Abstract
Information reconciliation (IR) corrects the errors in sifted keys and ensures the correctness of quantum key distribution (QKD) systems. Polar codes-based IR schemes can achieve high reconciliation efficiency; however, the incidental high frame error rate decreases the secure key rate of QKD systems. In this article, we propose a Shannon-limit approached (SLA) IR scheme, which mainly contains two phases: the forward reconciliation phase and the acknowledgment reconciliation phase. In the forward reconciliation phase, the sifted key is divided into sub-blocks and performed with the improved block checked successive cancellation list decoder of polar codes. Afterward, only the failure corrected sub-blocks perform the additional acknowledgment reconciliation phase, which decreases the frame error rate of the SLA IR scheme. The experimental results show that the overall failure probability of SLA IR scheme is decreased to \(10^{-8}\) and the efficiency is improved to 1.091 with the IR block length of 128 Mb. Furthermore, the efficiency of the proposed SLA IR scheme is 1.055, approached to Shannon limit, when the quantum bit error rate is 0.02 and the input scale of 1 Gb, which is hundred times larger than the state-of-the-art implemented polar codes-based IR schemes.
Similar content being viewed by others
Avoid common mistakes on your manuscript.
1 Introduction
Quantum key distribution (QKD) can generate information-theoretical secure keys between distant communication parties (Alice and Bob) [1,2,3]. Assume the sifted keys are \(K_\mathrm {s}^A\) and \(K_\mathrm {s}^B\) with length of n in both sides (Alice and Bob) after the quantum physical communication phase, \(K_\mathrm {s}^A\ne K_\mathrm {s}^B\) with the quantum bit error rate \(E_\mu \), which is introduced by imperfect implementations of QKD systems and potential attacks. Information reconciliation (IR), a critical procedure of the post-processing phase in QKD systems, aims at reconciling \(K_\mathrm {s}^A\) and \(K_\mathrm {s}^B\) to an equally weak secure key \(K_\mathrm {IR}\), by exchanging the minimized extra syndrome information [1, 4, 5]. IR ensures the correctness of QKD systems and is the precondition to generate the final secure keys.
Initially, IR procedure is implemented by performing interactive methods known as BBBSS [5, 6] and Cascade [7]. Though high efficiency is achieved by several improvements of Cascade algorithms, multiple rounds of communication are still required, resulting in significant heavy latency and authentication cost of QKD systems. Nowadays, IR is performed with forward error correction (FEC) codes, such as low-density parity-check codes [8, 9] and polar codes [10,11,12], where only one message containing a syndrome is exchanged between Alice and Bob, called as one-way IR scheme. Recently, most IR research focuses on performing with polar codes, for the advantage of the low computational complexity \(O(n\log n)\) and high efficiency with potential to reach the Shannon limit, when the block size of a sifted key becomes as large as possible [13,14,15]. Though several improvements of polar decoders achieve higher IR efficiency with certain input scale (\(\sim 10^6\) bits), the \(\varepsilon \)-correctness of QKD systems is increased to the level of \(10^{-3}\) [10,11,12, 16]. The state-of-the-art efficiency of polar codes-based IR scheme reaches 1.176 with the input block size of 1 Mb when \(E_\mu = 0.02\), while \(\varepsilon \) still stays to 0.001 [11]. Actually, \(\varepsilon \) should be decreased as low as possible (usually \(<10^{-6}\)), when performing polar codes into the IR procedure of QKD systems.
Therefore, in this article, we propose a Shannon-limit approached (SLA) IR scheme performing improved polar codes, which mainly composes of a forward reconciliation phase and an acknowledgment reconciliation phase. In the forward reconciliation procedure, a novel block checked successive cancellation list (BC-SCL) decoder was proposed to reduce the \(\varepsilon \)-correctness and error sub-blocks by remaining the successfully decoded sub-blocks with cyclic redundancy check (CRC) values in advance. Meanwhile, existed errors in sub-blocks after the forward reconciliation procedure can be found by calculating the CRC values. For failure corrected sub-blocks, an additional acknowledgment reconciliation procedure is performed to decrease the \(\varepsilon \) to the desired level. Finally, the corrected key \(K_\mathrm {IR}\) is achieved. With the advantage of CRC strategy, the BC-SCL decoder determines the corrected decoding path from multiple decoding paths to reduce the \(\varepsilon \)-correctness and choose the unsuccessfully decoded sub-blocks which are corrected by the acknowledgment reconciliation phase. The experimental results show that our SLA IR scheme achieves correctness \(\varepsilon \) to \(10^{-8}\) and the reconciliation efficiency is better than 1.091, while the input block size is 128 Mb. In principle, the efficiency and the SLA IR scheme can close to the Shannon limit as the block length increases as large as possible. We achieved an efficiency of 1.055 with the \(E_\mu =0.02\), when the input scale of SLA IR is increased to 1 Gb. Meanwhile, our SLA IR scheme with large-scale block size will benefit a lot in performing the rigorous statistical fluctuation analysis to remove the finite-size key effects [17, 18] on the final secure key. Thus, SLA IR scheme can be efficiently implemented in practical QKD systems.
