Abstract
Objectives
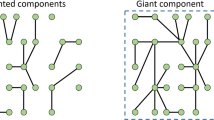
The current research examines how the efficiency/security tradeoff shapes the evolution of dynamic terrorist networks by focusing on the structural properties of these collectives. Some scholars argue that terrorist groups develop as chain-like, decentralized structures, while others maintain that terrorist networks form patterns of redundant ties and organize around a few highly connected individuals, or central hubs. We investigate these structural properties and consider whether patterns vary at different phases of a terrorist network’s formation.
Methods
Using a variety of descriptive network measures and Separable Temporal Exponential Random Graph Models, we consider patterns of tie formation across eleven multi-wave terrorism networks from the John Jay & ARTIS Transnational Terrorism database. This dataset includes networks from prominent attacks and bombings that occurred in the last 3 decades (e.g., the 2002 Bali Bombings), where nodes represent individual terrorists and ties represent social relationships.
Results
We find that terrorist groups navigate the efficiency/security tradeoff by developing increasingly well-connected networks as they prepare for a violent incident. Our results also show that highly central nodes acquire even more ties in the years directly preceding an attack, signifying that the evolution of terrorist networks tends to be structured around a few key actors.
Conclusions
Our findings have the potential to inform counterterrorism efforts by suggesting which actors in the network make the most influential targets for law enforcement. We discuss how these strategies should vary as extremist networks evolve over time.




Similar content being viewed by others
Notes
Additionally, according to Gerdes (2015), it is occasionally difficult to correctly distinguishing between the various relationship types in the JJATT data.
For instance, in the network that surrounded the November 17th attacks of 2000, all ties were present during each wave of interest. Because there was no observable change, this network was excluded from our final sample.
While these attack networks are distinct, they are not independent. Our sample includes individual terrorists who participated in multiple attack networks.
It is important to note that we cannot verify whether the relational ties observed during the attack year occurred before or after the group orchestrated the attack of interest.
For two of our networks (the 2000 Philippines Ambassador residence bombing and the 2000 Christmas Eve bombing), there are limited data on the structure of the network before each attack took place. As a result, our analyses of these two networks is characterized by larger gaps of time (e.g., 5 years) between the earliest waves of data.
In order for our multivariate models to achieve satisfactory goodness of fit statistics, it is necessary that we observe a time period with a sufficient degree of tie formation and tie dissolution. Across our five waves of data, the vast majority of tie formation (99.9%) occurred between Wave 1 and Wave 4, and only 9.8% of observed tie dissolution transpired between these time points. As a result, we include Wave 5 in our analytic sample because it introduces a necessary degree of tie dissolution for our statistical models to converge.
Note that Helfstein and Wright (2011) argue that it is unlikely that terrorist network structure and officials’ willingness to collect and release relational data are associated and, thus, this limitation is unlikely to substantively bias analyses of structural processes.
Transitivity is the geometrically weighted edgewise shared parameter and brokerage is the geometrically weighted dyadwise shared parameter (see Snijders et al. 2006). For all terms that require a decay parameter, we use a weight of 0.10.
In supplemental STERGMs, we include node match formation parameters to account for organizational role homophily and education homophily among the individual terrorists in our sample (available upon request). Including these controls does not substantively alter the interpretation of our parameters of interest. However, small sample sizes and missing data on these individual-level characteristics prevent us from examining these controls further.
We assess the goodness of fit of our STERGMs by comparing the degree distribution, distribution of edge-wise shared partners, and the distribution of geodesic distances of the observed networks to the simulated networks generated by the STERGMs (analyses available upon request). The STERGMs presented here come close to matching the observed data on all three of these higher-order statistics.
Degree, closeness, and betweenness centralization reach their maximum value of 1 in star-shaped graphs where one actor is tied to all other actors and these actors are not tied to each other. The measures reach their minimum score of 0 in networks where all actors share equal actor indices for the centralization measure of interest (Wasserman and Faust 1994).
