Abstract
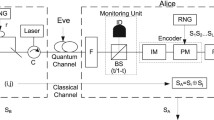
Measurement-device-independent quantum key distribution (MDI-QKD) has received much attention, with the goal of overcoming all of the security loopholes caused by an imperfect detection system. We here propose a plug-and-play MDI-QKD (P&P MDI-QKD) scheme whereby an untrusted relay node, Charlie, owns a laser and sends photons to Alice and Bob. Alice (Bob) modulates the polarization of the incident photons and returns them to Charlie. Charlie uses a modified Bell state analyzer (BSA) to perform Bell state measurements (BSM). In comparison with the original version of MDI-QKD, our scheme exploits a single untrusted laser as the photon source. This makes the signal photons identical and enhances the Hong-Ou-Mandel effect. Second, because of the P&P structure, the setup can automatically eliminate the birefringence influence of the fibers, which makes the setup highly stable. Finally, our modified BSA can identify \({{\left| \varPhi \right\rangle }^{+}}\) and \({{\left| \varPhi \right\rangle }^{-}}\) of four Bell states with polarization encoding but not \({{\left| \varPsi \right\rangle }^{+}}\) and \({{\left| \varPsi \right\rangle }^{-}}\). Based on practical experimental parameters, a simulation showed that the maximum theoretical secure transmission distance could reach more 280 km.



Similar content being viewed by others
References
Acín, A., Brunner, N., Gisin, N., Massar, S., Pironio, S., Scarani, V.: Device-independent security of quantum cryptography against collective attacks. Phys. Rev. Lett. 98(23), 230501 (2007). https://doi.org/10.1103/PhysRevLett.98.230501, 0702152
Bennett, C.H.: Quantum cryptography using any two nonorthogonal states. Phys. Rev. Lett. 68(21), 3121–3124 (1992). https://doi.org/10.1103/PhysRevLett.68.3121. arXiv:1011.1669v3
Bennett, C.H., Brassard, G.: Quantum cryprography: public key distribution and coin tossing. In: Proceedings of IEEE International Conference on Computers, Systems and Signal Processing, Institute of Electrical and Electronics Engineers, Bangalore, India, pp. 175–179 (1984)
Brassard, G., Lütkenhaus, N., Mor, T., Sanders, B.C.: Limitations on practical quantum cryptography. Phys. Rev. Lett. 85(6), 1330–1333 (2000). https://doi.org/10.1103/PhysRevLett.85.1330, 9911054
Chen, D., Zhao, S.H., Shi, L., Liu, Y.: Measurement-device-independent quantum key distribution with pairs of vector vortex beams. Phys. Rev. A 93(3), 032320 (2016). https://doi.org/10.1103/PhysRevA.93.032320
Cheng, G., Guo, B., Zhang, C., Guo, J., Fan, R.: Wavelength division multiplexing quantum key distribution network using a modified plug-and-play system. Opt. Quantum Electron. 47(7), 1809–1817 (2015). https://doi.org/10.1007/s11082-014-0039-4
Feihu, X., Curty, M., Qi, B., Lo, H.-K.: Measurement-device-independent quantum cryptography. IEEE J. Sel. Top. Quantum Electron. 21(3), 148–158 (2015). https://doi.org/10.1109/JSTQE.2014.2381460. URL http://ieeexplore.ieee.org/document/6985598/, 1409.5157
Fu, Y., Yin, H.L., Chen, T.Y., Chen, Z.B.: Long-distance measurement-device-independent multiparty quantum communication. Phys. Rev. Lett. 114(9), 090501 (2015). https://doi.org/10.1103/PhysRevLett.114.090501, 1412.0832
Gisin, N., Fasel, S., Kraus, B., Zbinden, H., Ribordy, G.: Trojan-horse attacks on quantum-key-distribution systems. Phys. Rev. A 73(2), 022320 (2006). https://doi.org/10.1103/PhysRevA.73.022320, 0507063
Gobby, C., Yuan, Z.L., Shields, A.J.: Quantum key distribution over 122 km of standard telecom fiber. Appl. Phys. Lett. 84(19), 3762–3764 (2004). https://doi.org/10.1063/1.1738173, 0412171
