Abstract
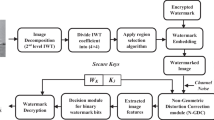
This paper proposes a novel human vision system based, spread spectrum method to scalable image watermarking. A scalable decomposition of the watermark is spread into the entire frequency sub-bands of the wavelet decomposed image. At each wavelet sub-band, the watermark data are inserted into the selected coefficients of the sub-band in a manner that the watermark embedding visual artifact occurs in the highly textured, highly contrasted and very dark/bright areas of the image. In the lowest frequency sub-band of wavelet transform, the coefficients are selected by independent analysis of texture, contrast and luminance information. In high frequency sub-bands, the coefficient selection is done by analyzing coefficients amplitude and local entropy. The experimental results show that the watermarked test images are highly transparent and robust against scalable wavelet-based image coding even at very low bit-rate coding. The proposed approach can guarantee content authentication for scalable coded images, especially on heterogeneous networks which different users with different process capabilities and network access bandwidth use unique multimedia sources.












Similar content being viewed by others
References
Abhayaratne C, Bhowmik D (2013) Scalable watermark extraction for real-time authentication of jpeg 2000 images. J Real-Time Image Process 8(3):307–325
Akhaee MA, Marvasti F (2013) A survey on digital data hiding schemes: principals, algorithms, and applications. ISC Int J Inform Secur 5(1):5–36
Akhbari B, Ghaemmaghami S (2005) Watermarking of still images in wavelet domain based on entropy masking model. In: TENCON IEEE Region 10. IEEE, pp 1–6
Antonini M, Barlaud M, Mathieu P, Daubechies I (1992) Image coding using wavelet transform. IEEE Trans Image Process 1(2):205–220
Bansal D, Mathuria M (2017) Color image dual watermarking using dct and dwt combine approach. In: International conference on trends in electronics and informatics (ICEI), pp 630–634
Barni M, Bartolini F, Piva A (2001) Improved wavelet-based watermarking through pixel-wise masking. IEEE Trans Image Process 10(5):783–791
Bhatnagar G, Wu QJ, Raman B (2012) Robust gray-scale logo watermarking in wavelet domain. Comput Electr Eng 38(5):1164–1176
Bhowmik D, Abhayaratne C (2009) The effect of quality scalable image compression on robust watermarking. In: 16Th international conference on digital signal processing. IEEE, pp 1–8
Bhowmik D (2011) Robust watermarking techniques for scalable coded image and video. Ph.D. thesis, University of Sheffield
Bhowmik D, Abhayaratne C (2014) On robustness against jpeg2000: a performance evaluation of wavelet-based watermarking techniques. Multimed Syst 20(2):239–252
Bhowmik D, Abhayaratne C (2016) Quality scalability aware watermarking for visual content. IEEE Trans Image Process 25(11):5158–5172
Boroumand M, Ebrahimi A (2009) An improved quantization based watermarking scheme using local entropy in wavelet domain. In: IEEE International conference on signal and image processing applications (ICSIPA). IEEE, pp 268–272
Charrier M, Cruz D, Larsson M (1999) Jpeg2000, the next millennium compression standard for still images. In: IEEE International conference on multimedia computing and systems. IEEE, vol 1, pp 131–132
Chen TPc, Chen T (2000) Progressive image watermarking. In: IEEE International conference on multimedia and expo (ICME). IEEE, vol 2, pp 1025–1028
Chen TS, Chen J, Chen JG (2004) A simple and efficient watermark technique based on jpeg2000 codec. Multimed Syst 10(1):16–26
Christopoulos C, Skodras A, Ebrahimi T (2000) The jpeg2000 still image coding system: an overview. IEEE Trans Consum Electron 46(4):1103–1127
Chunhua L, Li F (2011) Adaptive image watermarking algorithm based on biorthogonal wavelet transform. In: International conference on e-business and e-government (ICEE). IEEE, pp 1–4
Cover TM, Thomas JA (2012) Elements of information theory. Wiley, New York
Danyali H, Mertins A (2003) Fully spatial and snr scalable, spiht-based image coding for transmission over heterogenous networks. J Telecommun Inf Technol 3:92–98
