Abstract
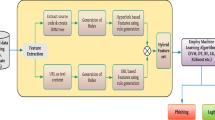
Almost all malwares running on web-server are php codes. Then, the present paper creates a next generation antivirus (NGAV) expert in auditing threats web-based, specifically from php files, in real time. In our methodology, the malicious behaviors, of the personal computer, serve as input attributes of the statistical learning machines. In all, our dynamic feature extraction monitors 11,777 behaviors that the web fileless attack can do when launched directly from a malicious web-server to a listening service in a personal computer. Our NGAV achieves an average 99.95% accuracy in the distinction between benign and malware web scripts. Distinct initial conditions and kernels of neural networks classifiers are investigated in order to maximize the accuracy of our NGAV. Our NGAV can supply the limitations of the commercial antiviruses as for the detection of Web fileless attack. In opposition of analysis of individual events, our engine employs authorial Web-server Sandbox, machine learning, and artificial intelligence in order to identify malicious Web-sites.





Similar content being viewed by others
Data availability
To make our work easier to understand, the machine learning repository is freely available in matlab and csv formats. Also, we make available all benign and malware samples.
Notes
malware (Malicious + Software)
Example of deep neural network architecture. Available at: https://se.mathworks.com/help/deeplearning/gs/create-simple-image-classification-network-using-deep-network-designer.html Accessed on June. 2021.
VirusShare is a repository of malware samples to provide security researchers, incident responders, forensic analysts, and the morbidly curious access to samples of live malicious code. Available at: https://virusshare.com/. Accessed on Nov. 2020.
phpMyAdmin: open source administration tool for MySQL. Available in: https://www.phpmyadmin.net/. Accessed on Nov. 2020.
Cuckoo: Automated Malware Analysis. Available in: https://cuckoosandbox.org/. Accessed on Nov. 2020.
URL: Uniform Resource Locator.
TCP: Transmission Control Protocol.
References
Abo-Hammour OAAZ (2014) Numerical solution of systems of second-order boundary value problems using continuous genetic algorithm. Inf Sci 279:396–415. https://doi.org/10.1016/j.ins.2014.03.128
Abu Arqub O, AL-Smadi MMS (2016) Numerical solutions of fuzzy differential equations using reproducing kernel hilbert space method. Soft Comput 20:3283–3302. https://doi.org/10.1007/s00500-015-1707-4
Arqub OA, Al-Smadi M (2020) Fuzzy conformable fractional differential equations: novel extended approach and new numerical solutions. Soft Comput 24:12501–12522. https://doi.org/10.1007/s00500-020-04687-0
Azevedo WW et al. (2015a) Fuzzy morphological extreme learning machines to detect and classify masses in mammograms. In: 2015 IEEE International conference on fuzzy systems (FUZZIEEE). Istanbul. https://doi.org/10.1109/FUZZ-IEEE.2015.7337975
Azevedo WW et al. (2015b) Morphological extreme learning machines applied to detect and classify masses in mammograms. In: 2015 International Joint Conference on Neural Networks (IJCNN). Killarney. https://doi.org/10.1109/IJCNN.2015.7280774
Azevedo WW et al. (2020) Morphological extreme learning machines applied to the detection and classification of mammary lesions. In: Tapan K Gandhi; Siddhartha Bhattacharyya; Sourav De; Debanjan Konar; Sandip Dey. (Org.). Advanced Machine Vision Paradigms for Medical Image Analysis. 1ed.Londres: Elsevier Science. , 1–30 https://doi.org/10.1016/B978-0-12-819295-5.00003-2
Ba L, Caurana R (2014) Do deep nets really need to be deep? Advances in neural information processing systems, 2654–2662
Chollet F (2017) Xception: Deep learning with depthwise separable convolutions. 2017 IEEE Conference on Computer Vision and Pattern Recognition (CVPR) https://doi.org/10.1109/CVPR.2017.195
CISCO (2018) CISCO 2018 Annual Cybersecurity Report. Accessed on Dec. 2020. https://www.cisco.com/c/dam/m/hu_hu/campaigns/security-hub/pdf/acr-2018.pdf
Conrad E, Misenar S, Feldman J (2017) Eleventh Hour CISSP (Certified Information Systems Security Professional). Syngress Publishing
Faruki P, Buddhadev B (2019) Droiddivesdeep: Android malware classification via low level monitorable features with deep neural networks. In: International conference on security & privacy. https://doi.org/10.1007/978-981-13-7561-3_10
Huang GB et al (2012) Extreme learning machine for regression and multiclass classification. IEEE Trans Syst Man Cybern 42(2):513–519. https://doi.org/10.1109/TSMCB.2011.2168604
IBM (2014) Explore the latest security trends–from malware delivery to mobile device risks–based on 2013 year-end data and ongoing research. Accessed on Dec. 2020
Intel (2018) McAfee Labs. Accessed on Feb 2020. https://www.mcafee.com/enterprise/en-us/assets/reports/rp-quarterly-threats-mar-2018.pdf
Lima S (2020) Limitation of COTS antiviruses: issues, controversies, and problems of COTS antiviruses. In: Cruz-Cunha MM, Mateus-Coelho NR (eds.) Handbook of Research on Cyber Crime and Information Privacy, vol. 1, 1st edn. IGI Global, Hershey. https://doi.org/10.4018/978-1-7998-5728-0.ch020
Lima S, Silva H, Luz J et al (2021) Artificial intelligence-based antivirus in order to detect malware preventively. Prog Artif Intell. https://doi.org/10.1007/s13748-020-00220-4
