied.
References
Chao, Y., & Derdenger, T. (2013). Mixed bunding in Two-Sided markets in the presence of installed base effects. Management Science, 59(8), 1904–1926.
Church, J., & Gandal, N. (1992). Integration, complementary products, and variety. Journal of Economics & Management Strategy, 1(4), 651–675.
Clements, M.T., & Ohashi, H. (2005). Indirect network effects and the product cycle: video games in the U.S., 1994-2002. Journal of Industrial Economics, 53(4), 515–542.
Conner, K.R., & Rumelt, R.P. (1991). Software piracy: an analysis of protection strategies. Management Science, 37(2), 125–139.
Derdenger, T. (2014). Technological tying and the intensity of price competition: an empirical analysis of the video game industry. Quantitative Marketing and Economics, 12(2), 127–165.
Derdenger, T., & Kumar, V. (2013). The dynamic effects of bundling as a product strategy. Marketing Science, 32(6), 827–859.
Dubė, J.-P.H., Hitsch, G.J., Chintagunta, P.K. (2010). Tipping and concentration in markets with indirect network effects. Marketing Science, 29(2), 216–249.
Fukugawa, N. (2011). How Serious is Piracy in the Videogame Industry? Empirical Economics Letters, 10(3), 225–233.
Gil, R., & Warzynski, F. (2015). Vertical integration, exclusivity, and game sales performance in the US video game industry. Journal of Law, Economics, and Organization, 31(1), i143–i168.
Givon, M., Mahajan, V., Muller, E. (1995). Software piracy: estimation of lost sales and the impact on software diffusion. Journal of Marketing, 59(1), 29–37.
Ishihara, M., & Rietveld, J. (2017). The effect of acquisitions on product innovativeness, quality, and sales performance: Evidence from the console video game industry (2002-2010). Working paper.
Jain, S. (2008). Digital piracy: A competitive analysis. Marketing Science, 27 (4), 610–626.
Lahiri, A., & Dey, D. (2013). Effects of piracy on quality of information goods. Management Science, 59(1), 245–264.
Lee, R.S. (2013). Vertical integration and exclusivity in platform and Two-Sided markets. American Economic Review, 103(7), 2960–3000.
Liu, H. (2010). Dynamics of pricing in the video game console market: Skimming or Penetration? Journal of Marketing Research, 47(3), 428–443.
Nair, H. (2007). Intertemporal price discrimination with Forward-Looking consumers: an application to the US market for console Video-Games. Quantitative Marketing and Economics, 5(3), 239–292.
Newey, W.K., & West, K.D. (1987). A simple, positive Semi-Definite, heteroscedasticity and autocorrelation consistent covariance matrix. Econometrica, 55 (3), 703–708.
Peitz, M. (2004). A strategic approach to software protection: comment. Journal of Economics & Management Strategy, 13(2), 371–374.
Rasch, A., & Wenzel, T. (2013). Piracy in a Two-Sided software market. Journal of Economic Behavior & Organization, 88, 78–89.
Rasch, A., & Wenzel, T. (2015). The Impact of Piracy on Prominent and Non-prominent Sofwtare Developers. Telecommunications Policy, 39(8), 735–744.
Rochet, J.-C., & Tirole, J. (2006). Two-Sided Markets: a progress report. RAND Journal of Economics, 37(3), 645–667.
Rysman, M. (2009). The economics of Two-Sided markets. Journal of Economic Perspectives, 23(3), 125–143.
Shy, O., & Thisse, J.-F. (1999). A strategic approach to software protection. Journal of Economics & Management Strategy, 8(2), 163–190.
Sinha, R.K., Machado, F.S., Sellman, C. (2010). Don’t think twice, it’s all right: Music piracy and pricing in a DRM-free environment. Journal of Marketing, 74(2), 40–54.
Staiger, D., & Stock, J.H. (1997). Instrumental variables regression with weak instruments. Econometrica, 65(3), 557–586.
Takeyama, L.N. (1994). The welfare implications of unauthorized reproduction of intellectual property in the presence of demand network externalities. Journal of Industrial Economics, 42(2), 155–166.
Vernik, D.A., Purohit, D., Desai, P.S. (2011). Music downloads and the flip side of digital rights management. Marketing Science, 30(6), 1011–1027.
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Appendix A
Appendix A
1.1 A.1 Proof of Proposition 1
The hardware firm’s problem is formulated as
subject to (1) Qh(ph) ≥ Qs(ps), and (2) \(Q_{h}(p_{h})\le \bar {\alpha }\).Footnote 25 The Lagrangian is then given by
and the Kuhn-Tucker conditions are
We solve this set of inequalities and equations. Below we examine every possible case.
- 1.
When both constraints (1) and (2) are not binding (λ1 = λ2 = 0): This is the case with an interior solution. We have
$$ \begin{array}{@{}rcl@{}} p_{h} &=& \frac{\bar{\alpha}\gamma+v}{2}, p_{s}=\frac{\bar{\alpha}(1-\gamma)}{2}\\ Q_{h} &=& \frac{\bar{\alpha}\gamma+v}{2\gamma}, Q_{s}=\frac{\bar{\alpha}}{4}. \end{array} $$Constraint (1) is satisfied for any γ because v > 0. Constraint (2) implies that \(\gamma \ge \frac {v}{\bar {\alpha }}\), and Assumption 1 (i.e., \(\bar {\alpha }>\sqrt {2}v\)) implies that the range of γ that supports this scenario is non-empty.
With the optimal ph and ps, the hardware firm’s profit is
$$ \pi_{h} = \frac{(\bar{\alpha}\gamma+v)^{2}}{4\gamma}+\frac{\bar{\alpha}^{2}(1-\gamma)}{4}-\frac{C_{h}}{2}. $$Now we check the condition for \(\pi _{h}\ge \bar {\alpha }v\), i.e., the hardware firm prefers to have software. This condition is equivalent to
$$ (\bar{\alpha}^{2}-2\bar{\alpha}v-2C_{h})\gamma + v^{2} \ge 0. $$When \(C_{h}\le \frac {\bar {\alpha }(\bar {\alpha }-2v)}{2}\), \(\pi _{h}>\bar {\alpha }v\) for any γ because v > 0. When \(C_{h}>\frac {\bar {\alpha }(\bar {\alpha }-2v)}{2}\), \(\pi _{h}\ge \bar {\alpha }v\) for \(\gamma \le \frac {v^{2}}{2C_{h}-\bar {\alpha }(\bar {\alpha }-2v)}\). For the latter case to be non-empty, we need \(\frac {v}{\bar {\alpha }}\le \frac {v^{2}}{2C_{h}-\bar {\alpha }(\bar {\alpha }-2v)}\), or \(C_{h}\le \frac {\bar {\alpha }(\bar {\alpha }-v)}{2}\).
In summary, this scenario is supported under the following conditions: (i) \(C_{h}\le \frac {\bar {\alpha }(\bar {\alpha }-2v)}{2}\) and \(\gamma \in \left [\frac {v}{\bar {\alpha }},1\right )\); (ii) \(C_{h}\in \left (\frac {\bar {\alpha }(\bar {\alpha }-2v)}{2},\frac {\bar {\alpha }(\bar {\alpha }-v)}{2}\right ]\) and \(\gamma \in \left [\frac {v}{\bar {\alpha }},\frac {v^{2}}{2C_{h}-\bar {\alpha }(\bar {\alpha }-2v)}\right ]\).
- 2.
When only constraint (2) is binding (λ1 = 0 and λ2 ≥ 0): This is the case with \(Q_{s}(p_{s})<Q_{h}(p_{h})=\bar {\alpha }\) (everyone buys hardware). We have
$$ \begin{array}{@{}rcl@{}} p_{h} &=& v, p_{s}=\frac{\bar{\alpha}(1-\gamma)}{2}\\ Q_{h} &=& \bar{\alpha}, Q_{s}=\frac{\bar{\alpha}}{4}. \end{array} $$Constraint (1) is satisfied for any γ. Since constraint (2) is binding, we need λ1 ≥ 0, which is equivalent to \(\gamma \le \frac {v}{\bar {\alpha }}\). Assumption 1 implies that the range of γ that supports this scenario is non-empty.
With the optimal ph and ps, the hardware firm’s profit is
$$ \pi_{h} = \bar{\alpha}v+\frac{\bar{\alpha}^{2}(1-\gamma)}{4} - \frac{C_{h}}{2}, $$and it is easy to check that \(\pi _{h}\ge \bar {\alpha }v\) for \(\gamma \le 1-\frac {2C_{h}}{\bar {\alpha }^{2}}\). In order for the range of γ that supports this scenario to be non-empty, we need \(1-\frac {2C_{h}}{\bar {\alpha }^{2}}>0\), or \(C_{h}<\frac {\bar {\alpha }^{2}}{2}\).
In summary, the following conditions support this scenario: (i) \(C_{h}\le \frac {\bar {\alpha }(\bar {\alpha }-v)}{2}\) and \(\gamma \in \left (0,\frac {v}{\bar {\alpha }}\right ]\); (ii) \(C_{h}\in \left (\frac {\bar {\alpha }(\bar {\alpha }-v)}{2},\frac {\bar {\alpha }^{2}}{2}\right )\) and \(\gamma \in \left (0,1-\frac {2C_{h}}{\bar {\alpha }^{2}}\right )\).
- 3.
When only constraint (1) is binding (λ1 ≥ 0 and λ2 = 0): This is the case with \(Q_{h}(p_{h})=Q_{s}(p_{s})<\bar {\alpha }\). This constraint gives the following relationship between ps and ph:
$$ p_{s} = \frac{(1-\gamma)(p_{h}-v)}{\gamma}. $$Substituting this into the first-order conditions, we get \(\lambda _{1}=-\frac {v}{\gamma }<0\) for any γ. Thus this scenario is not supported.
- 4.
When both constraints are binding (λ1 ≥ 0 and λ2 ≥ 0): This is the case with \(Q_{h}(p_{h})=Q_{s}(p_{s})=\bar {\alpha }\). From the discussion above, we can obtain
$$ \begin{array}{@{}rcl@{}} p_{h} &=& v, p_{s}=0\\ Q_{h} &=& Q_{s} = \bar{\alpha}. \end{array} $$Constraint (1) requires λ1 ≥ 0. However, substituting the above optimal prices into the first-order conditions, we can show that \(\lambda _{1}=-\bar {\alpha }(1-\gamma )<0\). Thus, this scenario is not supported.
Combining the results, we have:
- 1.
When \(C_{h}\le \frac {\bar {\alpha }(\bar {\alpha }-2v)}{2}\), the hardware firm will develop software for γ ∈ (0, 1).
For \(\gamma \in \left (0,\frac {v}{\bar {\alpha }}\right ]\), the optimal strategy is characterized by scenario 2.
For \(\gamma \in \left (\frac {v}{\bar {\alpha }},1\right )\), the optimal strategy is characterized by scenario 1.
- 2.
When \(C_{h}\in \left (\frac {\bar {\alpha }(\bar {\alpha }-2v)}{2},\frac {\bar {\alpha }(\bar {\alpha }-v)}{2}\right ]\), the hardware firm will develop software if \(\gamma \in \left (0,\frac {v^{2}}{2C_{h}-\bar {\alpha }(\bar {\alpha }-2v)}\right ]\). Otherwise, it will only sell hardware.
For \(\gamma \in \left (0,\frac {v}{\bar {\alpha }}\right ]\), the optimal strategy is characterized by scenario 2.
For \(\gamma \in \left (\frac {v}{\bar {\alpha }},\frac {v^{2}}{2C_{h}-\bar {\alpha }(\bar {\alpha }-2v)}\right )\), the optimal strategy is characterized by scenario 1.
- 3.
When \(C_{h}\in \left (\frac {\bar {\alpha }(\bar {\alpha }-v)}{2},\frac {\bar {\alpha }^{2}}{2}\right )\), the hardware firm will develop software if \(\gamma \in \left (0,1-\frac {2C_{h}}{\bar {\alpha }^{2}}\right )\). Otherwise, it will only sell hardware.
The optimal strategy is characterized by scenario 2.
- 4.
When \(C_{h}\ge \frac {\bar {\alpha }^{2}}{2}\), the hardware firm will not develop software for γ ∈ (0, 1).
In summary, when Ch is sufficiently low, regardless of γ’s value, software is supplied. When γ is small, all consumers buy hardware. When Ch is intermediate, the hardware firm does not supply software if γ is large. This is because the negative effect of software piracy on in-house software is so large that it would not make sense to pay Ch and sell software. When Ch is large, it is too costly to supply software so the hardware firm just sells hardware.
