Abstract
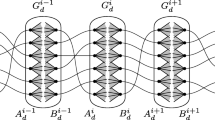
In a linear multi-secret sharing scheme with non-threshold structures, several secret values are shared among n participants, and every secret value has a specified access structure. The efficiency of a multi-secret sharing scheme is measured by means of the complexity σ and the randomness τ. Informally, the complexity σ is the ratio between the maximum of information received by each participant and the minimum of information corresponding to every key. The randomness τ is the ratio between the amount of information distributed to the set of users U = {1, ⋯, n} and the minimum of information corresponding to every key.
In this paper, we discuss σ and τ of any linear multi-secret sharing schemes realized by linear codes with non-threshold structures, and provide two algorithms to make σ and τ to be the minimum, respectively. That is, they are optimal.
Similar content being viewed by others
References
Anderson, R.J., Ding, C., Helleseth, T., Klove, T. How to build robust shared control systems. Design, Codes and Cryptography, 15: 111–124 (1998)
Ashikhmin, A., Barg, A. Minimal vectors in linear codes. IEEE Trans. Inf. Theory, 44(5): 2010–2017 (1998)
Dai, S., Tang, C., Chen, Y. The Optimal Linear Multi-Secret Sharing Scheme for Non-Threshold Access Structure. ACM International Conference Proceeding Series, SIN’11-Proceedings of the 4th International Conference on Security of Information and Networks, 2011, 43–48
Farras, O., Gracia, I., Martin, S., Padro, C. Linear threshold multisecret sharing schemes. ICITS, Lecture Notes in Computer Science, 5973: 110–126 (2010)
Jackson, W.A., Martin, K.M., O’Keefe, C.M. Multisecret threshold schemes. Advances in CRYPTO, Lecture Notes in Computer Science, 773: 126–135 (1994)
Liu, M., Zhang, Z. Secret Sharing Schemes and Secure Multiparty Computation. Publishing House of Electronics Industry, 2008 (in Chinese)
Massey, J.L. Minimal codewords and secret sharing. Proc. 6th Joint Swedish-Russian Workshop on Information Theory, 276–279 (1993)
Massey, J.L. Some applications of coding theory in cryptography. Codes and Ciphers: Cryptography and Coding IV, 33–47 (1995)
Renvall, A., Ding, C. The access structure of some secret sharing schemes. Information Security and Privacy, Lecture Notes in Computer Science, 1172: 67–78 (1996)
Shamir, A. How to share a secret. Comm. ACM, 22: 612–613 (1979)
Tang, C., Gao, X., Zhang C. The optimal linear secret sharing scheme for any given access structure. Journal of System Science and Complexity, 26(4): 634–649 (2013)
Xiao, L., Liu, M. Linear Multi-secret sharing schemes. Science in China Ser. F Information Science, 48(1): 125–136 (2005)
Xiao, L., Liu, M. Linear secret sharing schemes and rearrangements of access structures. Acta Mathematicae Applicatae Sinica (English Series), 20(4): 685–694 (2004)
Author information
Authors and Affiliations
Corresponding author
Additional information
Supported in part by the National Natural Science Foundation of China under Grant No. 11271003, the National Research Foundation for the Doctoral Program of Higher Education of China under Grant No. 20134410110003, High Level Talents Project of Guangdong, Guangdong Provincial Natural Science Foundation under Grant No. S2012010009950, the Project of Department of Education of Guangdong Province under Grant No 2013KJCX0146, and the Natural Science Foundation of Bureau of Education of Guangzhou under Grant No. 2012A004.
Rights and permissions
About this article
Cite this article
Tang, Cm., Dai, Sg. The complexity and randomness of linear multi-secret sharing schemes with non-threshold structures. Acta Math. Appl. Sin. Engl. Ser. 30, 1073–1084 (2014). https://doi.org/10.1007/s10255-014-0431-7
Received:
Revised:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10255-014-0431-7
Keywords
- secret sharing
- multi-secret sharing scheme
- non-threshold multi-access structure
- linear code
- complexity
- randomness