Abstract
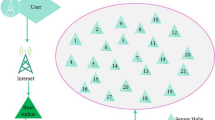
In wireless sensor networks (WSNs), the implemented conventional intrusion detection frame works need more energy and computation time, which impact the overall WSNs lifespan. Additionally, few of these models create considerable IDS traffic volume, which creates congestion band width constrained of WSN. This paper presents a new hierarchical type intrusion detection system for determining the malicious sensor nodes. This recommended intrusion detection framework is mainly works in two levels (1) Rule-based specification-based detection system (Level 1) and (2) Anomaly-based IDS via clustering (Level 2). In the initial phase, the IDS agent monitors the other sensor node for maliciousness using the specific set of rules. Owing to the second phase, the cluster head monitors the other cluster head for maliciousness, which is performed via Deep Belief Network (DBN) model, which is already trained with the node parameters. In order to make precise prediction process, this paper involves the optimization concept, which optimally tunes the weight of DBN by introducing a new hybrid optimization algorithm which named as Cuckoo Insisted Lion Algorithm, is the combination of Cuckoo Search and Lion Algorithm. In this recommended model, the overall performance is verified over the other modernization models relating to certain prediction parameters.











Similar content being viewed by others
Data availability
Data available on request from the authors.
References
Abadi, M.: Explicit communication revisited: two new attacks on authentication protocols. IEEE Trans. Software Eng. 23(3), 185–186 (1997)
Abdullah, M.A., Nada, E.A.: Energy efficient cluster-based intrusion detection system for wireless sensor networks. Int. J. Adv.Comput. Sci. Appl. 5, 10–15 (2014)
Ahn, J., Krishnamachari, B.: Scaling laws for data-centric storage and querying in wireless sensor networks. IEEE/ACM Trans. Netw. 17(4), 1242–1255 (2009)
Angove, P., O’Grady, M., Hayes, J., O’Flynn, B., O’Hare, G.M.P., Diamond, D.: A mobile gateway for remote interaction with wireless sensor networks. IEEE Sens. J. 11(12), 3309–3310 (2011)
Blum, C., Lozano, J.A., Davidson, P.P.: An artificial bioindicator system for network intrusion detection. Artif. Life 21(2), 93–118 (2015)
Borkar, G.M., Patil, L.H., Dalgade, D., Hutke, A.: A novel clustering approach and adaptive SVM classifier for intrusion detection in WSN: a data mining concept. Sustain. Comput.: Inform. Syst. 23, 120–135 (2019)
Cauteruccio, F., Fortino, G., Guerrieri, A., Liotta, A., Vega, M.T.: Short-long term anomaly detection in wireless sensor networks based on machine learning and multi-parameterized edit distance. Inform. Fus. 52, 13–30 (2019)
Cheng, L., Niu, J., Di Francesco, M., Das, S.K., Luo, C., Gu, Y.: Seamless streaming data delivery in cluster-based wireless sensor networks with mobile elements. IEEE Syst. J. 10(2), 805–816 (2016)
Cho, J.J., Ding, Y., Chen, Y., Tang, J.: Robust calibration for localization in clustered wireless sensor networks. IEEE Trans. Autom. Sci. Eng. 7(1), 81–95 (2010)
Han, G., Jiang, J., Shen, W., Shu, L., Rodrigues, J.: IDSEP: a novel intrusion detection scheme based on energy prediction in cluster-based wireless sensor networks. IET Inf. Secur. 7(2), 97–105 (2013)
Hong, J., Liu, C.: Intelligent electronic devices with collaborative intrusion detection systems. IEEE Trans. Smart Grid 10(1), 271–281 (2019)
Hosseini, S.M., Kahaei, M.H.: Target detection in cluster based WSN with massive MIMO systems. Electron. Lett. 53(1), 50–52 (2017)
Kim, D., An, S.: PKC-based dos attacks-resistant scheme in wireless sensor networks. IEEE Sens. J 16(8), 2217–2218 (2016)
