Abstract
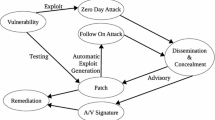
The inevitable use of web applications has resulted in increased exposure to security vulnerabilities which are exploited by attackers each passing day. Fixing these vulnerabilities requires a great deal of effort and time, hence developers need to prioritize and channel their resources to the most severe vulnerabilities to curtail further exploitation. The common vulnerability scoring system (CVSS) is the de-facto standard for characterizing and measuring the severity of security vulnerabilities. However, the efficiency of the CVSS metric has been challenged in previous studies, leading to varied vulnerability scoring metrics. This paper proposes an automated framework for evaluating open-source Web scanner vulnerability severity using a Web vulnerability detection scanner called zed attach proxy to detect vulnerabilities in a damn vulnerable web application. Additionally, we use the OWASP 2017 top ten selection and prioritization scheme as our benchmark for the severity measure and ranking. The preliminary result shows that the most frequent vulnerabilities in Web applications, such as SQL injection and cross-site scripting are of medium severe with a severity score of 8.



Similar content being viewed by others
References
Keramati M (2016) New vulnerability scoring system for dynamic security evaluation. In: Proceedings of the 8th international symposium on telecommunications (IST), pp 746–751
Dobrovoljc A, Trček D, Likar B (2017) Predicting exploitations of information systems vulnerabilities through attackers’ characteristics. IEEE Access 5:26063–26075
Liu Q, Zhang Y (2011) VRSS: a new system for rating and scoring vulnerabilities. Comput Commun 34:264–273
Younis A, Malaiya YK, Ray I (2016) Evaluating CVSS base score using vulnerability rewards programs. In: Proceedings of the international conference on ICT systems security and privacy protection, pp 62–75
Keramati M (2016) New vulnerability scoring system for dynamic security evaluation. In Proceedings of the 8th international symposium on telecommunications (IST), pp 746–751
Booth H, Rike D, Witte G (2013) The national vulnerability database (NVD): overview. National Institute of Standards and Technology, Gaithersburg
Mburano B, Si W (2018) Evaluation of web vulnerability scanners based on OWASP benchmark. In: Proceeding of the 26th international conference on systems engineering (ICSEng), pp 1–6
Ghezzi C, Jazayeri M, Mandrioli D (2002) Fundamentals of software engineering. Prentice Hall PTR, Upper Saddle River
Mell P, Scarfone K, Romanosky S (2006) Common vulnerability scoring system. IEEE Secur Privacy 4:85–89
Mell P, Scarfone K, Romanosky S (2007) A complete guide to the common vulnerability scoring system version 2.0. FIRST-Forum of Incident Response and Security Teams, p 23
Scarfone K, Mell P (2009) An analysis of CVSS version 2 vulnerability scoring. In: Proceedings of the 3rd international symposium on empirical software engineering and measurement, pp 516–525
Ali A, Beg MR, Ahmad S, Ali A (2012) Evaluation of security risk associated with different network layers. Int J Sci Eng Res 3(8):1–9
Wang Y, Yang Y (2012) PVL: a novel metric for single vulnerability rating and its application in IMS. J Comput Inf Syst 8:579–590
Hamid T, Maple C, Sant P (2012) Methodologies to develop quantitative risk evaluation metrics. Int J Comput Appl 48(14):17–24
Allodi L, Massacci F (2012) A preliminary analysis of vulnerability scores for attacks in wild: the ekits and sym datasets. In: Proceedings of the 2012 ACM workshop on building analysis datasets and gathering experience returns for security, pp 17–24
Zhang S, Ou X, Caragea D (2015) Predicting cyber risks through the national vulnerability database. Inf Secur J Glob Perspect 24:194–206
Holm H, Afridi KK (2015) An expert-based investigation of the common vulnerability scoring system. Comput Secur 53:18–30