Lima S, Silva-Filho AG, Santos WP (2016) Detection and classification of masses in mammographic images in a multi-kernel approach. Comput Methods Programs Biomed 134:11–29. https://doi.org/10.1016/j.cmpb.2016.04.029
Lima SML, Silva-Filho, Santos WP (2020) Morphological Decomposition to Detect and Classify Lesions in Mammograms.In: Wellington Pinheiro dos Santos; Maíra Araújo de Santana; Washington Wagner Azevedo da Silva. (Org.). Understanding a Cancer Diagnosis. https://novapublishers.com/shop/understanding-a-cancer-diagnosis/
Lima SML, Silva-Filho AG, Dos Santos WP (2014) A methodology for classification of lesions in mammographies using zernike moments, elm and svm neural networks in a multi-kernel approach. In: 2014 IEEE International Conference on Systems, Man and Cybernetics SMC, San Diego https://doi.org/10.1109/SMC.2014.6974041
Maniath S, Ashok A (2017) Deep learning lstm based ransomware detection. Recent Dev Control Autom Power Eng. https://doi.org/10.1109/RDCAPE.2017.8358312
Microsoft (2013) Trustworthy Computing. Microsoft Computing Safety Index (MCSI)Worldwide Results Summary. Technical report
PAEMAL (2020) PAEMAL(PHP Analysis Environment Applied to Malware Machine Learning). Accessed on Dec. 2020. https://github.com/rewema/PAEMAL
PALOALTO (2013) PALOALTO 2013 The network security company. The Modern Malware Review. Analysis of New and Evasive Malware in Live Enterprise Networks. volume 1st Edition
Patterson DA, HJL, (2017) Computer Organization and Design. The Hardware/Software Interface, Fifth edition, Morgan Kaufmann
Pereira JMS et al (2020) Method for Classification of Breast Lesions in Thermographic Images Using ELM Classifiers. In: Wellington Pinheiro dos Santos; Maíra Araújo de Santana; Washington Wagner Azevedo da Silva. (Org.). Understanding a Cancer Diagnosis. https://novapublishers.com/shop/understanding-a-cancer-diagnosis/
SANS (2017) SANS Institute InfoSec Reading Room. Out with The Old, In with The New: Replacing Traditional Antivirus. Accessed on Feb 2020. https://www.sans.org/reading-room/whitepapers/analyst/old-new-replacing-traditional-antivirus-37377
SANTOS WP (2011) Mathematical morphology in digital document analysis and processing, vol 8. Nova Science, New York
Skybox (2018) Skybox Security vulnerability and threat trends report 2018. Analysis of current vulnerabilities, exploits and threats in play. Accessed on Dec. 2020. https://lp.skyboxsecurity.com/rs/skyboxsecurity/images/Skybox_Report_Vulnerability_Threat_Trends_18.pdf
Skycure (2016) Skycure mobile threat defense. Mobile Threat Intelligence Report Q1 2016. Accessed on Dec. 2020. https://www.symantec.com/content/dam/symantec/docs/reports/skycure-mobile-threat-intelligence-report-q1-2016-en.pdf
Sophos (2014) Sophos Security made simple. Security Threat Report 2014. Smarter, Shadier, Stealthier Malware. Accessed on Dec. 2020. https://www.sophos.com/en-us/medialibrary/pdfs/other/sophos-security-threat-report-2014.pdf
Su J, VASCONCELLOS D, t (2018) Lightweight classification of iot malware based on image recognition. 2018 IEEE 42nd Annual computer software and applications conference (COMPSAC) https://doi.org/10.1109/COMPSAC.2018.10315
Symantec (2012) Symantec Reports. Internet security threat report: 2001 Trends. volume 17. Published April 2012. Symantec Corporation
Symantec (2017) Symantec reports. internet security threat report: living off the land and fileless attack techniques. An ISTR Special Report
Wang Y, Qiu Y, Thai T, Moore K, Liu H, Zheng B (2017) A two-step convolutional neural network based computer-aided detection scheme for automatically segmenting adipose tissue volume depicting on ct images. Comput Methods Progr Biomed 144:97–104. https://doi.org/10.1016/j.cmpb.2017.03.017
Wozniak M, Silka J (2015) Recurrent neural network model for iot and networking malware threads detection. IEEE Trans Industr Inf. https://doi.org/10.1109/TII.2020.3021689
Xiang C, Ding SQ, Lee TH (2005) Geometrical interpretation and architecture selection of mlp. The IEEE Trans Neural Netw Learn Syst 16:84–96. https://doi.org/10.1109/TNN.2004.836197
Funding
This study is not financed.
Author information
Authors and Affiliations
Contributions
WS and WS conceived the presented idea of morphological extreme learning machine. WS developed the theoretical formalism and WS performed the implementation. RP, DS, and SS carried out the experiment. PL, RL, JO, TM constructed the dataset and validated the samples, SL wrote the manuscript with support from SF and EA. All authors discussed the results and contributed to the final manuscript and the interpretation of the results. All authors provided critical feedback and helped shape the research, analysis and manuscript.
Corresponding author
Ethics declarations
Conflict of interest
The authors declare that they have no conflict of interest.
Animal and human rights
The authors declare that no human participants were involved in this research.
Informed consent
This research did not include healthcare intervention of human participants.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Springer Nature or its licensor holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Lima, S.M.L., Silva, S.H.M.T., Pinheiro, R.P. et al. Next-generation antivirus endowed with web-server Sandbox applied to audit fileless attack. Soft Comput 27, 1471–1491 (2023). https://doi.org/10.1007/s00500-022-07447-4
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s00500-022-07447-4