2 Related work
2.1 Information reconciliation
Information reconciliation (IR), as the critical post-processing procedure of QKD systems, corrects the errors in the sifted keys introduced by the implementation imperfectness and various attacks [1, 19, 20], so as to ensure the correctness of QKD systems [21]. Assume the sifted key is \(K_\mathrm {s}^A\) (\(K_\mathrm {s}^B\)) with length of n on Alice’s (Bob’s) side, the quantum bit error rate (QBER) is \(E_\mu \), and the error corrected key is \(K_{\mathrm {IR}}^A\) and \(K_{\mathrm {IR}}^B\), then the \(\varepsilon \)-correctness is equivalent to the requirement that the outputs of IR procedure, \(K_{\mathrm {IR}}^A\) and \(K_{\mathrm {IR}}^B\), differ only with small probability [21],
Assume the key information learned by eavesdroppers is S, then the reconciliation efficiency is defined as
where \(H_2(x)\) is the binary Shannon entropy, calculated by
The average yield of IR scheme is given by
2.2 Polar codes-based IR schemes
Given any binary-input discrete memoryless channel (B-DMC), E. Arikan first proposed a Shannon-limit approached information reconciliation scheme with complexity \(O\left( N\log N\right) \), named as polar codes in 2009 [13, 14]. In 2014, P. Jouguet and S. Kunz-Jacques performed the polar codes in the IR procedure in QKD systems; furthermore, they showed that polar codes have an equivalent efficiency below 1.12 for given upper bound \(\varepsilon =0.1\) and block length starting from 64 Kb to 16 Mb [10]. Afterward, A. Nakassis and A. Mink described flexible polar codes-based IR approaches for QKD systems and showed the potential to approach the Shannon limit with a more efficient decoder when the location and values of the frozen bits were known at the design time [12]. Yan et al. [11] improved the polar codes-based IR scheme with successive cancellation list (SCL) decoding and optimized coding structures, which decreased the \(\varepsilon \)-correctness to the level of \(10^{-3}\) and the equivalent efficiency reached to 1.176. The detailed performance of the above IR schemes and partial experimental results of our SLA IR scheme are described in Table 1.
3 Shannon-limit approached IR scheme
In principle, lower \(\varepsilon \)-correctness and Shannon-limit f of polar codes-based IR schemes can be approached with increased input block size and improved decoders [22,23,24,25,26,27,28,29]. Moreover, IR schemes with large-scale input block size benefit much in performing the rigorous statistical fluctuation analysis to remove the finite-size key effects on the final secure keys. However, \(\varepsilon \)-correctness of state-of-the-art polar codes-based IR schemes still stays on the level of \(10^{-3}\), which reduces the final secure key rates of QKD systems.