1.2 A.2 Proof of Proposition 2
The software provider’s problem given the licensing fee f is given by
The first-order condition with respect to ps yields
The hardware provider’s problem is then given by
subject to (1) Qh(ph) ≥ Qs(f), (2) \(Q_{h}(p_{h})\le \bar {\alpha }\), and (3) πs(f) ≥ 0. The Lagrangian is
The Kuhn-Tucker conditions are
We solve this set of inequalities and equations. Below we examine every possible case.
- 1.
When all constraints are not binding (λ1 = λ2 = λ3 = 0): This is the case with interior solutions. We have
$$ \begin{array}{@{}rcl@{}} p_{h} &=& \frac{\bar{\alpha}\gamma+v}{2}, f=\frac{\bar{\alpha}(1-\gamma)}{2}\\ Q_{h} &=& \frac{\bar{\alpha}\gamma+v}{2\gamma}, Q_{s}=\frac{\bar{\alpha}}{4}. \end{array} $$Constraint (1) is satisfied for any γ. Non-binding constraint (2) implies that \(\gamma \ge \frac {v}{\bar {\alpha }}\). Finally, non-binding constraint (3) implies that \(\gamma \le 1-\frac {8C_{s}}{\bar {\alpha }^{2}}\). The range of γ that supports this scenario is non-empty if \(\frac {v}{\bar {\alpha }}\le 1-\frac {8C_{s}}{\bar {\alpha }^{2}}\) or \(C_{s}\le \frac {\bar {\alpha }(\bar {\alpha }-v)}{8}\).
With the optimal ph and f, the hardware firm’s profit is
$$ \pi_{h} = \frac{(\bar{\alpha}\gamma+v)^{2}}{4\gamma}+\frac{\bar{\alpha}^{2}(1-\gamma)}{8}, $$and it is easy to check that \(\pi _{h}>\bar {\alpha }v\) for any γ in the range. Thus, the hardware firm prefers to have software developed. Moreover,
$$ \frac{\partial \pi_{h}}{\partial \gamma} = \frac{\bar{\alpha}^{2}}{8}-\frac{v^{2}}{4\gamma^{2}}. $$Thus, \(\frac {\partial \pi _{h}}{\partial \gamma }>0\) for \(\gamma >\frac {\sqrt {2}v}{\bar {\alpha }}\).
In summary, this scenario is supported under the following conditions: \(C_{h}<\frac {\bar {\alpha }(\bar {\alpha }-v)}{8}\) and \(\gamma \in \left [\frac {v}{\bar {\alpha }},1-\frac {8C_{s}}{\bar {\alpha }^{2}}\right ]\). Moreover, if \(C_{h}<\frac {\bar {\alpha }(\bar {\alpha }-\sqrt {2}v)}{8}\), then \(\frac {\partial \pi _{h}}{\partial \gamma }\le 0\) for \(\gamma \in \left [\frac {v}{\bar {\alpha }},\frac {\sqrt {2}v}{\bar {\alpha }}\right ]\) and \(\frac {\partial \pi _{h}}{\partial \gamma }>0\) for \(\gamma \in \left (\frac {\sqrt {2}v}{\bar {\alpha }},1-\frac {8C_{s}}{\bar {\alpha }^{2}}\right ]\). If \(C_{h}\in \left [\frac {\bar {\alpha }(\bar {\alpha }-\sqrt {2}v)}{8},\frac {\bar {\alpha }(\bar {\alpha }-v)}{8}\right )\), \(\frac {\partial \pi _{h}}{\partial \gamma }\le 0\) for all \(\gamma \in \left [\frac {v}{\bar {\alpha }},1-\frac {8C_{s}}{\bar {\alpha }^{2}}\right ]\).
- 2.
When only constraint (3) is binding (λ1 = λ2 = 0 and λ3 ≥ 0): This is the case where πs(f) = 0. We have
$$ \begin{array}{@{}rcl@{}} p_{h} &=&\frac{\bar{\alpha}\gamma+v}{2}, f = \bar{\alpha}(1-\gamma)-\sqrt{2(1-\gamma)C_{s}}\\ Q_{h} &=& \frac{\bar{\alpha}\gamma+v}{2\gamma}, Q_{s}=\sqrt{\frac{C_{s}}{2(1-\gamma)}}. \end{array} $$Constraint (1) requires \(\frac {\bar {\alpha }\gamma +v}{2\gamma }\ge \sqrt {\frac {C_{s}}{2(1-\gamma )}}\). Let \(g(\gamma ) = \frac {\bar {\alpha }\gamma +v}{2\gamma }- \sqrt {\frac {C_{s}}{2(1-\gamma )}}\). It is easy to check that \(\frac {\partial g(\gamma )}{\partial \gamma }<0\ \forall \gamma \), \(\lim _{\gamma \rightarrow 0}g(\gamma )=+\infty \), and \(\lim _{\gamma \rightarrow 1}g(\gamma )=-\infty \). Thus, there exist a unique threshold, say, γ1 ∈ (0, 1) such that g(γ) ≥ 0 for all γ ≤ γ1. Constraint (2) implies that \(\gamma \ge \frac {v}{\bar {\alpha }}\). Constraint (3) is binding thus we need λ3 ≥ 0, which is equivalent to \(\gamma \ge 1-\frac {8C_{s}}{\bar {\alpha }^{2}}\). The range of γ that supports this scenario is non-empty if g(γ) > 0 at \(\gamma =\max \limits \left \{\frac {v}{\bar {\alpha }},1-\frac {8C_{s}}{\bar {\alpha }^{2}}\right \}\). Suppose that \(\frac {v}{\bar {\alpha }}<1-\frac {8C_{s}}{\bar {\alpha }^{2}}\) (or \(C_{s}<\frac {\bar {\alpha }(\bar {\alpha }-v)}{8}\)). Then, it is easy to check \(g(\gamma =1-\frac {8C_{s}}{\bar {\alpha }^{2}})>0\), so \(\gamma _{1}>1-\frac {8C_{s}}{\bar {\alpha }^{2}}\). If \(\frac {v}{\bar {\alpha }}\ge 1-\frac {8C_{s}}{\bar {\alpha }^{2}}\) (or \(C_{s}\ge \frac {\bar {\alpha }(\bar {\alpha }-v)}{8}\)), then \(g(\gamma =\frac {v}{\bar {\alpha }})\ge 0\) (i.e., \(\frac {v}{\bar {\alpha }}\le \gamma _{1}\)) if \(C_{s}\le 2\bar {\alpha }(\bar {\alpha }-v)\). Together, the range of γ is non-empty if \(C_{s}\le 2\bar {\alpha }(\bar {\alpha }-v)\).
With the optimal ph and f, the hardware firm’s profit is
$$ \pi_{h} = \frac{(\bar{\alpha}\gamma+v)^{2}}{4\gamma}+\left( \bar{\alpha}(1-\gamma)-\sqrt{2(1-\gamma)C_{s}}\right)\sqrt{\frac{C_{s}}{2(1-\gamma)}}. $$When \(\gamma \ge \frac {v}{\bar {\alpha }}\), not everyone buys hardware and \(p_{h}Q_{h} = \frac {(\bar {\alpha }\gamma +v)^{2}}{4\gamma }\ge \bar {\alpha }v\). Thus, the above equation for πh suggests that πh can be lower than \(\bar {\alpha }v\) only when the optimal licensing fee is negative:
$$ \bar{\alpha}(1-\gamma)-\sqrt{2(1-\gamma)C_{s}}<0 \Leftrightarrow \gamma > 1-\frac{2C_{s}}{\bar{\alpha}^{2}}. $$We first check if a negative licensing fee could actually happen within the above range of γ. When \(\frac {v}{\bar {\alpha }}>1-\frac {2C_{s}}{\bar {\alpha }^{2}}\) (or \(C_{s}>\frac {\bar {\alpha }(\bar {\alpha }-v)}{2}\)), then the condition for this scenario to be non-empty (\(C_{s}\le 2\bar {\alpha }(\bar {\alpha }-v)\)) implies that \(1-\frac {2C_{s}}{\bar {\alpha }^{2}}<\gamma _{1}\). If \(\frac {v}{\bar {\alpha }}\le 1-\frac {2C_{s}}{\bar {\alpha }^{2}}\), then it can be shown that \(g(\gamma =1-\frac {2C_{s}}{\bar {\alpha }^{2}})=\frac {\bar {\alpha }^{2}v}{2(\bar {\alpha }^{2}-2C_{s})}>0\). Thus, the negative licensing fee could indeed happen. Below, we focus on \(\gamma \in \left (1-\frac {2C_{s}}{\bar {\alpha }^{2}},\gamma _{1}\right ]\).
First, note that
$$ \frac{\partial \pi_{h}}{\partial \gamma} = \frac{\bar{\alpha}^{2}}{4} - \frac{v^{2}}{4\gamma^{2}} - \frac{\bar{\alpha}}{2}\sqrt{\frac{C_{s}}{2(1-\gamma)}}. $$We can show that for \(\gamma > 1-\frac {2C_{s}}{\bar {\alpha }^{2}}\), \(\sqrt {\frac {C_{s}}{2(1-\gamma )}}>\frac {\bar {\alpha }}{2}\). Thus, we have \(\frac {\partial \pi _{h}}{\partial \gamma }<0\) for \(\gamma \in \left (1-\frac {2C_{s}}{\bar {\alpha }^{2}},\gamma _{1}\right ]\). Given this, if \(1-\frac {2C_{s}}{\bar {\alpha }^{2}}<\frac {v}{\bar {\alpha }}\) (or \(C_{s}>\frac {\bar {\alpha }(\bar {\alpha }-v)}{2}\)), then we have \(\pi _{h}<\bar {\alpha }v\) for \(\gamma \in \left [\frac {v}{\bar {\alpha }},\gamma _{1}\right ]\) because \(\pi _{h}<\bar {\alpha }v\) at \(\gamma =\frac {v}{\bar {\alpha }}\). For \(C_{s}\le \frac {\bar {\alpha }(\bar {\alpha }-v)}{2}\), since \(\pi >\bar {\alpha }v\) at \(\gamma =1-\frac {2C_{s}}{\bar {\alpha }^{2}}\), we can possibly have a unique threshold,say, \(\gamma _{2}\in \left (1-\frac {2C_{s}}{\bar {\alpha }^{2}},\gamma _{2}\right ]\) such that \(\pi _{h}<\bar {\alpha }v\) for γ ∈ (γ2, γ1]. For example, we can numerically check that for \((\bar {\alpha },v,C_{s})=(1.0,0.5,0.2)\), there exists such γ2 < γ1, but for \((\bar {\alpha },v,C_{s})=(1.5,0.5,0.2)\), \(\pi _{h}>\bar {\alpha }v\) at γ = γ1. Since we cannot derive a closed form for the thresholds, let us define \({\Theta }\equiv \{\theta =(\bar {\alpha },v,C_{s}):0<v<\bar {\alpha },0<C_{s}<\frac {\bar {\alpha }(\bar {\alpha }-v)}{2},\pi _{h}(\gamma =\gamma _{1})\ge \bar {\alpha }v\}\).
We can now summarize the range of γ that supports this scenario. When \(C_{h}<\frac {\bar {\alpha }(\bar {\alpha }-v)}{8}\), \(\gamma \in \left [1-\frac {8C_{s}}{\bar {\alpha }^{2}},\gamma _{1}\right ]\) for \((\bar {\alpha },v,C_{s})\in {\Theta }\). For \((\bar {\alpha },v,C_{s})\notin {\Theta }\), there exists a unique \(\gamma _{2}(\theta )\in \left (1-\frac {2C_{s}}{\bar {\alpha }^{2}},\gamma _{1}\right )\) such that \(\pi _{h}<\bar {\alpha }v\) for all γ ∈ (γ2(θ), γ1]. When \(C_{h}\in \left [\frac {\bar {\alpha }(\bar {\alpha }-v)}{8},\frac {\bar {\alpha }(\bar {\alpha }-v)}{2}\right ]\), \(\gamma \in \left [\frac {v}{\bar {\alpha }},\gamma _{1}\right ]\) for \((\bar {\alpha },v,C_{s})\in {\Theta }\). For \((\bar {\alpha },v,C_{s})\notin {\Theta }\), there exists a unique \(\gamma _{2}(\theta )\in \left (1-\frac {2C_{s}}{\bar {\alpha }^{2}},\gamma _{1}\right )\) such that \(\pi _{h}<\bar {\alpha }v\) for all γ ∈ (γ2(θ), γ1]. When \(C_{h}\in \left (\frac {\bar {\alpha }(\bar {\alpha }-v)}{2},2\bar {\alpha }(\bar {\alpha }-v)\right ]\), \(\gamma \in \left [\frac {v}{\bar {\alpha }},\gamma _{1}\right ]\). But as we saw, \(\pi _{h}<\bar {\alpha }v\) for this range of γ and the hardware firm prefers not to have software.
