Abstract
A certificate-based public key cryptosystem has been developed to solve key escrow problems in ID-based public key cryptography, and to remove computational operations for certificate management. Signcryption is a primitive cryptographic that enables signing and encryption to be done in a one step, improving performance by reducing computational loads and communication overheads. Recent research has suggested some pairing-based cryptographic protocols for public key cryptosystems. However, most use Type-1 pairings, which weaken system security by using supersingular elliptic curves over a finite field of characteristics 2 and 3, making them totally unsafe against new attacks designed for Discrete Logarithm Problems. Furthermore, Type-1 pairings that use supersingular elliptic curves over finite fields of massive characteristics are highly inefficient compared to Type-3 pairings. This work proposes a secure and efficient online/offline trade-off scheme based on Type-3 pairings. The safety of the suggested scheme is asserted according to confidentiality and unforgeability based on a random oracle model. Moreover, the efficiency of the proposed approach is evaluated and compared with Type-2 and Type-4 pairings.


Similar content being viewed by others
Data Availability
Enquiries about data availability should be directed to the authors.
References
Shamir, A. (1984). Identity-based cryptosystems and signature models. Lecture Notes in Computer ScienceAdvances in Cryptology - CRYPTO 1984 (Vol. 196, pp. 47–53). Berlin: Springer-Verlag.
K. T.Nguyen, N. Oualha, and M. Laurent (2015) Lightweight certificateless and provably secure signcryptosystem for Internet of Things. In: 2015 IEEE Trustcom/BigData SE/ISPA.
Zheng, Y. (2015). Digital signcryption or how to achieve cost (signature and encryption) 6 cost (signature) + cost(encryption). In G. Goos, J. Hartmanis, & J. van Leeuwen (Eds.), (2015) Advances in Cryptology-Crypto, LNCS (Vol. 1294, pp. 291–312). Berlin: Springer-Verlag.
An, J. H., Dodis, Y., & Rabin, T. (2002). On the security of joint signature and encryption. In L. R. Knudsen (Ed.), Advances in Cryptology-Eurocrypt 2002, LNCS (Vol. 2332, pp. 83–107). Springer-Verlag.
J. Malone-Lee. (2002) Identity based signcryption, Cryptology ePrint Archive, Report 2002/098, http://eprint.iacr.org/2002/098..
Libert, B., & Quisquater, J. J. (2003). A new identity based signcryption model from pairings. 2003 I.E. information theory workshop (pp. 155–158). Paris: France.
Even, S., Goldreich, O., & Micali, S. (1996). Online/offline digital signatures. Journal of Cryptology, 9(1), 35–67.
Zhang, F., Mu, Y. and Susilo, W. (2005). Reducing security overhead for mobile networks. In Proceedings of the advanced information net- working and applications, Taipei, Taiwan (pp. 398–403).
Sun, D., Huang, X., Mu, Y. and Susilo, W. (2008) Identity-based online/off- line signcryption. In Proceedings of the network and parallel com- puting, Shanghai, China (pp. 34–41).
Liu, J.K., Baek, J. and Zhou, J.Y. (2011). Online/offline identity-based signcryption re-visited. In Proceedings of the information security and cryptology, LNCS, Berlin, Springer-Verlag, (vol 6584, pp 36–51).
Selvi, S.S.D., Vivek, S.S and Rangan, C.P. (2010). Identity based online/offline signcryption model. Cryptology ePrint Archive. Available at: http://eprint.iacr.org/2010/376.pdf.
Li, F. G., Khan, M. K., Alghathbar, K., & Takagi, T. (2012). Identity-based online/offline signcryption for low power devices. Journal of Network and Computer Applications, 35, 340–347.
He, D., Chen, Y., Chen, J., et al. (2011). A new two-round certificateless authenticated key agreement protocol without bilinear pairings. Mathematical and Computer Modelling, 54(11), 3143–3152.
He, D., Chen, J., & Hu, J. (2012). A pairing-free certificateless authenticated key agreement protocol. International Journal of Communication Systems, 25(2), 221–230.
He, D., Padhye, S., & Chen, J. (2012). An efficient certificateless two-party authenticated key agreement protocol. Computers and Mathematics with Applications, 64(6), 1914–1926.
He, D., & Chen, J. (2013). An efficient certificateless designated verifier signature model. International Arab Journal of Information Technology, 10(4), 317–324.
He, D., Chen, Y., & Chen, J. (2013). An efficient certificateless proxy signature model without pairing. Mathematical and Computer Modelling, 57(9–10), 2510–2518.
He, D., Huang, B., & Chen, J. (2013). New certificateless short signature model. IET Information Security, 7(2), 113–117.
