Abstract
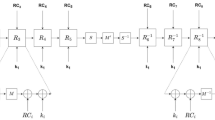
In this paper an improved Montgomery multiplier, based on modified four-to-two carry-save adders (CSAs) to reduce critical path delay, is presented. Instead of implementing four-to-two CSA using two levels of carry-save logic, authors propose a modified four-to-two CSA using only one level of carry-save logic taking advantage of pre-computed input values. Also, a new bit-sliced, unified and scalable Montgomery multiplier architecture, applicable for both RSA and ECC (Elliptic Curve Cryptography), is proposed. In the existing word-based scalable multiplier architectures, some processing elements (PEs) do not perform useful computation during the last pipeline cycle when the precision is not equal to an exact multiple of the word size, like in ECC. This intrinsic limitation requires a few extra clock cycles to operate on operand lengths which are not powers of 2. The proposed architecture eliminates the need for extra clock cycles by reconfiguring the design at bit-level and hence can operate on any operand length, limited only by memory and control constraints. It requires 2∼15% fewer clock cycles than the existing architectures for key lengths of interest in RSA and 11∼18% for binary fields and 10∼14% for prime fields in case of ECC. An FPGA implementation of the proposed architecture shows that it can perform 1,024-bit modular exponentiation in about 15 ms which is better than that by the existing multiplier architectures.
Similar content being viewed by others
References
Stallings W (1995) Network and internetwork security principles and practise. Prentice Hall, New York, USA
Menezes A, van Oorschot P, Vanstone S (1997) Handbook of applied cryptography. CRC Press, Florida, USA
Rivest RL, Shamir A, Adleman L (1978) A method for obtaining digital signatures and public-key cryptosystems. Comm ACM 21(2):120–126
Diffie W, Hellman ME (1976) New directions in cryptography. IEEE Trans Inf Theory 22:644–654
National Institute for Standards and Technology (2000) Digital Signature Standard (DSS). FIPS PUB 186–2, January
Menezes AJ (1993) Elliptic curve public key cryptosystems. Kluwer Academic Publishers, Boston, MA
Koblitz N (1987) Elliptic curve cryptosystems. Math Comput 48(177):203–209, January
Miller VS (1986) Uses of elliptic curves in cryptography. In: Williams HC (ed) Advances in cryptology—CRYPTO ’85, vol. 218 of Lecture Notes in Computer Science. Springer, Berlin, Germany, pp 417–426
Lenstra AK, Verheul ER (2000) Selecting cryptographic key sizes. In: Imai H, Zheng Y (eds), Public Key Cryptography—PKC 2000, vol. 1751 of Lecture Notes in Computer Science. Springer , Berlin, Germany, pp 446–465
US National Institute of Standards and Technology (NIST) (2002) Cryptographic toolkit Jun. 2002, pp 83–84 [online]. Available: http://csrc.nist.gov/CryptoToolkit/kms/guideline-1.pdf
Montgomery PL (1985) Modular multiplication without trail division. Math Comput 44(70):519–521
Kim YS, Kang WS, Choi JR. Implementation of 1024-bit modular processor for RSA cryptosystem’. http://www.ap-asic.org/2000/proceedings/10-4.pdf
Bunimov V, Schimmler M, Tolg B (2002) A complexity-effective version of Montgomery’s algorithm. Presented at the Workshop on Complexity Effective Designs (WECD02), May 2002
McIvor C, McLoone M, McCanny JV (2004) Modified Montgomery modular multiplication and RSA exponentiation techniques. IEE Proc Comput Digit Tech 151(6):402–408
Sudhakar M, Kamala RV, Srinivas MB (2007) An efficient, reconfigurable and unified Montgomery multiplier architecture. Proceedings. IEEE/ACM VLSI Design 2007, Bangalore, India, January 6–10, pp 750–755
Savas E, Tenca AF, Koc CK (2000) A scalable and unified multiplier architecture for finite fields GF(p) and GF(2m). Proceedings of CHES, pp 281–296
Großschädl J (2001) A bit-serial unified multiplier architecture for finite fields GF(p) and GF(2m). Proc. CHES 2001, August, pp 202–218
Savas E, Tenca AF, Ciftcibasi ME, Koc CK (2004) Multiplier architectures for GF(p) and GF(2n). IEE Proc Comput Digit Tech 151(2):147–160, March
Tenca AF, Koc CK (2003) A scalable architecture for modular multiplication based on Montgomery’s algorithm. IEEE Trans Comput 52(9):1215–1221, Sept
Harris D, Krishnamurthy R, Anders M, Mathew S, Hsu S (2005) An improved unified scalable radix-2 Montgomery multiplier. IEEE (ARITH-17), pp 172–178
Certicom Research, Recommended Elliptic Curve Domain Parameters, http://www.secg.org/download/aid-386/sec2_final.pdf
NIST DSS Standard, Basicrypt—Elliptic Curve Cryptography (ECC) Benchmark Suite benchmark, http://csrc.nist.gov/publications/fips/fips186-2/fips186-2-change1.pdf
Virtex™-E 1.8 V Field Programmable Gate Arrays, http://www.xilinx.com/bvdocs/publications/ds022.pdf
Virtex-II Pro and Virtex-II Pro X Platform FPGAs: Complete Data Sheet http://www.xilinx.xom/bvdocs/publications/ds083.pdf
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Sudhakar, M., Kamala, R.V. & Srinivas, M.B. New and Improved Architectures for Montgomery Modular Multiplication. Mobile Netw Appl 12, 281–291 (2007). https://doi.org/10.1007/s11036-007-0019-z
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11036-007-0019-z