Abstract
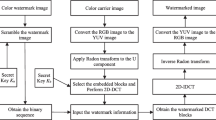
In the present digital scenario, false ownership claims and tampering with digital data have become serious concerns for users. There have been a very few schemes proposed in the past that can provide solutions for the three major requirements (ownership proof, tamper detection and self-recovery) in an efficient way. This paper presents a blind multipurpose image watermarking scheme for copyright/ownership protection, image authentication, and image restoration. Two different watermarking strategies (robust and fragile) are used to achieve the multipurpose nature. For Robust watermark insertion, an encrypted watermark is inserted into the host image using IWT (Integer wavelet transform). Afterward, a 9-base notation-based least significant bit replacement approach is used to embed the fragile sequence along with recovery information in a controlled randomized manner. During the testing phase, high imperceptibility, decent robustness, and good self-recovery are noticed against different types of attack. The scheme provides nearly 99.8% accurate tamper localization and can significantly recover even a severely tampered (up to 80%) image. The performance comparison with other existing watermarking schemes confirms the superiority of the proposed scheme. The multipurpose nature of the scheme makes it versatile and practical for the current scenario of digital technologies and era of internet.





Similar content being viewed by others
Data Availability
The dataset used is publicly available on the internet.
Code Availability
The code will be made available on reasonable demand.
References
I.A. Ansari, M. Pant, C.W. Ahn, SVD based fragile watermarking scheme for tamper localization and self-recovery. Int. J. Mach. Learn. Cybern. 7(6), 1225–1239 (2016)
I.A. Ansari, M. Pant, Multipurpose image watermarking in the domain of DWT based on SVD and ABC. Pattern Recogn. Lett. 94, 228–236 (2017)
S. Avila, M.N. Miyatake, Multipurpose image watermarking scheme based on self-embedding and data hiding into halftone image. in 2010 IEEE Electronics, Robotics and Automotive Mechanics Conference (IEEE, Cuernavaca, Mexico, 2010), pp. 394–398
R. Barnett, Digital watermarking: applications, techniques and challenges. Electron. Commun. Eng. J. 11(4), 173–183 (1999)
I. Cox, M. Miller, J. Bloom, J. Fridrich, T. Kalker, Digital Watermarking and Steganography (Morgan kaufmann, 2007)
N. Daneshmandpour, H. Danyali, M.S. Helfroush, Image tamper detection and multi-scale self-recovery using reference embedding with multi-rate data protection. China Commun. 16(11), 154–166 (2019)
B. Haghighi, A.H. Taherinia, A. Harati, M. Rouhani, WSMN: an optimized multipurpose blind watermarking in Shearlet domain using MLP and NSGA-II. Appl. Soft Comput. 101, 107029 (2021). https://doi.org/10.1016/j.asoc.2020.107029
A. Hore, D. Ziou, Image quality metrics: PSNR vs. SSIM. in 2010 20th International Conference on Pattern Recognition (IEEE, Istanbul, Turkey, 2010), pp. 2366–2369
Image databases, Accessed: May 2021. [Online]. Available: http://www.imageprocessingplace.com/root_files_V3/image_databases.htm
M. Islam, R.H. Laskar, Geometric distortion correction based robust watermarking scheme in LWT-SVD domain with digital watermark extraction using SVM. Multimed. Tools Appl. 77(11), 14407–14434 (2018)
M. Islam, A. Roy, R.H. Laskar, SVM-based robust image watermarking technique in LWT domain using different sub-bands. Neural Comput. Appl. 32(5), 1379–1403 (2020)
M. Jagannatam, Twister–A Pseudo Random Number Generator and Its Variants (George Mason University, Department of Electrical and Computer Engineering, 2008)
S. Lee, C.D. Yoo, T. Kalker, Reversible image watermarking based on integer-to-integer wavelet transform. IEEE Trans. Inf. Forensics Secur. 2(3), 321–330 (2007)
M. Li, Q. Liu, Steganalysis of SS steganography: hidden data identification and extraction. Circuits Syst. Signal Process. 34(10), 3305–3324 (2015)