Madhura Mahajan, K.T.V., Reddy, M.R.: Design and simulation of a blacklisting technique for detection of hello flood attack on LEACH protocol. Proc. Comput. Sci. 79, 675–682 (2016)
Mareli, M., Twala, B.: An adaptive cuckoo search algorithm for optimisation. Appl. Soft Comput. 37, 332–344 (2015)
Mehmood, A., Khanan, A., Umar, M.M., Abdullah, S., Ariffin, K.A.Z., Song, H.: Secure knowledge and cluster-based intrusion detection mechanism for smart wireless sensor networks. IEEE Access 6, 5688–5694 (2018)
Noor Alsaedi, F.H., Sali Fakhrul, A., Rokhani, Z.: Detecting sybil attacks in clustered wireless sensor networks based on energy trust system (ETS). Comput. Commun. 110, 75–82 (2017)
Sandhya, R., Sengottaiyan, N.: Dynamic CH selection and intrusion detection in WSN using reinforced weighted approximation based adaptive SEECH: an optimized routing framework. Int. J. Appl Eng. Res. 12(20), 9315–9326 (2017)
Shahaboddin Shamshirband, A.A., Badrul Anuar, N., Kiah, M.L., WahTeh, Y.: D-FICCA: a density-based fuzzy imperialist competitive clustering algorithm for intrusion detection in wireless sensor networks. Measurement 55, 212–226 (2014)
Silawan, T., Aswakul, C.: SybilVote: formulas to quantify the success probability of sybil attack in online social network voting. IEEE Commun. Lett. 21(7), 1553–1556 (2017)
Subba, B., Biswas, S.: A game theory based multi layered intrusion detection framework for wireless sensor networks. Int. J. Wireless Inf. Netw. 25(4), 399–421 (2018)
Wang, S.S., Yan, K.Q., Wang, S.C., Liu, C.W.: An integrated intrusion detection system for cluster-based wireless sensor networks. Expert Syst. Appl. 12, 15234 (2011)
Wang, C., Li, J., Yang, Y., Ye, F.: Combining solar energy harvesting with wireless charging for hybrid wireless sensor networks. IEEE Trans. Mob. Comput. 17(3), 560–576 (2018)
Wei, M., Kim, K.: Intrusion detection scheme using traffic prediction for wireless industrial networks. J. Commun. Netw. 14(3), 310–318 (2012)
Wei, W., Xu, F., Tan, C.C., Li, Q.: SybilDefender: a defense mechanism for sybil attacks in large social networks. IEEE Trans. Parallel Distrib. Syst. 24(12), 2492–2502 (2013)
Yu, M., Zhou, M., Su, W.: A secure routing protocol against byzantine attacks for MANETs in adversarial environments. IEEE Trans. Veh. Technol. 58(1), 449–460 (2009)
Zheng, J., Wang, P., Li, C.: Distributed data aggregation using slepian-wolf coding in cluster-based wireless sensor networks. IEEE Trans. Veh. Technol. 59(5), 2564–2574 (2010)
Zhou, B., Yang, S., Nguyen, T.H., Sun, T., Grattan, K.T.V.: Wireless sensor network platform for intrinsic optical fiber ph sensors. IEEE Sens. J. 14(4), 1313–1320 (2014)
Zuniga-Mejia, J., Villalpando-Hernandez, R., Vargas-Rosales, C., Spanias, A.: A linear systems perspective on intrusion detection for routing in reconfigurable wireless networks. IEEE Access 7, 60486–60500 (2019)
Acknowledgements
No acknowledge.
Funding
No funding is involved in this work.
Author information
Authors and Affiliations
Contributions
Conceptualization, Methodology, Software: SG Writing—Original draft preparation & Visualization, Investigation: Sravanthi Godala & M. Sunil Kumar
Corresponding author
Ethics declarations
Conflict of interest
Conflict of Interest is not applicable in this work.
Ethical approval and consent to participate
No participation of humans takes place in this implementation process.
Human and animal rights
No violation of Human and Animal Rights is involved.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Godala, S., Kumar, M.S. A weight optimized deep learning model for cluster based intrusion detection system. Opt Quant Electron 55, 1224 (2023). https://doi.org/10.1007/s11082-023-05509-x
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11082-023-05509-x