He, D., Chen, J., & Zhang, R. (2013). An efficient and provably-secure certificateless signature model without bilinear pairings. International Journal of Communication Systems, 25(11), 1432–1442.
Sun, Y., & Li, H. (2010). Short-ciphertext and BDH-based CCA2 secure certificateless encryption. SCIENCE CHINA Information Sciences, 53(10), 2005–2015.
Sun, Y., & Zhang, F. (2010). Secure certificateless encryption with short ciphertext. Chinese Journal of Electronics, 19(2), 313–318.
Adj, G., Menezes, A., Oliveira, T., & Rodríguez-Henríquez, F. (2015). Computing discrete logarithms in F 6 3 ·137 and F 6 3 ·163 using magma. In C. K. Koç, S. Mesnager, & E. Sava¸s (Eds.), Arithmetic of Finite Fields (pp. 3–22). Cham: Springer.
R. Barbulescu , P. Gaudry , A. Joux , E. Thomé, (2014), Proceedings of the advances in cryptology–EUROCRYPT 2014: Thirty-third annual international conference on the theory and applications of cryptographic techniques, Copenhagen, Denmark, Springer Berlin Heidelberg, Berlin, Heidelberg, (pp. 1–16).
Gölo˘glu, F., Granger, R., McGuire, G., & Zumbrägel, J. (2013). On the function field sieve and the impact of higher splitting probabilities (pp. 109–128). Berlin: Springer.
Granger, R., Kleinjung, T., & Zumbrägel, J. (2014). ‘128-bit secure’ supersingular binary curves. Advances in cryptology—CRYPTO 2014 (pp. 126–145). Springer.
Barbulescu, R., & Duquesne, S. (2018). Updating key size estimations for pairings. Journal of Cryptology. https://doi.org/10.1007/s00145-018-9280-5
Kim, T., & Jeong, J. (2017). Extended tower number field sieve with application to finite fields of arbitrary composite extension degree. In S. Fehr (Ed.), Public-key cryptography–PKC 2017 (pp. 388–408). Berlin: Springer.
Kim, T., Barbulescu, R. (2016). Proceedings of the advances in cryptology –CRYPTO, thirty-second annual cryptology conference, Springer, Berlin, August 14–18, 2012. Santa Barbara, CA, USA
Sarkar, P., & Singh, S. (2016). A general polynomial selection method and new asymptotic complexities for the tower number field sieve algorithm, advances in cryptology—ASIACRYPT 2016. Springer.
Kiraz, M.S., Uzunkol, O. (2018). Still wrong use of pairings in cryptography. Applied Mathematics and computation, 467–479.
Abe, M., Groth, J., Ohkubo, M., & Tango, T. (2014). Converting cryptography models from symmetric to asymmetric bilinear groups. Advances in cryptology CRYPTO 2014, volumes 8616 of Lecture Notes in Computer Science (pp. 241–260). Berlin Heidelberg: Springer.
Akinyele, J.A., Garman, C., and Hohenberger, S. (2015). Automating fast and secure translations from type-i to type-iii pairing models. In Proceedings of the 22Nd ACM SIGSAC conference on computer and communications security, CCS'15, pp 1370–1381. ACM.
Chatterjee, S., Hankerson, D., Menezes, A., (2010). On the efficiency and security of pairing-based protocols in the Type-1 and Type-4 settings. In International workshop on arithmetic of finite fields–WAIFI 2010, LNCS, (vol. 6087, pp. 114–134).
Galbraith, S. D., Paterson, K. G., & Smart, N. P. (2008). Pairings for cryptographers. Discrete Applied Mathematics, 156(16), 3113–3121.
H. Shacham.(2006) New Paradigms in Singnature Models, PhD thesis, Stanford.
Chen, L., Cheng, Z., & Smart, N. P. (2007). Identity-based key agreement protocols from pairings. International Journal of Information Security, 6(4), 213–241.
Barbulescu, R., Gaurdy, P., Joux, A., and Thome, E. (2014). Advances in Crptology-EUROCRYPT 2014: 33rd annual international conference on the theory and applications of cryptographic techniques, Copenhagen, Denmark, May 11–15, 2014. In Proceedings, chapter A heuristic quasi-polynomial algorithm for discrete logarithm in finite field of small characteristic, Springer Berlin (pp. 1–16).
Freeman, D., Scott, M., and Teske, E., (2006). A taxonomy of pairing-friendly elliptic curves. Cryptology eprint Archive report.
Enge, A. and Milan, J. (2014) Implementing cryptographic pairings at standard security levels, Security, privacy and applied cryptography engineering. Volume 8804 of the series Lecture Notes in Computer Science, (pp. 28–46).
