Abstract
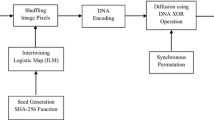
In this paper, a novel secure cryptosystem is proposed for direct encryption of color images, based on transformed logistic maps. The proposed cipher provides good confusion and diffusion properties that ensures extremely high security due to the mixing of colors pixels. The encryption scheme makes use of six odd secret keys and chaotic keys for each operation. The operations include initial permutation of all pixels with six odd keys, nonlinear diffusion using first chaotic key, xoring the second chaotic key with resultant values and zig-zag diffusion with third chaotic key. The proposed scheme supports key sizes ranging from 192 to 400 bits. The security and performance of the proposed image encryption technique have been analysed thoroughly using statistical analysis, key sensitivity analysis, differential analysis, key space analysis, entropy analysis and performance analysis. Results of the various types of analyses are showing that the proposed image encryption technique is more secure and fast and hence suitable for the real-time applications.






Similar content being viewed by others
References
Alvarez G, Li S (2009) Cryptanalyzing a nonlinear chaotic algorithm (NCA) for image encryption. Commun Nonlinear Sci Numer Simulat 14:3743–3749
Baptista MS (1998) Cryptography with chaos. Phys Lett A 240:50–54
Chen GR, Mao YB, Charles KC (2004) A symmetric image encryption scheme based on 3D chaotic cat maps. Chaos, Solitons Fractals 21:749–761
Gao TG, Chen ZQ (2008) Image encryption based on a new total shuffling algorithm. Chaos, Solitons Fractals 38:213–220
Jun H, Zheng J, Li Z-b, Qian H-f (2009) An improved color image encryption based on chaotic map and OCML model. In: IEEE international conference on networks security, wireless communications and trusted computing, pp 365–369
Liu S, Sun J, Xu Z, Liu J (2008) Analysis on an image encryption algorithm. In: IEEE international workshop on education technology and training & international workshop on geoscience and remote sensing, pp 803–806
Matthew R (1989) On the derivation of a chaotic encryption algorithm. Cryptologia 8(1):29–42
Menezes AJ, Oorschot PCV, Vanstone SA (1997) Handbook of applied cryptography. CRC Press, Boca Raton, FL
Pareek NK, Patidar V, Sud KK (2006) Image encryption using chaotic logistic map. Image Vis Comput 24:926–934
Patidar V, Pareek NK, Sud KK (2009) A new substitution diffusion based image cipher using chaotic standard and logistic maps. Commun Nonlinear Sci Numer Simulat 14:3056–3075
Rhouma R, Solak E, Belghith S (2010) Cryptanalysis of a new substitution-diffusion based image cipher. Commun Nonlinear Sci Numer Simulat 15:1887–1892
Sabery MK, Yaghoobi M (2008) A new approach for image encryption using chaotic logistic map. In: IEEE international conference on advanced computer theory and engineering, pp 585–590
Schneier B (1996) Applied cryptography: protocols algorithms and source code in C. Wiley, New York, USA
ShuTang LIU, Sun FY (2009) Spatial chaos-based image encryption design. Sci China Ser G Phys Mech Astron 52(2):177–183
Xiao H-P, Zhang G-J (2006) An image encryption scheme based on chaotic systems. In: IEEE international conference on machine learning and cybernetics, pp 2707–2711
Xie J, Yang C, Tian L (2009) An encryption algorithm based on transformed logistic map. In: IEEE international conference on network security, wireless communications and truested computing, pp 111–114
Xu S-J, Wang Y-L, Wang J-Z, Tian M (2008) A novel image encryption scheme based on chaotic maps. In: IEEE ICSP, pp 1014–1018
Zhang Y, Wang Y, Shen X (2007) A chaos-based image encryption algorithm using alternate structure. Sci China Ser F Inf Sci 50(3):334-341
Acknowledgements
This research is partially supported by the All India Council for Technical Education, New Delhi, India.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Sam, I.S., Devaraj, P. & Bhuvaneswaran, R.S. A novel image cipher based on mixed transformed logistic maps. Multimed Tools Appl 56, 315–330 (2012). https://doi.org/10.1007/s11042-010-0652-6
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-010-0652-6