Abstract
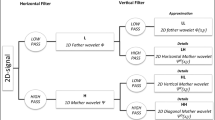
With the rapid development of communication technology and multimedia technology, digital watermark has played an important role in the protection of various forms of digital media works. In this paper, digital watermarking algorithms of wavelet domain are studied. Firstly, we apply discrete wavelet transform with different levels on the host images and combine them with corresponding discrete cosine transform. Next, we introduce the spread transform quantization index modulation algorithm to implement the watermark embedding. Then, we propose orthogonal matching pursuit compression reconstruction algorithm for the watermarking algorithm to optimize the watermark extraction through denoising-attacked watermarked images. We conduct several experiments and compare performance of different algorithms using statistical parameters such as peak signal-to-noise ratio and bit error rate. The experiments and comparisons prove the effectiveness of the proposed algorithms.









Similar content being viewed by others
References
A. Akter, Nur-E-Tajnina, A.U. Muhammad, Digital image watermarking based on DWT–DCT: evaluate for a new embedding algorithm, in 2014 International Conference on Informatics Electronics and Vision (ICIEV) (2014)
O. Benrhouma, O. Mannai, H. Hermassi, Digital images watermarking and partial encryption based on DWT transformation and chaotic maps, in IEEE 12th International Multi-Conference on Systems, Signals and Devices (SSD15) (2015), pp. 1–6
E.J. Candès, Compressive sampling, in Proceedings of the International Congress of Mathematicians (2006), pp. 1433–1452
B. Chen, G.W. Wornell, Quantization index modulation: a class of provably good methods for digital watermarking and information embedding. IEEE Trans. Inf. Theory 47(4), 1423–1443 (2001)
C. Das, S. Panigrahi, V.K. Sharma, K.K. Mahapatra, A novel blind robust image watermarking in DCT domain using inter-block coefficient correlation. AEU-Int. J. Electron. Commun. 68(3), 244–253 (2014)
K. Deb, M.S. Al-Seraj, M.M. Hoque, M.I.H. Sarkar, Combined DWT–DCT based digital image watermarking technique for copyright protection, in The seventh International Conference on Electrical and Computer Engineering (2012), pp: 458–461
D.L. Donoho, Compressed sensing. IEEE Trans. Inf. Theory 52(4), 1289–1306 (2006)
M.F.M. El Bireki, M.F.L. Abdullah, A.A.M. Ukasha, A.A. Elrowayati, Digital image watermarking based on joint (DCT–DWT) and arnold transform. Int. J. Secur. Appl. 10(5), 107–118 (2016)
R. Gill, R. Soni, Digital image watermarking using 2-DCT and 2-DWT in gray images, in International Conference on Intelligent Computing and Control Systems (ICICCS) (2017), pp. 797–803
M.C. Hernandez, M.N. Miyatake, H.M.P. Meana, Analysis of a DFT-based watermarking algorithm, in 2nd International Conference on Electrical and Electronics Engineering (2005), pp. 44–47
H.T. Hu, L.Y. Hsu, Collective blind image watermarking in DWT–DCT domain with adaptive embedding strength governed by quality metrics. Multimed. Tools Appl. 76(5), 6575–6594 (2017)
Y.L. Jiang, Y.F. Zhang, W.J. Pei, K. Wang, Adaptive image watermarking algorithm based on improved perceptual models. AEU-Int. J. Electron. Commun. 67(8), 690–696 (2013)
X.B. Kang, F. Zhao, G.F. Lin, Y.J. Chen, A novel hybrid of DCT and SVD in DWT domain for robust and invisible blind image watermarking with optimal embedding strength. Multimed. Tools Appl. 77(11), 13197–13224 (2018)
S.A. Kasmani, A. Naghsh-Nilchi, A new robust digital image watermarking technique based on joint DWT–DCT transformation, in IEEE 3rd International Conference on Convergence and Hybrid Information Technology (2008), pp. 539–544
D. Kundur, D. Hatzinakos, Digital watermarking for telltale tamper proofing and authentication. Proc. IEEE 87(7), 1167–1180 (1999)
