Abstract
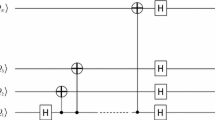
All previous semi-quantum secret sharing (SQSS) protocols have four common features: (1) they adopt product states or entangled states as quantum carriers; (2) the particles prepared by the quantum party are transmitted in a tree-type way; (3) they require the classical parties to possess the measurement capability; and (4) they are only suitable for two-level quantum system. In this paper, we generalize the SQSS concept into the d-level quantum system and propose two multiparty semi-quantum secret sharing (MSQSS) protocols with d-level single-particle states which do not require the classical parties to have the measurement capability. In the first protocol, the particles prepared by the quantum party are transmitted in a tree-type way, while in the second protocol, the particles prepared by the quantum party are transmitted in a circular way. The proposed MSQSS protocols are secure against some famous attacks, such as the intercept-resend attack, the measure-resend attack, the entangle-measure attack and the participant attack.


Similar content being viewed by others
References
Bennett, C.H., Brassard, G.: Quantum cryptography: public key distribution and coin tossing. In: Proceedings of the IEEE International Conference on Computers, Systems and Signal Processing, Bangalore. pp. 175–179 (1984)
Ekert, A.K.: Quantum cryptography based on bells theorem. Phys. Rev. Lett. 67(6), 661–663 (1991)
Bennett, C.H.: Quantum cryptography using any two nonorthogonal states. Phys. Rev. Lett. 68(21), 3121–3124 (1992)
Cabello, A.: Quantum key distribution in the Holevo limit. Phys. Rev. Lett. 85(26), 5635 (2000)
Hwang, W.Y.: Quantum key distribution with high loss: toward global secure communication. Phys. Rev. Lett. 91(5), 057901 (2003)
Li, X.H., Deng, F.G., Zhou, H.Y.: Efficient quantum key distribution over a collective noise channel. Phys. Rev. A. 78(2), 022321 (2008)
Zhang, C.M., Song, X.T., Treeviriyanupab, P., et al.: Delayed error verification in quantum key distribution. Chin. Sci. Bull. 59(23), 2825–2828 (2014)
Long, G.L., Liu, X.S.: Theoretically efficient high-capacity quantum-key-distribution scheme. Phys. Rev. A. 65(3), 032302 (2002)
Deng, F.G., Long, G.L., Liu, X.S.: Two-step quantum direct communication protocol using the Einstein- Podolsky-Rosen pair block. Phys. Rev. A. 68(4), 042317 (2003)
Gu, B., Huang, Y.G., Fang, X., Zhang, C.Y.: A two-step quantum secure direct communication protocol with hyperentanglement. Chin. Phys. B. 20(10), 100309 (2011)
Wang, J., Zhang, Q., Tang, C.J.: Quantum secure direct communication based on order rearrangement of single photons. Phys. Lett. A. 358(4), 256–258 (2006)
Hillery, M., Buzek, V., Berthiaume, A.: Quantum secret sharing. Phys. Rev. A. 59(3), 1829–1834 (1999)
Karlsson, A., Koashi, M., Imoto, N.: Quantum entanglement for secret sharing and secret splitting. Phys. Rev. A. 59(1), 162–168 (1999)
Cleve, R., Gottesman, D., Lo, H.K.: How to share a quantum secret. Phys. Rev. Lett. 83(3), 648–651 (1999)
Gottesman, D.: Theory of quantum secret sharing. Phys. Rev. A. 61(4), 042311 (2000)
Li, Y., Zhang, K., Peng, K.: Multiparty secret sharing of quantum information based on entanglement swapping. Phys. Lett. A. 324(5), 420–424 (2004)
Xiao, L., Long, G.L., Deng, F.G., et al.: Efficient multiparty quantum-secret-sharing schemes. Phys. Rev. A. 69(5), 052307 (2004)