Finally, we examine the effect of γ on πh. We saw that for \(\gamma \in \left (1-\frac {2C_{s}}{\bar {\alpha }^{2}},\gamma _{1}\right ]\), we have \(\frac {\partial \pi _{h}}{\partial \gamma }<0\). We thus consider \(\gamma \in \left [\max \limits \left \{\frac {v}{\bar {\alpha }},1-\frac {8C_{s}}{\bar {\alpha }^{2}}\right \},1-\frac {2C_{s}}{\bar {\alpha }^{2}}\right ]\). Note that
$$ \begin{array}{@{}rcl@{}} \frac{\partial^{2} \pi_{h}}{\partial^{2} \gamma} &=& \frac{v^{2}}{2\gamma^{3}}-\frac{\bar{\alpha}}{4(1-\gamma)}\sqrt{\frac{C_{s}}{2(1-\gamma)}}\\ &=& \frac{v^{2}}{2(1-\gamma)\sqrt{1-\gamma}}\left( \frac{(1-\gamma)\sqrt{1-\gamma}}{\gamma^{3}}-\frac{\bar{\alpha}\sqrt{C_{s}}}{2\sqrt{2}v^{2}}\right). \end{array} $$It is easy to check that \(\lim _{\gamma \rightarrow 0}\frac {\partial ^{2} \pi _{h}}{\partial ^{2} \gamma }=\infty \) and \(\lim _{\gamma \rightarrow 1}\frac {\partial ^{2} \pi _{h}}{\partial ^{2} \gamma }=-\infty \). Let \(h(\gamma )=\frac {(1-\gamma )\sqrt {1-\gamma }}{\gamma ^{3}}-\frac {\bar {\alpha }\sqrt {C_{s}}}{2\sqrt {2}v^{2}}\). We can show that \(\frac {\partial h(\gamma )}{\partial \gamma }<0\) for all γ, and thus, there exists a unique threshold, say, γ3 such that \(\left .\frac {\partial ^{2} \pi _{h}}{\partial ^{2} \gamma }\right |_{\gamma =\gamma _{3}}=0\). We can then consider three possibilities in terms of where γ3 falls into the range of γ above. Suppose \(\gamma _{3}>1-\frac {2C_{s}}{\bar {\alpha }^{2}}\). Then \(\frac {\partial ^{2} \pi _{h}}{\partial ^{2} \gamma }>0\) for \(\gamma \in \left [\max \limits \left \{\frac {v}{\bar {\alpha }},1-\frac {8C_{s}}{\bar {\alpha }^{2}}\right \},1-\frac {2C_{s}}{\bar {\alpha }^{2}}\right ]\). Since \(\frac {\partial \pi _{h}}{\partial \gamma }<0\) at \(\gamma =1-\frac {2C_{s}}{\bar {\alpha }^{2}}\), we have \(\frac {\partial \pi _{h}}{\partial \gamma }<0\) for \(\forall \gamma \in \left [\max \limits \left \{\frac {v}{\bar {\alpha }},1-\frac {8C_{s}}{\bar {\alpha }^{2}}\right \},1-\frac {2C_{s}}{\bar {\alpha }^{2}}\right ]\). For this to happen, we need \(h(\gamma =1-\frac {2C_{s}}{\bar {\alpha }^{2}})>0\). Next, if \(\gamma _{3}<\max \limits \left \{\frac {v}{\bar {\alpha }},1-\frac {8C_{s}}{\bar {\alpha }^{2}}\right \}\), then \(\frac {\partial ^{2} \pi _{h}}{\partial ^{2} \gamma }<0\) for \(\gamma \in \left [\max \limits \left \{\frac {v}{\bar {\alpha }},1-\frac {8C_{s}}{\bar {\alpha }^{2}}\right \},1-\frac {2C_{s}}{\bar {\alpha }^{2}}\right ]\). Thus the sign of \(\frac {\partial \pi _{h}}{\partial \gamma }\) depends on whether \(\frac {\partial \pi _{h}}{\partial \gamma }\) is positive or negative at \(\gamma =\max \limits \left \{\frac {v}{\bar {\alpha }},1-\frac {8C_{s}}{\bar {\alpha }^{2}}\right \}\). First, when \(\frac {v}{\bar {\alpha }}<1-\frac {8C_{s}}{\bar {\alpha }^{2}}\) (or \(C_{s}<\frac {\bar {\alpha }(\bar {\alpha }-v)}{8}\)), we have
$$ \left.\frac{\partial \pi_{h}}{\partial \gamma}\right|_{\gamma=1-\frac{8C_{s}}{\bar{\alpha}^{2}}} = \frac{\bar{\alpha}^{2}}{4}\left[\frac{1}{2}-\left( \frac{\bar{\alpha}v}{\bar{\alpha}^{2}-8C_{s}}\right)^{2}\right], $$which is positive if \(C_{s}<\frac {\bar {\alpha }(\bar {\alpha }-\sqrt {2}v)}{8}\). Thus, when \(C_{s}<\frac {\bar {\alpha }(\bar {\alpha }-\sqrt {2}v)}{8}\), there exists a unique threshold, say, γ4 such that \(\frac {\partial \pi _{h}}{\partial \gamma }>0\) for \(\gamma \in \left (1-\frac {8C_{s}}{\bar {\alpha }^{2}},\gamma _{4}\right )\) and \(\frac {\partial \pi _{h}}{\partial \gamma }\le 0\) otherwise. If \(C_{s}\in \left [\frac {\bar {\alpha }(\bar {\alpha }-\sqrt {2}v)}{8},\frac {\bar {\alpha }(\bar {\alpha }-v)}{8}\right )\), then \(\frac {\partial \pi _{h}}{\partial \gamma }<0\) for all \(\gamma \in \left (1-\frac {8C_{s}}{\bar {\alpha }^{2}},1-\frac {2C_{s}}{\bar {\alpha }^{2}}\right )\). When \(\frac {v}{\bar {\alpha }}<1-\frac {8C_{s}}{\bar {\alpha }^{2}}\), it is easy to check
$$ \left.\frac{\partial \pi_{h}}{\partial \gamma}\right|_{\gamma=\frac{v}{\bar{\alpha}}} = -\frac{\bar{\alpha}}{2}\sqrt{\frac{\bar{\alpha}C_{s}}{2(\bar{\alpha}-v)}}<0\ \ \forall \gamma\in\left( \frac{v}{\bar{\alpha}},1-\frac{2C_{s}}{\bar{\alpha}^{2}}\right). $$Finally, if \(\gamma _{3}\in \left [\max \limits \left \{\frac {v}{\bar {\alpha }},1-\frac {8C_{s}}{\bar {\alpha }^{2}}\right \},1-\frac {2C_{s}}{\bar {\alpha }^{2}}\right ]\), then \(\frac {\partial \pi _{h}}{\partial \gamma }\) is a parabola with a maximum at γ = γ3. Thus, we can check if the maximum attained can be positive. Analytically, it is cumbersome to show. However, our numerical analysis shows that there exists a set of \((\bar {\alpha },v,C_{s})\) such that the maximum is positive (e.g., \((\bar {\alpha },v,C_{s})=(1,0.2,0.1)\)). Under such a condition, there exist \(\gamma _{4},\gamma _{5}\in \left [\max \limits \left \{\frac {v}{\bar {\alpha }},1-\frac {8C_{s}}{\bar {\alpha }^{2}}\right \},1-\frac {2C_{s}}{\bar {\alpha }^{2}}\right ]\) such that \(\frac {\partial \pi _{h}}{\partial \gamma }>0\) for γ ∈ (γ4, γ5) and \(\frac {\partial \pi _{h}}{\partial \gamma }\le 0\) otherwise.
- 3.
When only constraint (2) is binding (λ1 = 0, λ2 ≥ 0, and λ3 = 0): This is the case where \(Q_{h}(p_{h})=\bar {\alpha }\). We have
$$ \begin{array}{@{}rcl@{}} p_{h} &=& v, f = \frac{\bar{\alpha}(1-\gamma)}{2}\\ Q_{h} &=& \bar{\alpha}, Q_{s}=\frac{\bar{\alpha}}{4}. \end{array} $$Constraint (1) is satisfied for any γ. Constraint (2) is binding thus we need λ2 ≥ 0, which results in \(\gamma \le \frac {v}{\bar {\alpha }}\). Constraint (3) implies \(\gamma \le 1-\frac {8C_{s}}{\bar {\alpha }^{2}}\). The range of γ that supports this scenario is non-empty if \(1-\frac {8C_{s}}{\bar {\alpha }^{2}}>0\), or \(C_{s}<\frac {\bar {\alpha }^{2}}{8}\).
The hardware firm’s profit is \(\pi _{h}=\bar {\alpha }v+\frac {\bar {\alpha }^{2}(1-\gamma )}{8}\), which is greater than \(\bar {\alpha }v\) for any \(\gamma \le \min \limits \left \{\frac {v}{\bar {\alpha }},1-\frac {8C_{s}}{\bar {\alpha }^{2}}\right \}\). Moreover, \(\frac {\partial \pi _{h}}{\partial \gamma }<0\).
In summary, this scenario is supported under the following conditions: (i) \(C_{s}\le \frac {\bar {\alpha }(\bar {\alpha }-v)}{8}\) and \(\gamma \in \left (0,\frac {v}{\bar {\alpha }}\right ]\); (ii) \(C_{s}\in \left [\frac {\bar {\alpha }(\bar {\alpha }-v)}{8},\frac {\bar {\alpha }^{2}}{8}\right ]\) and \(\gamma \in \left (0,1-\frac {8C_{s}}{\bar {\alpha }^{2}}\right )\). In both cases, \(\frac {\partial \pi _{h}}{\partial \gamma }<0\).
- 4.
When constraints (2) and (3) are binding (λ1 = 0, λ2 ≥ 0, and λ3 ≥ 0): This is the case where \(Q_{s}(f)\le Q_{h}(p_{h})=\bar {\alpha }\) and πs(f) = 0. We have
$$ \begin{array}{@{}rcl@{}} p_{h} &=&v, f = \bar{\alpha}(1-\gamma)-\sqrt{2(1-\gamma)C_{s}}\\ Q_{h} &=& \bar{\alpha}, Q_{s}=\sqrt{\frac{C_{s}}{2(1-\gamma)}}. \end{array} $$Constraint (1) requires \(\bar {\alpha }\ge \sqrt {\frac {C_{s}}{2(1-\gamma )}}\), which is equivalent to \(\gamma \le 1-\frac {C_{s}}{2\bar {\alpha }^{2}}\). Constraint (2) is binding thus we need λ2 ≥ 0, or \(\gamma \le \frac {v}{\bar {\alpha }}\). Constraint (3) is also binding thus we need λ3 ≥ 0, or \(\gamma \ge 1-\frac {8C_{s}}{\bar {\alpha }^{2}}\). The range of γ that supports this scenario is \(\gamma \in \left [1-\frac {8C_{s}}{\bar {\alpha }^{2}},\min \limits \left \{\frac {v}{\bar {\alpha }},1-\frac {C_{s}}{2\bar {\alpha }^{2}}\right \}\right ]\). In order for this range to be non-empty, we need the following conditions. When \(\frac {v}{\bar {\alpha }}\le 1-\frac {C_{s}}{2\bar {\alpha }^{2}}\) (or \(C_{s}\le 2\bar {\alpha }(\bar {\alpha }-v)\)), we need \(1-\frac {8C_{s}}{\bar {\alpha }^{2}}\le \frac {v}{\bar {\alpha }}\), or \(C_{s}\ge \frac {\bar {\alpha }(\bar {\alpha }-v)}{8}\). When \(\frac {v}{\bar {\alpha }}>1-\frac {C_{s}}{2\bar {\alpha }^{2}}\), we need \(1-\frac {C_{s}}{2\bar {\alpha }^{2}}>0\), or \(C_{s}<2\bar {\alpha }^{2}\). Thus, the range of γ is non-empty if \(C_{s}\in \left [\frac {\bar {\alpha }(\bar {\alpha }-v)}{8},2\bar {\alpha }^{2}\right )\).
