Abstract
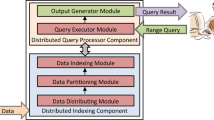
Access control is a fundamental component of any data management system, ensuring the prevention of unauthorized data access. Within the realm of data streams, it plays a crucial role in query processing by facilitating authorized access to them. This paper introduces the StreamFilter framework, which focuses on securely processing queries with range filters over streaming data. Leveraging the Role-Based Access Control model, the StreamFilter framework enables the specification of fine-grained access policies at various levels of granularity, such as tuples and attributes, through the utilization of a bit string structure. To enhance the search operation during data stream query processing, the framework employs a distributed indexing method, constructing a set of smaller B + Tree indices rather than a single large B + Tree index. Furthermore, it seamlessly integrates access authorization evaluation with query processing, efficiently filtering unauthorized parts from the query results. The experimental results demonstrate an approximately 50% increase in efficiency for processing queries with range filters compared to the post-filtering strategy. This improvement is observed across all types of data distribution, including uniform, skew, and hyper skew.












Similar content being viewed by others
Data availability
Enquiries about the source code and data availability should be directed to authors.
References
Margara, A., Rabl, T.: Definition of data streams. Encycl. Big Data Technol. (2019). https://doi.org/10.1007/978-3-319-77525-8_188
Bifet, A., Gama, J.: IoT data stream analytics. Ann. des Telecommun. Telecommun. 75(9–10), 491–492 (2020). https://doi.org/10.1007/s12243-020-00811-1
Tiwari, S., Agarwal, S.: Data stream management for CPS-based healthcare: a contemporary review. IETE Tech. Rev. (Institution Electron. Telecommun. Eng. India) 39(5), 987–1010 (2022). https://doi.org/10.1080/02564602.2021.1950578
Sumalatha, M.R., Ananthi, M.: Efficient data retrieval using adaptive clustered indexing for continuous queries over streaming data. Cluster Comput. 22(S5), 10503–10517 (2019). https://doi.org/10.1007/s10586-017-1093-z
Colombo, P., Ferrari, E.: Access control technologies for Big Data management systems: literature review and future trends. Cybersecurity (2019). https://doi.org/10.1186/s42400-018-0020-9
Qiu, J., Tian, Z., Du, C., Zuo, Q., Su, S., Fang, B.: A survey on access control in the age of internet of things. IEEE Internet Things J. 7(6), 4682–4696 (2020). https://doi.org/10.1109/JIOT.2020.2969326
Zaki, M., Lee, A.J., Chrysanthis, P.K.: Effective access control in shared-operator multi-tenant data stream management systems. In: Lecture Notes in Computer Science including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics, vol. 12122 LNCS, pp. 118–136. Springer, Cham (2020). https://doi.org/10.1007/978-3-030-49669-2_7
Rhujittawiwat, T., Saaudi, A., Farkas, C.: Stream Data Access Control Model: The Need for Data Semantics. In: International Joint Conference on Knowledge Discovery, Knowledge Engineering and Knowledge Management, IC3K - Proceedings, vol. 3, pp. 19–30. (2022) https://doi.org/10.5220/0011528600003335.
Carminati, B., Ferrari, E., Cao, J., Tan, K.L.: A framework to enforce access control over data streams. ACM Trans. Inf. Syst. Secur. (2010). https://doi.org/10.1145/1805974.1805984
Chakravarthy, S., Jiang, Q.: Stream Data Processing: A Quality of Service Perspective, vol. 36. Springer, Boston (2009). https://doi.org/10.1007/978-0-387-71003-7
Nehme, R.V., Lim, H.S., Bertino, E., Rundensteiner E.A.: StreamShield: A stream-centric approach towards security and privacy in data stream environments. In: SIGMOD-PODS’09—Proceedings of the International Conference on Management of Data and 28th Symposium on Principles of Database Systems, pp. 1027–1029. (2009) https://doi.org/10.1145/1559845.1559972.
Ma, C., Yan, Z., Chen, C.W.: Scalable access control for privacy-aware media sharing. IEEE Trans. Multimed. 21(1), 173–183 (2019). https://doi.org/10.1109/TMM.2018.2851446
Nehme, R.V., Rundensteiner, E.A., Bertino E.: A security punctuation framework for enforcing access control on streaming data. In: Proceedings—International Conference on Data Engineering, pp. 406–415. (2008). https://doi.org/10.1109/ICDE.2008.4497449.