X.L. Liu, C.C. Lin, S.M. Yuan, Blind dual watermarking for color images’ authentication and copyright protection. IEEE Trans. Circuits Syst. Video Technol. 28(5), 1047–1055 (2016)
S. Lu, H.Y. Liao, Multipurpose watermarking for image authentication and protection. IEEE Trans. Image Process. 10(10), 1579–1592 (2001)
R. Mehta, N. Rajpal, V.P. Vishwakarma, LWT-QR decomposition based robust and efficient image watermarking scheme using Lagrangian SVR. Multimed. Tools Appl. 75(7), 4129–4150 (2016)
I. Podilchuk, E.J. Delp, Digital watermarking: algorithms and applications. IEEE Signal Process. Mag. 18(4), 33–46 (2001)
C. Qin, P. Ji, C.C. Chang, J. Dong, X. Sun, Non-uniform watermark sharing based on optimal iterative BTC for image tampering recovery. IEEE Multimed. 25(3), 36–48 (2018)
V. Rajput, I.A. Ansari, Image tamper detection and self-recovery using multiple median watermarking. Multimed. Tools Appl. 79(47), 35519–35535 (2020)
M. Saito, M. Matsumoto, Variants of Mersenne twister suitable for graphic processors. ACM Trans. Math. Softw. 39(2), 1–20 (2013)
M. Saito, M. Matsumoto, SIMD-oriented fast Mersenne Twister: a 128-bit pseudorandom number generator. in Monte Carlo and Quasi-Monte Carlo Methods 2006 (Springer, Berlin, 2008), pp. 607–622. https://doi.org/10.1007/978-3-540-74496-2_36
J. Seitz, Digital watermarking for digital media. IGI Global (2005). https://doi.org/10.4018/978-1-59140-518-4
P. Singh, S. Agarwal, A self recoverable dual watermarking scheme for copyright protection and integrity verification. Multimed. Tools Appl. 76(5), 6389–6428 (2017)
S.K. Singh, Block truncation coding based effective watermarking scheme for image authentication with recovery capability. Multimed. Tools Appl. 78(4), 4197–4215 (2019)
R. Sinhal, I.A. Ansari, C.W. Ahn, Blind image watermarking for localization and restoration of color images. IEEE Access 8, 200157–200169 (2020)
N. Tarhouni, M. Charfeddine, C.B. Amar, Novel and robust image watermarking for copyright protection and integrity control. Circuits Syst. Signal Process. 39(10), 5059–5103 (2020)
X. Tong, Y. Liu, M. Zhang, Y. Chen, A novel chaos-based fragile watermarking for image tampering detection and self-recovery. Signal Process. Image Commun. 28(3), 301–308 (2013)
S.H. Wang, Y.P. Lin, Wavelet tree quantization for copyright protection watermarking. IEEE Trans. Image Process. 13(2), 154–165 (2004)
M. Wu, B. Liu, Watermarking for image authentication. in Proceedings 1998 International Conference on Image Processing. ICIP98 (Cat. No. 98CB36269) (IEEE, USA, 1998), vol. 2, pp. 437–441. https://doi.org/10.1109/ICIP.1998.723413
Wu, J. Zhang, W. Deng, D. He, Arnold transformation algorithm and anti-Arnold transformation algorithm. in 2009 First International Conference on Information Science and Engineering (IEEE, Nanjing, 2009), pp. 1164–1167. https://doi.org/10.1109/ICISE.2009.347
X. Zhang, S. Wang, Fragile watermarking with error-free restoration capability. IEEE Trans. Multimed. 10(8), 1490–1499 (2008)
X. Zhang, S. Wang, Z. Qian, G. Feng, Reference sharing mechanism for watermark self-embedding. IEEE Trans. Image Process. 20(2), 485–495 (2010)
X. Zhang, Z. Qian, Y. Ren, G. Feng, Watermarking with flexible self-recovery quality based on compressive sensing and compositive reconstruction. IEEE Trans. Inf. Forensics Secur. 6(4), 1223–1232 (2011)
X. Zhu, A.T. Ho, P. Marziliano, A new semi-fragile image watermarking with robust tampering restoration using irregular sampling. Signal Process. Image Commun. 22(5), 515–528 (2007)
Y.Q. Zou, Z. Shi, W. Ni, Su, A semi-fragile lossless digital watermarking scheme based on integer wavelet transform. IEEE Trans. Circuits Syst. Video Technol. 16(10), 1294–1300 (2006)
Funding
Not applicable.
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of interest
There is no conflict of interest.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Sinhal, R., Ansari, I.A. Multipurpose Image Watermarking: Ownership Check, Tamper Detection and Self-recovery. Circuits Syst Signal Process 41, 3199–3221 (2022). https://doi.org/10.1007/s00034-021-01926-z
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s00034-021-01926-z