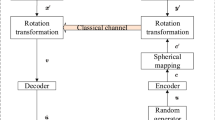
The schematic diagram of the proposed SLA IR scheme. TRNG: true random number generator, \(E_\mu \): quantum bit error rate, CRC: cyclic redundancy check, \(K_s^{\mathrm {A}}\) and \(K_s^{\mathrm {B}}\): the sifted key of Alice and Bob, LDPC: low density parity check. The detailed description of this figure is shown in the main text
In this article, we propose an improved Shannon-limit approached (SLA) IR scheme for QKD, and the schematic diagram is shown in Fig. 1. The proposed SLA IR scheme mainly contains two phases: the forward reconciliation phase and the acknowledgment reconciliation phase. In the forward reconciliation phase, Alice constructs the encoding vector U with true random numbers and the optimal frozen vector V, chosen from the frozen vector library with the quantum bit error rate \(E_\mu \). Then, Alice calculates the syndrome Z of \(K_\mathrm {s}^A\) with the polar codes encoder and, meanwhile, divides the vector U to m sub-blocks and calculates the cyclic redundancy check (CRC) value of each block. Afterward, the syndrome Z and combined CRC value vector T are transmitted to Bob via classical channel. Bob performs the same operations to select the frozen vector V and then performs the improved BC-SCL decoder (detail described in Sect. 3.3) to get the corrected vector \(U^\prime \) and the status vector \(\sigma \), indicating which sub-block is failure corrected. In the acknowledgment reconciliation phase, Alice and Bob perform a low-density parity-check (LDPC) error correction procedure to correct the error bits in the failure corrected sub-blocks. Afterward, Alice and Bob obtain the uniform key \(K_\mathrm {IR}\), respectively.
3.1 Forward reconciliation
Before Alice and Bob start the SLA IR scheme, optimized multi-rate frozen vectors of polar codes and parity-check matrix of LDPC codes are shared between each other.
First of all, Alice and Bob will calculate the required CRC length d and choose the appropriate number of sub-blocks m to achieve the expected \(\varepsilon \)-correctness. Given \(E_\mu \), Alice selects the optimized frozen vector V of polar codes, where the elements representing frozen bits are set to “0” and the rest are set to “− 1”. Then, k bits of true random numbers are used to replace the elements of V, whose value equals to “− 1”, marked as the vector U. Then, split U to m sub-blocks with length \(n^\prime =n/m\). For each sub-block \(U_i\), \(i\in [0,m)\) and \(i\in \mathbb {N}\), calculate the CRC tag value \(T_i=\mathrm {CRC}\left( U_i\right) \) and combined to T, \(T=(T_0|T_1|\dots |T_{m-1})\).
Meanwhile, the vector U is encoded to Z by
where \(G_n\) is the bit-reversal invariant matrix, defined as \(G_n=BF^{\otimes \log n}\), B is the permutation matrix for bit-reversal operation and \(F\overset{\varDelta }{=} \begin{bmatrix} 1 &{} 0\\ 1&{}1 \end{bmatrix}\) [13]. Afterward, Alice sends T and Z to Bob via the classical channel.
At Bob’s side, with Bob’s sifted key \(K_\mathrm {s}^B\), received T and Z, we can get the decoded vector \(U^\prime \) with failure probability \(\varepsilon _\mathrm {f}\) by performing our improved novel block checked (BC) SCL decoder, detailed described in Sect. 3.3. Additionally, a status vector \(\sigma \) also given for indicating which sub-block \(U^\prime _i\) is failure decoded. Each element of \(\sigma \) is defined as
Thus, in total r sub-blocks are failure decoded, \(r=\sum {\sigma _i}\). The position vector of these failure corrected sub-blocks is defined as \(E \overset{\varDelta }{=} \left\{ i|\sigma _i=1\right\} \).
3.2 Acknowledgment reconciliation
After the forward reconciliation phase, we have to perform the acknowledgment reconciliation phase to correct the remained errors in partial sub-blocks.
Here, Bob distinguishes two cases according to the value of r.
Case I. If \(r\ne 0\), Bob performs the permutation operation to \(K_\mathrm {s}^B\),
and then, divide Y to m sub-blocks with length \(n^\prime =n/m\). Then, Bob calculates the syndrome \(\mathscr {S} \) from \(Y_E\) by performing the LDPC encoding scheme with chosen optimized parity-check matrix, where \(Y_E\overset{\varDelta }{=} \left\{ Y_{e_i}|e_i\in E \right\} \). Then, Bob sends \(\sigma \) and \(\mathscr {S}\) to Alice. Alice performs the bit-reversal operation to \(K_\mathrm {s}^A\),
and then, divide X into m sub-blocks with length \(n^\prime =n/m\). Alice corrects the error bits in \(X_E\) with \(\mathscr {S}\), where \(X_E\overset{\varDelta }{=} \left\{ X_{e_i}|e_i\in E \right\} \).
In the end of acknowledgment reconciliation phase, Bob gets the error corrected key \(K_\mathrm {IR}^B\) with failure probability \(\varepsilon \), whose ith sub-block can be represented by
Alice performs similar procedure shown in Eq. (9) to the identical and weak secure key \(K_\mathrm {IR}^A\).
