Abstract
We prove an essentially tight lower bound on the unbounded-error communication complexity of every symmetric function, i.e., f(x,y)=D(|x∧y|), where D: {0,1,…,n}→{0,1} is a given predicate and x,y range over {0,1}n. Specifically, we show that the communication complexity of f is between Θ(k/log5 n) and Θ(k logn), where k is the number of value changes of D in {0,1,…, n}. Prior to this work, the problem was solved only for the parity predicate D (Forster 2001).
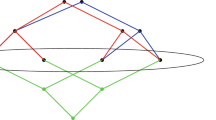
Our proof is built around two new ideas. First, we show that a predicate D gives rise to a rapidly mixing random walk on ℤ n2 , which allows us to reduce the problem to communication lower bounds for “typical” predicates. Second, we use Paturi’s approximation lower bounds (1992), suitably generalized here to clusters of real nodes in [0,n] and interpreted in their dual form, to prove that a typical predicate behaves analogous to the parity predicate with respect to a smooth distribution on the inputs.
Similar content being viewed by others
References
N. Alon, P. Frankl and V. Rödl: Geometrical realization of set systems and probabilistic communication complexity, in Proc. of the 26th Symposium on Foundations of Computer Science (FOCS), 277–280, 1985.
J. Aspnes, R. Beigel, M. L. Furst and S. Rudich: The expressive power of voting polynomials, Combinatorica 14(2) (1994), 135–148.
L. Babai, P. Frankl and J. Simon: Complexity classes in communication complexity theory, in Proc. of the 27th Symposium on Foundations of Computer Science (FOCS), 337–347, 1986.
Z. Bar-Yossef, T. S. Jayram, R. Kumar and D. Sivakumar: An information statistics approach to data stream and communication complexity, J. Comput. Syst. Sci. 68(4) (2004) 702–732.
H. Buhrman, N. K. Vereshchagin and R. de Wolf: On computation and communication with small bias, in Proc. of the 22nd Conf. on Computational Complexity (CCC), 24–32, 2007.
V. Feldman, P. Gopalan, S. Khot and A. K. Ponnuswami: New results for learning noisy parities and halfspaces, in Proceedings of the 47th Annual Symposium on Foundations of Computer Science (FOCS), 563–574, 2006.
J. Forster: A linear lower bound on the unbounded error probabilistic communication complexity. J. Comput. Syst. Sci., 65(4) (2002), 612–625.
J. Forster, M. Krause, S. V. Lokam, R. Mubarakzjanov, N. Schmitt and H.-U. Simon: Relations between communication complexity, linear arrangements computational complexity, in Proc. of the 21st Conf. on Foundations of Software Technology and Theoretical Computer Science (FST TCS), 171–182, 2001.
J. Forster and H. U. Simon: On the smallest possible dimension and the largest possible margin of linear arrangements representing given concept classes, Theor. Comput. Sci., 350(1) (2006), 40–48.
M. Goldmann, J. Håstad and A. A. Razborov: Majority gates vs. general weighted threshold gates, Computational Complexity, 2 (1992), 277–300.
A. Hajnal, W. Maass, P. Pudlák, M. Szegedy and G. Turán: Threshold circuits of bounded depth, J. Comput. Syst. Sci., 46(2) (1993), 129–154.
S. Jukna: Extremal combinatorics with applications in computer science, Springer-Verlag, Berlin, 2001.
B. Kalyanasundaram and G. Schnitger: The probabilistic communication complexity of set intersection. SIAM J. Discrete Math., 5(4) (1992), 545–557.
B. S. Kashin and A. A. Razborov: Improved lower bounds on the rigidity of Hadamard matrices, Matematicheskie zametki, 63(4) (1998), 535–540. In Russian.
M. Kearns and L. Valiant: Cryptographic limitations on learning Boolean formulae and finite automata, J. ACM, 41(1) (1994), 67–95.
M. Kharitonov: Cryptographic hardness of distribution-specific learning, in Proc. of the 25th Symposium on Theory of Computing, 372–381, 1993.
H. Klauck, R. Špalek and R. de Wolf: Quantum and classical strong direct product theorems and optimal time-space tradeoffs, SIAM J. Comput., 36(5) (2007), 1472–1493.