Johnson P, Lagerström R, Ekstedt M, Franke U (2016) Can the common vulnerability scoring system be trusted? A bayesian analysis. IEEE Trans Depend Secure Comput 15:1002–1015
Makino Y, Klyuev V (2015) Evaluation of web vulnerability scanners. In: Proceedings of the 8th IEEE international conference on intelligent data acquisition and advanced computing systems: technology and applications (IDAACS), pp 399–402
Porter AA, Votta LG Jr, Basili VR (1995) Comparing detection methods for software requirements inspections: a replicated experiment. IEEE Trans Softw Eng 21:563–575
Sutton M, Greene A, Amini P (2007) Fuzzing: brute force vulnerability discovery. Pearson Education, London
Joh H, Malaiya YK (2011) Defining and assessing quantitative security risk measures using vulnerability lifecycle and CVSS metrics. In: Proceedings of the 2011 international conference on security and management (SAM), pp 10–16
Schiffman M, Cisco C (2005) A complete guide to the common vulnerability scoring system (cvss). In: White paper. Identification of basic measurable security components in software intensive systems
Scarfone K, Mell P (2007) Guide to intrusion detection and prevention systems (IDPS). NIST Special Publ 800:94
Younis A, Malaiya YK, Ray I (2016) Assessing vulnerability exploitability risk using software properties. Softw Qual J 24:159–202
Cadariu M, Bouwers E, Visser J, van Deursen A (2015) Tracking known security vulnerabilities in proprietary software systems. In: Proceedings of the 22nd IEEE international conference on software analysis, evolution, and reengineering (SANER), pp 516–519
Alessandri D, Cachin C, Dacier M, Deak O, Julisch K, Randell B et al (2001) Towards a taxonomy of intrusion detection systems and attacks. In: MAFTIA deliverable D, vol 3
Owasp T (2013) 10 2017: The ten most critical web application security risks. The OWASP Foundation, Sl
Woo DH, Lee H (2007) Analyzing performance vulnerability due to resource denial of service attack on chip multiprocessors. In: Proceedings of the workshop on chip multiprocessor memory systems and interconnects
Du W, Mathur AP (1998) Vulnerability testing of software system using fault injection. Technique report. Purdue University, West Lafayette, pp 98–02
Haugh E, Bishop M (2003) Testing C programs for buffer overflow vulnerabilities. In: NDSS
Whalen S, Bishop M, Engle S (2005) Protocol vulnerability analysis. Technical report CSE-2005-04. Department of Computer Science, University of California, Davis
Kals S, Kirda E, Kruegel C, Jovanovic N (2006) Secubat: a web vulnerability scanner. In: Proceedings of the 15th international conference on world wide web, pp 247–256
Calzavara S, Conti M, Focardi R, Rabitti A, Tolomei G (2019) Mitch: a machine learning approach to the black-box detection of CSRF vulnerabilities. In: Proceedings of IEEE European symposium on security and privacy (EuroS&P), pp 528–543
Ibrahim AB, Kant S (2018) Penetration testing using SQL injection to recognize the vulnerable point on web pages. Int J Appl Eng Res 13:5935–5942
Hassan MM, Bhuyian T, Sohel MK, Sharif MH, Biswas S (2018) SAISAN: an automated local file inclusion vulnerability detection model. Int J Eng Technol 7:4
Sharma P, Johari R, Sarma S (2012) Integrated approach to prevent SQL injection attack and reflected cross-site scripting attack. Int J Syst Assur Eng Manag 3:343–351
Deepa G, Thilagam PS (2016) Securing web applications from injection and logic vulnerabilities: approaches and challenges. Inf Softw Technol 74:160–180
Deepa G, Thilagam PS, Praseed A, Pais AR (2018) DetLogic: a black-box approach for detecting logic vulnerabilities in web applications. J Netw Comput Appl 109:89–109
Alenezi M, Zarour M (2018) Software vulnerabilities detection based on security metrics at the design and code levels: empirical findings. J Eng Technol 6:570–583
Woo DH, Lee H (2007) Analyzing performance vulnerability due to resource denial of service attack on chip multiprocessors. In: Workshop on chip multiprocessor memory systems and interconnects