With the optimal ph and f, the hardware firm’s profit is
$$ \pi_{h} = \bar{\alpha}v+\left( \bar{\alpha}(1-\gamma)-\sqrt{2(1-\gamma)C_{s}}\right)\sqrt{\frac{C_{s}}{2(1-\gamma)}}. $$This is greater than or equal to \(\bar {\alpha }v\) as long as the licensing fee is non-negative, which implies \(\gamma \le 1- \frac {2C_{s}}{\bar {\alpha }^{2}}\). Since \(1- \frac {2C_{s}}{\bar {\alpha }^{2}}<1- \frac {C_{s}}{2\bar {\alpha }^{2}}\), the range of γ that supports this scenario becomes \(\gamma \in \left [1-\frac {8C_{s}}{\bar {\alpha }^{2}},\min \limits \left \{\frac {v}{\bar {\alpha }},1-\frac {2C_{s}}{\bar {\alpha }^{2}}\right \}\right ]\). When \(\frac {v}{\bar {\alpha }}\le 1-\frac {2C_{s}}{\bar {\alpha }^{2}}\) (or \(C_{s}\le \frac {\bar {\alpha }(\bar {\alpha }-v)}{2}\)), we need \(1-\frac {8C_{s}}{\bar {\alpha }^{2}}\le \frac {v}{\bar {\alpha }}\), or \(C_{s}\ge \frac {\bar {\alpha }(\bar {\alpha }-v)}{8}\). When \(\frac {v}{\bar {\alpha }}>1-\frac {2C_{s}}{\bar {\alpha }^{2}}\), we need \(1-\frac {2C_{s}}{\bar {\alpha }^{2}}>0\), or \(C_{s}<\frac {\bar {\alpha }^{2}}{2}\). Thus, the range of γ is non-empty if \(C_{s}\in \left [\frac {\bar {\alpha }(\bar {\alpha }-v)}{8},\frac {\bar {\alpha }^{2}}{2}\right )\). Moreover, note that
$$ \frac{\partial \pi_{h}}{\partial \gamma} = -\frac{\bar{\alpha}}{2}\sqrt{\frac{C_{s}}{2(1-\gamma)}}. $$Thus \(\frac {\partial \pi _{h}}{\partial \gamma }<0\).
In summary, this scenario is supported under the following conditions: (i) \(C_{s}\in \left [\frac {\bar {\alpha }(\bar {\alpha }-v)}{8}, \frac {\bar {\alpha }(\bar {\alpha }-v)}{2}\right ]\) and \(\gamma \in \left (\max \limits \left \{0,1-\frac {8C_{s}}{\bar {\alpha }^{2}}\right \},\frac {v}{\bar {\alpha }}\right ]\); (ii) \(C_{s}\in \left (\frac {\bar {\alpha }(\bar {\alpha }-v)}{2},\frac {\bar {\alpha }^{2}}{2}\right ]\), \(\gamma \in \left (\max \limits \left \{0,1-\frac {8C_{s}}{\bar {\alpha }^{2}}\right \},1-\frac {2C_{s}}{\bar {\alpha }^{2}}\right ]\). For \(C_{s}\in \left (\frac {\bar {\alpha }^{2}}{2},2\bar {\alpha }^{2}\right ]\), the optimal strategy is supported, but the hardware firm’s profits are lower than \(\bar {\alpha }v\). Moreover, we have \(\frac {\partial \pi _{h}}{\partial \gamma }<0\) under these conditions.
- 5.
When only constraint (1) is binding (λ1 ≥ 0 and λ2 = λ3 = 0): This is the case with Qh(ph) = Qs(f). Intuitively, this scenario will not be supported because when πs(f) > 0, the optimal licensing fee will be high enough to make Qs(f) smaller than Qh(ph). We can compute
$$ \begin{array}{@{}rcl@{}} p_{h} &= \frac{\bar{\alpha}(3-2\gamma)\gamma+(4-3\gamma)v}{2(2-\gamma)}, f=\frac{(\bar{\alpha}(1-\gamma)-v)(1-\gamma)}{2-\gamma}. \end{array} $$The first-order condition with respect to f gives \(\lambda _{1}=\frac {f}{\gamma (1-\gamma )}-\frac {\bar {\alpha }}{2\gamma }\). Substituting the optimal f into this, we can show that λ1 < 0 for any γ. Thus, this scenario is not supported.
- 6.
When constraints (1) and (3) are binding (λ1 ≥ 0, λ2 = 0, and λ3 ≥ 0): This is the case with \(Q_{h}(p_{h})=Q_{s}(f)<\bar {\alpha }\) and πs(f) = 0. This could happen when Cs is large and γ is also large so that the hardware firm needs to lower f sufficiently, which makes the software demand equal to the hardware demand. We can compute
$$ \begin{array}{@{}rcl@{}} p_{h} &=&\bar{\alpha}\gamma+v-\gamma\sqrt{\frac{C_{s}}{2(1-\gamma)}}, f = \bar{\alpha}(1-\gamma)-\sqrt{2(1-\gamma)C_{s}}\\ Q_{h} &=& Q_{s} = \sqrt{\frac{C_{s}}{2(1-\gamma)}}. \end{array} $$Constraint (1) is binding thus we need λ1 ≥ 0. From the first-order condition with respect to ph, we get
$$ \lambda_{1} = -\bar{\alpha}\gamma-v+2\gamma\sqrt{\frac{C_{s}}{2(1-\gamma)}} = 2\gamma\left( \sqrt{\frac{C_{s}}{2(1-\gamma)}}-\frac{\bar{\alpha}\gamma+v}{2\gamma}\right), $$which is greater than or equal to zero when γ ≥ γ1, where \(\tilde {\gamma }\) is defined in scenario 2 above. Constraint (2) requires \(Q_{h}\le \bar {\alpha }\), or \(\gamma \le 1-\frac {C_{s}}{2\bar {\alpha }^{2}}\). Constraint (3) is binding thus we need λ3 ≥ 0, which can be shown to be satisfied when γ ≥ γ1. To see this, note that the first-order condition with respect to f gives
$$ \lambda_{3}\ge 0 \Leftrightarrow \bar{\alpha}(1-\gamma)-2f+\lambda_{1}\ge 0. $$First, note that \(\bar {\alpha }(1-\gamma )-2f\ge 0\) for \(\gamma \ge 1-\frac {8C_{s}}{\bar {\alpha }^{2}}\) and that \(\gamma _{1}>1-\frac {8C_{s}}{\bar {\alpha }^{2}}\) (we have proven this in scenario 2 above, but it is easy to check that because \(\lambda _{1}(\gamma =1-\frac {8C_{s}}{\bar {\alpha }^{2}})<0\) and \(\frac {\partial \lambda _{1}}{\partial \gamma }>0\), it must be \(1-\frac {8C_{s}}{\bar {\alpha }^{2}}<\gamma _{1}\)). Thus, at γ = γ1, λ3 > 0. Overall, the range of γ that supports this scenario is \(\gamma \in \left [\gamma _{1},1-\frac {C_{s}}{2\bar {\alpha }^{2}}\right ]\). For this range of γ to be non-empty, we need \(\lambda _{1}(\gamma =1-\frac {C_{s}}{2\bar {\alpha }^{2}})\le 0\), which is equivalent to \(C_{s}\le 2\bar {\alpha }(\bar {\alpha }-v)\).
With the optimal ph and f, the hardware firm’s profit is
$$ \begin{array}{@{}rcl@{}} \pi_{h} &=& \left( \bar{\alpha}\gamma+v-\gamma\sqrt{\frac{C_{s}}{2(1-\gamma)}}\right)\sqrt{\frac{C_{s}}{2(1-\gamma)}}\\ &&+ \left( \bar{\alpha}(1-\gamma)-\sqrt{2(1-\gamma)C_{s}}\right)\sqrt{\frac{C_{s}}{2(1-\gamma)}}\\ &=&\left( \bar{\alpha}+v-(2-\gamma)\sqrt{\frac{C_{s}}{2(1-\gamma)}}\right)\sqrt{\frac{C_{s}}{2(1-\gamma)}}. \end{array} $$We note that at \(\gamma =1-\frac {C_{s}}{2\bar {\alpha }^{2}}\), we have ph = v, \(f=-\frac {C_{s}}{2\bar {\alpha }}\), \(Q_{h}=Q_{s}=\bar {\alpha }\). Thus,
$$ \pi_{h} = \left( v-\frac{C_{s}}{2\bar{\alpha}}\right)\bar{\alpha} = \bar{\alpha}v - \frac{C_{s}}{2}, $$which is clearly less than \(\bar {\alpha }v\). For \(\gamma \in \left [\gamma _{1},1-\frac {C_{s}}{2\bar {\alpha }}\right )\), note that
$$ \frac{\partial \pi_{h}}{\partial \gamma} = \frac{1}{1-\gamma}\sqrt{\frac{C_{s}}{2(1-\gamma)}}\left( \frac{\bar{\alpha}+v}{2}-\sqrt{\frac{C_{s}}{2(1-\gamma)}}\right). $$We know that \(\frac {\bar {\alpha }+v}{2}<\frac {\bar {\alpha }\gamma +v}{2\gamma }\) for γ < 1. Also, for γ > γ1, \(\frac {\bar {\alpha }\gamma +v}{2\gamma }<\sqrt {\frac {C_{s}}{2(1-\gamma )}}\). Thus, \(\frac {\partial \pi _{h}}{\partial \gamma }<0\) for \(\gamma \in \left [\gamma _{1},1-\frac {C_{s}}{2\bar {\alpha }^{2}}\right )\). As we saw in scenario 2, we can show that \(\pi _{h}-\bar {\alpha }v\) at γ = γ1 can be positive or negative under some values of \((\bar {\alpha },v,C_{s})\). Note that the hardware firm’s profit function in this scenario is identical to that in scenario 2 at γ = γ1. Thus, we can use the same set of Θ we defined in scenario 2, and summarize the results as follows.
When \(C_{h}<\frac {\bar {\alpha }(\bar {\alpha }-v)}{2}\) and \((\bar {\alpha },v,C_{s})\in {\Theta }\), there exists a unique threshold, say, \(\gamma _{6}(\theta )\in \left (\gamma _{1},1-\frac {C_{s}}{2\bar {\alpha }^{2}}\right )\) such that the hardware firm prefers to have software for γ ∈ [γ1, γ6(θ)]. When \(C_{h}<\frac {\bar {\alpha }(\bar {\alpha }-v)}{2}\) and \((\bar {\alpha },v,C_{s})\notin {\Theta }\) or \(C_{h}\in \left [\frac {\bar {\alpha }(\bar {\alpha }-v)}{2},2\bar {\alpha }(\bar {\alpha }-v)\right ]\), the hardware firm prefers not to have software. Moreover, \(\frac {\partial \pi _{h}}{\partial \gamma }<0\).
- 7.
When constraints (1) and (2) are binding (λ1 ≥ 0, λ2 ≥ 0, and λ3 = 0): This is the case with \(Q_{h}(p_{h})=Q_{s}(f)=\bar {\alpha }\). Once again, intuitively, this scenario will not be supported because when πs(f) > 0, the optimal licensing fee will be high enough to make Qs(f) smaller than Qh(ph). We can compute
$$ \begin{array}{@{}rcl@{}} p_{h} &= v f=-\bar{\alpha}(1-\gamma). \end{array} $$The first-order condition with respect to f gives \(\lambda _{1}=\frac {f}{\gamma (1-\gamma )}-\frac {\bar {\alpha }}{2\gamma }\). Substituting the optimal f into this, we can show that λ1 < 0 for any γ.
- 8.
When all constraints are binding (λ1 ≥ 0, λ2 ≥ 0, and λ3 ≥ 0): This is the case with \(Q_{h}(p_{h})=Q_{s}(f)=\bar {\alpha }\) and πs(f) = 0. We can compute
$$ \begin{array}{@{}rcl@{}} p_{h} &=& v f=-\bar{\alpha}(1-\gamma)\\ Q_{h} &=& Q_{s} = \bar{\alpha} \end{array} $$From the three constraints, we can show that this scenario is supported only at \(\gamma =1-\frac {C_{s}}{2\bar {\alpha }^{2}}\). At this γ, the first-order conditions give
$$ \lambda_{3} = \frac{\bar{\alpha}}{C_{s}}\lambda_{1} + 1, \lambda_{2} = \lambda_{1} + v + \frac{C_{s}}{2\bar{\alpha}}-\bar{\alpha}. $$First, for any λ1 ≥, λ3 > 0, but λ2 ≥ 0 if \(v + \frac {C_{s}}{2\bar {\alpha }}-\bar {\alpha }\ge 0\), or \(C_{s}\ge 2\bar {\alpha }(\bar {\alpha }-v)\).
Note that the hardware firm’s profits under the above optimal strategy are then
$$ \pi_{h} = \bar{\alpha}v - \bar{\alpha}(1-\gamma)\bar{\alpha} < \bar{\alpha}v. $$Thus, the hardware firm prefers not to have software.
Combining the results from supported scenarios, we have:
- 1.
