Abstract
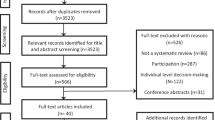
This systematic review aimed to identify the factors associated with information breaches in healthcare settings. We searched electronic databases, including PubMed, Embase, Scopus, and Wiley, for all publications until March 6, 2022 (no start date restriction) and outlined the eligibility criteria framework using Population, Concept, and Context (PCC). Our search strategies yielded 2,156 results, with nine studies included in the final review. We grouped the factors attributed to data breaches into four categories: organizational, information technology (IT), professionals/employees, and clients/patients. Hospital type, hospital size (more beds), higher operationalexpenses and revenue, higher admissions and discharges, and higher Electronic Medical Record (EMR) use, being at earlier phases of EMR adoption, were associated with higher information breaches. Professional factors such as the type of personnel involved and the hospital area can potentially impact the breaches' frequency and magnitude. Patients' sociodemographic, clinical, and behavioral characteristics, such as gender and educational attainment, appear to influence the perceived breach of confidentiality in healthcare settings. Identifying different factors contributing to health information breaches is crucial to protecting healthcare organizations and patients from the devastating consequences of data breaches.


Similar content being viewed by others
Availability of supporting data
The data used and/or analyzed during the current study are available from the corresponding author upon reasonable request.
Abbreviations
- DHHS:
-
Department of Health and Human Services
- ED:
-
Emergency Department
- EHR:
-
Electronic Health Record
- EMR:
-
Electronic Medical Record
- HIMSS:
-
Health Information and Management Systems Society
- HIPAA:
-
Health Insurance Portability and Accountability Act
- IT:
-
Information Technology
- OCR:
-
Office of Civil Rights
- PHI:
-
Protected Health Information
- SLR:
-
Systematic Literature Review
References
Chernyshev, M., S. Zeadally, and Z. Baig, Healthcare Data Breaches: Implications for Digital Forensic Readiness. J Med Syst, 2018. 43(1): 7. DOI: https://doi.org/10.1007/s10916-018-1123-2.
Bansal, G., F.M. Zahedi, and D. Gefen, The impact of personal dispositions on information sensitivity, privacy concern and trust in disclosing health information online. Decis Support Syst, 2010. 49(2): 138–150. DOI: https://doi.org/10.1016/j.dss.2010.01.010.
Seh, A.H., et al., Healthcare Data Breaches: Insights and Implications. Healthcare (Basel), 2020. 8(2): 133. DOI: https://doi.org/10.3390/healthcare8020133.
Gupta, M. and R. Sharman, Determinants of Data Breaches: A Categorization-Based Empirical Investigation. J Appl Secur Res, 2012. 7(3): 375–395. DOI: https://doi.org/10.1080/19361610.2012.686098.
K Pool, J., et al. Causes and impacts of personal health information (PHI) breaches: a scoping review and thematic analysis. in Twenty-Third Pacific Asia Conference on Information Systems, China July. 2019.
Cresswell, K.M. and A. Sheikh, Health information technology in hospitals: current issues and future trends. Future Hosp J, 2015. 2(1): 50–56. DOI: https://doi.org/10.7861/futurehosp.2-1-50.
U.S. Department of Health & Human Services. The HIPAA Privacy Rule. 2021 [cited 2022; Available from: https://www.hhs.gov/hipaa/for-professionals/privacy/index.html.
Dolezel, D. and A. McLeod, Managing Security Risk: Modeling the Root Causes of Data Breaches. Health Care Manag (Frederick), 2019. 38(4): 322–330. DOI: https://doi.org/10.1097/hcm.0000000000000282.
Shapiro, R., Breaking the code: is a promise always a promise. Ward Ethics: Dilemmas for Medical Students and Doctors in Training. J R Soc Med, 2001. 94(10): 545–546.
Choi, S.J. and M.E. Johnson, Understanding the relationship between data breaches and hospital advertising expenditures. Am J Manag Care, 2019. 25(1): e14-e20.
Kamoun, F. and M. Nicho, Human and organizational factors of healthcare data breaches: The swiss cheese model of data breach causation and prevention. Int J Healthc Inf Syst Inform, 2014. 9(1): 42–60.
Lee, I., An analysis of data breaches in the U.S. healthcare industry: diversity, trends, and risk profiling. Inf Secur J, 2021. 31:3, 346–358. DOI: https://doi.org/10.1080/19393555.2021.2017522.
Phua, C., Protecting organisations from personal data breaches. Comput Fraud Secur, 2009. 2009(1): 13–18. DOI: https://doi.org/10.1016/S1361-3723(09)70011-9.
Blanke, S.J. and E. McGrady, When it comes to securing patient health information from breaches, your best medicine is a dose of prevention: A cybersecurity risk assessment checklist. J Healthc Risk Manag, 2016. 36(1): 14–24. DOI: https://doi.org/10.1002/jhrm.21230.