Zhang S, Caragea D, Ou X (2011) An empirical study on using the national vulnerability database to predict software vulnerabilities. In: Proceeding of the international conference on database and expert systems applications, pp 217–231
Huang S, Tang H, Zhang M, Tian J (2010) Text clustering on national vulnerability database. In: Second international conference on computer engineering and applications, pp 295–299
Byers R, Waltermire D, Turner C (2020) National vulnerability database (NVD) metadata submission guidelines for common vulnerabilities and exposures (CVE) numbering authorities (CNAs) and authorized data publishers. National Institute of Standards and Technology
Zhang S, Caragea D, Ou X (2011) An empirical study on using the national vulnerability database to predict software vulnerabilities. In: International conference on database and expert systems applications, pp 217–231
Abedin M, Nessa S, Al-Shaer E, Khan L (2006) Vulnerability analysis for evaluating quality of protection of security policies. In: Proceedings of the 2nd ACM workshop on quality of protection, pp 49–52
Wang JA, Guo M (2010) Vulnerability categorization using Bayesian networks. In: Proceedings of the sixth annual workshop on cyber security and information intelligence research, p 29
Anbalagan P, Vouk M (2009) On mining data across software repositories. In: Proceedings of the 6th IEEE international working conference on mining software repositories. MSR’09, pp 171–174
Makino Y, Klyuev V (2015) Evaluation of web vulnerability scanners. In: IEEE 8th international conference on intelligent data acquisition and advanced computing systems: technology and applications (IDAACS), pp 399–402
Evans S (2008) Securing WebGoat using ModSecurity, summer of code 2008. In: OWASP beta level. OWASP Foundation
Kudjo PK, Chen J, Mensah S, Amankwah R (2018) Predicting vulnerable software components via bellwethers. Communications in computer and information science, Springer, Singapore, pp 389–407
Tripathi A, Singh UK (2011) On prioritization of vulnerability categories based on CVSS scores. In: Proceedings of the 6th international conference on computer sciences and convergence information technology (ICCIT), pp 692–697
Kudjo PK, Chen J, Zhou M, Mensah S, Huang R (2019) Improving the accuracy of vulnerability report classification using term frequency-inverse gravity moment. In: Proceedings of the 19th IEEE international conference on software quality, reliability and security (QRS), pp 248–259
Elizabeth F, Vadim O (2007) Web application scanners: definitions and functions. HICSS 2007:280b–280b
Khan ME (2010) Different forms of software testing techniques for finding errors. Int J Comput Sci Issues 7:24
Fink S, Haviv YA, Hay R, Pistoia M, Segal O, Sharabani A et al (2017) Simulating black box test results using information from white box testing. Google Patents
Nidhra S, Dondeti J (2012) Black box and white box testing techniques-a literature review. Int J Embedded Syst Appl (IJESA) 2:29–50
Slaby J, Strejcek J, Trtık M (2013) ÐÙÖ: classified bug-reports database tool for developers of program analysis tools. In: Proceedings of 14th international conference on verification, model checking, and abstract interpretation. VMCAI, Rome, Italy, January 20–22, 2013, p 268
OWASP Benchmark Project (2016) https://www.owasp.org/index.php/Benchmark (visited 2016-06-2), pp 1–6
Acknowledgement
This work is partly supported by the National Natural Science Foundation of China (NSFC Grant Numbers: U1836116, 61762040 and 61872167), the project of Jiangsu provincial Six Talent Peaks (Grant Numbers: XYDXXJS-016), and the Graduate Research Innovation Project of Jiangsu Province (Grant Numbers: KYCX17_1807).
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Amankwah, R., Chen, J., Kudjo, P.K. et al. An automated framework for evaluating open-source web scanner vulnerability severity. SOCA 14, 297–307 (2020). https://doi.org/10.1007/s11761-020-00296-9
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11761-020-00296-9