Abstract
In many sensitive Internet-of-Things (IoT) based applications, sensor devices send information in the form of images. Chaos theory is the study of deterministic laws that exhibit characteristics like unpredictability, randomness and irregularity. These characteristics can be used to encrypt images thus providing an extra layer of security over the existing security infrastructure of the IoT application. In this work, we present a symmetric image encryption algorithm called, IETD which is suitable for IoT applications. Here, we propose a new chaotic map named “TD Map” using Tinkerbell Map and Duffing Map. We also propose an advanced zigzag algorithm that can encrypt color images of any resolution. The “TD Map” is used to generate a 2-D chaotic sequence which is utilized by simple operations like scrambling and swapping to encrypt the image. The proposed scheme has undergone many statistical tests and analyses to evaluate its performance against cryptanalysis attacks, noise, data loss, correlation immunity and so on which show that it achieves better values in each of the standard metrics under consideration than the existing ciphers. MSE, PSNR, information entropy, NPCR and UACI values show that the proposed scheme is at par with the existing schemes. Moreover, it has exhibited good energy efficiency and is easy to implement in hardware. These altogether make IETD a suitable lightweight cipher to deploy in real-time IoT applications.



































Similar content being viewed by others
Code Availability
The source code is publicly available at https://github.com/Tejas-Dhopavkar/IETD
References
Agarwal N, Singh AK, Singh PK (2019) Survey of robust and imperceptible watermarking. Multimed Tools Appl 78(7):8603–8633
Alassaf N, Gutub A, Parah SA, Al Ghamdi M (2019) Enhancing speed of SIMON: a light-weight-cryptographic algorithm for IoT applications. Multimed Tools Appl 78(23):32633–32657
Arnol’d VI, Avez A (1968) Ergodic problems of classical mechanics
Babaei A, Motameni H, Enayatifar R (2020) A new permutation-diffusion-based image encryption technique using cellular automata and dna sequence. Optik 203:164000
Broumandnia A (2019) The 3d modular chaotic map to digital color image encryption. Futur Gener Comput Syst 99:489–499
Choi US, Cho SJ, Kim JG, Kang SW, Kim HD Color image encryption based on programmable complemented maximum length cellular automata and generalized 3-d chaotic cat map. Multimed Tool Appl:1–18
Dai JY, Ma Y, Zhou NR (2021) Quantum multi-image compression-encryption scheme based on quantum discrete cosine transform and 4D hyper-chaotic Henon map. Quantum Inf Process 20(7):1–24
Derhamy H, Eliasson J, Delsing J (2017) Iot interoperability—on-demand and low latency transparent multiprotocol translator. IEEE Internet Thing J 4(5):1754–1763
Diffie W, Hellman M (1976) New directions in cryptography. IEEE Trans Inform Theory 22(6):644–654
Dong C (2014) Color image encryption using one-time keys and coupled chaotic systems. Signal Process Image Commun 29(5):628–640
Enayatifar R, Guimarães F. G., Siarry P (2019) Index-based permutation-diffusion in multiple-image encryption using dna sequence. Opt Lasers Eng 115:131–140
Gao T, Chen Z (2008) A new image encryption algorithm based on hyper-chaos. Phys Lett A 372(4):394–400
Gong L, Wu R, Zhou N (2020) A New 4D Chaotic system with coexisting hidden chaotic attractors. Int J Bifurcation Chaos 30(10):2050142
Griffin J (2013) The sine map
Heuer J, Hund J, Pfaff O (2015) Toward the web of things: applying web technologies to the physical world. Computer 48(5):34–42
Hu X, Wei L, Chen W, Chen Q, Guo Y (2020) Color image encryption algorithm based on dynamic chaos and matrix convolution. IEEE Access 8:12452–12466