Wikina, S.B., What caused the breach? An examination of use of information technology and health data breaches. Perspect Health Inf Manag, 2014. 11(Fall): 1 h-1 h.
Sarah Coble. Report Reveals Worst State for Healthcare Data Breaches in 2019. 2020 [cited 2022; Available from: https://www.infosecurity-magazine.com/news/report-healthcare-data-breaches-in/.
Dolezel, D. and A. McLeod, Cyber-Analytics: Identifying Discriminants of Data Breaches. Perspect Health Inf Manag, 2019. 16(Summer): 1a-1a.
Hwang, H.-G. and Y. Lin, Evaluating people’s concern about their health information privacy based on power-responsibility equilibrium model: A case of Taiwan. J Med Syst, 2020. 44(6): 112. DOI: https://doi.org/10.1007/s10916-020-01579-6.
Luna, R., et al., Cyber threats to health information systems: A systematic review. Technol Health Care, 2016. 24(1): 1–9. DOI: https://doi.org/10.3233/thc-151102.
Kruse, C.S., et al., Cybersecurity in healthcare: A systematic review of modern threats and trends. Technol Health Care, 2017. 25(1): 1–10. DOI: https://doi.org/10.3233/thc-161263.
Page, M.J., et al., Updating guidance for reporting systematic reviews: development of the PRISMA 2020 statement. J Clin Epidemiol, 2021. 134: 103–112. DOI: https://doi.org/10.1016/j.jclinepi.2021.02.003.
Beltran-Aroca, C.M., et al., Confidentiality breaches in clinical practice: what happens in hospitals? BMC Med Ethics, 2016. 17(1): 52. DOI: https://doi.org/10.1186/s12910-016-0136-y.
Gabriel, M.H., et al., Data breach locations, types, and associated characteristics among US hospitals. Am J Manag Care, 2018. 24(2): 78–84.
McLeod, A. and D. Dolezel, Cyber-analytics: Modeling factors associated with healthcare data breaches. Decis Support Sys, 2018. 108: 57–68. DOI: https://doi.org/10.1016/j.dss.2018.02.007.
Angst, C.M., et al., When do it security investments matter? Accounting for the influence of institutional factors in the context of healthcare data breaches. MIS Quarterly: Manag Inf Syst, 2017. 41(3): 893–916. DOI: https://doi.org/10.25300/misq/2017/41.3.10.
Bayisa, L., et al., Are the Things Told to Care Providers Kept Confidential?: Perceived Breaches of Confidentiality and Associated Factors Among HIV/AIDS Clients on ART at Nekemte Specialized Hospital, Western Ethiopia, 2021. HIV AIDS (Auckl), 2022. 14: 1–12. DOI: https://doi.org/10.2147/HIV.S350091.
Choi, S.J. and M.E. Johnson, The relationship between cybersecurity ratings and the risk of hospital data breaches. J Am Med Inform Assoc, 2021. 28(10): 2085–2092. DOI: https://doi.org/10.1093/jamia/ocab142/2 PMC8449620%M 34338786.
Choi, S.J., M.E. Johnson, and J. Lee, An event study of data breaches and hospital IT spending. Health Policy Technol, 2020. 9(3): 372–378. DOI: https://doi.org/10.1016/j.hlpt.2020.04.008.
Heath, M., T.H. Porter, and G. Silvera, Hospital characteristics associated with HIPAA breaches. Int J Healthc Manag, 2021: 1–10. DOI: https://doi.org/10.1080/20479700.2020.1870349.
Kwon, J. and M.E. Johnson, Proactive Versus Reactive Security Investments in the Healthcare Sector. MIS Q, 2014. 38(2): 451-A3.
Acknowledgements
Not applicable.
Funding
No funding for this study.
Author information
Authors and Affiliations
Contributions
All authors contributed to the research process in various forms, including original draft preparation, writing, review, and editing. AK conceptualized and designed the study, performed the database search, and outlined and critically revised the manuscript. SI performed quality appraisal, led the data extraction, and outlined the findings. SA, SB, CC, and NO identified the relevant studies and performed the data extraction.
Corresponding author
Ethics declarations
Ethical Approval and Consent to participate
Not applicable.
Human Ethics
Not applicable.
Consent for publication
Not applicable.
Competing Interests
The authors declare no potential competing interests.
Additional information
Publisher’s Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Electronic Supplementary Material
Below is the link to the electronic supplementary material.
Rights and permissions
Springer Nature or its licensor holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Khanijahani, A., Iezadi, S., Agoglia, S. et al. Factors Associated with Information Breach in Healthcare Facilities: A Systematic Literature Review. J Med Syst 46, 90 (2022). https://doi.org/10.1007/s10916-022-01877-1
Received:
Revised:
Accepted:
Published:
DOI: https://doi.org/10.1007/s10916-022-01877-1