Case II. If \(r=0\), Bob sets \(\mathscr {S} =\)Ø. Then, \(\sigma \) and \(\mathscr {S}\) are transmitted to Alice. Afterward, Alice and Bob gets \(K_\mathrm {IR}^A=U\) and \(K_\mathrm {IR}^B=U^\prime \) as the error corrected key, respectively.
3.3 Block checked SCL decoder
In the article, we improve the successive cancellation list (SCL) decoder to reduce the \(\varepsilon \)-correctness by performing cyclic redundancy check (CRC) to divided sub-blocks, called as block checked (BC) SCL decoder [22].
In the BC-SCL decoder, we assume the list size is l, P is the list of decoded vectors, \(\mathcal {P} \in P\) with length of n, \(\mathcal {P}_{j}^{k}\) is a sub-vector of \(\mathcal {P} \in P\), where \(\mathcal {P}_{j}^{k}=[\mathcal {P}[j],\ldots ,\mathcal {P}[k]]\), \(0\le j \le k < n\) and the outcome of the decoder is U which can be split into the sub-blocks \(U_i\) of length \(n'\), \(0\le i <m\).
Definition 1
\(\mathcal {M}(\mathcal {P},i)\) is the path metric of the decoded vector \(\mathcal {P}_{0}^{i}\), calculated as [30]
where \(i\in \left[ 0,n\right) \).
Definition 2
\(\mathcal {M}_{\min }^{l}(P,i)\) is the lth minimum path metric of \(\mathcal {M}(P,i)\), where \(\mathcal {M}(P,i) = \left\{ \mathcal {M}(\mathcal {P},i) | \mathcal {P} \in P\right\} \) and \(i\in \left[ 0,n\right) \).
Definition 3
Fork(P, i) is defined as assume \(P^\prime = P\), for \(\forall \mathcal {P} \in P^\prime \), set \(\mathcal {P}[i]=1\) and \(P\leftarrow P \cup \mathcal {P}\), where \(i\in \left[ 0,n\right) \) [22].
Definition 4
Prune(P, i, l) is defined as the operation that when \(\left| P \right| >l\), for \(\forall \mathcal {P} \in P\) and \(\mathcal {M}(\mathcal {P},i) > \mathcal {M}_{\min }^{l}(P,i)\), set \(P\leftarrow P {\setminus } {\mathcal {P}}\) [30].
The detailed description of the decoding procedure of BC-SCL decoder is shown in Algorithm 1.

3.4 Performance of the SLA IR scheme
Let \(\mathcal {W}_i\) be the corresponding bit channel of polar codes performed in our forward reconciliation phase of the SLA IR scheme, \(P_e\left( \mathcal {W}_i\right) \) is the probability of error on the ith bit channel, where \(i=0,1,\ldots ,n-1\). The union upper bound of correctness \(\varepsilon _\mathrm {f}\) of forward reconciliation phase is estimated as [31]
Then, we analyze the total correctness of the SLA IR scheme in two cases.
Case I. \(r\ne 0\). In this case, the total \(\varepsilon \)-correctness \(\varepsilon _\mathrm {I}\) can be calculated as
where \(\varepsilon _a\) is the failure probability of the acknowledgment reconciliation phase and \(1-\left( 1-\frac{l}{2^d}\right) ^{m-i}\) is the probability of error on i sub-blocks which passed the CRC check in the forward reconciliation phase.
Case II. \(r = 0\). In this case, all outcome sub-blocks of the BC-SCL decoder will pass the CRC check in the forward reconciliation phase, and the total correctness \(\varepsilon _\mathrm {II}\) can be calculated as
Thus, the total \(\varepsilon \)-correctness of SLA IR scheme can be calculated as
With optimized construction of polar codes and LDPC codes [8, 31], we set \(\varepsilon _\mathrm {a} \le 10^{-6}\) and \(\varepsilon _\mathrm {f} \le 10^{-2}\). The analyzed results of \(\varepsilon \) versus d of the SLA IR scheme is shown in Fig. 2, according to Eq. (14), here \(l=16\), \(m=1,8,32,128\) and \(d\ge \log _2{l}\). As shown in Fig. 2, the value of \(\varepsilon \) becomes higher with larger m and approaches to the lower bound of \(10^{-8}\) when \(d\ge 36\).
