Abstract
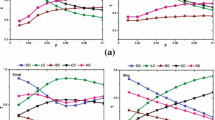
Key user identification for messages propagation constitutes one of the most important topics in social networks. The success of the information spreading depends on the selection of the key users. Besides the social attributes of users, the topology structure of the networks should be considered in this mechanism to ensure performance. In this paper, we propose the Social Attributes and Topology Structure (SATS) scheme for discovering key users in social networks. Firstly, the proposed SATS scheme utilizes four types of social attributes, and we extract the key social attributes. Then, we explore the feature of topology structure, in which social influence is defined and top-k influential users can be identified. Finally, the experiment results show that the proposed SATS scheme has effective propagation ability in the Susceptible Infected Recovered model, we can find the nodes which have more effects on network robustness while encountering the intentional attack by SATS scheme, and the proposed SATS scheme achieves better performance in identifying key users compared with some baseline approaches.



Similar content being viewed by others
References
Chen W, Wang Y, Yang S (2009) Efficient influence maximization in social networks. In: Proceedings of the 15th ACM SIGKDD international conference on Knowledge discovery and data mining, 199–208
Bian R, Koh YS, Doebbie G, Divoli A (2019) Identifying top-k nodes in social networks: a survey. ACM Comput Surv 52(1):1–33
Li Y, Fan J, Wang Y, Sellis T, Xia F (2018) Influence maximization on social graphs: a survey. IEEE Trans Knowl Data Eng 30(10):1852–1872
Kempe D, Kleinberg JM, Tardos E (2003) Maximizing the spread of influence through a social network. In: Proceedings of the 9th ACM SIGKDD conference on knowledge discovery and data mining, 137–146
Tang Y, Xiao X, Shi Y (2014) Influence maximization: near-optimal time complexity meets practical efficiency. In: Proceedings of the 2014 ACM SIGMOD international conference on management of data, 75–86
Yi X, Han Y, Wang X (2013) The evaluation of online social network’s nodes influence based on user’s attribute and behavior. Internet Conference of China (ICoC2013), 9–20
Gong Q, Chen Y, He X, Xiao Y, Hui P, Wang X, Fu X (2021) Cross-site prediction on social influence for cold-start users in online social networks. ACM Trans Web (TWEB) 15(2):1–23
Sheng J, Zhu J, Wang Y, Wang B, Hou Z (2020) Identifying influential nodes of complex networks based on trust-value. Algorithms 13(11):280–295
Banerjee S, Jenamani M, Pratihar DD (2020) A survey on influence maximization in a social network. Knowl Inform Syst 62(9):3417–3455
Zareie A, Sheikhahmadi A, Jalili M (2019) Identification of influential users in social networks based on users’ interest,. Inform Sci 493:217–231
Singh AK, Kailasam L (2021) Link prediction-based influence maximization in online social networks. Neurocomputing 453:151–163
Azaouzi M, Mnasri W, Romdhane LB (2021) New trends in influence maximization models. Comput Sci Rev 40:100393
Rui X, Meng F, Wang Z, Yuan G (2019) A reversed node ranking approach for influence maximization in social networks. Appl Intell 49(7):2684–2698
Wang C, Chen W, Wang Y (2012) Scalable influence maximization for independent cascade model in large-scale social networks. Data Min Knowl Discov 25(3):545–576
Newman MEJ (2010) Networks: an introduction. Oxford University Press, Oxford
Wang Y, Wang J, Wang H, Zhang R, Li M (2021) Users’ mobility enhances information diffusion in online social networks. Inform Sci 546:329–346
Chen D, Lu L, Shang M, Zhang Y, Zhou T (2012) Identifying influential nodes in complex networks. Phys A: Stat Mech Appl 391(4):1777–1787
Kirkley A, Barbosa H, Barthelemy M, Ghoshal G (2018) From the betweenness centrality in street networks to structural invariants in random planar graphs. Nature Commun 9(1):1–12
Aytac V, Turac T (2018) Closeness centrality in some splitting networks. Comput Sci J Moldova 26(3):251–269
Kitsak M, Gallos L, Havlin S, Liljeros F, Muchnik L, Stanley E, Makse H (2010) Identification of influential spreaders in complex networks. Nature Phys 6(11):888–893
Saleem M, Kumar R, Calders T (2019) Effective and efficient location influence mining in location-based social networks. Knowl Inform Syst 61(1):327–362
Page L (1998) The PageRank citation ranking: bringing order to the web,. Stanf Digit Libr Work Paper 9(1):1–14
Li X, Liu Y, Jiang Y, Liu X (2016) Identifying social influence in complex networks: a novel conductance eigenvector centrality model. Neurocomputing 210:141–154
Lu L, Zhang Y, Yeung C, Zhou T (2011) Leaders in social networks, the delicious case. PLOS One 6(6):21202–21213
Kleinberg J (1999) Authoritative sources in a hyberlinked environment. Struct Dyn Netw 46(5):604–632
Burt R (1992) Structure Holes: The Social Structure of Competition. Havard University Press, Cambridge
Lin Z, Zhang Y, Gong Q, Chen Y, Oksanen A, YiDing A(2022) Structural hole theory in social network analysis: a review. IEEE Trans Comput Soc Syst 9(3):724–739
Jafarzadehpour F, Molahosseini A, Zarandi A, Sousa L (2019) Efficient modular adder designs based on thermometer and one-hot coding. IEEE Trans Very Large Scale Integr Syst 99:1–14
Liu D, Jing Y, Zhao J, Wang W, Song G (2017) A fast and efficient algorithm for mining top-k nodes in complex networks. Sci Rep 7:43330
Zhang G, Cheng S, Shu J, Hu Q, Zheng W (2018) Accelerating breadth-first graph search on a single server by dynamic edge trimming. J Parallel Distrib Comput 120:383–394
Zachary W (1977) An information flow model for conflict and fission in small groups. J Anthropol Res 33:452–473
Xu Q, Qiu L, Lin R, Tang Y, He C, Yuan C (2021) “An improved community detection algorithm via fusing topology and attribute information. In: Proceedings of the 2021 IEEE 24th international conference on computer supported cooperative work in design
Ryan A, Nesreen K (2015) “The network data repository with interactive graph analytics and visualization,” http://networkrepository.com,
Cho E, Myers S, Leskovec J (2011) “Friendship and mobility: user movement in location-based social networks. In: ACM SIGKDD international conference on knowledge discovery and data mining (KDD), San Diego, pp. 1082–1090
Vragovic I, Louis E, Diaz G (2005) Efficiency of informational transfer in regular and complex networks. Phys Rev E 71(3):036122
Latora V, Marchiori M (2007) A measure of centrality based on network efficiency. New J Phys 9(6):188
Dereich S, Morters P (2013) Random networks with sublinear preferential attachment: the giant component. Ann Probab 41(1):329–384
Bedenknecht W, Mota G, Reiher C, Schacht M (2017) On the local density problem for graphs of given odd-girth. Electr Notes Discrete Math, 62:39–44
Ulrik B (2001) A faster algorithm for betweenness centrality. J Math Sociol 25(2):163–177
Acknowledgements
The authors would like to thank the National Natural Science Foundation of China (NOs. U1905211, 61771140, 62171132).
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Zhang, X., Gao, M., Xu, L. et al. Influence maximization based on SATS scheme in social networks. Computing 105, 275–292 (2023). https://doi.org/10.1007/s00607-022-01125-x
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s00607-022-01125-x