Abstract
A new Intrusion Detection System (IDS) for network security is proposed making use of a Vector-Based Genetic Algorithm (VBGA) inspired by evolutionary approaches. The novelty in the algorithm is to represent chromosomes as vectors and training data as matrices. This approach allows multiple pathways to calculate fitness function out of which one particular methodology is used and tested. The proposed method uses the overlap of the matrices with vector chromosomes for model building. The fitness of the chromosomes is calculated from the comparison of true and false positives in test data. The algorithm is flexible to train the chromosomes for one particular attack type or to detect the maximum number of attacks. The VBGA has been tested on two datasets (KDD Cup-99 and CTU-13). The proposed algorithm gives high detection rate and low false positives as compared to traditional Genetic Algorithm. A detailed comparative analysis is given of proposed VBGA with the traditional string-based genetic algorithm on the basis of accuracy and false positive rates. The results show that vector based genetic algorithm provides a significant improvement in detection rates keeping false positives at minimum.









Similar content being viewed by others
References
Gantz J, Reinsel D (2012) The digital universe in 2020: Big data, bigger digital shadows, and biggest growth in the far east. IDC iView: IDC Anal Fut 2007:1–16
Whitley D (1994) A genetic algorithm tutorial. Stat Comput 4(2):65–85
Srinivas M, Patnaik LM (1994) Genetic algorithms: A survey. Computer 27(6):17–26
Banković Z, Stepanović D, Bojanić S, Nieto-Taladriz O (2007) Improving network security using genetic algorithm approach. Comput Electr Eng 33(5):438–451
Li W (2004) Using genetic algorithm for network intrusion detection. In: Proceedings of the United States department of energy cyber security group, pp 1–8
De Castro LN, Timmis J (2002) Artificial immune systems: a new computational intelligence approach. Springer Science & Business Media
Dasgupta D, Attoh-Okine N (1997) Immunity-based systems: A survey. In: 1997 IEEE international conference on systems, man, and cybernetics, 1997. Computational cybernetics and simulation, vol 1. IEEE, pp 369–374
Om H, Kundu A (2012) A hybrid system for reducing the false alarm rate of anomaly intrusion detection system. In: 2012 1st International conference on recent advances in information technology (RAIT). IEEE, pp 131–136
Hean L, Shuguang W (2013) Research on false alarm rate of intrusion detection based on cloning immune method. Int J Adv Comput Technol 5:2
Patel A, Qassim Q, Wills C (2010) A survey of intrusion detection and prevention systems. Inf Manag Comput Secur 18(4):277–290
Gaidhane R, Vaidya C, Raghuwanshi M (2014) Survey: Learning techniques for intrusion detection system (ids)
Gharibian F, Ghorbani AA (2007) Comparative study of supervised machine learning techniques for intrusion detection. In: Fifth annual conference on communication networks and services research, 2007. CNSR’07. IEEE, pp 350– 358
Stolfo SJ, Fan W, Lee W, Prodromidis A, Chan PK (2000) Cost-based modeling for fraud and intrusion detection: results from the jam project. In: DARPA information survivability conference and exposition, 2000. DISCEX’00. Proceedings, vol 2. IEEE, pp 130– 144
Garcia S, Grill M, Stiborek J, Zunino A (2014) An empirical comparison of botnet detection methods. Comput Secur 45:100– 123
Chan PK, Lippmann RP (2006) Machine learning for computer security. J Mach Learn Res 7:2669–2672
Garcia-Teodoro P, Diaz-Verdejo J, Maciá-Fernández G, Vázquez E (2009) Anomaly-based network intrusion detection: techniques, systems and challenges. Comput Secur 28(1):18– 28
Davis L (1991) Handbook of genetic algorithms
Owais S, Snasel V, Kromer P, Abraham A (2008) Survey: using genetic algorithm approach in intrusion detection systems techniques. In: Computer information systems and industrial management applications, 2008. CISIM’08. 7th. IEEE, pp 300–307
Kim J, Bentley PJ, Aickelin U, Greensmith J, Tedesco G, Twycross J (2007) Immune system approaches to intrusion detection–a review. Nat Comput 6(4):413–466
