Abstract
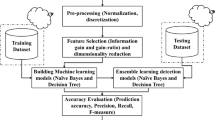
Computer systems, cloud networks, and information systems can all be attacked, but intrusion detection systems can find them. It is challenging to demonstrate the security of the information systems and to uphold such security when they are in use. We put forth the Staked Deep Ensemble Model for Intrusion Detection and Classification (SDEIC) as a solution to these issues. The three stages of feature extraction, optimal feature selection, and classification are used to implement this model. Data normalisation, feature conversion, and feature reduction are all included in the feature extraction phase. A better data normalisation procedure in particular normalises the supplied data. After that, feature conversion is applied to the normalised data. The feature reduction process is then subjected to the Principle Component Analysis (PCA) method. The reduced feature set is then used to select the best features, and this study suggests the Self-Upgraded Squirrel Search Optimisation (SUSSO) algorithm for doing so. In order to classify the specified features, the ensemble model—which consists of the models RNN (Recurrent Neural Network), Improved Deep Belief Network (IDBN), and Deep Max-out Network—is introduced. Additionally, the suggested SUSSO algorithm optimises the weights of the Deep Max-out model during training to guarantee accurate classification. The projected model's accuracy is 97 .5%, which is 12.5%, 2.3%, 41.9%, 1.6%, 18.8% and 15.8% higher than the previous models like NN, RNN, DBN, GRU, and SVM. Lastly, the effectiveness of the suggested approach outperforms the conventional methods. and has obtained satisfactory results.










Similar content being viewed by others
Data Availability
The data is available in https://github.com/ujjwalll/GACMIS.
Change history
09 March 2024
A Correction to this paper has been published: https://doi.org/10.1007/s11042-024-18858-w
Abbreviations
- SDEIC:
-
Staked Deep Ensemble Model for Intrusion detection and Classification
- PCA:
-
Principle Component Analysis
- SUSSO:
-
Self-Upgraded Squirrel Search Optimization
- IDBN:
-
Improved Deep Belief Network
- RNN:
-
Recurrent Neural Network
- DMN:
-
Deep Maxout Network
- CC:
-
Cloud Computing
- ABC:
-
Artificial Bee Colony
- IDS:
-
Intrusion Detection System
- PC:
-
Personal Computer
- FPR:
-
False Positive Rate
- CNN:
-
Convolutional Neural Network
- MLP:
-
Multi-Layer Perceptron
- MAE:
-
Mean Absolute Error
- RMSE:
-
Root Mean Square Error
- NSL-KDD:
-
Network Security Laboratory-Knowledge Discovery in Database
- CDOSD:
-
Cloud-based DOS attack Detection
- DT:
-
Decision Tree
- DDOS:
-
Distributed Denial of Service
- DOS:
-
Denial of Service
- FCM-ANN:
-
Fuzzy C-means clustering-Artificial Neural Network
- V-ELM:
-
Voting-Extreme Learning Machine
- AFA:
-
Anti Forensic Attack
- BHE:
-
B-tree Huffman Encoding
- IP:
-
Internet Protocol
- MECC:
-
Modified Elliptic Curve Cryptography
- DLMNN:
-
Deep Learning Modified Neural Network
- CIDD:
-
Cloud Intrusion Detection Dataset
- GSA:
-
Group Search Algorithm
- GG-SVNN:
-
Gravitational Group Search-based Support Vector Neural Network
- PSO-PNN:
-
Particle Swarm Optimization based Probability Neural Network
- CSTR:
-
Cloud Security Threat Report
- FPR:
-
False Positive Rate
- ANN:
-
Artificial Neural Network
- MAD:
-
Mean Absolute Deviation
- RBM:
-
Restricted Boltzmann Machine
- SSA:
-
Squirrel Search Algorithm
- SSOA:
-
Shark Smell Optimization Algorithm
- SGO:
-
Sea Gull Optimization
- GSKA:
-
Gaining Sharing Knowledge-based Algorithm
- BSO:
-
Brain Storm Optimization
- PSO:
-
Particle Swarm Optimization
- ABC:
-
Artificial Bee Colony
- MCC:
-
Mathew Correlation Co-efficient
- FNR:
-
False Negative Rate
- SEIT:
-
School of Engineering and Information Technology
- ADFA:
-
Australian Defence Force Academy
- GRU:
-
Gated Recurrent Unit
- NPV:
-
Negative Predictive Value
- NN:
-
Neural Network
- DBN:
-
Deep Belief Network
- IoT:
-
Internet of Things
- BABCO:
-
Binary version of Artificial Bee Colony Optimization
- SVM:
-
Support Vector Machine