Mirabi, M., Ibrahim, H., Fathi, L., Udzir, N.I., Mamat, A.: A dynamic compressed accessibility map for secure XML querying and updating. J. Inf. Sci. Eng. 31(1), 59–93 (2015). https://doi.org/10.1688/JISE.2015.31.1.4
Mirabi, M., Ibrahim, H., Udzir, N.I., Mamat, A.: A compact bit string accessibility map for secure XML query processing. Procedia Comput. Sci. 10, 1172–1179 (2012). https://doi.org/10.1016/j.procs.2012.06.169
Safaee, S., Mirabi, M., Rahmani, A.M., Safaei, A.A.: A distributed B+Tree indexing method for processing range queries over streaming data. Cluster Comput. (2023). https://doi.org/10.1007/s10586-023-04015-9
Lindner, W., Meier, J.: Securing the borealis data stream engine. In: Proceedings of the International Database Engineering and Applications Symposium, IDEAS, pp. 137–147. (2006). https://doi.org/10.1109/IDEAS.2006.40.
Carminati, B., Ferrari, E., Tan, K.L.: Enforcing access control over data streams. Proc. ACM Symp. Access Control Model Technol. Sacmat. (2007). https://doi.org/10.1145/1266840.1266845
B. Carminati, E. Ferrari, and L. T. Kian, “Specifying access control policies on data streams,” in Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics), vol. 4443 LNCS, Berlin, Heidelberg: Springer Berlin Heidelberg, 2007, pp. 410–421. doi: https://doi.org/10.1007/978-3-540-71703-4_36.
Cao, J., Carminati, B., Ferrari, E., Tan, K.L.: ACStream: enforcing access control over data streams. Proc. - Int. Conf. Data Eng. (2009). https://doi.org/10.1109/ICDE.2009.25
Streambase home page. http://www.streambase.com/.
Abadi, D.J., Carney, D., Çetintemel, U., Cherniack, M., Convey, C., Lee, S., Stonebraker, M., Tatbul, N., Zdonik, S.: Aurora: a new model and architecture for data stream management. VLDB J. 12(2), 120–139 (2003). https://doi.org/10.1007/s00778-003-0095-z
Nehme, R.V., Lim, H.S., Bertino, E.: FENCE: Continuous Access Control Enforcement in Dynamic Data Stream Environments In: ICDE, pp. 940–943. (2010). https://db.cs.pitt.edu/courses/cs3551/16-1/handouts/icde2010fence.pdf.
Nehme, R.V., Lim, H.S., Bertino, E.: FENCE: Continuous Access control enforcement in dynamic data stream environments. In: CODASPY 2013—Proceedings of the 3rd ACM Conference on Data and Application Security and Privacy, pp. 243–254. (2013). https://doi.org/10.1145/2435349.2435383.
Safaei, A.A.: Real-time processing of streaming big data. Real-Time Syst. 53(1), 1–44 (2017). https://doi.org/10.1007/s11241-016-9257-0
Deng, Z., Wu, X., Wang, L., Chen, X., Ranjan, R., Zomaya, A., Chen, D.: Parallel processing of dynamic continuous queries over streaming data flows. IEEE Trans. Parallel Distrib. Syst.Distrib. Syst. 26(3), 834–846 (2015). https://doi.org/10.1109/TPDS.2014.2311811
Lee, C.C., Chen, T.J., Wu, Y.H., Tsai, K.C., Yuan, A.: Spontaneous retropharyngeal emphysema and pneumomediastinum presented with signs of acute upper airway obstruction. Am. J. Emerg. Med. 23(3), 402 (2005)
Pollari-malmi, K.: B+trees. https://www.cs.helsinki.fi/u/mluukkai/tirak2010/B-tree.pdf.
Cormen, T.H., Leiserson, C.E., Rivest, R.L.: Introduction to Algorithms, fourth edition, 4th ed. The MIT Press, Cambridge (2022). https://mitpress.mit.edu/books/introduction-algorithms-fourth-edition.
Mishra, A.: Movielens dataset. Kaggle, 2020. https://grouplens.org/datasets/movielens/.
Funding
The authors have not disclosed any funding.
Author information
Authors and Affiliations
Contributions
All authors contributed to the study conception and design. The first draft of the manuscript was written by SS and MM, and then it was reviewed by AAS. All authors commented on previous versions of the manuscript. All authors read and approved the final manuscript.
Corresponding author
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Safaee, S., Mirabi, M. & Safaei, A.A. StreamFilter: a framework for distributed processing of range queries over streaming data with fine-grained access control. Cluster Comput (2024). https://doi.org/10.1007/s10586-024-04402-w
Received:
Revised:
Accepted:
Published:
DOI: https://doi.org/10.1007/s10586-024-04402-w