Aickelin U, Bentley P, Cayzer S, Kim J, McLeod J (2003) Danger theory: The link between ais and ids? Artif Immune Syst 147–155
Aickelin U, Greensmith J (2007) Sensing danger: Innate immunology for intrusion detection. Inf Secur Tech Rep 12(4):218–227
Yang H, Li T, Hu X, Wang F, Zou Y (2014) A survey of artificial immune system based intrusion detection. Sci World J 2014
Devi S, Nagpal R (2012) Intrusion detection system using genetic algorithm-a review. Int J Comput Bus Ress
Dave MH, Sharma SD (2008) Improved algorithm for intrusion detection using genetic algorithm and snort
Siahmarzkooh AT, Tabarsa S, Nasab ZH, Sedighi F (2015) An optimized genetic algorithm with classification approach used for intrusion detection
Hoque MS, Mukit M, Bikas M, Naser A et al (2012) An implementation of intrusion detection system using genetic algorithm. arXiv:1204.1336
Jongsuebsuk P, Wattanapongsakorn N, Charnsripinyo C (2013) Real-time intrusion detection with fuzzy genetic algorithm. In: 2013 10th International conference on Electrical engineering/electronics, computer, telecommunications and information technology (ECTI-CON). IEEE, pp 1–6
Ireland E (2013) Intrusion detection with genetic algorithms and fuzzy logic. In: UMMC Sci senior seminar conference, pp 1–30
Kim DS, Nguyen H-N, Ohn S-Y, Park JS (2005) Fusions of ga and svm for anomaly detection in intrusion detection system. In: Advances in neural networks–ISNN 2005. Springer, pp 415– 420
Stein G, Chen B, Wu AS, Hua KA (2005) Decision tree classifier for network intrusion detection with ga-based feature selection. In: Proceedings of the 43rd annual southeast regional conference-volume 2. ACM, pp 136–141
Tsang C-H, Kwong S, Wang H (2007) Genetic-fuzzy rule mining approach and evaluation of feature selection techniques for anomaly intrusion detection. Pattern Recogn 40(9):2373–2391
Kannan A, Maguire GQ, Sharma A, Schoo P (2012) Genetic algorithm based feature selection algorithm for effective intrusion detection in cloud networks. In: 20112 IEEE 12th international conference on data mining workshops (ICDMW). IEEE, pp 416– 423
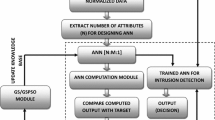
Dastanpour A, Ibrahim S, Mashinchi R (2014) Using genetic algorithm to supporting artificial neural network for intrusion detection system. In: The international conference on computer security and digital investigation (ComSec2014). The Society of Digital Information and Wireless Communication, pp 1–13
Aslahi-Shahri B, Rahmani R, Chizari M, Maralani A, Eslami M, Golkar M, Ebrahimi A (2015) A hybrid method consisting of ga and svm for intrusion detection system. Neural Comput Applic 1–8
Anil S, Remya R (2013) A hybrid method based on genetic algorithm, self-organised feature map, and support vector machine for better network anomaly detection. In: 2013 Fourth international conference on computing, communications and networking technologies (ICCCNT). IEEE, pp 1–5
Alazab M, Venkatraman S, Watters P, Alazab M (2011) Zero-day malware detection based on supervised learning algorithms of api call signatures. In: Proceedings of the Ninth Australasian data mining conference-volume 12. Australian Computer Society Inc., pp 171–182
Srinivasa K (2012) Application of genetic algorithms for detecting anomaly in network intrusion detection systems. In: Advances in computer science and information technology. Networks and communications. Springer, pp 582–591
Aziz ASA, Azar AT, Salama MA, Hassanien AE, Hanafy SE-O (2013) Genetic algorithm with different feature selection techniques for anomaly detectors generation. In: 2013 Federated conference on computer science and information systems (FedCSIS). IEEE, pp 769–774
Amiri F, Yousefi MR, Lucas C, Shakery A, Yazdani N (2011) Mutual information-based feature selection for intrusion detection systems. J Netw Comput Appl 34(4):1184–1199
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Ijaz, S., Hashmi, F.A., Asghar, S. et al. Vector Based Genetic Algorithm to optimize predictive analysis in network security. Appl Intell 48, 1086–1096 (2018). https://doi.org/10.1007/s10489-017-1026-9
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10489-017-1026-9