Abstract
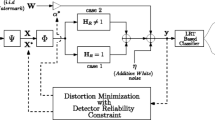
An improved detection model for spread spectrum image watermarking is developed assuming that compressive measurements of watermarked image are transmitted over multiple channels. A closed form expression of detection threshold in log-likelihood ratio model is derived followed by developing the two optimization problems. First one is to find the optimal number of compressed sensing measurements as the product of the number of channels and the number of samples per channel (bandwidth) under the constraint of a detection reliability and watermarked image power. The second one finds an optimal set of watermarked image measurements (that lead to watermarked image power) under the constraint of a detection reliability. Extensive simulation results are reported to highlight the efficacy of the watermark detector for both the optimization problems. An improvement of \(\sim \) 5.65% in detection performance is observed for 82.35% CS measurements and for a given probability of false alarm value 0.1 on multiplicative (fading) degradation having power 0.7.










Similar content being viewed by others
References
Ahmed F, Anees A, Abbas VU, Siyal MY (2014) A noisy channel tolerant image encryption scheme. Wirel Personal Commun 77(4):2771–2791
Bian Y, Liang S (2013) Image watermark detection in the wavelet domain using bessel k densities. IET Image Process 7(4):281–289
Bose A, Maity SP (2017) Spread spectrum watermark detection on degraded compressed sensing. IEEE Sens Lett 1:4
Bose A, Maity SP (2017) On robust watermark detection for optimum multichannel compressive transmission. In: Proceedings of computational intelligence, communications, and business analytics. Springer, Berlin
Bose A, Maity SP, Delpha C (2014) On improved spread spectrum watermark detection under compressive sampling. In: Proceedings of 5th European workshop on visual information processing (EUVIP). pp 1–6
Bose A, Maity SP (2016) Improved spread spectrum compressive image watermark detection with distortion minimization. In: International conference on signal processing and communications (SPCOM), IEEE. pp 1–5
Cox IJ, Kilian J, Leighton T, Shamoon T (1997) Secure spread spectrum watermarking for multimedia. IEEE Trans Image Process 6:1673–1687
Ding W, Lu Y, Yang F, Dai W, Li P, Liu S, Song J (2016) Spectrally efficient csi acquisition for power line communications: a Bayesian compressive sensing perspective. IEEE J Sel Areas Commun 34(7):2022–2032
Donoho DL, Tsaig Y, Drori I, Starck JL (2012) Sparse solution of underdetermined systems of linear equations by stagewise orthogonal matching pursuit. IEEE Trans Inf Theory 58(2):1094–1121
Goldsmith A (2005) Wireless communications. Cambridge University Press, Cambridge
Gonçalves D, Costa DG (2015) A survey of image security in wireless sensor networks. J Image 1(1):4–30
Gu ZF, Li GF, Yang ZX (2012) Study on digital image watermark algorithm based on chaos mapping and dwt. In: Proceedings of international conference on advanced mechatronic systems. pp 160–164
Huang HC, Chang FC, Wu CH, Lai WH (2012) Watermarking for compressive sampling applications. In: 2012 Eighth international conference on intelligent information hiding and multimedia signal processing. pp 223–226
Kong L, Zhang D, He Z, Xiang Q, Wan J, Tao M (2016) Embracing big data with compressive sensing: a green approach in industrial wireless networks. IEEE Commun Mag 54(10):53–59
Liu H, Xiao D, Zhang R, Zhang Y, Bai S (2016) Robust and hierarchical watermarking of encrypted images based on compressive sensing. Signal Process Image Commun 45:41–51
Ntranos V, Maddah-Ali MA, Caire G (2015) Cellular interference alignment. IEEE Trans Inf Theory 61(3):1194–1217
Pudlewski S, Melodia T (2013) A tutorial on encoding and wireless transmission of compressively sampled videos. IEEE Commun Surv Tutor 15(2):754–767
Qin Z, Liu Y, Gao Y, Elkashlan M, Nallanathan A (2017) Wireless powered cognitive radio networks with compressive sensing and matrix completion. IEEE Trans Commun 65(4):1464–1476
Rathore H, Mohamed A, Al-Ali A, Du X, Guizani M (2017) A review of security challenges, attacks and resolutions for wireless medical devices. In: 2017 13th international wireless communications and mobile computing conference (IWCMC), IEEE. pp 1495–1501
Tanchenko A (2014) Visual-psnr measure of image quality. J Visual Commun Image Represent 25(5):874–878
Tse D, Viswanath P (2005) Fundamentals of wireless communication. Cambridge University Press, Cambridge
Wang A, Lin F, Jin Z, Xu W (2016) A configurable energy-efficient compressed sensing architecture with its application on body sensor networks. IEEE Trans Ind Inf 12(1):15–27
Wang A, Zeng B, Chen H (2014) Wireless multicasting of video signals based on distributed compressed sensing. Signal Process Image Commun 29(5):599–606
Wang Q, Zeng W, Tian J (2014) A compressive sensing based secure watermark detection and privacy preserving storage framework. IEEE Trans Image Process 23(3):1317–1328
Wu H, Tao X, Han Z, Li N, Xu J (2017) Secure transmission in misome wiretap channel with multiple assisting jammers: maximum secrecy rate and optimal power allocation. IEEE Trans Commun 65(2):775–789
Xiang S, Cai L (2013) Transmission control for compressive sensing video over wireless channel. IEEE Trans Wirel Commun 12(3):1429–1437
Yu Y, Sun S, Madan RN, Petropulu A (2014) Power allocation and waveform design for the compressive sensing based mimo radar. IEEE Trans Aerosp Electron Syst 50(2):898–909
Zhou F, Beaulieu NC, Li Z, Si J, Qi P (2016) Energy-efficient optimal power allocation for fading cognitive radio channels: ergodic capacity, outage capacity, and minimum-rate capacity. IEEE Trans Wirel Commun 15(4):2741–2755
Author information
Authors and Affiliations
Corresponding author
Appendices
Appendix A
1.1 Parameter estimation of the detector
Let \(\mu _{\mathcal {H}_i}\) and \(\sigma _{\mathcal {H}_i}^2\) be the mean and the variance of \(t(\mathbf {Y})\) under \(\mathcal {H}_i~ (i=0,1)\). Then the detector distribution parameters are derived as,
Appendix B
1.1 Proof of \(E[\Vert \varvec{\Theta } \mathbf {P} \Vert _2^2]=\frac{LK}{N}\sigma _\mathbf {P}^2\)
Let \(\varvec{\Theta }\) be taken as \(\varvec{\Theta }=[\varvec{\phi }^1 \vdots \varvec{\phi }^2 \vdots \ldots \vdots \varvec{\phi }^L]^T\) and each \(\varvec{\phi }^i \in \mathcal {R}^{K\times N}\), thus the matrix \(\varvec{\Theta } \in \mathcal {R}^{LK\times N}\). The watermark \(\mathbf {P} \in \mathcal {R}^N\), thus the product \(\varvec{\Theta }\mathbf {P}\) is a vector in \(\mathcal {R}^{LK}\). Since each \(\varvec{\phi }^i \in \mathcal {N}(0,1/N)\), thus
Here,
Hence,
Rights and permissions
About this article
Cite this article
Bose, A., Maity, S.P. On robust watermark detection for optimum multichannel compressive transmission. Microsyst Technol 28, 485–497 (2022). https://doi.org/10.1007/s00542-018-3840-3
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s00542-018-3840-3