Huang C, Nien HH (2009) Multi chaotic systems based pixel shuffle for image encryption. Opt Commun 282(11):2123–2127
Khan MA, Salah K (2018) Iot security: review, blockchain solutions, and open challenges. Futur Gener Comput Syst 82:395–411
Kimbahune VV, Deshpande AV, Mahalle PN (2017) Lightweight key management for adaptive addressing in next generation internet. International Journal of Ambient Computing and Intelligence (IJACI) 8 (1):50–69
Li C, Luo G, Qin K, Li C (2017) An image encryption scheme based on chaotic tent map. Nonlinear Dyn 87(1):127–133
May RM (1976) Simple mathematical models with very complicated dynamics. Nature 261(5560):459–467
Mhetre NA, Deshpande AV, Mahalle PN (2016) Trust management model based on fuzzy approach for ubiquitous computing. International Journal of Ambient Computing and Intelligence (IJACI) 7(2):33–46
Mishra M, Singh P, Garg C (2014) A new algorithm of encryption and decryption of images using chaotic mapping. International Journal of Information & Computation Technology. ISSN:0974–2239
Muñoz-Guillermo M. (2021) Image encryption using q-deformed logistic map. Inf Sci 552:352–364
Nadeem A, Javed MY (2005) A performance comparison of data encryption algorithms. In: 2005 International conference on information and communication technologies, pp 84–89. IEEE
Nayak P, Nayak SK, Das S (2018) A secure and efficient color image encryption scheme based on two chaotic systems and advanced encryption standard. In: 2018 International conference on advances in computing, communications and informatics (ICACCI), pp 412–418. IEEE
Nayak SK, Tripathy S (2018) Sepdp: secure and efficient privacy preserving provable data possession in cloud storage. IEEE Trans Serv Comput
Neshenko N, Bou-Harb E, Crichigno J, Kaddoum G, Ghani N (2019) Demystifying iot security: an exhaustive survey on iot vulnerabilities and a first empirical look on internet-scale iot exploitations. IEEE Commun Surveys Tutorial 21(3):2702–2733
Noura M, Atiquzzaman M, Gaedke M (2019) Interoperability in internet of things: taxonomies and open challenges. Mobile Netw Appl 24(3):796–809
Omoniwa B, Hussain R, Javed MA, Bouk SH, Malik SA (2018) Fog/edge computing-based iot (feciot): architecture, applications, and research issues. IEEE Int Thing J 6(3):4118–4149
Parashar D, Roy S, Dey N, Jain V, Rawat U (2018) Symmetric key encryption technique: a cellular automata based approach. In: Cyber security, pp 59–67. Springer
Prasithsangaree P, Krishnamurthy P (2003) Analysis of energy consumption of rc4 and aes algorithms in wireless lans. In: GLOBECOM’03. IEEE Global telecommunications conference (IEEE cat. no. 03CH37489), vol 3, pp 1445–1449. IEEE
Rivest RL, Shamir A, Adleman L (1978) A method for obtaining digital signatures and public-key cryptosystems. Commun ACM 21(2):120–126
Roy S, Karjee J, Rawat U, Dey N, et al. (2016) Symmetric key encryption technique: a cellular automata based approach in wireless sensor networks. Procedia Comput Sci 78:408–414
Roy S, Rawat U, Karjee J (2019) A lightweight cellular automata based encryption technique for iot applications. IEEE Access 7:39782–39793
Roy S, Rawat U, Sareen HA, Nayak SK (2020) Ieca: an efficient iot friendly image encryption technique using programmable cellular automata. J Ambient Intell Human Comput:1–20
Roy S, Shrivastava M, Pandey CV, Nayak SK, Rawat U (2020) IEVCA: an efficient image encryption technique for IoT applications using 2-D Von-Neumann cellular automata. Multimed Tools Appl:1–39
Sanchez-Avila C, Sanchez-Reillol R (2001) The rijndael block cipher (aes proposal): a comparison with des. In: Proceedings IEEE 35th Annual 2001 international carnahan conference on security technology (Cat. No. 01CH37186), pp 229–234. IEEE