C.C. Lai, C.C. Tsai, Digital image watermarking using discrete wavelet transform and singular value decomposition. IEEE Trans. Instrum. Meas. 59(11), 3060–3063 (2010)
Q. Li, I.J. Cox, Improved spread transform dither modulation using a perceptual model: robustness to amplitude scaling and JPEG compressing, in IEEE International Conference on Acoustics, Speech and Signal Processing (2007), pp. 185–188
M.M. Li, C. Han, A DCT–SVD domain watermarking for color digital image based on compressed sensing theory and chaos theory in 2014 Seventh International Symposium on Computational Intelligence and Design, Hangzhou (2014), pp. 35–38
X. Li, J. Liu, J. Sun, X. Yang, W. Liu, Step-projection-based spread transform dither modulation. IET Inf. Secur. 5(3), 170–180 (2011)
S.D. Lin, S.C. Shie, J.Y. Guo, Improving the robustness of DCT-based image watermarking against JPEG compression. Comput. Stand. Interfaces 32(1–2), 54–60 (2010)
H. Liu, D. Xiao, R. Zhang, Y. Zhang, S. Bai, Robust and hierarchical watermarking of encrypted images based on compressive sensing. Signal Process. Image Commun. 45, 41–51 (2016)
K.K. Neetha, A.M. Koya, A compressive sensing approach to DCT watermarking system, in 2015 International Conference on Control Communication and Computing India (ICCC) (2015), pp. 495–500
E. Nezhadarya, Z.J. Wang, R.K. Ward, Robust image watermarking based on multiscale gradient direction quantization. IEEE Trans. Inf. Forensic Secur. 6(4), 1200–1213 (2011)
V.M. Potdar, S. Han, E. Chang, A survey of digital image watermarking techniques, in Proceedings of the IEEE International Conference on Industrial Informatics (2005), pp. 709–716
D. Singh, S.K. Singh, DWT–SVD and DCT based robust and blind watermarking scheme for copyright protection. Multimed. Tools Appl. 76(11), 13001–13024 (2017)
B. Sukanti, Mardolkar, S. Nayana, A blind digital watermarking algorithm based on DWT–DCT transformation, in Nitte Conference on Advances in Electrical Engineering (2016), pp. 212–216
P. Tay, J. Havlicek, Image watermarking using wavelets, in IEEE Midwest Symposium on Circuits and System (2002), pp. 258–261
J.A. Tropp, A.C. Gilbert, Signal recovery from random measurements via orthogonal matching pursuit. IEEE Trans. Inf. Theory 53(12), 4655–4666 (2007)
T.K. Tsui, X.P. Zhang, D. Androutsos, Color image watermarking using multidimensional fourier transforms. IEEE Trans. Inf. Forensic Secur. 3(1), 16–28 (2008)
W. Wang, A.D. Men, X.B. Chen, Robust image watermarking scheme based on phase features in DFT domain and generalized radon transformations, in 2nd International Congress on Image and Signal Processing (2009), pp. 1510–1514
H.C. Xu, X.B. Kang, Y.H. Wang, Y.L. Wang, Exploring robust and blind watermarking approach of colour images in DWT–DCT–SVD domain for copyright protection. Int. J. Electron. Sec. Digit. Forensics 10(1), 79–96 (2018)
Y. Zhang, L.Y. Zhang, J. Zhou, L. Liu, F. Chen, X. He, A review of compressive sensing in information security field. IEEE Access, Special Section Green Commun. Netw. 5G Wirel. 4, 2507–2519 (2016)
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher’s Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
This work was supported in part by the Natural Science Foundation of Jiangsu Province under Grant BK20151102, in part by the Ministry of Education Key Laboratory of Machine Perception, Peking University under Grant K-2016-03, in part by the Open Project Program of the Ministry of Education Key Laboratory of Underwater Acoustic Signal Processing, Southeast University under Grant UASP1502, and in part by the Natural Science Foundation of China under Grant 61673108.
Rights and permissions
About this article
Cite this article
Zhang, Y., Li, Y. & Sun, Y. Digital Watermarking Based on Joint DWT–DCT and OMP Reconstruction. Circuits Syst Signal Process 38, 5135–5148 (2019). https://doi.org/10.1007/s00034-019-01112-2
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s00034-019-01112-2