When \(C_{s}\le \frac {\bar {\alpha }(\bar {\alpha }-v)}{8}\) and \(\theta =(\bar {\alpha },v,C_{s})\in {\Theta }\), there exists a unique \(\gamma _{6}(\theta )\in \left (\gamma _{1},1-\frac {C_{s}}{2\bar {\alpha }^{2}}\right )\) such that the optimal strategy is characterized as follows.
For \(\gamma \in \left (0,\frac {v}{\bar {\alpha }}\right ]\), the optimal strategy is characterized by scenario 3.
For \(\gamma \in \left (\frac {v}{\bar {\alpha }},1-\frac {8C_{s}}{\bar {\alpha }^{2}}\right )\), the optimal strategy is characterized by scenario 1.
For \(\gamma \in \left (1-\frac {8C_{s}}{\bar {\alpha }^{2}},\gamma _{1}\right )\), the optimal strategy is characterized by scenario 2.
For \(\gamma \in \left (\gamma _{1},\gamma _{6}(\theta )\right ]\), the optimal strategy is characterized by scenario 6.
For \(\gamma \in \left (\gamma _{6}(\theta ),1\right )\), the hardware firm chooses not to have software.
- 2.
When \(C_{s}\le \frac {\bar {\alpha }(\bar {\alpha }-v)}{8}\) and \(\theta =(\bar {\alpha },v,C_{s})\notin {\Theta }\), there exists a unique \(\gamma _{2}(\theta )\in \left (1-\frac {2C_{s}}{\bar {\alpha }^{2}},\gamma _{1}\right )\) such that the optimal strategy is characterized as follows.
For \(\gamma \in \left (0,\frac {v}{\bar {\alpha }}\right ]\), the optimal strategy is characterized by scenario 3.
For \(\gamma \in \left (\frac {v}{\bar {\alpha }},1-\frac {8C_{s}}{\bar {\alpha }^{2}}\right )\), the optimal strategy is characterized by scenario 1.
For \(\gamma \in \left (1-\frac {8C_{s}}{\bar {\alpha }^{2}},\gamma _{2}(\theta )\right ]\), the optimal strategy is characterized by scenario 2.
For \(\gamma \in \left (\gamma _{2}(\theta ),1\right )\), the hardware firm chooses not to have software.
- 3.
When \(C_{s}\in \left (\frac {\bar {\alpha }(\bar {\alpha }-v)}{8},\frac {\bar {\alpha }(\bar {\alpha }-v)}{2}\right ]\) and \(\theta =(\bar {\alpha },v,C_{s})\in {\Theta }\), there exists a unique \(\gamma _{6}(\theta )\in \left (\gamma _{1},1-\frac {C_{s}}{2\bar {\alpha }^{2}}\right )\) such that the optimal strategy is characterized as follows.
For \(C_{s}\le \frac {\bar {\alpha }^{2}}{8}\):
For \(\gamma \in \left (0,1-\frac {8C_{s}}{\bar {\alpha }^{2}}\right ]\), the optimal strategy is characterized by scenario 3.
For \(\gamma \in \left (1-\frac {8C_{s}}{\bar {\alpha }^{2}},\frac {v}{\bar {\alpha }}\right )\), the optimal strategy is characterized by scenario 4.
For \(\gamma \in \left (\frac {v}{\bar {\alpha }},\gamma _{1}\right )\), the optimal strategy is characterized by scenario 2.
For \(\gamma \in \left (\gamma _{1},\gamma _{6}(\theta )\right ]\), the optimal strategy is characterized by scenario 6.
For \(\gamma \in \left (\gamma _{6}(\theta ),1\right )\), the hardware firm chooses not to have software.
For \(C_{s}>\frac {\bar {\alpha }^{2}}{8}\):
For \(\gamma \in \left (0,\frac {v}{\bar {\alpha }}\right )\), the optimal strategy is characterized by scenario 4.
For \(\gamma \in \left (\frac {v}{\bar {\alpha }},\gamma _{1}\right )\), the optimal strategy is characterized by scenario 2.
For \(\gamma \in \left (\gamma _{1},\gamma _{6}(\theta )\right ]\), the optimal strategy is characterized by scenario 6.
For \(\gamma \in \left (\gamma _{6}(\theta ),1\right )\), the hardware firm chooses not to have software.
- 4.
When \(C_{s}\in \left (\frac {\bar {\alpha }(\bar {\alpha }-v)}{8},\frac {\bar {\alpha }(\bar {\alpha }-v)}{2}\right ]\) and \(\theta =(\bar {\alpha },v,C_{s})\notin {\Theta }\), there exists a unique \(\gamma _{2}(\theta )\in \left (1-\frac {2C_{s}}{\bar {\alpha }^{2}},\gamma _{1}\right )\) such that the optimal strategy is characterized as follows.
For \(C_{s}\le \frac {\bar {\alpha }^{2}}{8}\):
For \(\gamma \in \left (0,1-\frac {8C_{s}}{\bar {\alpha }^{2}}\right ]\), the optimal strategy is characterized by scenario 3.
For \(\gamma \in \left (1-\frac {8C_{s}}{\bar {\alpha }^{2}},\frac {v}{\bar {\alpha }}\right )\), the optimal strategy is characterized by scenario 4.
For \(\gamma \in \left (\frac {v}{\bar {\alpha }},\gamma _{2}(\theta )\right ]\), the optimal strategy is characterized by scenario 2.
For \(\gamma \in \left (\gamma _{2}(\theta ),1\right )\), the hardware firm chooses not to have software.
For \(C_{s}>\frac {\bar {\alpha }^{2}}{8}\):
For \(\gamma \in \left (0,\frac {v}{\bar {\alpha }}\right )\), the optimal strategy is characterized by scenario 4.
For \(\gamma \in \left (\frac {v}{\bar {\alpha }},\gamma _{2}(\theta )\right ]\), the optimal strategy is characterized by scenario 2.
For \(\gamma \in \left (\gamma _{2}(\theta ),1\right )\), the hardware firm chooses not to have software.
- 5.
When \(C_{s}\in \left (\frac {\bar {\alpha }(\bar {\alpha }-v)}{2},\frac {\bar {\alpha }^{2}}{2}\right ]\), the optimal strategy is characterized as follows. Note that Assumption 1 implies that \(\frac {\bar {\alpha }(\bar {\alpha }-v)}{2}>\frac {\bar {\alpha }^{2}}{8}\), thus \(C_{s}>\frac {\bar {\alpha }^{2}}{8}\) in this region of Cs.
For \(\gamma \in \left (0,1-\frac {2C_{s}}{\bar {\alpha }^{2}}\right ]\), the optimal strategy is characterized by scenario 4.
For \(\gamma \in \left (1-\frac {2C_{s}}{\bar {\alpha }^{2}},1\right )\), the hardware firm chooses not to have software.
- 6.
When \(C_{s}>\frac {\bar {\alpha }^{2}}{2}\), the hardware firm prefers not to have software for γ ∈ (0, 1).
1.3 A.3 Proof of Proposition 3a
The software provider’s problem given the licensing fee f is given by
The first-order condition with respect to ps yields
The hardware provider’s problem is then given by
subject to (1) Qh(ph) ≥ Qs(f), (2) \(Q_{h}(p_{h})\le \bar {\alpha }\), and (3) πs(f) ≥ 0. The Lagrangian is
The Kuhn-Tucker conditions are
We solve this set of inequalities and equations by restricting our attention to the interior solution case (λ1 = λ2 = λ3 = 0).
The first-order conditions with respect to ph and f give:
Note that \(Q_{h}>\frac {\bar {\alpha }}{2}\) and \(Q_{s}\le \frac {\bar {\alpha }}{2}\). Thus, constraint (1) is satisfied. The first-order condition with respect to δ then gives
As in Fig. 2, the solution does not exist (i.e., the marginal return on δ is strictly positive for any δ) if the LHS is strictly greater than the RHS for all δ. It is easy to check that this is the case for \(\gamma <1-\frac {128C_{h}}{27\bar {\alpha }^{2}}\). In other words, when γ is very small, we expect a corner solution in which δ = 1.
Now consider \(\gamma \ge 1-\frac {128C_{h}}{27\bar {\alpha }^{2}}\). As γ increases, the RHS shifts down. Also, the RHS is equivalent to the software firm’s per-software profit ((ps(f) − f)Qs(f)). Thus, in order to satisfy constraint (3) (i.e., the software firm’s participation constraint), we need
The LHS is independent of γ, so there is a lower bound of γ that satisfies the first-order conditions and constraint (3). At the lower bound, we have \(\frac {\bar {\alpha }^{2}(1-\gamma )}{4(2-\delta )^{2}} = C_{h}\delta =\frac {C_{s}}{2}(1-\delta )\). Thus, the lower bound of δ is obtained as \(\delta = \frac {C_{s}}{2C_{h}+C_{s}}\). Substituting this into constraint (3), we get
Constraint (2) requires \(\gamma \ge \frac {v}{\bar {\alpha }}\). Because we focus on \(\gamma \ge 1-\frac {128C_{h}}{27\bar {\alpha }^{2}}\), constraint (2) is satisfied on this range as long as \(\frac {v}{\bar {\alpha }}\le 1-\frac {128C_{h}}{27\bar {\alpha }^{2}}\). This implies that \(C_{h}\le \frac {27\bar {\alpha }(\bar {\alpha }-v)}{128}\). Assumption 1 guarantees that the RHS is strictly positive. Thus, constraint (2) is satisfied as long as Ch is sufficiently low.
Next, we discuss the sufficient conditions. Recall that when \(\gamma \in \left (1-\frac {128C_{h}}{27\bar {\alpha }^{2}},1-\frac {4C_{h}}{\bar {\alpha }^{2}}\right ]\), two δ’s satisfy the first-order condition.Footnote 26 However, we can show that one of the δ’s that is greater than \(\frac {2}{3}\) is a saddle point (i.e., the point b in Fig. 2).
To see this, we check the second-order condition of the hardware firm’s problem. First note that \(\frac {\partial ^{2} \pi _{h}}{\partial p_{h} \partial f}=\frac {\partial ^{2} \pi _{h}}{\partial p_{h} \partial \delta }=0\) and \(\frac {\partial ^{2} \pi _{h}}{\partial ^{2} p_{h}}<0\). Thus, we only need to examine the condition for (f, δ). The Hessian is given by
We know that \(-\frac {2-\delta }{2(1-\gamma )}<0\), and
Since the denominator is positive, we only need to check the sign of the numerator. In order for H to be negative semidefinite, we need
Thus, we conclude that when \(\gamma \in \left (1-\frac {128C_{h}}{27\bar {\alpha }^{2}},1-\frac {4C_{h}}{\bar {\alpha }^{2}}\right ]\), one of the solutions for δ that is greater than \(\frac {2}{3}\) is a saddle point.
Finally, since the licensing fee is positive, it is easy to show that the hardware firm’s profits are larger than \(\bar {\alpha }v\).
1.4 A.4 Proof of Proposition 3b
First, it is easy to show that when \(\gamma <1-\frac {128C_{h}}{27\bar {\alpha }^{2}}\), the marginal return on δ becomes strictly positive for any δ. As a result, we have a corner solution with δ = 1. This is equivalent to the Full Integration case, and we have provided details in Appendix 1.
Now consider \(\gamma >1-\frac {4(4C_{h}+C_{s})^{2}C_{h}C_{s}}{(2C_{h}+C_{s})^{3}\bar {\alpha }^{2}}\), and recall the first-order conditions from Appendix 3a:
Since the constraint πs ≥ 0 is now binding, we have λ3 ≥ 0. Also, we know from Appendix 2 that when γ is even higher, the constraint Qh ≥ Qs binds. So for now, consider the case where λ2 = 0. Also, we know that we can satisfy \(Q_{h}\le \bar {\alpha }\) for sufficiently low Ch. The constraint πs = 0 gives:
This condition characterizes the relationship between δ and f and implies that δ increases monotonically as f increases. Moreover,
It is easy to check \(\frac {\partial \lambda _{3}}{\partial f}<0\), and thus λ3 is uniquely determined given f. The first-order condition with respect to δ is
It is easy to check that the LHS is monotonically decreasing in f. Thus, there is a unique f that satisfies the first-order condition. Since δ and λ3 are uniquely determined given f, there is a unique optimal strategy \((p_{h}^{*},f^{*},\delta ^{*})\) (note that \(p_{h}^{*}\) is the same as the interior solution).
Now consider the case where λ2, λ3 ≥ 0. We now have another constraint:
The first-order condition with respect to ph is now
Since λ2 ≥ 0, \(f<-\frac {(1-\gamma )v}{\gamma }\). The first-order condition with respect to f gives
We can check that λ3 monotonically decreases in f. The first-order condition with respect to δ is
We can also check that the LHS monotonically decreases in f. Thus, there is a unique f that satisfies the first-order condition. Since ph, δ, λ2 and δ3 are uniquely determined given f, there is a unique optimal strategy \((p_{h}^{*},f^{*},\delta ^{*})\).