References
Hajimirzaei B, Navimipour NJ (2018) Intrusion detection for cloud computing using neural networks and artificial bee colony optimization algorithm. ICT Express 5(1):5659. https://doi.org/10.1016/j.icte.2018.01.014
Wang W, Du X, Shan D, Qin R, Wang N (2020) Cloud intrusion detection method based on stacked contractive auto-encoder and support vector machine. IEEE transactions on cloud computing 10(3):1634–1646. https://doi.org/10.1109/TCC.2020.3001017
Wahab OA, Bentahar J, Otrok H, Mourad A (2019) Resource-aware detection and defense system against multi-type attacks in the cloud: Repeated bayesian stackelberg game. IEEE Trans Dependable Secure Comput 18(2):605–622. https://doi.org/10.1109/TDSC.2019.2907946
Alkadi O, Moustafa N, Turnbull B, Choo KR (2020) A deep blockchain framework-enabled collaborative intrusion detection for protecting IoT and cloud networks. IEEE Int Things J 8(12):9463–9472. https://doi.org/10.1109/JIOT.2020.2996590
Mishra P, Varadharajan V, Pilli E, Tupakula U (2018) VMGuard: A vmi-based security architecture for intrusion detection in cloud environment, in IEEE Trans Cloud Comput. https://doi.org/10.1109/TCC.2018.2829202
Seth JK, Chandra S (2018) An effective DOS attack detection model in cloud using artificial bee colony optimization. 3D Res 9:1–13. https://doi.org/10.1007/s13319-018-0195-6
Tummalapalli Siva Rama Krishna, Chakravarthy ASN (2020) Intrusion detection system for cloud forensics using bayesian fuzzy clustering and optimization based SVNN. Evolution Intell 14(2):699–709. https://doi.org/10.1007/s12065-020-00410-y
Singh Jagsir, Singh Jaswinder (2020) Detection of malicious software by analyzing the behavioral artifacts using machine learning algorithms. Inf Softw Technol 121:106–273. https://doi.org/10.1016/j.infsof.2020.106273
Rabbani Mahdi, Wang Yong Li, Khoshkangini Reza, Jelodar Hamed, Zhao Ruxin, Peng Hu (2020) A hybrid machine learning approach for malicious behaviour detection and recognition in cloud computing. J Netw Comput Appl 151:102507. https://doi.org/10.1016/j.jnca.2019.102507
Huda S, Miah S, Yearwood J, Alyahya S (2018) Robin Doss, A malicious threat detection model for cloud assisted internet of things (CoT) based industrial control system (ICS) networks using deep belief network. J Parallel Distribute Comput 120:23–31
Sohal Amandeep Singh, Sandhu Rajinder, Sood Sandeep K, Chang Victor (2018) A cybersecurity framework to identify malicious edge device in fog computing and cloud-of-things environments. Comput Secur 74:340–354. https://doi.org/10.1016/j.cose.2017.08.016
Somani G, Gaur MS, Sanghi D, Conti M, Rajarajan M (2018) Scale inside-out: rapid mitigation of cloud DDoS attacks. IEEE Trans Depend Sec Comput 15(6):959–973. https://doi.org/10.1109/TDSC.2017.2763160
Alkadi O, Moustafa N, Turnbull B (2020) A review of intrusion detection and blockchain applications in the cloud: Approaches, challenges and solutions. IEEE Access 8:104893–104917
Sahi A, Lai D, Li Y, Diykh M (2017) An efficient DDoS TCP flood attack detection and prevention system in a cloud environment. IEEE Access 5:6036–6048
Dong S, Abbas K, Jain R (2019) A survey on Distributed Denial of Service (DDoS) attacks in SDN and cloud computing environments. IEEE Access 7:80813–80828
AbdulazizAldribi Issa Traoré, Moa Belaid, Nwamuo Onyekachi (2020) Hypervisor-based cloud intrusion detection through online multivariate statistical change tracking. Comput Secur 88:101646. https://doi.org/10.1016/j.cose.2019.101646
Garg Sahil, Kaur Kuljeet, Batra Shalini, Aujla Gagangeet Singh, Ranjan Rajiv (2020) En-ABC: An ensemble artificial bee colony based anomaly detection scheme for cloud environment. J Parallel Distribute Comput 135:219–233. https://doi.org/10.1016/j.jpdc.2019.09.013
Mishra Preeti, Verma Ishita, Gupta Saurabh (2020) KVMInspector: KVM Based introspection approach to detect malware in cloud environment. J Inform Secur Appl 51(51):102460. https://doi.org/10.1016/j.jisa.2020.102460
Ravi N, Shalinie SM (2020) Learning-driven detection and mitigation of DDoS attack in IoT via SDN-cloud architecture. IEEE Internet Things J 7(4):3559–3570