Deng, F.G., Long, G.L., Zhou, H.Y.: An efficient quantum secret sharing scheme with Einstein-Podolsky- Rosen pairs. Phys. Lett. A. 340(1–4), 43–50 (2005)
Wang, T.Y., Wen, Q.Y., Chen, X.B., et al.: An efficient and secure multiparty quantum secret sharing scheme based on single photons. Opt. Commun. 281(24), 6130–6134 (2008)
Hao, L., Wang, C., Long, G.L.: Quantum secret sharing protocol with four state Grover algorithm and its proof-of-principle experimental demonstration. Opt. Commun. 284(14), 3639–3642 (2011)
Guo, G.P., Guo, G.C.: Quantum secret sharing without entanglement. Phys. Lett. A. 310(4), 247–251 (2003)
Markham, D., Sanders, B.C.: Graph states for quantum secret sharing. Phys. Rev. A. 78(4), 042309 (2008)
Keet, A., Fortescue, B., Markham, D., et al.: Quantum secret sharing with qudit graph states. Phys. Rev. A. 82(6), 062315 (2010)
Qin, H., Dai, Y.: Dynamic quantum secret sharing by using d-dimensional GHZ state. Quantum Inf. Process. 16(3), 64 (2017)
Boyer, M., Kenigsberg, D., Mor, T.: Quantum key distribution with classical bob. Phys. Rev. Lett. 99(14), 140501 (2007)
Boyer, M., Gelles, R., Kenigsberg, D., et al.: Semiquantum key distribution. Phys. Rev. A. 79(3), 032341 (2009)
Lu, H., Cai, Q.Y.: Quantum key distribution with classical Alice. Int. J. Quantum Inf. 6(6), 1195–1202 (2008)
Zhang, X.Z., Gong, W.G., Tan, Y.G., et al.: Quantum key distribution series network protocol with M-classical Bobs. Chin. Phys. B. 18(6), 2143–2148 (2009)
Tan, Y.G., Lu, H., Cai, Q.Y.: Comment on “Quantum key distribution with classical Bob”. Phys. Rev. Lett. 102(9), 098901 (2009)
Zou, X.F., Qiu, D.W., Li, L.Z., et al.: Semiquantum-key distribution using less than four quantum states. Phys. Rev. A. 79(5), 052312 (2009)
Boyer, M., Mor, T.: Comment on “Semiquantum-key distribution using less than four quantum states”. Phys. Rev. A. 83(4), 046301 (2011)
Wang, J., Zhang, S., Zhang, Q., et al.: Semiquantum key distribution using entangled states. Chin. Phys. Lett. 28(10), 100301 (2011)
Miyadera, T.: Relation between information and disturbance in quantum key distribution protocol with classical Alice. Int. J. Quantum Inf. 9(6), 1427–1435 (2011)
Krawec, W.O.: Restricted attacks on semi-quantum key distribution protocols. Quantum Inf. Process. 13(11), 2417–2436 (2014)
Yang, Y.G., Sun, S.J., Zhao, Q.Q.: Trojan-horse attacks on quantum key distribution with classical Bob. Quantum Inf. Process. 14(2), 681–686 (2015)
Yu, K.F., Yang, C.W., Liao, C.H., et al.: Authenticated semi-quantum key distribution protocol using Bell states. Quantum Inf. Process. 13(6), 1457–1465 (2014)
Krawec, W.O.: Mediated semiquantum key distribution. Phys. Rev. A. 91(3), 032323 (2015)
Zou, X.F., Qiu, D.W., Zhang, S.Y.: Semiquantum key distribution without invoking the classical party’s measurement capability. Quantum Inf. Process. 14(8), 2981–2996 (2015)
Li, Q., Chan, W.H., Zhang, S.Y.: Semiquantum key distribution with secure delegated quantum computation. Sci. Rep. 6, 19898 (2016)
Zou, X.F., Qiu, D.W.: Three-step semiquantum secure direct communication protocol. Sci. China Phys. Mech. Astron. 57(9), 1696–1702 (2014)
Luo, Y.P., Hwang, T.: Authenticated semi-quantum direct communication protocols using Bell states. Quantum Inf. Process. 15(2), 947–958 (2016)
Zhang, M.H., Li, H.F., Xia, Z.Q., et al.: Semiquantum secure direct communication using EPR pairs. Quantum Inf. Process. 16(5), 117 (2017)
Li, Q., Chan, W.H., Long, D.Y.: Semiquantum secret sharing using entangled states. Phys. Rev. A. 82(2), 022303 (2010)
