Abstract
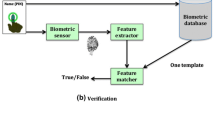
This paper pioneers an experimentation on assessing security and performance of a well-established biometric authentication protocol. Using the gold standard in software reliability, a path-oriented software quality control tool, the work exploits the attack surface leveraging path analysis. The test not only identifies security vulnerabilities in a system but also pinpoints those vulnerabilities at real security risk to optimize resource allocation. The automated holistic examination of the authentication process reveals a weakness in the biometric authentication protocol at study. The attack map generated from the analysis directs its improvement. Reexamination validates the security of the protocol. The work also studies the computational complexity of the protocol, thereby, recommends the key length suitable to biometric authentication for wireless body area networks.










Similar content being viewed by others
References
Kanjee MR, Liu H (2013) A generic authentication protocol for wireless body area networks. BODYNETS, Boston
Cherukuri S, Venkatasubramanian K, Gupta S (2003) Biosec: a biometric based approach for securing communication in wireless networks of biosensors implanted in the human body. In 2003 International Conference on Parallel Precessing Workshops (ICPPW 2003), Kaohsiung, Taiwan
Zeng K, Govindan K, Mohapatra P (2010) Non-cryptographic authentication and identification in wireles networks. IEEE Wirel Commun Secur Priv Emerg Wirel Netw 15(5):56–62
Shi L, Li M, Yu S, Yuan J (2013) BANA: body area network authentication exploiting channel characteristics. IEEE J Sel Areas Commun Spec Issue Sig Proc Tech Wirel Phys Layer Secur
Zhang Z, Wang H, Vasilakos V, Fang H (2012) ECG-cryptography and authentication in body area networks. IEEE Trans Inf Technol Biomed 16(6):1070–1078
Yao L, Ali ST, Sivaraman V, Ostry D (2011) Improving secret key generation performance for on-body devices. In 6th International Conference on Body Area Networks (BodyNets), Beijing, China
Rong C, Cheng H (2012) Authenticated health monitoring scheme for wireless body sensor networks. In 7th International Conference on Body Area Networks (BodyNets), Oslo, Norway
Dam M, Stadler R (2005) A generic protocol for network state aggregation. Radiovetenskap och Kommunikation (RVK), Linkoping
Venkatasubramanian KK, Gupta SK, Banerjee A (2010) PSKA: usable and secure key agreement scheme for body area networks. IEEE Trans Inf Technol Biomed 14(1):60–68
Kleinjun T, Aoki K, Franke J, Lenstra A, Thomé E, Bos J, Gaudry P, Kruppa A, Montgomery P, Osvik DA, Riele HT, Timofeev A, Zimmermann P (2010) Factorization of a 768-bit RSA modulus. Cryptology ePrint Archive, Report 2010/006
Kanjee MR, Liu H (2014) Authentication and key relay in medical cyber-physical systems. Wiley’s Secur Commun Netw J 8
Suzuki J, Phan DH, Budiman H (2014) A nonparametric stochastic optimizer for TDMA-based neuronal signaling. IEEE Trans NanoBiosci 13(3):244–254
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Liu, H., El Lazkani, E. Biometric Inspired Mobile Network Authentication and Protocol Validation. Mobile Netw Appl 21, 130–138 (2016). https://doi.org/10.1007/s11036-016-0701-0
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11036-016-0701-0