Assume \(P^U_j\) is error probability of the decoded sub-block in the forward reconciliation and the error probability threshold of a sub-block is \(\epsilon \), where \(j=0, 1, \cdots , m-1\). Thus, the upper bound of \(P^U_j\) can be estimated by \(P_e(\mathcal {W}_i)\) as
and the upper bound of the decoded sub-blocks with error bits in forward reconciliation r can be estimated as
With the implementation of upgrading and degrading channel construction of polar codes [31, 32], the upper bound of \(P_e(\mathcal {W}_j)\) is calculated, and the estimated upper bound of r is shown in Fig. 3 with different m when \(\epsilon = 10^{-3}\), \(E_\mu =0.02\), \(d=32\) and \(md < n H(E_\mu )\).
Assume the efficiency of polar codes as \(f_\mathrm {I}\) and the efficiency of the LDPC codes as \(f_\mathrm {II}\). After the acknowledgment reconciliation, the total efficiency of SLA IR scheme is
where md is the upper bound of leaked information to Eve from the transmitted CRC tag values, extra m bits information may leaked to Eve from the vector \(\sigma \) and \(\varepsilon _\mathrm {f}rn' f_\mathrm {II}H_2(E_\mu )\) is the syndrome information leaked in the acknowledgment reconciliation.
In the proposed SLA IR scheme, we divide the error correction block to m sub blocks, which will increase the overall efficiency. Without block partition strategy, we have \(m=1\) and the efficiency \(f_{m=1}\) can be calculated as
Thus, given the fixed \(f_\mathrm {I}\), the increased efficiency yield \(\mathcal {Y}(m)\) of SLA IR scheme with divide the error correction block into m sub blocks can be calculated as
The estimation results of \(\mathcal {Y}(m)\) are shown in Fig. 4, where \(E_\mu =0.02\), \(m=32\). The yield of efficiency increases as block length and \(\varepsilon _\mathrm {f}\) increase and approaches to 0.01 when \(\varepsilon _\mathrm {f}\) equals 0.1 and block length is larger than \(10^8\). According to Eq. (4), the yield of efficiency will lead to higher final secure key rates of QKD systems.
4 Results
We have implemented the Shannon-limit approached (SLA) IR scheme with the BC-SCL decoder. Afterward, a series of experiments have been conducted to evaluate the efficiency of the SLA IR scheme with the limitation of \(\varepsilon _\mathrm {f} \le 0.01\). In the experiments, the upgrading and degrading channel construction of polar codes [31, 32] is used to determine the frozen vector of polar codes. The number of sub-blocks m and length of CRC d are both set as 32 and the list size of BC-SCL decoder l is set as 16, so that \(\varepsilon \)-correctness of SLA scheme is calculated as the level of \(10^{-8}\) with \(\varepsilon _\mathrm {II}=10^{-6}\). Meanwhile, the correction threshold of LDPC codes [8] is directly used to evaluate the efficiency of the acknowledgment reconciliation. We collected the sifted key from the QKD network [33], and extended the collected data with the targeted length and QBER as the sifted key used in experiment.
The sifted key used in the experiment is collected from the QKD network experiment [33], and extended to the targeted length and QBER.
The SLA IR scheme is tested for 10,000 times each round with QBER ranging from 0.01 to 0.12 with interval of 0.01, block length of 1 Mb, 16 Mb, 128 Mb. The experimental results of the \(\varepsilon _\mathrm {f}\), the reconciliation efficiency f and average yield \(\gamma \) are shown in Table 2. In particular, the leaked information used for calculating the efficiency is accumulated from all tests instead of one test for the different error sub-blocks in the forward reconciliation. Meanwhile, we have tested the SLA IR scheme for three practical cases [33,34,35] and the performance is shown in Appendix section.
The efficiency f of the SLA IR scheme is 1.205, 1.114, 1.091 when the block length is 1 Mb, 16 Mb, 128 Mb, respectively. When the block length increases to 128 Mb, the f and \(\gamma \) of our SLA IR scheme are much more efficient than the previous polar codes-based IR schemes shown in Table 1. Meanwhile, the efficiency increases and the \(\varepsilon _\mathrm {f}\) decreases as block length is increased to 1 Mb, 16 Mb and 128 Mb. Moreover, the SLA IR scheme runs around 167 h on a personal computer with the block length \(n=\) 1 Gb, \(E_\mu =0.02\), resulting the efficiency of 1.055 and \(\varepsilon _\mathrm {f}\) less than \(10^{-2}\). As shown in Table 2, performance of polar codes-based IR schemes can be improved by increasing the block lengths; however, the implementation of large-scale decoders will result in huge computational complexity, which may destroy the system availability. Therefore, with limited block lengths, our SLA IR scheme can be performed to further improve both the reconciliation efficiency and the correctness of QKD systems.