Gottesman, D., Lo, H.K., Lutkenhaus, N., Preskill, J.: Security of quantum key distribution with imperfect devices. Quantum Inf. Comput. 4(5), 325–360 (2004)
Hong, C.K., Ou, Z.Y., Mandel, L.: Measurement of subpicosecond time intervals between two photons by interference. Phys. Rev. Lett. 59(18), 2044–2046 (1987). https://doi.org/10.1103/PhysRevLett.59.2044
Inamori, H.: Security of practical time-reversed EPR quantum key distribution. Algorithmica 34(4), 340–365 (2002). https://doi.org/10.1007/s00453-002-0983-4
Inoue, K., Waks, E., Yamamoto, Y.: Differential phase shift quantum key distribution. Phys. Rev. Lett. 89(3), 037902 (2002). https://doi.org/10.1103/PhysRevLett.89.037902
Liu, Y., Chen, T.Y., Wang, L.J., Liang, H., Shentu, G.L., Wang, J., Cui, K., Yin, H.L., Liu, N.L., Li, L., Ma, X., Pelc, J.S., Fejer, M.M., Peng, C.Z., Zhang, Q., Pan, J.W.: Experimental measurement-device-independent quantum key distribution. Phys. Rev. Lett. 111(13), 130502 (2013). https://doi.org/10.1103/PhysRevLett.111.130502, 1209.6178
Lo, H.K., Ma, X., Chen, K.: Decoy state quantum key distribution. Phys. Rev. Lett. 94(23), 230504 (2005). https://doi.org/10.1103/PhysRevLett.94.230504, 0411004
Lo, H.K., Curty, M., Qi, B.: Measurement-device-independent quantum key distribution. Phys. Rev. Lett. 108(13), 130503 (2012). https://doi.org/10.1103/PhysRevLett.108.130503. arXiv:1109.1473v1
Lucamarini, M., Yuan, Z.L., Dynes, J.F., Shields, A.J.: Overcoming the rate-distance limit of quantum key distribution without quantum repeaters. Nature 557(7705), 400–403 (2018). https://doi.org/10.1038/s41586-018-0066-6
Lütkenhaus, N.: Security against individual attacks for realistic quantum key distribution. Phys. Rev. A 61(5), 052304 (2000). https://doi.org/10.1103/PhysRevA.61.052304, 9910093
Lydersen, L., Wiechers, C., Wittmann, C., Elser, D., Skaar, J., Makarov, V.: Hacking commercial quantum cryptography systems by tailored bright illumination. Nat. Photonics 4(10), 686–689 (2010). https://doi.org/10.1038/nphoton.2010.214, 1008.4593
Ma, X., Fung, C.H.F., Razavi, M.: Statistical fluctuation analysis for measurement-device-independent quantum key distribution. Phys. Rev. A 86(5), 052305 (2012). https://doi.org/10.1103/PhysRevA.86.052305. arXiv:1210.3929v1
Marsili, F., Verma, V.B., Stern, J.A., Harrington, S., Lita, A.E., Gerrits, T., Vayshenker, I., Baek, B., Shaw, M.D., Mirin, R.P., Nam, S.W.: Detecting single infrared photons with 93% system efficiency. Nat. Photonics 7(3), 210–214 (2013). https://doi.org/10.1038/nphoton.2013.13, 1209.5774
Muller, A., Herzog, T., Huttner, B., Tittel, W., Zbinden, H., Gisin, N.: “Plug and play” systems for quantum cryptography. Appl. Phys. Lett. 70(7), 793–795 (1997). https://doi.org/10.1063/1.118224, 9611042
Qi, B., Fung, C.H.F., Lo, H.K., Ma, X.: Time-shift attack in practical quantum cryptosystems. Quantum Inf. Comput. 7(1), 073–082 (2007). arXiv:quant-ph/0512080, 0512080
Rubenok, A., Slater, J.A., Chan, P., Lucio-Martinez, I., Tittel, W.: Real-world two-photon interference and proof-of-principle quantum key distribution immune to detector attacks. Phys. Rev. Lett. 111(13), 130501 (2013). https://doi.org/10.1103/PhysRevLett.111.130501. arXiv:1204.0738v4
Scarani, V., Acín, A., Ribordy, G., Gisin, N.: Quantum cryptography protocols robust against photon number splitting attacks for weak laser pulse implementations. Phys. Rev. Lett. 92(5), 057901 (2004). https://doi.org/10.1103/PhysRevLett.92.057901, 0211131
Stucki, D., Gisin, N., Guinnard, O., Ribordy, G., Zbinden, H.: Quantum key distribution over 67 km with a plug&play system. New J. Phys. 4, 41 (2002). https://doi.org/10.1088/1367-2630/4/1/341. arXiv:quant-ph/0203118, 0203118