Som S, Kotal A, Mitra A, Palit S, Chaudhuri B (2014) A chaos based partial image encryption scheme. In: 2014 2Nd international conference on business and information management (ICBIM), pp 58–63. IEEE
Stoyanov B, Kordov K (2014) Novel image encryption scheme based on chebyshev polynomial and duffing map. Sci World J:2014
Tong XJ, Wang Z, Zhang M, Liu Y (2013) A new algorithm of the combination of image compression and encryption technology based on cross chaotic map. Nonlinear Dyn 72(1-2):229–241
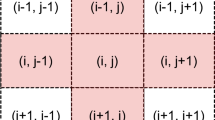
Wang X, Guan N (2020) A novel chaotic image encryption algorithm based on extended zigzag confusion and rna operation. Opt Laser Technol 106366:131
Wong KW, Kwok BSH, Law WS (2008) A fast image encryption scheme based on chaotic standard map. Phys Lett A 372(15):2645–2652
Wu Y, Noonan JP, Agaian S, et al. (2011) Npcr and uaci randomness tests for image encryption. Cyber journals: multidisciplinary journals in science and technology. Journal of Selected Areas in Telecommunications (JSAT) 1(2):31–38
Xian Y, Wang X (2021) Fractal sorting matrix and its application on chaotic image encryption. Inf Sci 547:1154–1169
Yan L, Fu J, Wang C, Ye Z, Chen H, Ling H (2021) Enhanced network optimized generative adversarial network for image enhancement. Multimed Tools Appl 80(9):14363–14381
Yang Y, Wu L, Yin G, Li L, Zhao H (2017) A survey on security and privacy issues in internet-of-things. IEEE Int Thing J 4(5):1250–1258
Yuan S, Jiang T, Jing Z (2011) Bifurcation and chaos in the tinkerbell map. Int J Bifurcation Chaos 21(11):3137–3156
Zarebnia M, Pakmanesh H, Parvaz R (2019) A fast multiple-image encryption algorithm based on hybrid chaotic systems for gray scale images. Optik 179:761–773
Zear A, Singh PK (2021) Secure and robust color image dual watermarking based on LWT-DCT-SVD. Multimed Tools Appl:1–18
Zhang X, Parhi KK (2004) High-speed vlsi architectures for the aes algorithm. IEEE Transactions on Very Large Scale Integration (VLSI) Systems 12 (9):957–967
Zhang YQ, He Y, Li P, Wang XY (2020) A new color image encryption scheme based on 2dnlcml system and genetic operations. Opt Lasers Eng 106040:128
Zhou J, Cao Z, Dong X, Vasilakos AV (2017) Security and privacy for cloud-based iot: Challenges. IEEE Commun Mag 55(1):26–33
Zhou NR, Hua TX, Gong LH, Pei DJ, Liao QH (2015) Quantum image encryption based on generalized Arnold transform and double random-phase encoding. Quantum Inf Process 14(4):1193–1213
Zhou NR, Huang LX, Gong LH, Zeng QW (2020) Novel quantum image compression and encryption algorithm based on DQWT and 3D hyper-chaotic Henon map. Quantum Inf Process 19(9):1–21
Zhu C (2012) A novel image encryption scheme based on improved hyperchaotic sequences. Opt Commun 285(1):29–37
Funding
This work is supported by Research Funding programme of Data Security Council of India (DSCI).
Author information
Authors and Affiliations
Contributions
Tejas Atul Dhopavkar and Sanjeet Kumar Nayak found the problem and designed the IETD. Tejas Atul Dhopavkar implemented the proposed scheme. Tejas Atul Dhopavkar, Sanjeet Kumar Nayak, and Satyabrata Roy conducted the experiments to evaluate the performance of the IETD and wrote the paper.
Corresponding author
Ethics declarations
Conflict of Interests
The authors declare that they have no conflict of interest.
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Dhopavkar, T.A., Nayak, S.K. & Roy, S. IETD: a novel image encryption technique using Tinkerbell map and Duffing map for IoT applications. Multimed Tools Appl 81, 43189–43228 (2022). https://doi.org/10.1007/s11042-022-13162-x
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-022-13162-x