Abstract
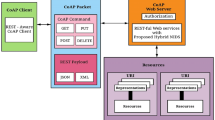
The rapidly increasing volume of lightweight devices in Internet of Things (IoT) environment needs a strong Intrusion Detection System (IDS). Conventional IDS cannot be applied directly in IoT networks due to various communication architectures, standards, technologies, and environment specific services. The main problem with current IDS and handling techniques is that they can’t adapt to service changes in real-time. To overcome this open challenge, adaptive hybrid IDS based on timed automata controller approach is proposed in this paper. Proposed Hybrid IDS have additional knowledge in relation to frequent multimedia file formats and use this knowledge to carry out a comprehensive analysis of packets carrying multimedia files. Crowd sourcing online repository for signature based malicious pattern set generation is designed and self-tuning timed automaton is developed to detect the intruder in IoT networks. From the experimental results, it is evident that our proposed method, an adaptive hybrid IDS suit smart city applications and are accurate (99.06%) in detecting Denial of Service (DoS) attacks, control hijacking attacks, zero day attacks, and replay attacks in IoT environments.











Similar content being viewed by others
References
Alghuried A (2017) A model for anomalies detection in internet of things (IoT) using inverse weight clustering and decision tree. Dublin Institute of Technology. https://doi.org/10.21427/d7wk7s
Alur R, Dill DL (1994) Fundamental study a theory of timed automata. Theor Comput Sci 126(2):183–235
Amaral J, Oliveira L, Rodrigues J, Han G, Shu L (2014) Policy and network based intrusion detection system for IPv6-enabled wireless sensor networks. In: 2014 IEEE International Conference on Communications (ICC), pp 1796–1801
Bao F, Chen I-R, Chang M, Cho J-H (2012) Hierarchical Trust Management for Wireless Sensor Networks and its applications to trust-based routing and intrusion detection. IEEE Trans Netw Serv Manag 9(2):169–183
Bastille Security for the Internet of Radios. Retrieved Jun 2017 from Bastille Networks: https://www.bastille.net/research/mission/. Accessed 5 June 2017
Bosman H, Iacca G, Tejada A, Wörtche HJ, Liotta A (2017) Spatial anomaly detection in sensor networks using neighborhood information. Information Fusion 33:41–56
Constrained Application Protocol (CoAP) (2017). https://tools.ietf.org/id/draft-ietf-core-coap-03.html. Accessed 5 June 2017
DDoS attack that disrupted internet was largest of its kind in history, experts say, 2016. https://www.theguardian.com/technology/2016/oct/26/ddos-attack-dyn-mirai-botne. Accessed 8 Dec 2016
Fu Y, Yan Z, Cao J, Kone O, Cao X (2017) An automata based intrusion detection method for internet of things. Mob Inf Syst 2017(1750637):13. https://doi.org/10.1155/2017/1750637
Haddad Pajouh H, Javadian R, Khayami R, Dehghantanha A, Choo R (2016) A two-layer dimension reduction and two-tier classification model for anomaly-based intrusion detection in IoT backbone networks, IEEE Transactions on Emerging Topics in Computing, (in Press)
Heady R, Luger G, Maccabe A, Servilla M (1990) The architecture of network level intrusion detection system. In: Technical report, Department of Computer Science, University of new Mexico
Hodo E, Bellekens X, Hamilton A, Dubouilh PL (2016) Threat analysis of IoT networks using artificial neural network intrusion detection system. In: International Symposium on Networks, Computers and Communications (ISNCC) pp 1–6
http://economictimes.indiatimes.com/industry/banking/finance/banking/3-2-million-debit-cards-compromised-sbi-hdfc-bank-icici-yes-bank-and-axis-worst-hit/articleshow /54945561.cms. Accessed 26 Dec 2017
http://www.securityweek.com/fbi-reminds-cars-are-increasingly-vulnerable-remote-exploits. March 2016
Jun C, Chi C (2014) Design of complex event processing IDS in internet of things. In: Sixth International Conference on Measuring Technology and Mechatronics Automation, pp 226–229