It is important to note that the lack of power in these supplemental analyses preclude us from relying on their findings. The number of terrorist networks in our sample is too limited to justify a thorough analysis of contextual variation. We leave further questions about variation across terrorist networks open to future research.
Note that these findings only apply to those networks included in our final analytic sample. Due to the constraints of our modeling approach, it was necessary to exclude attack networks that did not exhibit any structural change over the five waves of interest.
References
Albert R, Jeong H, Barabási AL (2000) Error and attack tolerance of complex networks. Nature 406:378–382
Armal LAN, Scala A, Barthelemy M, Stanley HE (2000) Classes of small-world networks. Proc Natl Acad Sci 97(21):11149–11152
Asal V, Rethemeyer K (2006) Researching terrorist networks. J Secur Educ 1(4):65–74
Baker WE, Faulkner RR (1993) The social organization of conspiracy: illegal networks in the heavy electrical equipment industry. Am Sociol Rev 58(6):837–860
Bakker RM, Raab J, Milward HW (2011) A preliminary theory of dark network resilience. J Policy Anal Manag 31(1):33–62
Barabási AL, Albert R (1999) Emergence of scaling in random networks. Science 286(5439):509–512
Blau PM (1968) The hierarchy of authority in organizations. Am J Sociol 73(4):453–467
Block P (2015) Reciprocity, transitivity, and the mysterious three-cycle. Soc Netw 40:163–173
Block P, Koskinen J, Holloway J, Steglich C, Stadtfeld C (2018) Change we can believe in: comparing longitudinal network models on consistency, interpretability and predictive power. Soc Netw 52:180–191
Bright D, Koskinen J, Malm A (2018) Illicit network dynamics: the formation and evolution of a drug trafficking network. J Quant Criminol. https://doi.org/10.1007/s10940-018-9379-8
Carley KM (2006) Destabilization of covert networks. Comput Math Organ Theory 12(1):51–66
Crossley N, Edwards G, Harries E, Stevenson R (2012) Covert social movement networks and the secrecy-efficiency trade off: the case of the UK suffragettes (1906–1914). Soc Networks 34:634–644
Cunningham D, Everton S, Murphy P (2016) Understanding dark networks: a strategic framework for the use of social network analysis. Rowman & Littlefield, Landham
Desmarais BA, Cranmer SJ (2012) Micro-level interpretation of exponential random graph models with application to estuary networks. Policy Stud J 40(3):402–434
Duxbury SW, Haynie DL (2019) Criminal network security: an agent-based approach to evaluating network resilience. Criminology 57(2):314–342
Enders W, Su X (2007) Rational terrorists and optimal network structure. J Confl Resolut 51(1):33–57
Erickson BH (1981) Secret societies and social structure. Soc Forces 60(1):188–210
Everton SF (2012) Disrupting dark networks. Cambridge University Press, New York
Everton SF (2016) Social networks and religious violence. Rev Relig Res 58(2):191–217
Felmlee D, Faris R (2016) Toxic ties: a network of friendship, dating, and cyber victimization. Soc Psychol Q 79:243–262
Felmlee D, McMillan C, Inara Rodis P, Osgood DW (2018) Falling behind: lingering costs of the high school transition for youth friendships and grades. Sociol Educ 91(2):159–182
Gartner SS, Felmlee D, Yarlagadda R, Verma D (2019) Understanding patterns of terrorism in India using AI machine learning: 2007–2017. In: Fifteenth international conference on technology, knowledge & society, Barcelona
Gerdes LM (2015) Dark dimensions: clarifying relationships among clandestine actors. In: Gerdes LM (ed) Illuminating dark networks: the study of clandestine groups and organizations. Cambridge University Press, New York, pp 19–38
Gill P, Lee J, Rethemeyer KR, Horgan J, Asal V (2014) Lethal connections: the determinants of networks connections in the Provisional Irish Republican Army, 1970–1998. Int Interact 40(1):52–78