Wang, J., Zhang, S., Zhang, Q., et al.: Semiquantum secret sharing using two-particle entangled state. Int. J. Quantum Inf. 10(5), 1250050 (2012)
Li, L.Z., Qiu, D.W., Mateus, P.: Quantum secret sharing with classical Bobs. J. Phys. A Math. Theor. 46(4), 045304 (2013)
Lin, J., Yang, C.W., Tsai, C.W., et al.: Intercept-resend attacks on semi-quantum secret sharing and the improvements. Int. J. Theor. Phys. 52(1), 156–162 (2013)
Yang, C.W., Hwang, T.: Efficient key construction on semi-quantum secret sharing protocols. Int. J. Quantum Inf. 11(5), 1350052 (2013)
Xie, C., Li, L.Z., Qiu, D.W.: A novel semi-quantum secret sharing scheme of specific bits. Int. J. Theor. Phys. 54(10), 3819–3824 (2015)
Yin, A., Fu, F.: Eavesdropping on semi-quantum secret sharing scheme of specific bits. Int. J. Theor. Phys. 55(9), 4027–4035 (2016)
Gao, G., Wang, Y., Wang, D.: Multiparty semiquantum secret sharing based on rearranging orders of qubits. Mod. Phys. Lett. B. 30(10), 1650130 (2016)
Tavakoli, A., Herbauts, I., Zukowski, M., et al.: Secret sharing with a single d-level quantum system. Phys. Rev. A. 92(3), 03030 (2015)
Ye, C.Q., Ye, T.Y.: Circular multi-party quantum private comparison with n-level single-particle states. Int. J. Theor. Phys. 58(4), 1282–1294 (2019)
Cai, Q.Y.: Eavesdropping on the two-way quantum communication protocols with invisible photons. Phys. Lett. A. 351(1–2), 23–25 (2006)
Deng, F.G., Zhou, P., Li, X.H., Li, C.Y., Zhou, H.Y.: Robustness of two-way quantum communication protocols against Trojan horse attack. arXiv: quant-ph/0508168 (2005)
Li, X.H., Deng, F.G., Zhou, H.Y.: Improving the security of secure direct communication based on the secret transmitting order of particles. Phys. Rev. A. 74, 054302 (2006)
Gisin, N., Ribordy, G., Tittel, W., Zbinden, H.: Quantum cryptography. Rev. Mod. Phys. 74(1), 145–195 (2002)
Gao, F., Qin, S.J., Wen, Q.Y., Zhu, F.C.: A simple participant attack on the Bradler-Dusek protocol. Quantum Inf. Comput. 7, 329 (2007)
Gao, F.Z., Wen, Q.Y., Zhu, F.C.: Comment on: “quantum exam”[Phys Lett A 350(2006)174]. Phys. Lett. A. 360(6), 748–750 (2007)
Guo, F.Z., Qin, S.J., Gao, F., Lin, S., Wen, Q.Y., Zhu, F.C.: Participant attack on a kind of MQSS schemes based on entanglement swapping. Eur. Phys. J. D. 56(3), 445–448 (2010)
Qin, S.J., Gao, F., Wen, Q.Y., Zhu, F.C.: Cryptanalysis of the Hillery-Buzek-Berthiaume quantum secret sharing protocol. Phys. Rev. A. 76(6), 062324 (2007)
Nie, Y.Y., Li, Y.H., Wang, Z.S.: Semi-quantum information splitting using GHZ-type states. Quantum Inf. Process. 12, 437–448 (2013)
Acknowledgments
Funding by the Natural Science Foundation of Zhejiang Province (Grant No.LY18F020007), the Public Welfare Project Foundation of Zhejiang Provincial Science and Technology Department (Grant No. LGG18F020006) and the Foundation of Zhejiang Provincial Education Department (Grant No. Y201737672) is gratefully acknowledged.
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher’s Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Chong-Qiang, Y., Tian-Yu, Y., De, H. et al. Multiparty Semi-Quantum Secret Sharing with d-Level Single-Particle States. Int J Theor Phys 58, 3797–3814 (2019). https://doi.org/10.1007/s10773-019-04248-8
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10773-019-04248-8
Keywords
- Semi-quantum cryptography
- Multiparty semi-quantum secret sharing (MSQSS)
- d-level single- particle states
- Measurement capability