Abstract
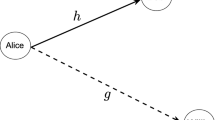
In view of the threats to wireless communication security caused by technical means such as wireless eavesdropping, the state-of-the-art scheme of wireless covert channel modulates the artificial noise from secret messages and superimposes it on normal signals for transmission which avoids detection by unauthorized third parties. This type of wireless covert channel is undetectable. However, the transmission of secret messages is easily interfered. This paper proposes a wireless covert channel scheme based on syndrome-trellis codes. By constructing the syndrome-trellis codes, the sender embeds secret messages in the cover messages to generate the stego messages undetectably. The receiver extracts the secret messages from the stego messages through the corresponding parity check matrix of the syndrome trellis codes. The simulation results show that the proposed scheme has an improvement in reliability while maintaining good undetectability.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Liu, G., Yang, W., Liu, W., Dai, Y.: Designing S-boxes based on 3-D four-wing autonomous chaotic system. Nonlinear Dyn. 82(4), 1867–1877 (2015). https://doi.org/10.1007/s11071-015-2283-y
Soderi, S., Mucchi, L., Hämäläinen, M., Piva, A., Iinatti, J.: Physical layer security based on spread-spectrum watermarking and jamming receiver. Trans. Emerg. Telecommun. Technol. 28, 3142–3158 (2017)
Shu, F., Xu, L., Wang, J., Zhu, W., Xiaobo, Z.: Artificial-noise-aided secure multicast precoding for directional modulation systems. IEEE Trans. Veh. Technol. 67, 6658–6662 (2018)
Xu, G., Yang, W., Huang, L.: Hybrid covert channel in LTE-A: modeling and analysis. J. Netw. Comput. Appl. 111, 117–126 (2018)
Harley, P.M., Tummala, M., McEachen, J.C.: High-throughput covert channels in adaptive rate wireless communication systems. In: 2019 International Conference on Electronics, Information and Communication (ICEIC), 1–7 (2019)
Kitano, T., Iwai, H., Sasaoka, H.: A wireless Steganography technique by embedding DS-SS signal in digital mobile communication systems. Sci. Eng. Rev. Doshisha Univ. 52, 127–134 (2011)
Hijaz, Z., Frost, V.S.: Exploiting OFDM for covert communication. In: Military Communications Conference, 2149–2155 (2010)
Cao, P., Liu, W., Liu, G., Ji, X., Zhai, J., Dai, Y.: A wireless covert channel based on constellation shaping modulation. Secur. Commun. Netw., 1–15 (2018)
Filler, T., Judas, J., Fridrich, J.: Minimizing additive distortion in steganography using syndrome-trellis codes. IEEE Trans. Inf. Forensics Secur. 6, 920–935 (2011)
Archibald, R., Ghosal, D.: A comparative analysis of detection metrics for covert timing channels. Comput. Secur. 45, 284–292 (2014)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2023 The Author(s), under exclusive license to Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Cao, P., Liu, Y., Bu, W., Cao, J. (2023). A Wireless Covert Channel Based on Syndrome-Trellis Codes. In: Dong, J., Zhang, L. (eds) Proceedings of the International Conference on Internet of Things, Communication and Intelligent Technology . IoTCIT 2022. Lecture Notes in Electrical Engineering, vol 1015. Springer, Singapore. https://doi.org/10.1007/978-981-99-0416-7_27
Download citation
DOI: https://doi.org/10.1007/978-981-99-0416-7_27
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-99-0415-0
Online ISBN: 978-981-99-0416-7
eBook Packages: EngineeringEngineering (R0)