Raja Sree T, SairaBhanu SM (2019) HAP: detection of HTTP flooding attacks in cloud using diffusion map and affinity propagation clustering. IET Inf Secur 13(3):188–200. https://doi.org/10.1049/iet-ifs.2018.5382
Li G, Wu SX, Zhang S, Li Q (2020) Neural networks-aided insider attack detection for the average consensus algorithm. IEEE Access 8:51871–51883
Rajakumar BR (2013) Impact of static and adaptive mutation techniques on genetic algorithm. Int J Hybrid Intell Syst 10 1 11 12. https://doi.org/10.3233/HIS-120161
Rajakumar BR (2013) Static and adaptive mutation techniques for genetic algorithm: A systematic comparative analysis. Int J Comput Sci Eng 8(2):180–193. https://doi.org/10.1504/IJCSE.2013.053087
Swamy SM, Rajakumar BR, Valarmathi IR (2013) Design of hybrid wind and photovoltaic power system using opposition-based genetic algorithm with cauchy mutation, IET chennai fourth international conference on sustainable energy and intelligent systems (SEISCON 2013), Chennai, India. https://doi.org/10.1049/ic.2013.0361
Aloysius G, Rajakumar BR (2013) APOGA: An Adaptive Population Pool Size based Genetic Algorithm, AASRI procedia - 2013 AASRI conference on intelligent systems and control (ISC 2013), Vol. 4, pages: 288–296. https://doi.org/10.1016/j.aasri.2013.10.04
Jain M, Singh V, Rani A (2019) A novel nature-inspired algorithm for optimization: Squirrel search algorithm. Swarm Evol Comput 44:148–175
Pandeeswari N, Kumar Ganesh (2016) Anomaly detection system in cloud environment using fuzzy clustering based ANN. Mob Netw Appl 21(3):494–505. https://doi.org/10.1007/s11036-015-0644-x
Gopal Singh Kushwah and Virender Ranga (2020) Voting extreme learning machine based distributed denial of service attack detection in cloud computing. J Inf Secur Appl 53:102532. https://doi.org/10.1016/j.jisa.2020.102532
Rani DR, Geethakumari G (2020) Secure data transmission and detection of anti-forensic attacks in cloud environment using MECC and DLMNN. Comput Commun 150:799–810
Ahmad Shokoohsaljooghi and Hamid Mirvaziri (2019) Performance improvement of intrusion detection system using neural networks and particle swarm optimization algorithms. Int J Inf Technol 12(3):849–860. https://doi.org/10.1007/s41870-019-00315-9
Rabbani M, Wang YL, Khoshkangini R, Jelodar H, Zhao R, Hu P (2020) A hybrid machine learning approach for malicious behaviour detection and recognition in cloud computing. J Netw Comput Appl 151:102507
Anowar F, Sadaoui S, Selim B (2021) Conceptual and empirical comparison of dimensionality reduction algorithms (pca, kpca, lda, mds, svd, lle, isomap, le, ica, t-sne). Comput Sci Rev 40:100378
Furqan M, Hartono H, Ongko E, Ikhsan M (2017) Performance of arithmetic crossover and heuristic crossover in genetic algorithm based on alpha parameter. IOSR J Comput Eng (IOSR-JCE) 19(1):31–36
Wang Y, Yang G, Xie R, Liu H, Liu K, Li X (2021) An ensemble deep belief network model based on random subspace for NO x concentration prediction. ACS Omega 6(11):7655–7668
Li J, Zhao S, Yang J, Huang Z, Liu B, Chen S, Pan H, Wang Q (2020) WCP-RNN: a novel RNN-based approach for Bio-NER in Chinese EMRs. J Supercomput 76(3):1450–1467
Cai M, Shi Y, Liu J (2013) Deep maxout neural networks for speech recognition. In: 2013 IEEE Workshop on Automatic Speech Recognition and Understanding. IEEE, pp 291–296
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of Interest
The writers say they have no competing interests.
Informed consent
Not Applicable.
Ethical approval.
Not Applicable.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
The original online version of this article was revised: The affiliation of V. Tamizhazhagan was incorrect in the original publication of this article.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Mohan, M., Tamizhazhagan, V. & Balaji, S. Staked deep ensemble model for intruder behaviour detection and classification in cloud. Multimed Tools Appl 83, 57861–57892 (2024). https://doi.org/10.1007/s11042-023-17677-9
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-023-17677-9