Granovetter MS (1973) The strength of weak ties. Am J Sociol 78(6):1360–1380
Helfstein S, Wright D (2011) Covert or convenient? Evolution of terror attack networks. J Confl Resolut 55(5):785–813
Horowitz MC, Potter PBK (2014) Allying to kill: terrorist intergroup cooperation and the consequences for lethality. J Confl Resolut 58(2):199–225
Hunter DR (2007) Curved exponential family models for social networks. Soc Netw 29:216–230
Hunter DR, Handcock MS, Butts CT, Goodreau SM, Morris M (2008) ergm: a package to fit, simulate and diagnose exponential-family models for networks. J Stat Softw 24(3):1–29
John Jay & ARTIS Transnational Terrorism (JJATT) database (2009) http://doitapps.jjay.cuny.edu/jjatt/index.php. Accessed 4 May 2018
Knoke D (2013) ‘It takes a network:’ the rise and fall of social network analysis in U.S. army counterinsurgency doctrine. Connections 33(1):1–10
Krebs VE (2002) Mapping networks of terrorist cells. Connections 24(3):23–52
Krivitsky PN, Goodreau SM (2017) STERGM—separable temporal ERGMs for modeling discrete relational dynamics with statnet
Lantz B, Hutchison R (2015) Co-offender ties and the criminal career: the relationship between co-offender group structure and the individual offender. J Res Crime Delinq 52(5):658–690
Lubbers MJ, Snijders TAB (2007) A comparison of various approaches to the exponential random graph model: a reanalysis of 102 student networks in school classes. Soc Netw 29(4):489–507
Magouirk J, Atran S, Sageman M (2008) Connecting terrorist networks. Stud Confl Terror 31(1):1–16
Maoz Z, Terris LG, Kuperman RD, Talmund I (2007) What is the enemy of my enemy? Causes and consequences of imbalanced international relations, 1816–2001. J Polit 69(1):100–115
Matthew R, Shambaugh G (2005) The limits of terrorism: a network perspective. Int Stud Rev 7(4):617–627
McAllister B (2004) Al Qaeda and the innovative firm: demythologizing the network. Stud Confl Terror 27(4):297–319
McFarland DA, Moody J, Diehl D, Smith JA, Thomas RJ (2014) Network ecology and adolescent social structure. Am Sociol Rev 79(6):1088–1121
McMillan C (2019) Tied together: adolescent friendship networks, immigrant status, and health outcomes. Demography 56(3):1075–1103
McMillan C, Felmlee D, Osgood DW (2018) Peer influence, friend selection, and gender: how network processes shape adolescent smoking, drinking, and delinquency. Soc Netw 55:86–96
Milward HB, Raab J (2006) Dark networks as organizational problems: elements of a theory. Int Public Manag J 9(3):333–360
Morselli C, Giguère C, Petit K (2007) The efficiency/security trade-off in criminal networks. Soc Netw 29:143–153
Newcomb TM (1961) The acquaintance process. Holt, Rinehart & Winston, New York
Newman MEJ (2001) Clustering and preferential attachment in growing networks. Phys Rev E 64:1–4
Osgood DW, Ragan DT, Wallace L, Gest SD, Feinberg ME, Moody J (2013) Peers and the emergence of alcohol use: influence and selection processes in adolescent friendship networks. J Res Adolesc 23(3):500–512
Papachristos AV (2009) Murder by structure: dominance relations and the social structure of gang homicide. Am J Sociol 115(1):74–128
Pedahzur A, Perliger A (2006) The changing nature of suicide attacks. Soc Forces 84(4):1987–2008
Perliger A (2018) Terrorism networks. In: Victor JN, Montgomery AH, Lubell M (eds) The oxford handbook of political networks. Oxford University Press, New York, pp 653–668
Pirolli P, Card S (2005) The sensemaking process and leverage points for analyst technology as identified through cognitive task analysis. In: Proceedings of international conference on intelligence analysis, p 4
Price DD (1976) A theory of bibliometric and other cumulative advantage processes. J Am Soc Inf Sci 27(5):292–306
Robins G, Pattison P, Kalish Y, Lusher D (2007) An introduction to exponential random graph (p*) models for social networks. Soc Netw 29(2):173–191