5 Conclusion
In this article, we propose a Shannon-limit approached (SLA) information reconciliation (IR) scheme based on polar codes in quantum key distribution (QKD) systems, which achieves high reconciliation efficiency and decreases the overall IR failure probability to \(10^{-8}\). The proposed SLA IR scheme mainly consists of two phases: the forward reconciliation phase and the acknowledgment reconciliation phase. In the forward reconciliation phase, the sifted key is divided into sub-blocks and performed with the improved block checked successive cancellation list decoder, where errors can be efficient located and corrected in each sub-block. Afterward, the additional acknowledgment reconciliation phase is performed to the failure corrected sub-blocks. The experimental results show that the overall failure probability of the SLA IR scheme is decreased to \(10^{-8}\) and the efficiency is improved to 1.091 with the IR block length of 128 Mb. Therefore, with limited block lengths, our SLA IR scheme can be performed to further improve both the reconciliation efficiency and the correctness of QKD systems. The SLA IR scheme achieves the efficiency of 1.055 with quantum bit error rate of 0.02, when the input scale length increased to 1 Gb, which is hundred times larger than the state-of-the-art implemented polar codes-based IR schemes.
References
Lo, H.K., Curty, M., Tamaki, K.: Secure quantum key distribution. Nat. Photonics 8, 595 (2014). https://doi.org/10.1038/nphoton.2014.149
Scarani, V., Bechmann-Pasquinucci, H., Cerf, N.J., Duek, M., Ltkenhaus, N., Peev, M.: The security of practical quantum key distribution. Rev. Mod. Phys. 81(3), 1301 (2009). https://doi.org/10.1103/RevModPhys.81.1301
Gisin, N., Ribordy, G., Tittel, W., Zbinden, H.: Quantum cryptography. Rev. Mod. Phys. 74(1), 145 (2002). https://doi.org/10.1103/RevModPhys.74.145
Martinez-Mateo, J., Elkouss, D., Martin, V.: Key reconciliation for high performance quantum key distribution. Sci. Rep. 3, 1576 (2013). https://doi.org/10.1038/srep01576
Brassard, G., Salvail, L.: Secret-key reconciliation by public discussion. In: Workshop on the Theory and Application of of Cryptographic Techniques. Springer, pp. 410–423 (1993)
Bennett, C.H., Bessette, F., Brassard, G., Salvail, L., Smolin, J.: Experimental quantum cryptography. J. Cryptol. 5(1), 3 (1992)
Yan, H., Ren, T., Peng, X., Lin, X., Jiang, W., Liu, T., Guo, H.: Information reconciliation protocol in quantum key distribution system. In: 2008 Fourth International Conference on Natural Computation, vol. 3, pp. 637–641. IEEE (2008)
Elkouss, D., Leverrier, A., Alleaume, R., Boutros, J.J.: Efficient reconciliation protocol for discrete-variable quantum key distribution. In: 2009 IEEE International Symposium on Information Theory, pp. 1879–1883 (2009). https://doi.org/10.1109/ISIT.2009.5205475
Li, Q., Wen, X., Mao, H., Wen, X.: An improved multidimensional reconciliation algorithm for continuous-variable quantum key distribution. Quantum Inf. Process. 18(1), 25 (2018). https://doi.org/10.1007/s11128-018-2126-0
Jouguet, P., Kunz-Jacques, S.: High performance error correction for quantum key distribution using polar codes. Quantum Info. Comput. 14(3–4), 329 (2014)
Yan, S.L., Wang, J.D., Fang, J.B., Jiang, L., Wang, X.: An improved polar codes-based key reconciliation for practical quantum key distribution. Chin. J. Electron. 27(2), 250 (2018). https://doi.org/10.1049/cje.2017.07.006
Nakassis, A., Mink, A.: Polar codes in a QKD environment. In: SPIE Sensing Technology + Applications, vol. 9123. SPIE (2014). https://doi.org/10.1117/12.2050919
Arikan, E.: Channel polarization: a method for constructing capacity-achieving codes. In: 2008 IEEE International Symposium on Information Theory, pp. 1173–1177 (2013). https://doi.org/10.1109/ISIT.2008.4595172
