Abstract
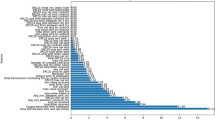
Blockchain-based currencies, i.e., Ethereum, have increased in popularity among followers since 2009. However, scammers have customized offline frauds to this new ecosystem depending on blockchain’s anonymity. As a result, smart Ponzi contracts are circulating on Ethereum, which appear to be secure investment schemes. We employ data mining techniques to present an effective detection model for smart Ponzi contracts over the Ethereum blockchain. First, we extended the dataset of smart Ponzi contracts and eliminated the imbalanced dataset by performing adaptive synthetic sampling. Next, we defined four kinds of feature sets based on the operation codes (opcodes) of smart contracts such as opcode frequency, count vector, n-gram Term Frequency-Inverse Document Frequency (TF-IDF), and opcode sequence features. It is noteworthy that the feature sets are based on the opcodes of smart contracts, which makes our model more reliable once the smart contract is uploaded to the Ethereum Blockchain. Finally, we designed an ensemble classification model combining Bagging-Tree and XGBoost classifiers, compared to other methods, to increase the detection accuracy of smart Ponzi contracts. The empirical and comparative results show that the ensemble model with only n-gram based features presents the best performance and achieves high precision and recall.
Supported by The Key-Area Research and Development Program of Guangdong Grant No. 2019B010137002.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Iansiti, M., Lakhani, K.R.: The truth about blockchain. Harvard Bus. Rev. 95(1), 118–127 (2017)
Nakamoto, S.: Bitcoin: a peer-to-peer electronic cash system (2008). https://bitcoin.org/bitcoin.pdf
Zheng, Z., Xie, S., Dai, H.N., Chen, X., Wang, H.: Blockchain challenges and opportunities: a survey. Int. J. Web Grid Serv. 14(4), 352 (2018)
Higgins, S.: SEC seizes assets from alleged altcoin pyramid scheme (2015). https://www.coindesk.com/sec-seizesalleged-altcoinpyramid-scheme
Morris, D.: The rise of cryptocurrency Ponzi schemes (2017). https://www.theatlantic.com/technology/archive/2017/05/cryptocurrency-ponzi-schemes/5286
Bartoletti, M., Carta, S., Cimoli, T., Saia, R.: Dissecting Ponzi schemes on ethereum: identification, analysis, and impact. Futur. Gener. Comput. Syst. 102, 259–277 (2020)
Zhou, Y., Kumar, D., Bakshi S., Mason, J., Miller, A., Bailey, M.: Erays: reverse engineering ethereum’s opaque smart contracts. In: 27th USENIX Security Symposium (USENIX Security’18). USENIX Association (2018), pp. 1371–1385. https://www.usenix.org/conference/usenixsecurity18/presentation/zhou
Vasek, M., Moore, T.: Analyzing the bitcoin ponzi scheme ecosystem. In: Zohar, A., Eyal, I., Teague, V., Clark, J., Bracciali, A., Pintore, F., Sala, M. (eds.) FC 2018. LNCS, vol. 10958, pp. 101–112. Springer, Heidelberg (2019). https://doi.org/10.1007/978-3-662-58820-8_8
Chen, W., Zheng, Z., Cui, J., Ngai, E., Zheng, P., Zhou, Y.: Detecting Ponzi schemes on ethereum: towards healthier blockchain technology. In: Proceedings of the World Wide Web Conference. International World Wide Web Conferences Steering Committee, pp. 1409–1418 (2018)
Chen, W., Zheng, Z., Ngai, E.C., Zheng, P., Zhou, Y.: Exploiting blockchain data to detect smart Ponzi schemes on ethereum. IEEE Access 7, 37575–37586 (2019)
Bartoletti, M., Pes, B., Serusi, S.: Data mining for detecting bitcoin Ponzi schemes (2018). http://arxiv.org/abs/1803.00646
Rahouti, M., Xiong, K., Ghani, N.: Bitcoin concepts, threats, and machine-learning security solutions. IEEE Access 6, 67189–67205 (2018)
https://etherscan.io/accounts/label/phish-hack. Accessed 4 Sept 2021
https://etherscan.io/accounts. Accessed 4 Sept 2021
He, N., Wu, L., Wang, H., Guo, Y., Jiang, X.: Characterizing code clones in the ethereum smart contract ecosystem. arXiv preprint arXiv:1905.00272 (2019)
Bistarelli, S., Mazzante, G., Micheletti, M., Mostarda, L., Tiezzi, F.: Analysis of ethereum smart contracts and opcodes. In: Barolli, L., Takizawa, M., Xhafa, F., Enokido, T. (eds.) Advanced Information Networking and Applications. AINA 2019. Advances in Intelligent Systems and Computing, vol. 926. Springer, Cham (2020). https://doi.org/10.1007/978-3-030-15032-7_46
Wood, G.: Ethereum: a secure decentralised generalised transaction ledger. http://gavwood.com/paper.pdf
Zhang, Y., Jin, R., Zhou, Z.H.: Understanding bag-of-words model: a statistical framework. Int. J. Mach. Learn. Cybern. 1(1–4), 43–52 (2010). https://doi.org/10.1007/s13042-010-0001-0
Bansal, S.: A comprehensive guide to understand and implement text classification in Python. https://www.analyticsvidhya.com/blog/2018/04/a-comprehensive-guide-to-understand-andimplement-textclassification-in-python. Accessed 1 July 2021
He, H., Bai, Y, Garcia, E.A., Li, S.: ADASYN: adaptive synthetic sampling approach for imbalanced learning. In: IEEE International Joint Conference on Neural Networks (IEEE World Congress on Computational Intelligence), pp. 1322–1328 (2008). https://doi.org/10.1109/IJCNN.2008.4633969
Chen, T., Guestrin, C.: XGBoost: a scalable tree boosting system. In: Proceedings of the 22nd ACM SIGKDD International Conference on Knowledge Discovery and Data Mining, pp. 785–794. ACM (2016)
Breiman, L.: Bagging predictors. Mach. Learn. 24(2), 123–140 (1996)
Raschka, S.: Python Machine Learning. Packt Publishing Ltd., Birmingham (2015)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2022 Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Aljofey, A., Jiang, Q., Qu, Q. (2022). A Supervised Learning Model for Detecting Ponzi Contracts in Ethereum Blockchain. In: Tian, Y., Ma, T., Khan, M.K., Sheng, V.S., Pan, Z. (eds) Big Data and Security. ICBDS 2021. Communications in Computer and Information Science, vol 1563. Springer, Singapore. https://doi.org/10.1007/978-981-19-0852-1_52
Download citation
DOI: https://doi.org/10.1007/978-981-19-0852-1_52
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-19-0851-4
Online ISBN: 978-981-19-0852-1
eBook Packages: Computer ScienceComputer Science (R0)