Abstract
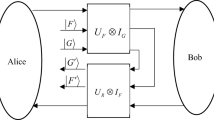
We discuss the security of the kind of multiparty quantum secret sharing protocols encrypting in series. It is secure against the eavesdroppers outside. However it is weak to withstand the attack of insider with a fake signal and cheating. An idiographic attack strategy is given based on the protocol. Furthermore, we conclude the key leak of the protocols and present a possible way to prevent the dishonest agents from stealing the secret.
Similar content being viewed by others
References
Shamir A. How to Share a Secret [J].Communications of the ACM, 1979,22(11):612–613.
Blakley G R. Safeguarding Cryptographic Keys [C]//Proceedings of the National Computer Conference. New York: AFIPS Press, 1979:313–317.
Hillery M, Buzek V, Berthiaume A. Quantum Secret Sharing [J].Phys Rev A, 1999,59:1829–1834.
Karlsson A, Koashi M, Imoto N. Quantum Entanglement for Secret Sharing and Secret Splitting [J].Phys Rev A, 1999,59:162–168.
Cleve R, Gottesman D, Lo H K. How to Share a Quantum Secret [J].Phys Rev Lett, 1999,83:648–651.
Gottesman D. Theory of Quantum Secret Sharing [J].Phys Rev A, 2000,61:42311.
Guo G P, Guo G C. Quantum Secret Sharing Without Entanglement [J].Phys Lett A, 2003,310:247–251.
Lance A M, Symul T, Bowen W P,et al. Tripartite Quantum State Sharing [J].Phys Rev Lett, 2004,92:177903.
Qin S J, Liu T L, Wen Q Y. Quantum Secret Sharing Based on Entanglement Swapping and Local Operation [J].Journal of Beijing University of Posts and Telecommunications, 2005,28(4):74–77 (Ch).
Qin S J, Wen Q Y, Zhu F C. A Ring Quantum Secret Sharing Protocol Based on Entanglement Swapping of Bell States [J].Journal of Beijing University of Posts and Telecommunications, 2006,29(2):34–37 (Ch).
Xiao L, Long G L, Deng F G,et al. Efficient Multiparty Quantum-Secret-Sharing Schemes [J].Phys Rev A, 2004,69:52307.
Li Y M, Zhang K S, Peng K C. Multiparty Secret Sharing of Quantum Information Based on Entanglement Swapping [J].Phys Lett A, 2004,324:420–424.
Tokunaga Y, Okamoto T, Imoto N. Threshold Quantum Cryptography [J].Phys Rev A, 2005,71:12314.
Zhang Z J, Li Y, Man Z X. Multiparty Quantum Secret Sharing [J].Phys Rev A, 2005,71:44301.
Deng F G, Li X H, Zhou H Y,et al. Improving the Security of Multiparty Quantum Secret Sharing against Trojan Horse Attack [J].Phys Rev A, 2005,72:44302.
Yan F L, Gao T. Quantum Secret Sharing between Multiparty and Multiparty without Entanglement [J].Phys Rev A, 2005,72:12304.
Zhang Z J. Multiparty Quantum Secret Sharing of Secure Direct Communication [J].Phys Lett A, 2005,342:60–66.
Deng F G, Li X H, Li C Y,et al. Multiparty Quantum Secret Splitting and Quantum State Sharing [J].Phys Lett A, 2006,354:190–195.
Deng F G, Long G L, Liu X S. Two-Step Quantum Direct Communication Protocol Using the Einstein-Podolsky-Rosen Pair Block [J].Phys Rev A, 2003,68:42317.
Deng F G, Long G L. Secure Direct Communication with a Quantum One-Time Pad [J].Phys Rev A, 2004,69: 52319.
Bennett C H, Brassard G. Quantum Cryptography: Public-Key Distribution and Coin Tossing [C].Proceedings of the International Conference on Computers, Systems and Signal Processing. New York: Bangalore Press, 1984:175–179.
Author information
Authors and Affiliations
Corresponding author
Additional information
Foundation item: Supported by the Major Research Plan of the National Natural Science Foundation of China (90604023), the National Natural Science Foundation of China (60373059), the National Research Foundation for the Doctoral Program of Higher Education of China (20040013007), the National Laboratory for Modern Communications Science Foundation of China (9140C1101010601) and the Graduate Students Innovation Foundation and the Integrated Service Networks Open Foundation
Biography: QIN Sujuan (1979-), female, Ph.D. candidate, research direction: quantum eryptography.
Rights and permissions
About this article
Cite this article
Sujuan, Q., Qiaoyan, W. & Fuchen, Z. Eavesdropping on the orderly-encrypting multiparty quantum secret sharing protocols. Wuhan Univ. J. Nat. Sci. 11, 1593–1596 (2006). https://doi.org/10.1007/BF02831828
Received:
Issue Date:
DOI: https://doi.org/10.1007/BF02831828