Sun, S.H., Gao, M., Li, C.Y., Liang, L.M.: Practical decoy-state measurement-device-independent quantum key distribution. Phys. Rev. A 87(5), 052329 (2013). https://doi.org/10.1103/PhysRevA.87.052329. 1305.7396
Tang, G.Z., Sun, S.H., Xu, F., Chen, H., Li, C.Y., Liang, L.M.: Experimental asymmetric plug-and-play measurement-device-independent quantum key distribution. Phys. Rev. A 94(3), 032326 (2016). https://doi.org/10.1103/PhysRevA.94.032326. 1609.02648
Tang, Y.L., Yin, H.L., Chen, S.J., Liu, Y., Zhang, W.J., Jiang, X., Zhang, L., Wang, J., You, L.X., Guan, J.Y., Yang, D.X., Wang, Z., Liang, H., Zhang, Z., Zhou, N., Ma, X., Chen, T.Y., Zhang, Q., Pan, J.W.: Measurement-device-independent quantum key distribution over 200 km. Phys. Rev. Lett. 113(19), 190501 (2014a). https://doi.org/10.1103/PhysRevLett.113.190501. 1407.8012
Tang, Z., Liao, Z., Xu, F., Qi, B., Qian, L., Lo, H.K.: Experimental demonstration of polarization encoding measurement-device-independent quantum key distribution. Phys. Rev. Lett. 112(19), 190503 (2014b). https://doi.org/10.1103/PhysRevLett.112.190503. 1306.6134
Wai, P., Menyak, C.: Polarization mode dispersion, decorrelation, and diffusion in optical fibers with randomly varying birefringence. J. Lightwave Technol. 14(2), 148–157 (1996). https://doi.org/10.1109/50.482256
Wu, C.F., Du, Y.N., Wang, J.D., Wei, Z.J., Qin, X.J., Zhao, F., Zhang, Z.M.: Analysis on performance optimization in measurement-device-independent quantum key distribution using weak coherent states. Acta Physica Sinica 65(10), 100302 (2016a). https://doi.org/10.7498/aps.65.100302
Wu, Y., Zhou, J., Gong, X., Guo, Y., Zhang, Z.M., He, G.: Continuous-variable measurement-device-independent multipartite quantum communication. Phys. Rev. A 93(2), 022325 (2016b). https://doi.org/10.1103/PhysRevA.93.022325. 1512.03876
Xu, F., Qi, B., Lo, H.K.: Experimental demonstration of phase-remapping attack in a practical quantum key distribution system. New J. Phys. 12(11), 113026 (2010). https://doi.org/10.1088/1367-2630/12/11/113026. 1005.2376
Zhang, C.X., Guo, B.H., Cheng, G.M., Guo, J.J., Fan, R.H.: Spin-orbit hybrid entanglement quantum key distribution scheme. Sci. China Phys. Mech. Astron. 57(11), 2043–2048 (2014). https://doi.org/10.1007/s11433-014-5557-3
Zhao, Y., Fung, C.H.F., Qi, B., Chen, C., Lo, H.K.: Quantum hacking: experimental demonstration of time-shift attack against practical quantum-key-distribution systems. Phys. Rev. A 78(4), 042333 (2008). https://doi.org/10.1103/PhysRevA.78.042333. 0704.3253
Zhu, C., Xu, F., Pei, C.: W-state analyzer and multi-party measurement-device-independent quantum key distribution. Sci. Rep. 5(1), 17449 (2015). https://doi.org/10.1038/srep17449
Acknowledgements
This work is financially supported by the National Natural Science Foundation of China (Grant No. 61572203); the Open Research Fund (Grant No. KQI201508) of the Key Lab of Quantum Information, Chinese Academy of Sciences; the Open Research Fund (Grant No. SKLST201602) of the State Key Laboratory of Transient Optics and Photonics, Chinese Academy of Sciences; and Guangdong Innovative Research Team Program (Grant No. 201001D0104799318).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Hu, M., Zhang, L., Guo, B. et al. Polarization-based plug-and-play measurement-device-independent quantum key distribution. Opt Quant Electron 51, 22 (2019). https://doi.org/10.1007/s11082-018-1736-1
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11082-018-1736-1