A. R. Klivans and R. A. Servedio: Learning DNF in time \(2^{\tilde O(n^{1/3} )}\), J. Comput. Syst. Sci., 68(2) (2004), 303–318.
A. R. Klivans and A. A. Sherstov: A lower bound for agnostically learning disjunctions, in Proc. of the 20th Conf. on Learning Theory (COLT), 409–423, 2007.
A. R. Klivans and A. A. Sherstov: Unconditional lower bounds for learning intersections of halfspaces, Machine Learning, 69(2–3) (2007), 97–114.
A. R. Klivans and A. A. Sherstov: Cryptographic hardness for learning intersections of halfspaces, J. Comput. Syst. Sci., 75(1) (2009), 2–12.
E. Kushilevitz and N. Nisan: Communication complexity, Cambridge University Press, New York, 1997.
S. V. Lokam: Spectral methods for matrix rigidity with applications to size-depth trade-offs and communication complexity, J. Comput. Syst. Sci., 63(3) (2001), 449–473.
M. L. Minsky and S. A. Papert: Perceptrons: An Introduction to Computational Geometry, MIT Press, Cambridge, Mass., 1969.
I. Newman: Private vs. common random bits in communication complexity, Inf. Process. Lett., 39(2) (1991), 67–71.
N. Nisan: The communication complexity of threshold gates, in Combinatorics, Paul Erdős is Eighty, 301–315, 1993.
R. Paturi: On the degree of polynomials that approximate symmetric Boolean functions, in Proc. of the 24th Symposium on Theory of Computing (STOC), 468–474, 1992.
R. Paturi and J. Simon: Probabilistic communication complexity. J. Comput. Syst. Sci., 33(1) (1986), 106–123.
R. Raz: Fourier analysis for probabilistic communication complexity, Comput. Complex., 5(3/4) (1995), 205–221.
A. A. Razborov: Bounded-depth formulae over the basis {&,⊕} and some combinatorial problems, Complexity Theory and Applied Mathematical Logic, vol. “Problems of Cybernetics” (1988), 146–166. In Russian.
A. A. Razborov: On the distributional complexity of disjointness, Theor. Comput. Sci., 106(2) (1992), 385–390.
A. A. Razborov: Quantum communication complexity of symmetric predicates, Izvestiya: Mathematics, 67(1) (2003), 145–159.
A. A. Razborov and A. A. Sherstov: The sign-rank of AC0, in Proc. of the 49th Symposium on Foundations of Computer Science (FOCS), 57–66, 2008.
T. J. Rivlin: An Introduction to the Approximation of Functions, Dover Publications, New York, 1981.
A. A. Sherstov: Powering requires threshold depth 3, Inf. Process. Lett., 102(2–3) (2007), 104–107.
A. A. Sherstov: Halfspace matrices. Comput. Complex., 17(2) (2008), 149–178. Preliminary version in 22nd CCC, 2007.
A. A. Sherstov: The pattern matrix method, SIAM J. Comput., 2010, To appear. Preliminary version in 40th STOC, 2008.
A. A. Sherstov: Separating AC0 from depth-2 majority circuits, SIAM J. Comput., 38(6) (2009), 2113–2129. Preliminary version in 39th STOC, 2007.
Y. Shi and Y. Zhu: Quantum communication complexity of block-composed functions, Quantum Information & Computation, 9(5–6) (2009), 444–460.
L. G. Valiant: A theory of the learnable, Commun. ACM, 27(11) (1984), 1134–1142.
R. de Wolf: Quantum computing and communication complexity, PhD thesis, University of Amsterdam, 2001.
Author information
Authors and Affiliations
Corresponding author
Additional information
An extended abstract of this article appeared in Proceedings of the 49th IEEE Symposium on Foundations of Computer Science (FOCS), pages 384–393, 2008.
Rights and permissions
About this article
Cite this article
Sherstov, A.A. The unbounded-error communication complexity of symmetric functions. Combinatorica 31, 583–614 (2011). https://doi.org/10.1007/s00493-011-2580-0
Received:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s00493-011-2580-0