Abstract
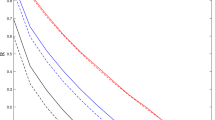
The decoy-state method was proposed as an effective way to resist photon-number splitting attack in quantum key distribution (QKD) system. However, due to the limitation of computing power, the final key rate of the QKD system is affected by statistical fluctuation. Until now, the key rate of active decoy-state method under statistical fluctuations has been rigorously analysed and improved by applying the improved Chernoff bound. In this paper, the improved Chernoff bound method is applied in the passive decoy-state method and an improved bound for estimating the final key rate is obtained. The simulation results show that the maximum secure transmission distance by our method can reach 205 km under standard optical fiber, which is very close to the asymptotic limit of 212 km. With a number of pulses up to 1013, our method can reach the highest final key rates among existing results, which can be considered as the best choice for QKD implementations with passive mudulation.



Similar content being viewed by others
References
Acín, A., Brunner, N., Gisin, N., Massar, S., Pironio, S., Scarani, V.: Device-independent security of quantum cryptography against collective attacks. Phys. Rev. Lett. 98(23), 230501 (2007). https://doi.org/10.1103/PhysRevLett.98.230501
Adachi, Y., Yamamoto, T., Koashi, M., Imoto, N.: Simple and efficient quantum key distribution with parametric down-conversion. Phys. Rev. Lett. 99(18), 180503 (2007). https://doi.org/10.1103/PhysRevLett.99.180503
Asadpour, S.H.: Goos-Hänchen shifts due to spin-orbit coupling in the carbon nanotube quantum dot nanostructures. Appl. Opt. 56(8), 2201–2208 (2017). https://doi.org/10.1364/AO.56.002201
Asadpour, S.H., Rahimpour Soleimani, H.: Phase and thickness control of optical bistability and multistability in a defect slab with a single layer of graphene. Laser Phys. Lett. 13(1), 015201 (2014a). https://doi.org/10.1088/1612-2011/13/1/015201
Asadpour, S.H., Rahimpour Soleimani, H.: Subluminal and superluminal pulse propagation via spin coherence in a defect dielectric medium. Opt. Commun. 315, 394–398 (2014b). https://doi.org/10.1016/j.optcom.2013.11.025
Bennett, C.H., Brassard, G.: Quantum cryptography: public key distribution and coin tossing. In: Proceedings of IEEE International Conference on Computers, Systems and Signal Processing, Institute of Electrical and Electronics Engineers, Bangalore, India, pp. 175–179 (1984). https://doi.org/10.1016/j.tcs.2014.05.025
Branciard, C., Cavalcanti, E.G., Walborn, S.P., Scarani, V., Wiseman, H.M.: One-sided device-independent quantum key distribution: security, feasibility, and the connection with steering. Phys. Rev. A 85(1), 010301 (2012). https://doi.org/10.1103/PhysRevA.85.010301
Gottesman, D., Lo, H.K., Lütkenhaus, N., Preskill, J.: Security of quantum key distribution with imperfect devices. Quantum Inf. Comput. 4(5),325–360 (2004). https://doi.org/10.1109/ISIT.2004.1365172
Hayashi, M., Tsurumaru, T.: Concise and tight security analysis of the Bennett-Brassard 1984 protocol with finite key lengths. New J. Phys. 14(9), 093014 (2012). https://doi.org/10.1088/1367-2630/14/9/093014
Hwang, W.–Y.: Quantum key distribution with high loss: toward global secure communication. Phys. Rev. Lett. 91(5), 057901 (2003). https://doi.org/10.1103/PhysRevLett.91.057901
Inoue, K., Honjo, T.: Robustness of differential-phase-shift quantum key distribution against photon-number-splitting attack. Phys. Rev. A 71(4), 042305 (2005). https://doi.org/10.1103/PhysRevA.71.042305
Lo, H.K., Curty, M., Qi, B.: Measurement-device-independent quantum key distribution. Phys. Rev. Lett. 108(13), 130503 (2012). https://doi.org/10.1103/PhysRevLett.108.130503
Ma, X., Qi, B., Zhao, Y., Lo, H.-K.: Practical decoy state for quantum key distribution. Phys. Rev. A 72(1), 012326 (2005). https://doi.org/10.1103/PhysRevA.72.012326
Mauerer, W., Silberhorn, C.: Quantum key distribution with passive decoy state selection. Phys. Rev. A 75(5), 050305 (2007). https://doi.org/10.1103/PhysRevA.75.050305
Pawłowski, M., Brunner, N.: Semi-device-independent security of one-way quantum key distribution. Phys. Rev. A 84(1), 010302 (2011). https://doi.org/10.1103/PhysRevA.84.010302
Song, T.-T., Wen, Q.-Y., Guo, F.-Z., Tan, X.-Q.: Finite-key analysis for measurement-device-independent quantum key distribution. Phys. Rev. A 86(2), 022332 (2012). https://doi.org/10.1103/PhysRevA.86.022332
Stucki, D., Brunner, N., Gisin, N., Scarani, V., Zbinden, H.: Fast and simple one-way quantum key distribution. Appl. Phys. Lett. 87(19), 194108 (2005). https://doi.org/10.1063/1.2126792
Tan, Y.G., Cai, Q.Y.: Practical decoy state quantum key distribution with finite resource. Eur. Phys. J. D 56(3), 449–455 (2010). https://doi.org/10.1140/epjd/e2009-00316-1
Tang, Y.–L., Yin, H.-L., Ma, X., Fung, C.-H.F., Liu, Y., Yong, H.-L., Chen, T.-Y., Peng, C.-Z., Chen, Z.-B., Pan, J.-W.: Source attack of decoy-state quantum key distribution using phase information. Phys. Rev. A 88(2), 022308 (2013). https://doi.org/10.1103/PhysRevA.88.022308
Zhang, Z., Zhao, Q., Razavi, M., Ma, X.: Improved key-rate bounds for practical decoy-state quantum-key-distribution systems. Phys. Rev. A 95(1), 012333 (2017). https://doi.org/10.1103/PhysRevA.95.012333
Zhou, C., Bao, W.-S., Li, H.-W., Wang, Y., Li, Y., Yin, Z.-Q., Chen, W., Han, Z.-F.: Tight finite-key analysis for passive decoy-state quantum key distribution under general attacks. Phys. Rev. A 89(5), 052328 (2014). https://doi.org/10.1103/PhysRevA.89.052328
Acknowledgements
Supported by the National Natural Science Foundation of China under Grant Nos 61505261, 61675235 and 61605248 and the National Basic Research Program of China under Grant No 2013CB338002.
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Liu, F., Zhou, C., Wang, Y. et al. Improved secure bounds for passive decoy state quantum key distribution system. Opt Quant Electron 52, 156 (2020). https://doi.org/10.1007/s11082-020-02270-3
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11082-020-02270-3