Danyali H (2004) Highly scalable wavelet image and video coding for transmission over heterogeneous networks
Danyali H, Mertins A (2004) Flexible, highly scalable, object-based wavelet image compression algorithm for network applications. IEE Proceedings-Vision. Image Signal Process 151(6):498–510
Daubechies I (1990) The wavelet transform, time-frequency localization and signal analysis. IEEE Trans Inf Theory 36(5):961–1005
Davis GM, Nosratinia A (1999) Wavelet-based image coding: an overview. In: Applied and computational control, signals, and circuits. Springer, pp 369–434
Deb K (2001) Multi-objective optimization using evolutionary algorithms, 1st edn. Wiley, New York. http://www.worldcat.org/isbn/047187339X
Deljavan Amiri M, Danyali H, Zahir-Azami B (2011) Intelligent scalable image watermarking robust against progressive dwt-based compression using genetic algorithms. ISC Int J Inform Secur 3(1):51–66
Dufaux F, Wee S, Apostolopoulos J, Ebrahimi T (2004) Jpsec for secure imaging in jpeg 2000. In: SPIE Proceedings of Applications of digital image processing XXVII, LTS-CONF-2004-041. SPIE
Ebrahim Sorkhabi A, Deljavan Amiri M, Khanteymoori AR (2017) Duality evolution: an efficient approach to constraint handling in multi-objective particle swarm optimization. Soft Comput 21(24):7251–7267
Fatemizadeh E, Maneshi M (2012) A new watermarking algorithm based on human visual system for content integrity verification of region of interest. Comput Inf 31(4):877–899
Feng Xc, Yang Y (2005) A new watermarking method based on dwt. Comput Intell Secur 1:1122–1126
Gonzalez RC, Woods RE (2002) Digital image processing. Prentice Hall, Upper Saddle River
Gupta A, Agrawal K (2017) New embedding algorithm for digital watermarking using 5-dwt and 2-dct. In: 2Nd international conference on telecommunication and networks (TEL-NET), pp 1–5
Hsiang S (2003) Highly scalable subband/wavelet image and video coding
Huo F, Gao X (2006) A wavelet based image watermarking scheme. In: 2006 IEEE international conference on Image processing. IEEE, pp 2573–2576
Islam M, Mallikharjunudu G, Parmar AS, Kumar A, Laskar RH (2017) Svm regression based robust image watermarking technique in joint dwt-dct domain. In: International conference on intelligent computing, instrumentation and control technologies (ICICICT), pp 1426–1433
Jin C, Peng J (2006) A robust wavelet-based blind digital watermarking algorithm. Inf Technol J 5(2):358–363
Kundur D, Hatzinakos D (1998) Digital watermarking using multiresolution wavelet decomposition. In: Proceedings of the IEEE International Conference on Acoustics, Speech and Signal Processing. IEEE, vol 5, pp 2969–2972
Kundur D, Hatzinakos D (2004) Toward robust logo watermarking using multiresolution image fusion principles. IEEE Trans Multimed 6(1):185–198
Lewis AS, Knowles G (1992) Image compression using the 2-d wavelet transform. IEEE Trans Image Process 1(2):244–250
Li W (1998) Bit-plane coding of dct coefficients for fine granularity scalability. ISO/IEC JTC1/SC29/WG11 MPEG98/m3989
Lumini A, Maio D (2000) A wavelet-based image watermarking scheme. In: International conference on information technology: Coding and computing. IEEE, pp 122–127
Makbol NM, Khoo BE, Rassem TH (2016) Block-based discrete wavelet transform-singular value decomposition image watermarking scheme using human visual system characteristics. IET Image Process 10(1):34–52
Mallat SG (1989) A theory for multiresolution signal decomposition: the wavelet representation. IEEE Trans Pattern Anal Mach Intell 11(7):674–693
Marusic S, Tay DB, Deng G, Palaniswami M (2003) A study of biorthogonal wavelets in digital watermarking. In: International conference on image processing (ICIP). IEEE, vol 2, pp II–463
Mazumdar H, Anand P, Soni SJ, Joshi M, Rajeev K, Rajak M (2015) Human visual system models in digital watermarking. In: International conference and workshop on computing and communication (IEMCON). IEEE, pp 1–7
Meerwald P (2001) Quantization watermarking in the jpeg2000 coding pipeline. In: Communications and multimedia security issues of the new century. Springer, pp 69–79
Meerwald P, Uhl A (2008) Scalability evaluation of blind spread-spectrum image watermarking. In: IWDW. Springer, pp 61–75