Arikan, E.: Channel polarization: a method for constructing capacity-achieving codes for symmetric binary-input memoryless channels. IEEE Trans. Inf. Theory 55(7), 3051 (2009). https://doi.org/10.1109/TIT.2009.2021379
Mori, R., Tanaka, T.: Performance and construction of polar codes on symmetric binary-input memoryless channels. In: 2009 IEEE International Symposium on Information Theory, pp. 1496–1500 (2009). https://doi.org/10.1109/ISIT.2009.5205857
Lee, S., Heo, J.: Efficient reconciliation protocol with polar codes for quantum key distribution. In: 2018 Tenth International Conference on Ubiquitous and Future Networks (ICUFN), pp. 40–43 (2018). https://doi.org/10.1109/ICUFN.2018.8436787
Tang, B.Y., Liu, B., Zhai, Y.P., Wu, C.Q., Yu, W.R.: High-speed and large-scale privacy amplification scheme for quantum key distribution. Sci. Rep. 9(1), 15733 (2019). https://doi.org/10.1038/s41598-019-50290-1
Cai, R.Y., Scarani, V.: Finite-key analysis for practical implementations of quantum key distribution. New J. Phys. 11(4), 045024 (2009)
Pedersen, T. B., Toyran, M.: High performance information reconciliation for QKD with CASCADE. arXiv preprint arXiv:1307.7829 (2013)
Mateo, J.M.: Efficient information reconciliation for quantum key distribution = reconciliacin eficiente de informacin para la distribucin cuntica de claves. Doctoral thesis, Universidad Politcnica de Madrid (2011). http://oa.upm.es/9717/
Mller-Quade, J., Renner, R.: Composability in quantum cryptography. New J. Phys. 11(8), 085006 (2009). https://doi.org/10.1088/1367-2630/11/8/085006
Tal, I., Vardy, A.: List decoding of polar codes. In: 2011 IEEE International Symposium on Information Theory Proceedings, pp. 1–5 (2011). https://doi.org/10.1109/ISIT.2011.6033904
Niu, K., Chen, K.: CRC-aided decoding of polar codes. IEEE Commun. Lett. 16(10), 1668 (2012). https://doi.org/10.1109/LCOMM.2012.090312.121501
Wang, T., Qu, D., Jiang, T.: Parity-check-concatenated polar codes. IEEE Commun. Lett. 20(12), 2342 (2016). https://doi.org/10.1109/LCOMM.2016.2607169
Hashemi, S.A., Condo, C., Gross, W.J.: Fast simplified successive-cancellation list decoding of polar codes. In: 2017 IEEE Wireless Communications and Networking Conference Workshops (WCNCW), pp. 1–6 (2017). https://doi.org/10.1109/WCNCW.2017.7919044
Hashemi, S.A., Condo, C., Gross, W.J.: Simplified successive-cancellation list decoding of polar codes. In: 2016 IEEE International Symposium on Information Theory (ISIT), pp. 815–819 (2016). https://doi.org/10.1109/ISIT.2016.7541412
Hashemi, S.A., Condo, C., Gross, W.J.: Fast and flexible successive-cancellation list decoders for polar codes. IEEE Trans. Signal Process. 65(21), 5756 (2017). https://doi.org/10.1109/TSP.2017.2740204
Chen, K., Li, B., Shen, H., Jin, J., Tse, D.: Reduce the complexity of list decoding of polar codes by tree-pruning. IEEE Commun. Lett. 20(2), 204 (2016). https://doi.org/10.1109/LCOMM.2015.2506568
Chen, J., Fan, Y., Xia, C., Tsui, C., Jin, J., Chen, K., Li, B.: Low-complexity list successive-cancellation decoding of polar codes using list pruning. In: 2016 IEEE Global Communications Conference (GLOBECOM), pp. 1–6 (2016). https://doi.org/10.1109/GLOCOM.2016.7841969
Balatsoukas-Stimming, A., Parizi, M.B., Burg, A.: LLR-based successive cancellation list decoding of polar codes. IEEE Trans. Signal Process. 63(19), 5165 (2015). https://doi.org/10.1109/TSP.2015.2439211
Tal, I., Vardy, A.: How to construct polar codes. IEEE Trans. Inf. Theory 59(10), 6562 (2013). https://doi.org/10.1109/TIT.2013.2272694
Tang, B.Y.: The impletmentation of upgrading channels for construction of polar code. https://github.com/cfxtby/PolarCodeForQKD. Accessed 2 Jan (2020)
Joshi, S.K., Aktas, D., Wengerowsky, S., Lonari, M., Neumann, S.P., Liu, B., Scheidl, T., Samec, K.L., Qiu, A.: A trusted-node-free eight-user metropolitan quantum communication network. arXiv preprint arXiv:1907.08229 (2019)