Rodríguez JA (2005) The March 11th terrorist network: in its weakness lies its strength. EPP-LEA working papers
Sageman M (2004) Understanding terror networks. University of Pennsylvania Press, Philadelphia
Sageman M (2008) The next generation of terror. Foreign Policy 165:37–42
Schaefer DR, Marcum CS (2018) Modeling network dynamics. SocArXiv https://doi.org/10.17605/osf.io/6rm9q
Schaefer DR, Simpkins SD, Vest AE, Price CD (2011) The contributions of extracurricular activities to adolescent friendships: new insights through social network analysis. Dev Psychol 47(4):1141–1152
Simmel G (1906) The sociology of secrecy and of secret societies. Am J Sociol 11(4):441–498
Snijders TAB, Baerveldt C (2003) A multilevel network study of the effects of delinquent behavior on friendship evolution. J Math Sociol 27(2–3):123–151
Snijders TAB, Pattison PA, Robins GL, Handcock MS (2006) New specifications for exponential random graph models. Sociol Methodol 36(1):99–153
Snijders TAB, van de Bunt GG, Steglich CEG (2010) Introduction to stochastic actor-based models for network dynamics. Soc Netw 32(1):44–60
Steglich C, Snijders TAB, Pearson M (2010) Dynamic networks and behavior: separating selection from influence. Sociol Methodol 40:329–393
Stevenson R, Crossley N (2014) Change in covert movement networks: the ‘inner circle’ of the Provisional Irish Republican Army. Soc Mov Stud 13(1):70–91
Stohl C, Stohl M (2007) Networks of terror: theoretical assumptions and pragmatic consequences. Commun Theor 17(2):93–124
Ünal MC (2019) Do terrorists make a difference in criminal networks? An empirical analysis on illicit drug and narco-terror networks in the prioritization between security and efficiency. Soc Netw 57:1–17
Wasserman S, Faust K (1994) Social network analysis: methods and applications. Cambridge University Press, Cambridge
Watts DJ, Strogatz SH (1998) Collective dynamics of ‘small-world’ networks. Nature 393(4):440–442
Weerman FM (2011) Delinquent peers in context: a longitudinal network analysis of selection and influence effects. Criminology 49(1):253–286
White G, Porter MD, Mazerolle L (2013) Terrorism risk, resilience and volatility: a comparison of terrorism patterns in three southeast Asian countries. J Quant Criminol 29(2):295–320
Widmer ED (1999) Family contexts as cognitive networks: a structural approach of family relationships. Pers Relatsh 6(4):487–503
Wood G (2017) The structure and vulnerability of a drug trafficking collaboration network. Soc Netw 48:1–9
Yarlagadda R, Felmlee D, Verma D, Gartner S (2018) Implicit terrorist networks: a two-mode social network analysis of terrorism in India. SBP-BRiMS 2018. LNCS 10899:1–8
Zech ST, Gabbay M (2016) Social network analysis in the study of terrorism and insurgency: from organization to politics. Int Stud Rev 18:214–243
Acknowledgements
This research was sponsored by the U.S. Army Research Laboratory and the U.K. Ministry of Defence under Agreement Number W911NF-16-3-0001. The views and conclusions contained in this document are those of the authors and should not be interpreted as representing the official policies, either expressed or implied, of the U.S. Army Research Laboratory, the U.S. Government, the U.K. Ministry of Defence or the U.K. Government. The U.S. and U.K. Governments are authorized to reproduce and distribute reprints for Government purposes notwithstanding any copyright notation hereon. This work was also supported by Pennsylvania State University and the National Science Foundation under an IGERT award # DGE-1144860, Big Data Social Science.
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
McMillan, C., Felmlee, D. & Braines, D. Dynamic Patterns of Terrorist Networks: Efficiency and Security in the Evolution of Eleven Islamic Extremist Attack Networks. J Quant Criminol 36, 559–581 (2020). https://doi.org/10.1007/s10940-019-09426-9
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10940-019-09426-9