Now we are interested in the sign of \(\frac {\partial \delta ^{*}}{\partial \gamma }\). It is difficult to analytically derive the sign. However, the optimal strategy is unique, so we can numerically solve for \((p_{h}^{*},f^{*},\delta ^{*})\) and examine how δ∗ changes with γ. Specifically, given \((\bar {\alpha },C_{h},C_{s})\), we solve for the optimal strategy \((p_{h}^{*},f^{*},\delta ^{*})\) over γ ∈ (0, 1). We use 10,000 evenly spaced grid points over (0, 1). We have tested extensive sets of \((\bar {\alpha },C_{h},C_{s})\), and consistently found that \(\frac {\partial \delta ^{*}}{\partial \gamma }>0\) for \(\gamma >1-\frac {4(4C_{h}+C_{s})^{2}C_{h}C_{s}}{(2C_{h}+C_{s})^{3}\bar {\alpha }^{2}}\).
1.5 A.5 Proof of Proposition 4a
Let pi and ps be the price of in-house and outsourced software, respectively, and pi is set by the hardware firm and ps is set by the software firm. We consider a case where we take our main analysis in Section 2.4 as the basis (except that we now assume v = 0) and allow pi to be set by the hardware firm.
We first derive the demand for in-house and outsourced software. As before, let ph be the price of hardware, δ be the proportion of in-house software, and α be the benefit from software. Consumers now have the following four options regarding software acquisition:
We show that regardless of whether pi is higher or lower than ps, the marginal consumer who is indifferent between buying and pirating in-house software depends only on pi, not ps, and the marginal consumer who is indifferent between buying and pirating outsourced software depends only on ps. To see this, first notice that the slope on α is the highest for (b,b) (the slope is 1), the lowest for (p,p) (the slope is γ). The slope on (b,p) (i.e., δ + (1 − δ)γ) is larger than the slope on (p,b) (i.e., δγ + (1 − δ)) if \(\delta >\frac {1}{2}\). Notice that the marginal consumer who is indifferent between (b,b) and (b,p) is given by \(\alpha =\frac {p_{s}}{1-\gamma }\). But the marginal consumer who is indifferent between (p,b) and (p,p) is also given by \(\frac {p_{s}}{1-\gamma }\). Consider the utility for each buying/pirating behavior at \(\alpha =\frac {p_{s}}{1-\gamma }\). Then, we know that the utility for (b,b) is equal to that for (b,p), and the utility for (p,b) is equal to that for (p,p). Comparing the utilities for (b,b) and (p,b) at \(\alpha =\frac {p_{s}}{1-\gamma }\), we know that the utility for (b,b) is higher than that for (p,b) when
Suppose ps > pi. Then, we know that \(\alpha \in \left [\frac {p_{s}}{1-\gamma },\bar {\alpha }\right ]\) will choose (b,b). Also, we know that for \(\alpha <\frac {p_{s}}{1-\gamma }\), the utility for (p,p) is higher than that for (p,b). Thus, no one chooses (p,b), and there is a marginal consumer who is indifferent between (b,p) and (p,p), which is given by \(\alpha =\frac {p_{i}}{1-\gamma }\). Thus, the segments will be: (b,b) for \(\alpha \in \left [\frac {p_{s}}{1-\gamma },\bar {\alpha }\right ]\), (b,p) for \(\alpha \in \left [\frac {p_{i}}{1-\gamma },\frac {p_{s}}{1-\gamma }\right ]\), and (p,p) for the rest who buys hardware.
Now suppose ps < pi. Then, we know that \(\alpha <\frac {p_{s}}{1-\gamma }\) will choose (p,p). Also, we know that for \(\alpha >\frac {p_{s}}{1-\gamma }\), the utility for (b,b) is higher than that for (b,p). Thus, no one chooses (b,p), and there is a marginal consumer who is indifferent between (p,b) and (b,b), which is given by \(\alpha =\frac {p_{i}}{1-\gamma }\). Thus, the segments will be: (b,b) for \(\alpha \in \left [\frac {p_{i}}{1-\gamma },\bar {\alpha }\right ]\), (p,b) for \(\alpha \in \left [\frac {p_{s}}{1-\gamma },\frac {p_{i}}{1-\gamma }\right ]\), and (p,p) for the rest who buys hardware.
The same logic applies when \(\delta <\frac {1}{2}\). In this case, the slope on α for (p,b) is larger than that for (b,p). But then the indifferent consumer for (b,b) and (p,b) \(\left (\frac {p_{i}}{1-\gamma }\right )\) is the same as that for (b,p) and (p,p). Thus, we just swap ps and pi and get the same result.
Thus, regardless of whether pi < ps or not and \(\delta >\frac {1}{2}\) or not, the per-unit demand for in-house and outsourced software will be given by
The software firm’s problem given (f, δ) is
The first-order condition with respect to ps gives
The hardware firm’s problem is now
subject to (1) Qh(ph) ≥ Qs(f), (2) \(Q_{h}(p_{h})\le \bar {\alpha }\), and (3) πs(f, δ) ≥ 0.Footnote 27 The Lagrangian is then given by
The Kuhn-Tucker conditions are
We first note that the FOC for pi is not influenced by the constraints. Solving the FOC gives
The per-unit gross profit of in-house software decreases in γ through a lower price. We solve this set of inequalities and equations.
We restrict our attention to the interior solution case (λ1 = λ2 = λ3 = 0). The FOC for ph gives:
The profit from hardware is increasing in γ. Next, the first-order condition with respect to f gives
We thus have
We note that \(\frac {\partial p_{i}Q_{i}}{\partial \gamma }<\frac {\partial fQ_{s}}{\partial \gamma }\). This is one driving force to push software development to the software firm when γ increases. This can be seen in the first-order condition for δ, which gives
Thus, we have \(\frac {\partial \delta }{\partial \gamma }<0\). Given δ ≤ 1, we require \(\gamma \ge 1-\frac {8C_{h}}{\bar {\alpha }^{2}}\).
With the optimal strategy, the software firm’s profit is
Thus πs ≥ 0 if and only if
Finally, hardware firm’s profit is
Also,
Thus, hardware firm benefits from piracy.
1.6 A.6 Proof of Proposition 4b
The proof here is similar to Appendix A.4. First, it is easy to show that when \(\gamma <1-\frac {8C_{h}}{\bar {\alpha }^{2}}\), the marginal return on δ becomes strictly positive for any δ. As a result, we have a corner solution with δ = 1. This is equivalent to the Full Integration case, and we have provided details in Appendix 1.
Now consider \(\gamma >1-\frac {8C_{h}C_{s}}{\bar {\alpha }^{2}(C_{h}+C_{s})}\), and recall the first-order conditions from Appendix A.5:
Since the constraint πs ≥ 0 is now binding, we have λ3 ≥ 0. Also, we know from Appendix 2 that when γ is even higher, the constraint Qh ≥ Qs binds. So for now, consider the case where λ2 = 0. Also, we know that we can satisfy \(Q_{h}\le \bar {\alpha }\) for sufficiently low Ch. The constraint πs = 0 gives:
This condition characterizes the relationship between δ and f and implies that δ increases monotonically as f increases. Moreover,
Since λ3 ≥ 0, \(f\le \frac {\bar {\alpha }(1-\gamma )}{2}\). It is easy to check \(\frac {\partial \lambda _{3}}{\partial f}<0\), and thus λ3 is uniquely determined given f. The first-order condition with respect to δ is
It is easy to check that the LHS is monotonically decreasing in f. Thus, there is a unique f that satisfies the first-order condition. Since δ and λ3 are uniquely determined given f, there is a unique optimal strategy \((p_{h}^{*},f^{*},\delta ^{*})\) (note that \(p_{h}^{*}\) is the same as the interior solution).
Now consider the case where λ2, λ3 ≥ 0. We now have another constraint:
The first-order condition with respect to ph is now
Since λ2 ≥ 0, f < 0. The first-order condition with respect to f gives
We can check that λ3 monotonically decreases in f. The first-order condition with respect to δ is
We can also check that the LHS monotonically decreases in f. Thus, there is a unique f that satisfies the first-order condition. Since δ, ph, λ2 and δ3 are uniquely determined given f, there is a unique optimal strategy \((p_{h}^{*},f^{*},\delta ^{*})\).
We are interested in the sign of \(\frac {\partial \delta ^{*}}{\partial \gamma }\). Similar to Appendix app4A.4, it is difficult to analytically derive the sign. Thus we numerically examine it using a similar approach described there. Again, we consistently found that \(\frac {\partial \delta ^{*}}{\partial \gamma }>0\) for \(\gamma >1-\frac {8C_{h}C_{s}}{\bar {\alpha }^{2}(C_{h}+C_{s})}\).
1.7 A.7 Proof of Proposition 5
The software firm’s profit is
The first-order conditions with respect to ps and ns give:
Given ps and ns(f), the hardware firm’s problem is
where ph is the price of hardware, Qh is the demand for hardware (\(Q_{h}=\bar {\alpha }-\frac {p_{h}}{(n_{i}+n_{s}(f))\gamma })\), pi is the price of in-house software, Qi is the demand for in-house software (\(Q_{i}(p_{i})=\bar {\alpha }-\frac {p_{i}}{1-\gamma }\)).
First, pi influences only the in-house software profit, so can be simply determined by \(\frac {\partial \pi _{h}}{\partial p_{i}}=0\):
Thus the problem now is
The hardware firm maximizes the profit subject to Qh(ph, ni, f) ≥ Qs(f) and πs(f) ≥ 0. However, the latter is always satisfied because the software firm can choose ns optimally. Thus, we consider two scenarios based on the first constraint.
- 1.
Qh ≥ Qs is not binding:
$$ \pi_{h}(p_{h},n_{i},f) = p_{h}Q_{h}(p_{h},n_{i},f)+n_{i}\frac{\bar{\alpha}^{2}(1-\gamma)}{4}+n_{s}(f) f Q_{s}(f) - \frac{C_{h}{n_{i}^{2}}}{2}. $$The first-order conditions are:
$$ \begin{array}{@{}rcl@{}} \frac{\partial \pi_{h}}{\partial p_{h}} &=& \bar{\alpha}-\frac{2p_{h}}{\gamma(n_{i}+n_{s})} = 0 \Longleftrightarrow p_{h}=\frac{\bar{\alpha}\gamma(n_{i}+n_{s})}{2},\ Q_{h}=\frac{\bar{\alpha}}{2}\\ \frac{\partial \pi_{h}}{\partial n_{i}} &=& \frac{\bar{\alpha}^{2}\gamma}{4} + \frac{\bar{\alpha}^{2}(1-\gamma)}{4} - C_{h} n_{i}=0 \Longleftrightarrow n_{i}=\frac{\bar{\alpha}^{2}}{4C_{h}}\\ \frac{\partial \pi_{h}}{\partial f} &=&\frac{\bar{\alpha}^{2}\gamma}{4}n_{s}^{\prime} + n_{s}^{\prime}(fQ_{s})+n_{s}(fQ_{s})'=0 \end{array} $$Note that f influences πh in two channels: via ns and via fQs:
$$ \frac{\partial \pi_{h}}{\partial f} =\left[\frac{\bar{\alpha}^{2}\gamma}{4}+fQ_{s}\right]n_{s}^{\prime} + n_{s}(fQ_{s})' $$The first term captures the return on f via ns and the second term is the direct return on f. Solving the FOC, we get
$$ f = \frac{5\bar{\alpha}(1-\gamma)\pm\bar{\alpha}\sqrt{(1-\gamma)(9+7\gamma)}}{8}. $$Note that \((1-\gamma )(9+7\gamma )=9(1-\gamma )(1+\frac {7}{9}\gamma )>9(1-\gamma )^{2}\). Thus,
$$ \frac{5\bar{\alpha}(1-\gamma)+\bar{\alpha}\sqrt{(1-\gamma)(9+7\gamma)}}{8}> \frac{5\bar{\alpha}(1-\gamma)+3\bar{\alpha}(1-\gamma)}{8}=\bar{\alpha}(1-\gamma). $$Since \(f\le \bar {\alpha }(1-\gamma )\), the optimal f is
$$ f = \frac{5\bar{\alpha}(1-\gamma)-\bar{\alpha}\sqrt{(1-\gamma)(9+7\gamma)}}{8}. $$We thus have
$$ \begin{array}{@{}rcl@{}} p_{s} = \frac{\bar{\alpha}(1-\gamma)\left( 13-\sqrt{\frac{9+7\gamma}{1-\gamma}}\right)}{16}, Q_{s} = \frac{\bar{\alpha}\left( 3+\sqrt{\frac{9+7\gamma}{1-\gamma}}\right)}{16} \end{array} $$Since we require \(Q_{s}\le Q_{h}=\frac {\bar {\alpha }}{2}\),
$$ \begin{array}{@{}rcl@{}} \frac{\bar{\alpha}\left( 3+\sqrt{\frac{9+7\gamma}{1-\gamma}}\right)}{16} \le \frac{\bar{\alpha}}{2} \Longleftrightarrow \gamma \le \frac{1}{2}. \end{array} $$For \(\gamma \le \frac {1}{2}\), \(\frac {\partial f}{\partial \gamma }<0\). Also, note that
$$ \begin{array}{@{}rcl@{}} p_{s}-f =\frac{\bar{\alpha}(1-\gamma)\left( 3+\sqrt{\frac{9+7\gamma}{1-\gamma}}\right)}{16} \end{array} $$Thus,
$$ \begin{array}{@{}rcl@{}} n_{s} = \frac{(p_{s}-f)Q_{s}}{C_{s}}=\frac{K\bar{\alpha}^{2}}{256}\left( 3\sqrt{1-\gamma}+\sqrt{9+7\gamma}\right)^{2} \end{array} $$and
$$ \begin{array}{@{}rcl@{}} \frac{\partial n_{s}}{\partial \gamma} = \frac{\bar{\alpha}^{2}}{128C_{s}}\left( 3\sqrt{1-\gamma}+\sqrt{9+7\gamma}\right)\left( -\frac{3}{2\sqrt{1-\gamma}}+\frac{7}{2\sqrt{9+7\gamma}}\right). \end{array} $$It is straightforward to show that \(\frac {\partial n_{s}}{\partial \gamma }<0\).
