Abstract
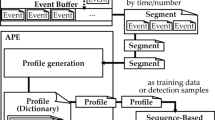
In this paper, we report about software behavior anomalies detection technique using Markov chains as model of normal software behavior.
Similar content being viewed by others
References
Warrender, C., Forrest, S., and Pearlmutter, B., Detecting Intrusions Using System-Calls: Alternative Data Models, IEEE Symposium on Security and Privacy, 1999.
Jha, S., Tan, K., and Maxion, R.A., Markov chains, classifiers, and intrusion detection, Proceedings of the 14th IEEE workshop on Computer Security Foundations, 2001.
Eskin, E., Lee, W., and Stolfo, S.J., Modeling system calls for intrusion detection with dynamic window sizes, DARPA Information Survivability Conference and Exposition, 2001.
Lee, W. and Xiang, D., Information-Theoretic Measures for Anomaly Detection, 2001.
Kort, S.S., Theoretical Bases of Protection of Information, Saint-Petersburg: Helios, 2004.
Author information
Authors and Affiliations
Corresponding author
Additional information
The article is published in the original.
About this article
Cite this article
Zegzhda, P.D., Kort, S.S. & Suprun, A.F. Detection of anomalies in behavior of the software with usage of Markov chains. Aut. Control Comp. Sci. 49, 820–825 (2015). https://doi.org/10.3103/S0146411615080386
Received:
Published:
Issue Date:
DOI: https://doi.org/10.3103/S0146411615080386