Abstract
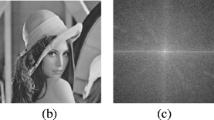
Photographs play a very crucial role in our lives, be it in the field of forensic investigation, military intelligence, scientific research, and publications. Nowadays, most of these photographs are in the digital format; which can be easily edited in any photo editing software without requiring any special knowledge of the field. It has become quite hard to identify whether an image is real or fake. This can be very crucial in the cases of forensic investigation or authorization of images. So, we need a solution, which not only identifies the attacks from different schemes like collage attack, crop attack, etc. but also recovers the edited or tampered portion. In proposed work, 4 reduced-size copy of the original image is hidden in the original image’s 4-LSB using four pseudo-random codes. Later on, these copies are used for tamper detection. As image gets tampered, recovery images (which are stored in the 4-LSB’s of the original image) also get tampered. So, before recovering the edited portion using the median image (or one out of the four recovery images) various filters like median filters, sharpening filters, and noise removal filters are used to enhance the quality. The proposed scheme recovers the host better than the many recently proposed schemes.















Similar content being viewed by others
References
Cao F, An B, Wang J, Ye D, Wang H (2017) Hierarchical recovery for tampered images based on watermark self-embedding. Displays 46:52–60
Celik MU, Sharma G, Saber E, Tekalp AM (2002) Hierarchical watermarking for secure image authentication with localization. IEEE Trans Image Process 11(6):585–595
Chang YF, Tai WL (2013) A block-based watermarking scheme for image tamper detection and self-recovery. Opto-Electron Rev 21(2):182–190
Chang CC, Fan YH, Tai WL (2008) Four-scanning attack on hierarchical digital watermarking method for image tamper detection and recovery. Pattern Recogn 41(2):654–661
Fridrich J (2002) Security of fragile authentication watermarks with localization. In Security and Watermarking of Multimedia Contents IV (Vol. 4675, pp 691–701). International Society for Optics and Photonics
He HJ, Zhang JS, Chen F (2009) Adjacent-block based statistical detection method for self-embedding watermarking techniques. Signal Process 89(8):1557–1566
He H, Chen F, Tai HM, Kalker T, Zhang J (2012) Performance analysis of a blockneighborhood-based self-recovery fragile watermarking scheme. IEEE Trans Inf Forensics Secur 7(1):185–196
Hore A, Ziou D (2010) Image quality metrics: PSNR vs. SSIM. In 2010 20th International Conference on Pattern Recognition (pp 2366–2369). IEEE
Islam M, Roy A, Laskar RH SVM-based robust image watermarking technique in LWT domain using different sub-bands. Neural Comput Applic 1–25
Izquierdo E, Guerra V (2003) An ill-posed operator for secure image authentication. IEEE Trans Circuits Syst Video Technol 13(8):842–852
Korus P, Dziech A (2014) Adaptive self-embedding scheme with controlled reconstruction performance. IEEE Trans Inf Forensics Secur 9(2):169–181
Kundur D, Hatzinakos D (1999) Digital watermarking for telltale tamper proofing and authentication. Proc IEEE 87(7):1167–1180
Lee TY, Lin SD (2008) Dual watermark for image tamper detection and recovery. Pattern Recogn 41(11):3497–3506
Li J, Li X, Yang B, Sun X (2015) Segmentation-based image copy-move forgery detection scheme. IEEE Trans Inf Forensics Secur 10(3):507–518
Lin PL, Hsieh CK, Huang PW (2005) A hierarchical digital watermarking method for image tamper detection and recovery. Pattern Recogn 38(12):2519–2529
Qi X, Xin X (2015) A singular-value-based semi-fragile watermarking scheme for image content authentication with tamper localization. J Vis Commun Image Represent 30:312–327
Qian Z, Feng G, Zhang X, Wang S (2011) Image self-embedding with high-quality restoration capability. Digital Signal Process 21(2):278–286
Sarreshtedari S, Akhaee MA (2015) A source-channel coding approach to digital image protection and self-recovery. IEEE Trans Image Process 24(7):2266–2277
Shehab A, Elhoseny M, Muhammad K, Sangaiah AK, Yang P, Huang H, Hou G (2018) Secure and robust fragile watermarking scheme for medical images. IEEE Access 6:10269–10278
Singh D, Singh SK (2016) Effective self-embedding watermarking scheme for image tampered detection and localization with recovery capability. J Vis Commun Image Represent 38:775–789
Verma VS, Jha RK, Ojha A (2015) Digital watermark extraction using support vector machine with principal component analysis based feature reduction. J Vis Commun Image Represent 31:75–85
Wong PW, Memon N (2001) Secret and public key image watermarking schemes for image authentication and ownership verification. IEEE Trans Image Process 10(10):1593–1601
Yang CW, Shen JJ (2010) Recover the tampered image based on VQ indexing. Signal Process 90(1):331–343
Yeung MM, Mintzer F (1997) An invisible watermarking technique for image verification. In Image Processing, 1997. Proceedings, International Conference on (Vol. 2, pp 680–683). IEEE
Zhang Z, Sun H, Gao S, Jin S (2018) Self-recovery reversible image watermarking algorithm. PLoS One 13(6):e0199143
Acknowledgements
This work was supported by Faculty Initiation Grant of PDPM Indian Institute of Information Technology Design and Manufacturing Jabalpur, India.
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Rajput, V., Ansari, I.A. Image tamper detection and self-recovery using multiple median watermarking. Multimed Tools Appl 79, 35519–35535 (2020). https://doi.org/10.1007/s11042-019-07971-w
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-019-07971-w