Liu, Y., Chen, T.Y., Wang, L.J., Liang, H., Shentu, G.L., Wang, J., Cui, K., Yin, H.L., Liu, N.L., Li, L., Ma, X., Pelc, J.S., Fejer, M.M., Peng, C.Z., Zhang, Q., Pan, J.W.: Experimental measurement-device-independent quantum key distribution. Phys. Rev. Lett. 111(13), 130502 (2013). https://doi.org/10.1103/PhysRevLett.111.130502
Wei, K., Li, W., Tan, H., Li, Y., Min, H., Zhang, W., Li, H., You, L., Wang, Z., Jiang, X.: High-speed measurement-device-independent quantum key distribution with integrated silicon photonics. arXiv: Quantum Physics (2019)
Acknowledgements
This work was supported in part by the National Natural Science Foundation of China under Grant No. 61972410 and the research plan of National University of Defense Technology under Grant No. ZK19-13.
Author information
Authors and Affiliations
Contributions
BYT and BL proposed the scheme, performed the experiments, wrote the paper and contributed equally. This work was conceived by BL and WRY, supervised by WRY and co-supervised by CQW. All authors reviewed the manuscript.
Corresponding authors
Ethics declarations
Conflict of interest
The authors declare no competing interests.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Appendix
Appendix
Our SLA IR scheme can be directly adapted into the practical QKD systems. And we tested the performance of the SLA IR scheme for three practical cases [33,34,35].
In article [34], the QKD system generated keys with the length of about 0.5Mb and the QBER of 0.005. Thus, we tested our SLA IR scheme with QBER of 0.005 and input length of 0.5 Mb, and the reconciliation efficiency reaches to 1.315. Meanwhile, our SLA IR scheme reaches the efficiency of 1.273, 1.168 and 1.084 with the input length of 1Mb, 16Mb and 128Mb, respectively, when the QBER is 0.005. Table 3 shows the experimental results of the SLA IR scheme when the QBER is 0.005.
In Ref. [35], the length of the sifted key is about 7Mb, the reconciliation efficiency is set as 1.16 and the final secure key rate is calculated as \(1.29 \times 10^{-7}\) bits/pulse when QBER is about 0.028 and the total loss is 28.0 dB. We tested the reconciliation efficiency of the SLA IR scheme with the QBER of 0.028 and the input length of 1 Mb. The SLA IR scheme improves the efficiency to 1.141, so that the final secure key rate is improved to \(1.3038 \times 10^{-7}\) bits/pulse with the same parameter used in Ref. [35].
Afterward, we performed the SLA IR scheme to correct the sifted key with the length of 16 Mb and the QBER shown in Table 4, which is collected from the QKD network experiment [33]. In our experiments, the frozen vectors are optimized for the IR block size of 16 Mb and the constant QBER (upper thresholds) with the interval of 0.01. In practical QKD systems, the sifted key with the measured QBER \(E_\mu \) is corrected by the polar code optimized with the closest upper threshold.
Table 5 shows the reconciliation efficiency results between each pair of users. Partial pairs of users suffer worse reconciliation efficiency than the experimental results shown in Table 2. For example, the reconciliation efficiency between Alice and Feng drops to 1.2190 when the QBER of the sifted key is 0.042 and the frozen vector used has the correction threshold of 0.05. Thus, the reconciliation efficiency can be further improved by the frozen vectors for constant QBER with smaller intervals.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Tang, BY., Liu, B., Yu, WR. et al. Shannon-limit approached information reconciliation for quantum key distribution. Quantum Inf Process 20, 113 (2021). https://doi.org/10.1007/s11128-020-02919-8
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11128-020-02919-8