Mekarsari YA, Setiadi DRIM, Sari CA, Rachmawanto EH (2018) Muljono: Non-blind rgb image watermarking technique using 2-level discrete wavelet transform and singular value decomposition. In: International conference on information and communications technology (ICOIACT), pp 623–627
Mittal N, Bisen AS, Gupta R (2017) An improved digital watermarking technique based on 5-dwt, fft svd. In: International conference on trends in electronics and informatics (ICEI), pp 561–566
Pereira S, Voloshynovskiy S, Madueno M, Marchand-Maillet S, Pun T (2001) Second generation benchmarking and application oriented evaluation. In: International workshop on information hiding. Springer, pp 340–353
Petitcolas FA, Steinebach M, Raynal F, Dittmann J, Fontaine C, Fatès N (2001) Public automated web-based evaluation service for watermarking schemes: Stirmark benchmark. In: Security and watermarking of multimedia contents, pp 575–584
Piper A, Safavi-Naini R, Mertins A (2005) Resolution and quality scalable spread spectrum image watermarking. In: Proceedings of the 7th workshop on Multimedia and security. ACM, pp 79–90
Piper A (2010) Scalable watermarking for images
Piper A, Safavi-Naini R (2013) Scalable fragile watermarking for image authentication. IET Inf Secur 7(4):300–311
Rhayma H, Makhloufi A, Hamam H, ben Hmida A (2018) Semi fragile watermarking scheme for image recovery in wavelet domain. In: 4Th international conference on advanced technologies for signal and image processing (ATSIP), pp 1–5
Said A, Pearlman WA (1996) A new, fast, and efficient image codec based on set partitioning in hierarchical trees. IEEE Trans Circ Syst Video Technol 6(3):243–250
Schwarz H, Marpe D, Wiegand T (2007) Overview of the scalable video coding extension of the h. 264/avc standard. IEEE Trans Circ Syst Video Technol 17 (9):1103–1120
Selvan S, Ramakrishnan S (2007) Svd-based modeling for image texture classification using wavelet transformation. IEEE Trans Image Process 16(11):2688–2696
Soheili MR (2010) Blind wavelet based logo watermarking resisting to cropping. In: 20Th international conference on pattern recognition (ICPR). IEEE, pp 1449–1452
Su PC, Wang HJM, Kuo CCJ (2001) An integrated approach to image watermarking and jpeg-2000 compression. J VLSI Signal Process 27(1):35–53
Suhail M, Obaidat MS, Ipson SS, Sadoun B (2003) A comparative study of digital watermarking in jpeg and jpeg 2000 environments. Inf Sci 151:93–105
Sullivan GJ, Boyce JM, Chen Y, Ohm JR, Segall CA, Vetro A (2013) Standardized extensions of high efficiency video coding (hevc). IEEE J Sel Top Signal Process 7(6):1001–1016
Sun Q, Chang SF (2005) A secure and robust digital signature scheme for jpeg2000 image authentication. IEEE Trans Multimed 7(3):480–494
Tao H, Liu J, Tian J (2001) Digital watermarking technique based on integer harr transforms and visual properties. In: Image compression and encryption technologies. International society for optics and photonics, vol 4551, pp 239–245
Verma P, Dastidar RG, Jain S, Potghan S (2017) Comparative analysis of conventional 2-level dwt and color plane watermarking for telemedicine applications. In: 2Nd international conference on telecommunication and networks (TEL-NET), pp 1–8
Wang Z, Bovik AC, Sheikh HR, Simoncelli EP (2004) Image quality assessment: from error visibility to structural similarity. IEEE Trans Image Process 13 (4):600–612
Watson AB (1993) Dct quantization matrices visually optimized for individual images. In: Proceedings of SPIE, vol 1913
Xie L, Arce GR (1998) Joint wavelet compression and authentication watermarking. In: International conference on image processing (ICIP). IEEE, vol 2, pp 427–431
Zhang Z, Mo YL (2001) Embedding strategy of image watermarking in wavelet transform domain. In: Image compression and encryption technologies. International society for optics and photonics, vol 4551, pp 127–132
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher’s Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Deljavan Amiri, M., Meghdadi, M. & Amiri, A. HVS-based scalable image watermarking. Multimed Tools Appl 78, 7097–7124 (2019). https://doi.org/10.1007/s11042-018-6419-1
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-018-6419-1