Finally, we check πh:
$$ \begin{array}{@{}rcl@{}} \pi_{h} &=& p_{h}Q_{h} + n_{i}p_{i}Q_{i} + n_{s}fQ_{s} - \frac{C_{h}{n_{i}^{2}}}{2}\\ &=&\frac{\bar{\alpha}^{2}\gamma(n_{i}+n_{s})}{4} + n_{i}\frac{\bar{\alpha}^{2}(1-\gamma)}{4} + n_{s} fQ_{s} - \frac{C_{h}{n_{i}^{2}}}{2}\\ &=&\left[\frac{\bar{\alpha}^{2}\gamma}{4}+fQ_{s}\right]n_{s} + \frac{\bar{\alpha}^{2}}{4}n_{i}-\frac{C_{h}}{2}{n_{i}^{2}}\\ &=&\left[\frac{\bar{\alpha}^{2}\gamma}{4}+fQ_{s}\right]n_{s} + \frac{\bar{\alpha}^{4}}{32C_{h}}>0. \end{array} $$Thus hardware firm is in business. Also, we check how γ influences πh. Note that
$$ \begin{array}{@{}rcl@{}} \frac{\partial \pi_{h}}{\partial \gamma} = \left[\frac{\bar{\alpha}^{2}}{4}+\frac{\partial (fQ_{s})}{\partial \gamma}\right]n_{s} + \left[\frac{\bar{\alpha}^{2}\gamma}{4}+fQ_{s}\right]\frac{\partial n_{s}}{\partial \gamma} \end{array} $$where a change in γ influences (1) the marginal return on ns (i.e., first bracket) and (2) ns (i.e., \(\frac {\partial n_{s}}{\partial \gamma }\)). First,
$$ \begin{array}{@{}rcl@{}} fQ_{s} &=& \frac{\bar{\alpha}^{2}(5\sqrt{1-\gamma}-\sqrt{9+7\gamma})(3\sqrt{1-\gamma}+\sqrt{9+7\gamma})}{128}>0\ \forall \gamma\le\frac{1}{2}\\ \frac{\partial (fQ_{s})}{\partial \gamma} &=& \frac{\bar{\alpha}^{2}\left( 7(1-\gamma)-(9+7\gamma)-22\sqrt{(1-\gamma)(9+7\gamma)}\right)}{64\sqrt{(1-\gamma)(9+7\gamma)}} <0\ \forall \gamma \end{array} $$It can be shown that the change in marginal return on ns due to an increase in γ is negative:
$$ \left[\frac{\bar{\alpha}^{2}}{4}+\frac{\partial (fQ_{s})}{\partial \gamma}\right]=\frac{\bar{\alpha}^{2}}{64AB}(7A+B)(A-B)<0 $$where \(A=\sqrt {1-\gamma }\) and \(B=\sqrt {9+7\gamma }\). Then
$$ \begin{array}{@{}rcl@{}} \frac{\partial \pi_{h}}{\partial \gamma} &=& \left[\frac{\bar{\alpha}^{2}}{4}+\frac{\bar{\alpha}^{2}(7A^{2}-B^{2}-22AB)}{64AB}\right]\frac{K\bar{\alpha}^{2}(3A+B)^{2}}{256}\\ &&+\left[\frac{\bar{\alpha}^{2}\gamma}{4} + \frac{\bar{\alpha}^{2}(5A-B)(3A+B)}{128}\right]\frac{K\bar{\alpha}^{2}(3A+B)(7A-3B)}{256AB}\\ &=&\frac{\bar{\alpha}^{2}(16AB+7A^{2}-B^{2}-22AB)}{64AB}\frac{K\bar{\alpha}^{2}(3A+B)^{2}}{256}\\ &&+\frac{\bar{\alpha}^{2}(32\gamma+(5A-B)(3A+B)}{128}\frac{K\bar{\alpha}^{2}(3A+B)(7A-3B)}{256AB}\\ &=&\frac{K\bar{\alpha}^{4}(3A+B)}{128\cdot256AB}\left[2(7A+B)(A-B)(3A+B)\right.\\ &&\left.-[32\gamma+(5A-B)(3A+B)](7A-3B)\right] \end{array} $$Note \(\frac {K\bar {\alpha }^{4}(3A+B)}{128\cdot 256AB}>0\). Thus, we drop it and focus on
$$ S\equiv 2(7A+B)(A-B)(3A+B)-[32\gamma+(5A-B)(3A+B)](7A-3B) $$First, we note that when \(\gamma \le \frac {1}{2}\),
$$ S = 2\underbrace{(7A+B)}_{+}\underbrace{(A-B)}_{-}\underbrace{(3A+B)}_{+} -[32\gamma+\underbrace{(5A-B)}_{+}\underbrace{(3A+B)}_{+}]\underbrace{(7A-3B)}_{-} $$Thus, its sign could depend on γ. This expression can be simplified as
$$ S = -108A-196\gamma A - 36B + 52\gamma B < 0\ \forall \gamma\le\frac{1}{2} $$because \((-36 + 52\gamma )<0\ \forall \gamma \le \frac {1}{2}\). Thus, \(\frac {\partial \pi _{h}}{\partial \gamma }<0\) in this scenario.
- 2.
Qh = Qs:
This happens when γ is high (i.e., \(\gamma >\frac {1}{2}\)) and f < 0. Recall that the constraint implies
$$ \bar{\alpha}-\frac{p_{h}}{(n_{i}+n_{s})\gamma)} = \bar{\alpha} - \frac{p_{s}}{1-\gamma}\ \Longleftrightarrow\ p_{h} = \frac{\gamma(n_{i}+n_{s})}{1-\gamma}p_{s} $$Thus the profit from hardware can be written as
$$ p_{h}Q_{h}=\frac{\gamma(n_{i}+n_{s})}{1-\gamma}p_{s}Q_{s}=\frac{\bar{\alpha}^{2}(1-\gamma)^{2}-f^{2}}{4(1-\gamma)} $$The hardware firm’s profit is now
$$ \begin{array}{@{}rcl@{}} \pi_{h}(n_{i},f) &=& \frac{\gamma(n_{i}+n_{s}(f))}{1-\gamma}\frac{\bar{\alpha}^{2}(1-\gamma)^{2}-f^{2}}{4(1-\gamma)}+n_{i}\frac{\bar{\alpha}^{2}(1-\gamma)}{4}\\ &&+n_{s}(f) f Q_{s}(f) - \frac{C_{h}{n_{i}^{2}}}{2}. \end{array} $$First, the FOC with respect to ni is
$$ \frac{\partial \pi_{h}}{\partial n_{i}} = \frac{\gamma}{1-\gamma}\frac{\bar{\alpha}^{2}(1-\gamma)^{2}-f^{2}}{4(1-\gamma)} + \frac{\bar{\alpha}^{2}(1-\gamma)}{4}-C_{h} n_{i}=0 $$We then get
$$ n_{i} = \frac{\bar{\alpha}^{2}(1-\gamma)^{2}-\gamma f^{2}}{4C_{h}(1-\gamma)^{2}}. $$Note that this is less than \(\frac {\bar {\alpha }^{2}}{4C_{h}}\) (optimal ni when \(\gamma \le \frac {1}{2}\)). Next, the FOC with respect to f is
$$ \begin{array}{@{}rcl@{}} \frac{\partial \pi_{h}}{\partial f} &= \frac{\gamma}{1-\gamma}n_{s}^{\prime}(p_{s}Q_{s})+\frac{\gamma(n_{i}+n_{s})}{1-\gamma}(p_{s}Q_{s})' + n_{s}^{\prime}(fQ_{s})+n_{s}(fQ_{s})'=0, \end{array} $$where
$$ \begin{array}{@{}rcl@{}} \frac{\gamma}{1-\gamma}n_{s}^{\prime}(p_{s}Q_{s})&=&\frac{\gamma}{1-\gamma}\left( -\frac{\bar{\alpha}(1-\gamma)-f}{2(1-\gamma)C_{s}}\right)\left( \frac{\bar{\alpha}^{2}(1-\gamma)^{2}-f^{2}}{4(1-\gamma)}\right)\\ &=& -\frac{\gamma(\bar{\alpha}(1-\gamma)-f)^{2}(\bar{\alpha}(1-\gamma)+f)}{8(1-\gamma)^{3}C_{s}}\\ \frac{\gamma(n_{i}+n_{s})}{1-\gamma}(p_{s}Q_{s})^{\prime}\!&=&\!\frac{\gamma}{1-\gamma}\left[\frac{\bar{\alpha}^{2}(1-\gamma)^{2}-\gamma f^{2}}{4(1-\gamma)^{2}C_{h}}+\frac{(\bar{\alpha}(1-\gamma)-f)^{2}}{4(1-\gamma)C_{s}}\right]\\ &&\!\times \left( -\frac{f}{2(1-\gamma)}\right)\frac{\gamma}{1-\gamma}n_{s}^{\prime}(p_{s}Q_{s}) + \frac{\gamma(n_{i}+n_{s})}{1-\gamma}(p_{s}Q_{s})^{\prime}\\ \!&=&\!-\frac{\gamma(\bar{\alpha}(1-\gamma)-f)^{2}(\bar{\alpha}(1-\gamma)+2f)}{8(1-\gamma)^{3}C_{s}}\\ &&- \frac{\gamma(\bar{\alpha}^{2}(1-\gamma)^{2}-\gamma f^{2})f}{8(1-\gamma)^{4}C_{h}} \end{array} $$and
$$ \begin{array}{@{}rcl@{}} n_{s}^{\prime}(fQ_{s})&=&\left( -\frac{\bar{\alpha}(1-\gamma)-f}{2(1-\gamma)C_{s}}\right)\left( \frac{\bar{\alpha}(1-\gamma)-f)f}{2(1-\gamma)}\right)\\ &=& -\frac{(\bar{\alpha}(1-\gamma)-f)^{2}f}{4(1-\gamma)^{2}C_{s}}\\ n_{s}(fQ_{s})^{\prime}&=&\left( \frac{(\bar{\alpha}(1-\gamma)-f)^{2}}{4(1-\gamma)C_{s}}\right)\left( \frac{\bar{\alpha}(1-\gamma)-2f}{2(1-\gamma)}\right)\\ &=& \frac{(\bar{\alpha}(1-\gamma)-f)^{2}(\bar{\alpha}(1-\gamma)-2f)}{8(1-\gamma)^{2}C_{s}}\\ n_{s}^{\prime}(fQ_{s})+n_{s}(fQ_{s})^{\prime}&=&\frac{(\bar{\alpha}(1-\gamma)-f)^{2}(\bar{\alpha}(1-\gamma)-4f)}{8(1-\gamma)^{2}C_{s}} \end{array} $$Thus,
$$ \begin{array}{@{}rcl@{}} \frac{\partial \pi_{h}}{\partial f} &=&-\frac{\gamma(\bar{\alpha}(1-\gamma)-f)^{2}(\bar{\alpha}(1-\gamma)+2f)}{8(1-\gamma)^{3}C_{s}} - \frac{\gamma(\bar{\alpha}^{2}(1-\gamma)^{2}-\gamma f^{2})f}{8(1-\gamma)^{4}C_{h}}\\ &&+ \frac{(\bar{\alpha}(1-\gamma)-f)^{2}(\bar{\alpha}(1-\gamma)-4f)}{8(1-\gamma)^{2}C_{s}}\\ &=&\frac{(\bar{\alpha}(1-\gamma)-f)^{2}(\bar{\alpha}(1-\gamma)(1-2\gamma)-2(2-\gamma)f)}{8(1-\gamma)^{3}C_{s}}\\ &&- \frac{\gamma(\bar{\alpha}^{2}(1-\gamma)^{2}-\gamma f^{2})f}{8(1-\gamma)^{4}C_{h}} \end{array} $$We note that since \(f\in [-\bar {\alpha }(1-\gamma ),0]\) (otherwise, we have Qs < Qh or \(Q_{s}>\bar {\alpha }\)), we have \(\bar {\alpha }^{2}(1-\gamma )^{2}-\gamma f^{2}>0\). Thus, the second component is positive
$$ -\frac{\gamma(\bar{\alpha}^{2}(1-\gamma)^{2}-\gamma f^{2})f}{8(1-\gamma)^{4}C_{h}} >0 $$and zero only when f = 0. Thus the first component needs to be negative, or zero (when f = 0). First, the first component under f = 0 becomes zero only when \(\gamma =\frac {1}{2}\). Thus, this is one solution, and consistent with the previous case where Qh ≥ Qs. For \(\gamma >\frac {1}{2}\) and f < 0, the first component is negative if
$$ \bar{\alpha}(1-\gamma)(1-2\gamma)-2(2-\gamma)f<0\Leftrightarrow f>\frac{\bar{\alpha}(1-\gamma)(1-2\gamma)}{2(2-\gamma)}. $$So when \(\gamma >\frac {1}{2}\), \(f\in (\frac {\bar {\alpha }(1-\gamma )(1-2\gamma )}{2(2-\gamma )},0)\). Now rewrite the FOC as
