Abstract
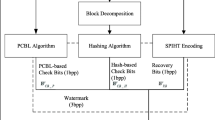
This paper analyses the security of an effective SVD-based image tampering detection and self-recovery scheme that has been recently proposed by S. Dadkhah et al. Some errors in the embedding/extraction processes are underlined and an attack against this scheme is demonstrated. The theoretical and experimental results show that the proposed scheme is not secure. Finally, an improvement of the scheme is proposed to enhance its security.


















Similar content being viewed by others
References
Arnold V, Avez A (1968) Ergodic problems of classical mechanics. Benjamin, New York, p 564
Aslantas V, Ozer S, Ozturk S (2009) Improving the performance of dct-based fragile watermarking using intelligent optimization algorithms. Opt Commun 282:2806–2817
Bao J, Yang Q (2012) Period of the discrete arnold cat map and general cat map. Nonlin Dyn 70:1365–1375
Benrhouma O, Hermassi H, El-Latif AAA, Belghith S (2015) Chaotic watermark for blind forgery detection in images. Multimed Tools Appl:1–24
Bhatnagar G, Raman B (2011) A new robust reference logo watermarking scheme. Multimed Tools Appl 52:621–640
Botta M, Cavagnino D, Pomponiu V (2015) A successful attack and revision of a chaotic system based fragile watermarking scheme for image tamper detection. AEU - Int J Electron Commun 69(1):242–245
Chang CC, Hu YS, LU TC (2006) A watermarking-based image ownership and tampering authentication scheme. Pattern Recogn Lett 27:439–446
Dadkhah S, Manaf AA, Hori Y, Hassanien AE, Sadeghi S (2014) An effective svd-based image tampering detection and self-recovery using active watermarking. Signal Process Image Commun 29(10):1197–1210
Dyson F, Falk H (1992) Period of a discrete cat mapping. Am Math Mon 99 (7):603–614
Kerckhoffs A (1883) La cryptographie militaire. J des Sciences Militaires 9:5–38
Li M, Zhang J, Wen W (2014) Cryptanalysis and improvement of a binary watermark-based copyright protection scheme for remote sensing images. Optik - Int J Light Electron Opt 125(24):7231–7234
Li J, Li X, Yang B, Sun X (2015) Segmentation-based image copy-move forgery detection scheme. IEEE Trans Inf Forens Secur 10(3):507–518
Oussama B, Houcemeddine H, Safya B (2015) Tamper detection and self-recovery scheme by dwt watermarking. Nonlin Dyn 79(3):1817–1833
Peterson G (1997) Arnold’s cat map. http://online.redwoods.cc.ca.us/instruct/darnold/laproj/Fall97/Gabe/catmap.pdf
Qin C, Zhang X (2015) Effective reversible data hiding in encrypted image with privacy protection for image content. J Vis Commun Image Represent 31:154–164
Qin C, Chang C-C, Chen P-Y (2012) Self-embedding fragile watermarking with restoration capability based on adaptive bit allocation mechanism. Signal Process 92(4):1137–1150
Qin C, Chang CC, Chiu YP (2014) A novel joint data-hiding and compression scheme based on smvq and image inpainting. IEEE Trans Image Process 23(3):969–978
Qin C, Chang C-C, Hsu T-J (2015) Reversible data hiding scheme based on exploiting modification direction with two steganographic images. Multimed Tools Appl 74(15):5861–5872
Singh D, Singh SK (2016) Effective self-embedding watermarking scheme for image tampered detection and localization with recovery capability. J Vis Commun Image Represent 38:775–789
Teng L, Wang X, Wang X (2013) Cryptanalysis and improvement of a chaotic system based fragile watermarking scheme. AEU - Int J Electron Commun 67 (6):540–547
Wang X, Pang K, Zhou X, Zhou Y, Li L, Xue J (2015) A visual model-based perceptual image hash for content authentication. IEEE Trans Inf Forens Secur 10(7):1336–1349
Wu XY, Guan ZH (2007) A novel digital watermark algorithm based on chaotic maps. Phys Lett A 365:403–406
Zhang X, Wang S (2008) Fragile watermarking with error-free restoration capability. IEEE Trans Multimed 10(8):1490–1499
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Benrhouma, O., Hermassi, H. & Belghith, S. Security analysis and improvement of an active watermarking system for image tampering detection using a self-recovery scheme. Multimed Tools Appl 76, 21133–21156 (2017). https://doi.org/10.1007/s11042-016-4054-2
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-016-4054-2