Kasinathan P, Pastrone C, Spirito MA, Vinkovits M (2013) Denial-of-Service detection in 6LoWPAN based Internet of Things. In: IEEE 9th International Conference on Wireless and Mobile Computing, Networking and Communications (WiMob), pp 600–607
Krimmling J, Peter S (2014) Integration and evaluation of intrusion detection for CoAP in smart city applications. In: IEEE Conference on Communications and Network Security (CNS'14), pp 73–78
Misra S, Abraham KI, Obaidat MS, Krishna PV (2009) LAID: a learning automata-based scheme for intrusion detection in wireless sensor networks. Security Comm Networks 2:105–115. https://doi.org/10.1002/sec.74
Mutz D, Valeur F, Vigna G, Kruegel C (2006) Anomalous system call detection. ACM Trans Inf Syst Secur 9(1):61–93
Onat I, Miri A (2005) An intrusion detection system for wireless sensor networks. In: Proceeding of the IEEE International Conference on Wireless and Mobile Com- puting, Networking and Communications, Montreal, Canada, August 2005, vol 3, pp 253–259
Osborne C 2014 How hackers stole millions of credit card records from target, http://www.zdnet.com/article/how-hackers-stole-millions-of-credit-card-records-from-target/. Accessed 23 Mar 2018
Provost F, Fawcett T (2001) Robust classification for imprecise environments, machine learning, vol 42/3, pp 203-231
Raza S, Wallgren L, Voigt T (2013) SVELTE: real-time intrusion detection in the internet of things. Ad Hoc Netw 11(8):2661–2674
Roesch M (1999) Snort – lightweight intrusion detection for networks. In: Proceedings of the 13th USENIX Conference on System Administration Seattle, Washington, pp 229–238
Sforzin A, Marmol FG, Conti M, Bohli JM (2016) RPiDS: Raspberry Pi IDS - A Fruitful Intrusion Detection System for IoT, Intl IEEE Conferences on Ubiquitous Intelligence & Computing, Advanced and Trusted Computing, Scalable Computing and Communications, Cloud and Big Data Computing, Internet of People, and Smart World Congres, pp 440–448
Shatnawi M, Hefeeda M (2018) Dynamic Input Anomaly Detection in Interactive Multimedia Services. In: 9th ACM International Conference on Multimedia System, Amsterdam, Netherlands, June 12–15
Sicari S, Rizzardi A, Grieco LA, Coen-Porisini A (2015) Security, privacy and trust in internet of things: the road ahead. Comput Netw 76:146–164
Summerville DH, Zach KM, Chen Y (2015) Ultra-lightweight deep packet anomaly detection for Internet of Things devices. In: IEEE 34th International Performance Computing and Communications Conference (IPCCC), IEEE, pp 1–8
Sun B, Wu K, Xiao Y, Wang R (2007) Integration of mobility and intrusion detection for wireless ad hoc networks. Wiley’s International Journal of Communication Systems 20(6):695–721
Vasilomanolakis E, Karuppayah S, Fischer M (2015) 55 taxonomy and survey of collaborative intrusion detection. ACM Comput Surv 47(4):1–33
Venkatraman S, Arun Raj Kumar P (2018) Improving Adhoc wireless sensor networks security using distributed automaton. Clust Comput. https://doi.org/10.1007/s10586-018-2352-3
Vijayan J (2014) Target attack shows danger of remotely accessible HVAC systems. http://www.computerworld.com/article/2487452/cybercrime-hacking/target-attack-shows-danger-of-remotely-accessible-hvac-systems.html. Accessed 23 Mar 2018
Wang G, Barbara S, Wang T, Barbara S, Zheng H, Zhao BY (2014) Man vs. Machine : Practical Adversarial Detection of Malicious Crowdsourcing Workers. In: Proceedings of the 23rd USENIX Security Symposium, pp 239-254
Xiao Y, Shen XS, Du DZ (2007) Wireless Network Security, Springer Science + Business Media, LLC,USA. E-ISBN-10 0-387-33112-3
Zhou CV, Leckie C, Karunasekera S (2009) Decentralized multi-dimensional alert correlation for collaborative intrusion detection. J Netw Comput Appl 32(5):1106–1123
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of interest
The Authors and Co-Authors have no conflict of interest. The paper is not submitted to any other journals.
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Venkatraman, S., Surendiran, B. Adaptive hybrid intrusion detection system for crowd sourced multimedia internet of things systems. Multimed Tools Appl 79, 3993–4010 (2020). https://doi.org/10.1007/s11042-019-7495-6
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-019-7495-6