Abstract
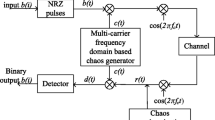
Sparse code multiple access (SCMA) has emerged as a significant technology to satisfy the essential criteria for 5G wireless networks, including high data rates, widespread connection, reliability, and greater spectrum efficiency. Under the restriction of scarce and limited spectrum utilization in 5G networks, the integrated cognitive radio (CR) with SCMA is a promising solution to handle these crucial needs. A reliable and secure connection network should be built in addition to this integrated network to deal with densely deployed networks. A secure transmission sensing approach for CR-SCMA systems employing chaos theory has been presented in the paper. Different chaotic maps, including the logistic map, tent map, Chebyshev map, sine map, and the generalized cascaded chaotic map (CCS), have been employed for sensing with secure communication. Bit error rate (BER) and probability of detection with effective simulation are two of the metrics used for performance evaluation. Instead of using random sequences, the chaos-based signal transmission provides a viable solution for 5G generation networks with a secure wireless communication link. Using chaotic map signals, which are extremely sensitive to their initial conditions and have non-periodic properties, the eavesdropper or the unauthorized user cannot simply grab the encrypted and secured vital data.

















Similar content being viewed by others
Data Availability
The research is experimentally set up and the operation is performed on Matlab R2020a software. All the data and simulation code will be available as per the reasonable request of human researchers.
References
Gamal S, Rihan M, Hussin S, Zaghloul A, Salem AA. Multiple access in cognitive radio networks: from orthogonal and non-orthogonal to rate-splitting. IEEE Access. 2021;9:95569–84.
Dai L, Wang B, Yuan Y, Han S, Chih-Lin I, Wang Z. Non-orthogonal multiple access for 5G: solutions, challenges, opportunities, and future research trends. IEEE Commun Mag. 2015;53(9):74–81.
Kumar A, Kumar K, Gupta MS, Kumar S. A survey on NOMA techniques for 5G scenario. In: Proceedings of the international conference on advances in electronics, electrical and computational intelligence (ICAEEC) 2019.
Nikopour H, Baligh H. Sparse code multiple access. In: 2013 IEEE 24th Annual international symposium on personal, indoor, and mobile radio communications (PIMRC). IEEE 2013, pp. 332–336.
Salameh HB, Abdel-Razeq S, Al-Obiedollah H. Integration of cognitive radio technology in NOMA-based B5G networks: state of the art, challenges, and enabling technologies. IEEE Access 2023.
Shekhawat GK, Yadav R. Review on classical to deep spectrum sensing in cognitive radio networks. In: 2021 Sixth international conference on wireless communications, signal processing and networking (WiSPNET). IEEE, pp. 11–15 (2021).
Hosseini H, Anpalagan A, Raahemifar K, Erkucuk S. Wavelet-based cognitive SCMA system for mmWave 5G communication networks. IET Commun. 2017;11(6):831–6.
Yonis A. Design and simulation of smart wireless devices using SCMA technology. J Eng Sci Technol. 2021;16(6):4404–13.
Shekhawat GK, Yadav R. Sparse code multiple access based cooperative spectrum sensing in 5g cognitive radio networks. In: 2020 5th International conference on computing, communication and security (ICCCS). IEEE, pp. 1–6 (2020).
Hamdani F, Arifianto MS. On the performance evaluations of uplink cognitive femtocell scma systems under imperfect channel sensing. In: 2018 4th International conference on wireless and telematics (ICWT). IEEE, pp. 1–5 (2018).
Zou Y, Wang X, Shen W. Physical-layer security with multiuser scheduling in cognitive radio networks. IEEE Trans Commun. 2013;61(12):5103–13.
Chen G, Gong Y, Xiao P, Chambers JA. Dual antenna selection in secure cognitive radio networks. IEEE Trans Veh Technol. 2015;65(10):7993–8002.