Boyen, X. (2008). The uber-assumption family – A unified complexity framework for blinear groups. In Pairing-based cryptography – pairing 2008, (vol. 5209, pp. 39–56).
Smart, N., & Vercauteren, F. (2007). On computable isomorphisms in efficient pairing-based systems. Discrete Applied Mathematics, 155, 538–547.
Chen, L., & Cheng, Z. (2005). Security proof of Sakai-Kasahara’s identity-based encryption model. Cryptography and Coding, in: LNCS, 3706, 442–459.
Chatterjee, S., Hankerson, D., Knapp, E., & Menezes, A. (2010). Comparing two pairing-based aggregate signature models. Designs, Codes and Cryptography, 55, 141–167.
Chatterjee, S., & Menezes, A. (2011). On cryptographic protocols employing asymmetric pairings-the role of ѱ revisited. Discrete Applied Mathematics, 159(13), 1311–1322.
Chen, L., Cheng, Z. (2005). Security proof of Sakai-Kasahara's identity-based encryption model. Cryptography and Coding, (pp. 442–459).
Li, F., Han, Y., & Jin, C. (2017). Certificateless online/offline signcryption for the Internet of Things. Wireless Networks, 23(1), 145–158.
Barreto, P. S. L. M., Libert, B., McCullagh, N. and Quisquter, J. (2005) Efficient and provably-secure identity-based signatures and signcryption from bilinear maps. In: Asiacrypt 05 proceedings of the 11th international conference on theory and application of cryptology and information security, (pp. 515–532).
Pointcheval, D., & Stern, J. (2000). Security arguments for digital signatures and blind signatures. Journal of Cryptology, 13(3), 361–396.
Cha, J. C., & Cheon, J. H. (2003). An identity-based signature from gap Diffie-Hellman groups. In Public Key Cryptography- PKC 2003. LNCS, 2567, 18–30.
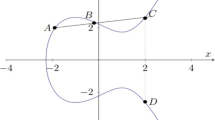
Khamseh, E. (2021). The review on elliptic curves as cryptographic pairing groups. Mathematics and Computational Sciences, 1(3), 50–59.
Odlyzko. A. M. (1985). Advances in cryptology: Proceedings of EUROCRYPT 84 a workshop on the theory and application of cryptographic techniques Paris, France, Aprill 9–11, 1984, chapter Discrete logarithms in finite fields and their cryptographic significance, pages 224–314, Springer Berlin.
Rasori, M., La Manna, M., Perazzo, P., & Dini, G. (2022). A survey on attribute-based encryption models suitable for the Internet of Things. IEEE Internet of Things Journal. https://doi.org/10.1109/JIOT.2022.3154039
Rao, V., & Prema, K. V. (2021). A review on lightweight cryptography for Internet-of-Things based applications. J Ambient Intell Human Comput, 12, 8835–8857.
Padmalayan, N., & Swapna, G. (2023). Security issues in IoT applications using certificateless aggregate signcryption models: An overview. Internet of Things, 21, 100641.
Shan, S. (2022). Cryptanalysis of a certificateless hybrid signcryption model and a certificateless encryption model for Internet of Things, security and communication networks. Article ID, 6174031, 6.
Granger, R., Page, D., & Smart, N. (2006). High security pairing-based cryptography revisited. Algorithmic number theory symposium VII (pp. 480–494). Springer.
Hess, F., Smart, N. P., & Vercauteren, F. (2006). The Eta pairing revisited. IEEE Transactions on Information Theory, 52(10), 4595–4602.
Shim, K. A. (2024). A secure certificateless signature scheme for cloud-assisted Industrial IoT. IEEE Transactions on Industrial Informatics, 20, 1–10.
Cherbal, S., Zier, A., Hebal, S., Louail, L., & Annane, B. (2024). Security in internet of things: A review on approaches based on blockchain, machine learning, cryptography, and quantum computing. The Journal of Supercomputing, 80(3), 3738–3816.
Acknowledgements
We thank Islamic Azad university Shahr-e-Qods branch for supporting us. Also we thank the referees for the comments.
Funding
No specific grants have been granted by any public, private or not for profit funding agency to this research.
Ethics declarations
Conflict of interest
The authors declare that they have no conflict of interest.
Ethical Approval
No studies with human subjects or animals carried out by any of the authors shall be included in ethical approval for this article.
Consent for Publication
No requirement.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Khamseh, E., Reza, A. & Esterabadi, A.S. Lightweight Certificateless Signcryption Scheme Using Type-3 Pairing on Elliptic Curve. Wireless Pers Commun 135, 1497–1517 (2024). https://doi.org/10.1007/s11277-024-11120-4
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11277-024-11120-4