$$ \begin{array}{@{}rcl@{}} \frac{\partial \pi_{h}}{\partial f} \!&=&\!\frac{(\bar{\alpha}^{2}(1-\gamma)^{2}-\gamma f^{2})}{8(1-\gamma)^{3}C_{s}}\\ &&\!\times \left( \frac{(\bar{\alpha}(1-\gamma)-f)^{2}(\bar{\alpha}(1-\gamma)(1-2\gamma)-2(2-\gamma)f)}{(\bar{\alpha}^{2}(1-\gamma)^{2}-\gamma f^{2})}-\frac{\gamma C_{s}f}{(1-\gamma)C_{h}}\right) \end{array} $$Let
$$ \begin{array}{@{}rcl@{}} A(f) &\equiv& \frac{(\bar{\alpha}(1-\gamma)-f)^{2}(\bar{\alpha}(1-\gamma)(1-2\gamma)-2(2-\gamma)f)}{(\bar{\alpha}^{2}(1-\gamma)^{2}-\gamma f^{2})}\\ B(f) &\equiv& \frac{\gamma C_{s}f}{(1-\gamma)C_{h}} \end{array} $$and consider their values on \(f\in (\frac {\bar {\alpha }(1-\gamma )(1-2\gamma )}{2(2-\gamma )},0)\). First, B(f) increases monotonically in f and
$$ B(f=\frac{\bar{\alpha}(1-\gamma)(1-2\gamma)}{2(2-\gamma)})<0\text{and} B(f=0)=0 $$Also, we can show
$$ A(f=\frac{\bar{\alpha}(1-\gamma)(1-2\gamma)}{2(2-\gamma)}) = 0\text{and} A(f=0)<0 $$Thus, if A(f) decreases monotonically in f, we have a unique f that satisfies the FOC. Now let
$$ \begin{array}{@{}rcl@{}} C(f)&=&\bar{\alpha}(1-\gamma)-f,\quad D(f)=\bar{\alpha}(1-\gamma)(1-2\gamma)-2(2-\gamma)f, \\ E(f) &=&\bar{\alpha}^{2}(1-\gamma)^{2}-\gamma f^{2} \end{array} $$and note that for \(f\in (\frac {\bar {\alpha }(1-\gamma )(1-2\gamma )}{2(2-\gamma )},0)\), C(f) > 0, D(f) < 0, E(f) > 0, and
$$ C(f)'=-1,\ D(f)'=-2(2-\gamma),\ E(f)'=-2\gamma f $$Then \(A(f)=\frac {C(f)^{2}D(f)}{E(f)}\) and
$$ \begin{array}{@{}rcl@{}} \frac{\partial A(f)}{\partial f} &=& \frac{[2C(f)C(f)'D(f)+C(f)^{2}D(f)']E(f)-C(f)^{2}D(f)E(f)'}{E(f)^{2}}\\ &=&\frac{[-2D(f)-2(2-\gamma)C(f)]C(f)E(f)+2\gamma fC(f)^{2}D(f)}{E(f)^{2}}\\ &=&-\frac{2C(f)}{E(f)^{2}}\left( \left[D(f)+(2-\gamma)C(f)\right]E(f)-\gamma fC(f)D(f)\right) \end{array} $$Since \(\frac {C(f)}{E(f)^{2}}>0\), the sign of \(\frac {\partial A(f)}{\partial f}\) depends on \(\left [D(f)+(2-\gamma )C(f)\right ]E(f)-\gamma fC(f)D(f)\). Let this be F and note that
$$ \begin{array}{@{}rcl@{}} F \!&=&\! \left[(\bar{\alpha}(1-\gamma)(1-2\gamma)-2(2-\gamma)f)+(2-\gamma)(\bar{\alpha}(1-\gamma)-f)\right] \\ &&\times (\bar{\alpha}^{2}(1-\gamma)^{2}-\gamma f^{2})-\gamma f (\bar{\alpha}(1-\gamma)-f)(\bar{\alpha}(1-\gamma)(1-2\gamma)-2(2-\gamma)f)\\ \!&=&\! 3\left[\bar{\alpha}(1-\gamma)^{2}-(2-\gamma)f\right] (\bar{\alpha}^{2}(1-\gamma)^{2}-\gamma f^{2})\\ &&-\gamma f\left[\bar{\alpha}^{2}(1-\gamma)^{2}(1-2\gamma)-2\bar{\alpha}(1-\gamma)(2-\gamma)f\right.\\&&\left.-\bar{\alpha}(1-\gamma)(1-2\gamma)f+2(2-\gamma)f\vphantom{\bar{\alpha}^{2}}\right]\\ \!&=&\! 3\bar{\alpha}^{3}(1-\gamma)^{4}-3\bar{\alpha}(1-\gamma)^{2}\gamma f^{2}-3(2-\gamma)f\bar{\alpha}^{2}(1-\gamma)^{2}+3(2-\gamma)\gamma f^{3}\\ &&-\bar{\alpha}^{2}(1\!-\gamma)^{2}(1\!-2\gamma)\gamma f+\bar{\alpha}(1\!-\gamma)\gamma f^{2} (4\!-2\gamma+1\!-2\gamma)- 2(2\!-\gamma)\gamma f^{3}\\ \!&=&\! 3\bar{\alpha}^{3}(1-\gamma)^{4} - f\bar{\alpha}^{2}(1-\gamma)^{2}[6-3\gamma+\gamma-2\gamma^{2}] + f^{2}\bar{\alpha}(1-\gamma)\\ &&\times \gamma[5-4\gamma-3+3\gamma] - (2-\gamma)\gamma f^{3}\\ \!&=&\!\underbrace{3\bar{\alpha}^{3}(1-\gamma)^{4}}_{+} - \underbrace{2f\bar{\alpha}^{2}(1-\gamma)^{2}[3-\gamma-\gamma^{2}]}_{-} + \underbrace{f^{2}\bar{\alpha}(1-\gamma)(2-\gamma)\gamma}_{+}\\ &&- \underbrace{(2-\gamma)\gamma f^{3}}_{-}\\ &>&0 \end{array} $$Thus \(\frac {\partial A(f)}{\partial f}<0\) and the solution of f is unique and lies on \((\frac {\bar {\alpha }(1-\gamma )(1-2\gamma )}{2(2-\gamma )},0)\). We can also show that for a given δ, an increase in \(\frac {C_{s}}{C_{h}}\) increases the optimal f (i.e., less negative). This is due to the fact that as it costs less to develop in-house software (relative to outsourced software), the hardware firm increases in-house production (relative to outsourced production) so it can lower the “subsidy” to the software firm.
Since the optimal strategy is unique, we use numerical analyses to examine: (1) \(\frac {\partial f}{\partial \gamma }\), (2) \(\frac {\partial n_{i}}{\partial \gamma }\), \(\frac {\partial n_{s}}{\partial \gamma }\), and (3) \(\frac {\partial \pi _{h}}{\partial \gamma }\) and \(\frac {\partial \pi _{s}}{\partial \gamma }\). As before, for extensive sets of \((\bar {\alpha },C_{h},C_{s})\), we observe the following:
There exists \(\gamma _{1}\in \left (\frac {1}{2},1\right )\) such that \(\frac {\partial f}{\partial \gamma }<0\) for \(\gamma \in \left (\frac {1}{2},\gamma _{1}\right )\) and \(\frac {\partial f}{\partial \gamma }>0\) for γ ∈ (γ1, 1).
\(\frac {\partial n_{i}}{\partial \gamma }<0\) and \(\frac {\partial n_{s}}{\partial \gamma }<0\) for all \(\gamma >\frac {1}{2}\). Also, the proportion of outsourced software \(\left (\frac {n_{s}}{n_{i}+n_{s}}\right )\) is decreasing in γ.
\(\frac {\partial \pi _{h}}{\partial \gamma }<0\) and \(\frac {\partial \pi _{s}}{\partial \gamma }<0\) for all \(\gamma >\frac {1}{2}\).
1.8 A.8 Proof of Proposition 6
Let f ∈ [0, 1] be the proportion of the outsourced software revenue taken by the hardware firm. Then the software firm’s profit is
The first-order conditions with respect to ps and ns give:
The hardware firm’s profit is then
The first-order conditions with respect to ph, pi, ni give
The first-order condition with respect to f is
Since we require f ∈ [0, 1], the above result is supported when \(\gamma \le \frac {1}{2}\). Given f, we have
When \(\gamma >\frac {1}{2}\) (i.e., f = 0 is binding), the optimal quantity of outsourced software is \(n_{s}=\frac {\bar {\alpha }^{2}(1-\gamma )}{4C_{s}}\). Other strategies will remain the same as above.
Now we consider a case in which the total software variety is fixed at one and the hardware firm chooses the proportion of in-house software. The software firm’s profit in this case is
The first-order condition with respect to ps gives
The hardware firm’s profit is
We first note that \(\frac {\partial \pi _{h}}{\partial f}=(1-\delta )p_{s}Q_{s}>0\) when δ < 1. Thus, we only have a corner solution where the hardware firm will choose f based on the condition that πs = 0, which gives
Thus, we can re-write the hardware firm’s profit as
The first-order conditions with respect to ph and pi give
The first-order condition with respect to δ is
Thus we have
Since we require f ≥ 0, the above is valid when
Note that under the optimal δ and f, the hardware firm’s profits are given by
which is greater than the profits under Full Integration \(\frac {\bar {\alpha }^{2}}{4}-\frac {C_{h}}{2}\) for all Ch, Cs > 0.
When \(\gamma \ge 1-\frac {2C_{h}C_{s}}{(C_{h}+C_{s})\bar {\alpha }^{2}}\), we have f = 0 and πs = 0. These constraints give \(\delta = 1-\frac {\bar {\alpha }^{2}(1-\gamma )}{2C_{s}}\). We also note than under the optimal δ and f, the hardware firm’s profits are given by
This is higher than the profits under Full Integration if \(\gamma \ge 1- \frac {4C_{h}C_{s}}{(C_{h}+C_{s})\bar {\alpha }^{2}}\). This condition is satisfied because \(1-\frac {2C_{h}C_{s}}{(C_{h}+C_{s})\bar {\alpha }^{2}}>1- \frac {4C_{h}C_{s}}{(C_{h}+C_{s})\bar {\alpha }^{2}}\).
In summary, the results under the proportional licensing fee are weakly consistent with those under the per-unit licensing fee.
Rights and permissions
About this article
Cite this article
Ishihara, M., Muller, E. Software piracy and outsourcing in two-sided markets. Quant Mark Econ 18, 61–124 (2020). https://doi.org/10.1007/s11129-019-09221-7
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11129-019-09221-7