Jin Z, Anand S, Subbalakshmi KP. Impact of primary user emulation attacks on dynamic spectrum access networks. IEEE Trans Commun. 2012;60(9):2635–43.
Sharifi AA, Sharifi M, Niya MJM. Secure cooperative spectrum sensing under primary user emulation attack in cognitive radio networks: attack-aware threshold selection approach. AEU-Int J Electron Commun. 2016;70(1):95–104.
Chen R, Park J-M, Hou YT, Reed JH. Toward secure distributed spectrum sensing in cognitive radio networks. IEEE Commun Mag. 2008;46(4):50–5.
Muchandi N, Khanai R. Cognitive radio spectrum sensing: a survey. In: 2016 International conference on electrical, electronics, and optimization techniques (ICEEOT), pp. 3233–3237 (2016). https://doi.org/10.1109/ICEEOT.2016.7755301.
Shekhawat GK, Yadav R. Sensing performance analysis using chaotic signal based SCMA codebook for secure cognitive communication systems in 5G. In: Data science and security: proceedings of ICDSA. Lecture Notes in Networks and Systems (LNNS, vol. 818). Springer Singapore (2023).
Li M-L, Tian L-L, Yang X-X, Li Y, Wang A-H, Dong Z-S, Sami M, Mehrdad D. On the secrecy performance of NOMA-based cognitive radio networks with STBC. Acta Electron Sin. 2020;48(3):463.
Kaddoum G, Gagnon G, Gagnon F. Spread spectrum communication system with sequence synchronization unit using chaotic symbolic dynamics modulation. Int J Bifurc Chaos. 2013;23(02):1350019.
Almusawi I, Al-Hussaibi W, Tahir Y. Chaos-based NOMA for secure wireless communications over Rayleigh fading channels. In: Proceedings of the 1st international multi-disciplinary conference theme: sustainable development and smart planning, IMDC-SDSP 2020, Cyperspace, 28–30 June 2020 (2020).
Fang Y, Li L, Li Y, Peng H. High efficient and secure chaos-based compressed spectrum sensing in cognitive radio IoT network. In: 2021 IEEE sixth international conference on data science in cyberspace (DSC). IEEE 2021, pp. 670–676.
Wang B, Dai L, Yuan Y, Wang Z. Compressive sensing based multi-user detection for uplink grant-free non-orthogonal multiple access. In: 2015 IEEE 82nd vehicular technology conference (VTC2015-Fall). IEEE 2015, pp. 1–5.
Madbushi S, Raut R, Rukmini MSS. A novel chaotic communication based test signal approach for identification of primary user emulation attack in cognitive radio networks. Int J Intell Eng Syst. 2018;11(2).
Kaddoum G. Wireless chaos-based communication systems: a comprehensive survey. IEEE Access. 2016;4:2621–48.
Okamoto E, Horiike N, Yamamoto T. Sparse chaos code multiple access scheme achieving larger capacity and physical layer security. In: 2017 20th International symposium on wireless personal multimedia communications (WPMC). IEEE, pp. 604–610 (2017).
Mora HRC, Garzón NVO, García FDA, Sánchez JDV, López OLA. Secure transmission for uplink SCMA systems over \(\kappa \)-\(\mu \) fading channels. IEEE Trans Veh Technol (2023).
Gu J, Sohn SH, Kim JM, Jin M. Chaotic characteristic based sensing for cognitive radio. In: 2009 5th International conference on wireless communications, networking and mobile computing. IEEE, pp. 1–4 (2009).
Miao Y, Jian-ping A, Ning C, Jing-chong W. Spectrum sensing algorithm based on chaotic system in cognitive radio. J Beijing Inst Technol Nat Ed. 2011;3:329–32.
Falih SM. A new chaotic map for generating chaotic binary sequence. Kufa J Eng. 2017;8(1).
