Abstract
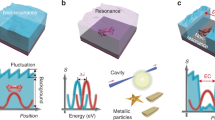
We propose a novel method for observing and utilizing nanometrically fluctuating signals due to optical near-field interactions between a probe and target in near-field optical microscopy. Based on a hierarchical structure of the interactions, it is possible to obtain signals that represent two-dimensional spatial patterns without requiring any scanning process. Such signals reveal individual features of each target, and these features, when appropriately extracted and defined, can be used in security applications—an approach that we call nanophotonic security. As an experimental demonstration, output signals due to interactions between a SiO2 probe and Al nanorods were observed by using near-field optical microscopy at a single readout point, and these signals were quantitatively evaluated using an algorithm that we developed for extracting and defining features that can be used for security applications.





Similar content being viewed by others
References
R.L. van Renesse, Optical Document Security (Artech, Morristown, 1994)
H. Matsumoto, T. Matsumoto, IPSJ J. 44, 1991–2001 (2003)
D. Lim, J.W. Lee, B. Gassend, G.E. Suh, M. van Dijk, S. Devadas, IEEE T. VLSI Syst. 13, 1200–1205 (2005)
G. DeJean, K. Darko, Lect. Notes Comput. Sci. 4727, 346–363 (2007)
J.D. Buchanan, R.P. Cowburn, A.V. Jausovec, D. Petit, P. Seem, G. Xiong, M.T. Bryan, Nature 436, 475 (2005)
M. Yamakoshi, J. Tanaka, M. Furuie, M. Hirabayashi, T. Matsumoto, Proc. SPIE 6819, 68190H-1–68190H-10 (2008)
T. Ikeda, S. Hiroe, T. Yamada, T. Matsumoto, Y. Takemura, 3rd International Conference on Anti-counterfeiting, Security, and Identification in Communication 2009, pp. 382–385 (2009)
R. Pappu, B. Recht, J. Taylor, N. Gershenfeld, Science 297, 2026–2030 (2002)
T. Matsumoto, in Proceedings of the IEICE Symposium on Cryptography and Information Security, SCIS 97-19C (1997)
K. Kobayashi, S. Sangu, H. Ito, M. Ohtsu, Near-field optical potential for a neutral atom. Phys. Rev. A 63, 013806 (2001)
M. Ohtsu, K. Kobayashi, Optical Near Fields (Springer, Berlin, 2004)
Y. Tanaka, K. Kobayashi, Spatial localization of an optical near field in one-dimensional nanomaterial system. Phys. E 40(2), 297–300 (2007)
M. Ohtsu, Dressed Photons—Concepts of Light-Matter Fusion Technology (Springer, Berlin, 2013)
M. Naruse, H. Hori, K. Kobayashi, M. Ishikawa, K. Leibnitz, M. Murata, N. Tate, M. Ohtsu, J. Opt. Soc. Am. B 26(9), 1772–1779 (2009)
E. Candès, J. Romberg, T. Tao, IEEE Trans. Inf. Theory 52, 489–509 (2006)
D. Donoho, IEEE Trans. Inf. Theory 52, 1289–1306 (2006)
J. Haupt, R. Nowak, IEEE Trans. Inf. Theory 52, 4036–4048 (2006)
E. Rosten, T. Drummond, in European Conference on Computer Vision, pp. 430–443 (2006)
C. Harris, M. Stephens, in Alvey Vision Conference, pp. 147–151 (1988)
S.M. Smith, J.M. Brady, Int. J. Comput. Vision 23, 45–78 (1997)
D.G. Lowe, in International Conference on Computer Vision, pp. 1150–1157 (1999)
Y. Pihosh, I. Turkevych, J. Ye, M. Goto, A. Kasahara, M. Kondo, M. Tosa, ECS Trans. 16(5), 49–58 (2009)
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Tate, N., Naruse, M., Matsumoto, T. et al. Non-scanning optical near-field microscopy for nanophotonic security. Appl. Phys. A 121, 1383–1387 (2015). https://doi.org/10.1007/s00339-015-9387-6
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s00339-015-9387-6