Zhao G, Ma Y, Ma Y. Design of SCMA codebook based on chaotic signal and system performance analysis. J Commun. 2019;40(2).
Benazzouza S, Ridouani M, Salahdine F, Hayar A. Chaotic compressive spectrum sensing based on Chebyshev map for cognitive radio networks. Symmetry. 2021;13(3):429.
Abed HS, Abdullah HN. Secure collaborative cognitive radio based on chaotic modulation and compressive sensing. Phys Commun. 2022;52: 101671.
Chen S-L, Hwang T, Lin W-W. Randomness enhancement using digitalized modified logistic map. IEEE Trans Circuits Syst II Express Briefs. 2010;57(12):996–1000.
Addabbo T, Alioto M, Fort A, Pasini A, Rocchi S, Vignoli V. A class of maximum-period nonlinear congruential generators derived from the Rényi chaotic map. IEEE Trans Circuits Syst I Regul Pap. 2007;54(4):816–28.
Chen G, Yu X. Chaos control: theory and applications, vol. 292. Berlin: Springer; 2003.
Gao T, Chen Z. A new image encryption algorithm based on hyper-chaos. Phys Lett A. 2008;372(4):394–400.
Zhou Y, Hua Z, Pun C-M, Chen CP. Cascade chaotic system with applications. IEEE Trans Cybern. 2014;45(9):2001–12.
Gao Z-M, Zhao J, Zhang Y-J. Review of chaotic mapping enabled nature-inspired algorithms. Math Biosci Eng. 2022;19:8215–58.
Naik RB, Singh U. A review on applications of chaotic maps in pseudo-random number generators and encryption. Ann Data Sci. 2022:1–26.
Naderpour M, Ghobadzadeh A, Tadaion A, Gazor S. Generalized Wald test for binary composite hypothesis test. IEEE Signal Process Lett. 2015;22(12):2239–43.
Kumar A, Saha S, Tiwari K. A double threshold-based cooperative spectrum sensing with novel hard-soft combining over fading channels. IEEE Wirel Commun Lett. 2019;8(4):1154–8.
Shekhawat GK, Karmakar P. Penalty based weighted cooperative spectrum sensing using normal factor graph. In: 2016 International conference on advances in computing, communications and informatics (ICACCI). IEEE, pp. 82–87 (2016).
Ma Z, Bao J. Sparse code multiple access (SCMA). Multiple access techniques for 5G wireless networks and beyond, pp. 369–416 (2019).
Association IS. IEEE standard for information technology—local and metropolitan area networks– specific requirements—part 22: Cognitive wireless ran medium access control (MAC) and physical layer (PHY) specifications: policies and procedures for operation in the TV bands. IEEE Std 802.22-2011, pp. 1–680 (2011). https://doi.org/10.1109/IEEESTD.2011.5951707.
Acknowledgements
The article is an extended version of our previous conference paper presented in Ref. [17].
Funding
There is no funding availability.
Author information
Authors and Affiliations
Contributions
All the authors have equally contributed in the research.
Corresponding author
Ethics declarations
Conflict of Interest
On behalf of all the authors, there is no conflict of interest. The authors declare that they have no known competing financial interest or personal relationships that could have appeared to influence the work reported in the paper.
Ethical Standards
The authors declare that they have no conflict of interest and there was no human or animal testing or participation involved in the research work.
Human Participants or Animal Rights
This article does not contain any studies with human participants or animals performed by any of the authors.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
This article is part of the topical collection “Emerging Applications of Data Science for Real-World Problems” guest edited by Satyasai Jagannath Nanda, Rajendra Prasad Yadav and Mukesh Saraswat.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Shekhawat, G.K., Yadav, R.P. Efficient Data Sensing Algorithm with Generalized Cascaded Chaotic Maps for Secure Cognitive Radio in 5G Networks. SN COMPUT. SCI. 5, 384 (2024). https://doi.org/10.1007/s42979-024-02699-3
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s42979-024-02699-3